Paloalto Networks PCCSE Prisma Certified Cloud Security Engineer Exam Practice Test
Prisma Certified Cloud Security Engineer Questions and Answers
What improves product operationalization by adding visibility into feature utilization and missed opportunities?
Prisma Cloud supports which three external systems that allow the import of vulnerabilities and provide additional context on risks in the cloud? (Choose three.)
An administrator sees that a runtime audit has been generated for a host. The audit message is:
“Service postfix attempted to obtain capability SHELL by executing /bin/sh /usr/libexec/postfix/postfix- script.stop. Low severity audit, event is automatically added to the runtime model”
Which runtime host policy rule is the root cause for this runtime audit?
What are the three states of the Container Runtime Model? (Choose three.)
Which two proper agentless scanning modes are supported with Prisma Cloud? (Choose two).
How is the scope of each rule determined in the Prisma Cloud Compute host runtime policy?
The exclamation mark on the resource explorer page would represent?
One of the resources on the network has triggered an alert for a Default Config policy.
Given the following resource JSON snippet:
Which RQL detected the vulnerability?
A)
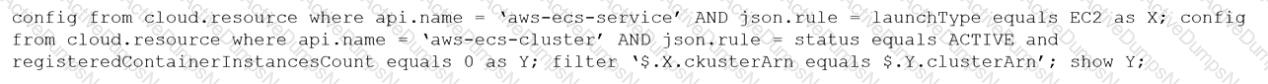
B)
C)
D)
Which of the following is a reason for alert dismissal?
The InfoSec team wants to be notified via email each time a Security Group is misconfigured. Which Prisma Cloud tab should you choose to complete this request?
Taking which action will automatically enable all severity levels?
Web-Application and API Security (WAAS) provides protection for which two protocols? (Choose two.)
An administrator sees that a runtime audit has been generated for a container.
The audit message is:
“/bin/ls launched and is explicitly blocked in the runtime rule. Full command: ls -latr”
Which protection in the runtime rule would cause this audit?
A security team notices a number of anomalies under Monitor > Events. The incident response team works with the developers to determine that these anomalies are false positives.
What will be the effect if the security team chooses to Relearn on this image?
Which of the following is not a supported external integration for receiving Prisma Cloud Code Security notifications?
Which three actions are required in order to use the automated method within Azure Cloud to streamline the process of using remediation in the identity and access management (IAM) module? (Choose three.)
The security team wants to enable the “block” option under compliance checks on the host.
What effect will this option have if it violates the compliance check?
A Prisma Cloud administrator is tasked with pulling a report via API. The Prisma Cloud tenant is located on app2.prismacloud.io.
What is the correct API endpoint?
An administrator has been tasked with a requirement by your DevSecOps team to write a script to continuously query programmatically the existing users, and the user’s associated permission levels, in a Prisma Cloud Enterprise tenant.
Which public documentation location should be reviewed to help determine the required attributes to carry out this step?
Creation of a new custom compliance standard that is based on other individual custom compliance standards needs to be automated.
Assuming the necessary data from other standards has been collected, which API order should be used for this new compliance standard?
Prisma Cloud Compute has been installed on Onebox. After Prisma Cloud Console has been accessed. Defender is disconnected and keeps returning the error "No console connectivity" in the logs.
What could be causing the disconnection between Console and Defender in this scenario?
The security auditors need to ensure that given compliance checks are being run on the host. Which option is a valid host compliance policy?
Given the following information, which twistcli command should be run if an administrator were to exec into a running container and scan it from within using an access token for authentication?
• Console is located at https://prisma-console.mydomain.local
• Token is: TOKEN_VALUE
• Report ID is: REPORTJD
• Container image running is: myimage:latest
A security team has a requirement to ensure the environment is scanned for vulnerabilities. What are three options for configuring vulnerability policies? (Choose three.)
What happens when a role is deleted in Prisma Cloud?
Which two information types cannot be seen in the data security dashboard? (Choose two).
A user from an organization is unable to log in to Prisma Cloud Console after having logged in the previous day.
Which area on the Console will provide input on this issue?
Which two bot categories belong to unknown bots under Web-Application and API Security (WAAS) bot protection? (Choose two.)
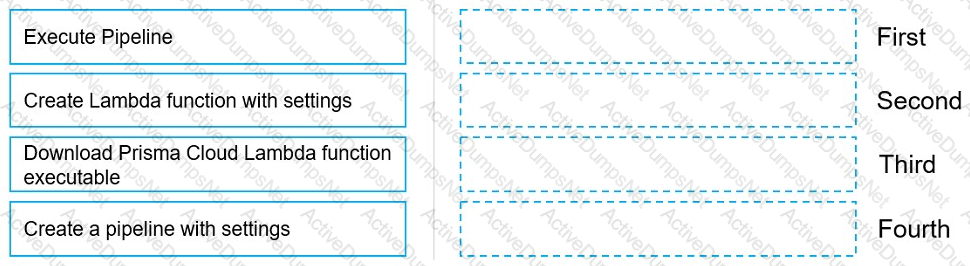
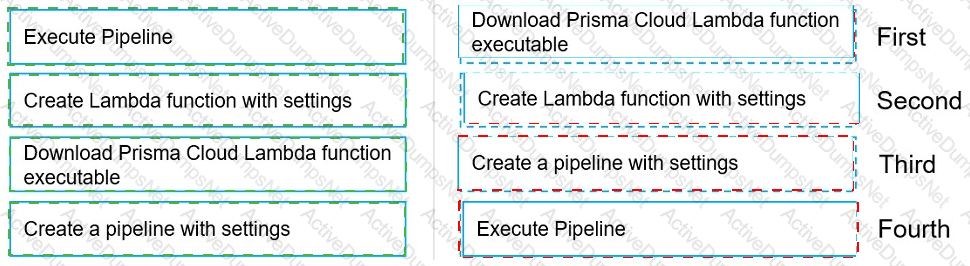
Move the steps to the correct order to set up and execute a serverless scan using AWS DevOps.
In Azure, what permissions need to be added to Management Groups to allow Prisma Cloud to calculate net effective permissions?
Which two offerings will scan container images in Jenkins pipelines? (Choose two.)
Which two integrations enable ingesting host findings to generate alerts? (Choose two.)
The attempted bytes count displays?
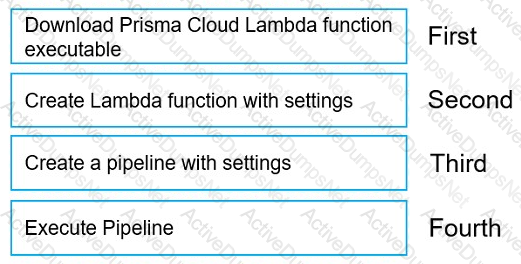
What is the order of steps in a Jenkins pipeline scan?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
Which type of compliance check is available for rules under Defend > Compliance > Containers and Images > CI?
Which three steps are involved in onboarding an account for Data Security? (Choose three.)
What is the primary purpose of Prisma Cloud Code Security?
Given this information:
The Console is located at https://prisma-console.mydomain.local The username is: cluster
The password is: password123
The image to scan is: myimage:latest
Which twistcli command should be used to scan a Container for vulnerabilities and display the details about each vulnerability?
Which step is included when configuring Kubernetes to use Prisma Cloud Compute as an admission controller?
Which three elements are part of SSH Events in Host Observations? (Choose three.)
Which command should be used in the Prisma Cloud twistcli tool to scan the nginx:latest image for vulnerabilities and compliance issues?
A)
B)
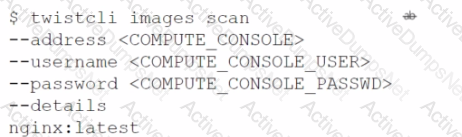
C)
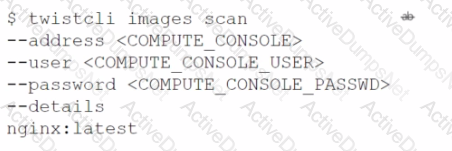
D)
Which two filters are available in the SecOps dashboard? (Choose two.)
Which action would be applicable after enabling anomalous compute provisioning?
How does assigning an account group to an administrative user on Prisma Cloud help restrict access to resources?
What is the behavior of Defenders when the Console is unreachable during upgrades?
Which categories does the Adoption Advisor use to measure adoption progress for Cloud Security Posture Management?
A customer wants to harden its environment from misconfiguration.
Prisma Cloud Compute Compliance enforcement for hosts covers which three options? (Choose three.)
A customer has a development environment with 50 connected Defenders. A maintenance window is set for Monday to upgrade 30 stand-alone Defenders in the development environment, but there is no maintenance window available until Sunday to upgrade the remaining 20 stand-alone Defenders.
Which recommended action manages this situation?
Which options show the steps required after upgrade of Console?
What are two alarm types that are registered after alarms are enabled? (Choose two.)
If you are required to run in an air-gapped environment, which product should you install?
When would a policy apply if the policy is set under Defend > Vulnerability > Images > Deployed?
Which field is required during the creation of a custom config query?
What is the default namespace created by Defender DaemonSet during deployment?
What are two key requirements for integrating Okta with Prisma Cloud when multiple Amazon Web Services (AWS) cloud accounts are being used? (Choose two.)
Which statement applies to Adoption Advisor?
Which option identifies the Prisma Cloud Compute Edition?
Which Prisma Cloud policy type can protect against malware?
An organization wants to be notified immediately to any “High Severity” alerts for the account group “Clinical Trials” via Slack.
Which option shows the steps the organization can use to achieve this goal?
An administrator has access to a Prisma Cloud Enterprise.
What are the steps to deploy a single container Defender on an ec2 node?
Which Defender type performs registry scanning?
Which of the below actions would indicate – “The timestamp on the compliance dashboard?
Which statement is true about obtaining Console images for Prisma Cloud Compute Edition?
What are two ways to scan container images in Jenkins pipelines? (Choose two.)
Which two attributes of policies can be fetched using API? (Choose two.)
A customer wants to be notified about port scanning network activities in their environment. Which policy type detects this behavior?
Which statement about build and run policies is true?
The security team wants to protect a web application container from an SQLi attack. Which type of policy should the administrator create to protect the container?
Which RQL query will help create a custom identity and access management (1AM) policy to alert on Lambda functions that have permission to terminate EC2 instances?
A customer has configured the JIT, and the user created by the process is trying to log in to the Prisma Cloud console. The user encounters the following error message:
What is the reason for the error message?
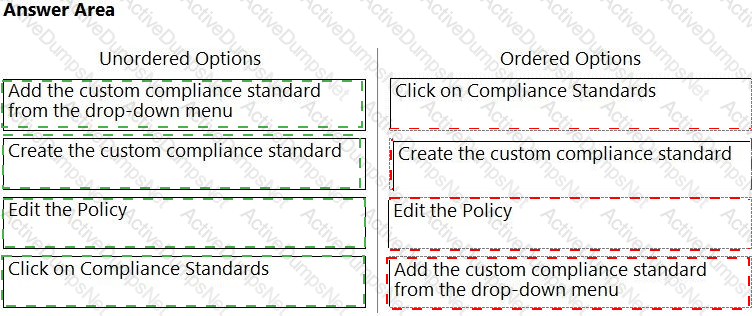
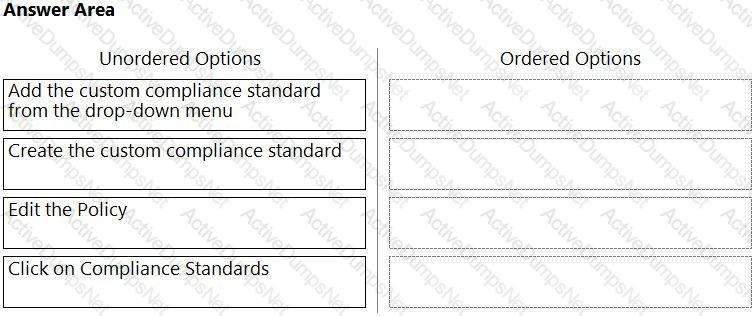
Which order of steps map a policy to a custom compliance standard?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
What must be created in order to receive notifications about alerts generated when the operator is away from the Prisma Cloud Console?
What is required for Prisma Cloud to successfully execute auto-remediation commands?
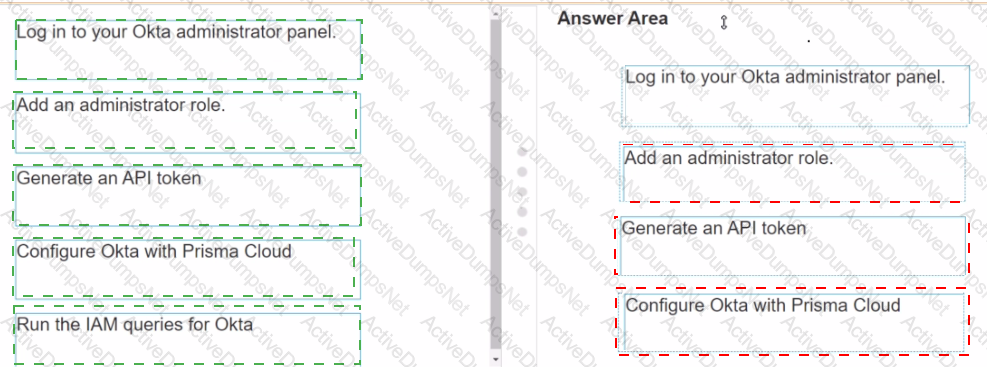
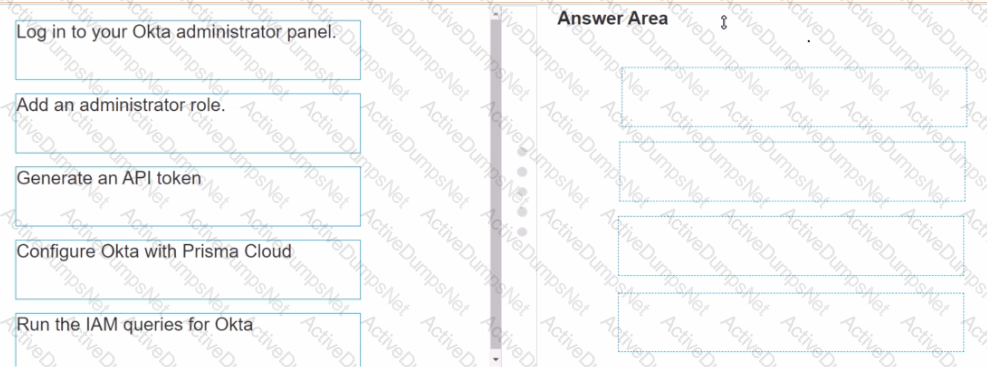
Put the steps of integrating Okta with Prisma Cloud in the right order in relation to CIEM or SSO okra integration.
The administrator wants to review the Console audit logs from within the Console.
Which page in the Console should the administrator use to review this data, if it can be reviewed at all?
Which component(s), if any, will Palo Alto Networks host and run when a customer purchases Prisma Cloud Enterprise Edition?
A customer finds that an open alert from the previous day has been resolved. No auto-remediation was configured.
Which two reasons explain this change in alert status? (Choose two.)
Which two CI/CD plugins are supported by Prisma Cloud as part of its DevOps Security? (Choose two.).

 Graphical user interface, text, application
Description automatically generated
Graphical user interface, text, application
Description automatically generated