Splunk SPLK-3003 Splunk Core Certified Consultant Exam Practice Test
Splunk Core Certified Consultant Questions and Answers
Which event processing pipeline contains the regex replacement processor that would be called upon to run event masking routines on events as they are ingested?
A customer with a large distributed environment has blacklisted a large lookup from the search bundle to decrease the bundle size using distsearch.conf. After this change, when running searches utilizing the lookup that was blacklisted they see error messages in the Splunk Search UI stating the lookup file does not exist.
What can the customer do to resolve the issue?
Report acceleration has been enabled for a specific use case. In which bucket location is the corresponding CSV file located?
The Splunk Validated Architectures (SVAs) document provides a series of approved Splunk topologies. Which statement accurately describes how it should be used by a customer?
A customer is using regex to whitelist access logs and secure logs from a web server, but only the access logs are being ingested. Which troubleshooting resource would provide insight into why the secure logs are not being ingested?
What happens when an index cluster peer freezes a bucket?
Where are Splunk Data Model Acceleration (DMA) summaries stored?
In a large cloud customer environment with many (>100) dynamically created endpoint systems, each with a UF already deployed, what is the best approach for associating these systems with an appropriate serverclass on the deployment server?
A customer has asked for a five-node search head cluster (SHC), but does not have the storage budget to use a replication factor greater than 2. They would like to understand what might happen in terms of the users’ ability to view historic scheduled search results if they log onto a search head which doesn’t contain one of the 2 copies of a given search artifact.
Which of the following statements best describes what would happen in this scenario?
The customer has an indexer cluster supporting a wide variety of search needs, including scheduled search, data model acceleration, and summary indexing. Here is an excerpt from the cluster mater’s server.conf:
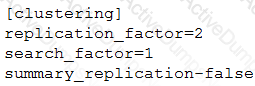
Which strategy represents the minimum and least disruptive change necessary to protect the searchability of the indexer cluster in case of indexer failure?
A customer would like to remove the output_file capability from users with the default user role to stop them from filling up the disk on the search head with lookup files. What is the best way to remove this capability from users?
A customer wants to understand how Splunk bucket types (hot, warm, cold) impact search performance within their environment. Their indexers have a single storage device for all data. What is the proper message to communicate to the customer?
