Fortinet FCSS_CDS_AR-7.6 FCSS - Public Cloud Security 7.6 Architect Exam Practice Test
FCSS - Public Cloud Security 7.6 Architect Questions and Answers
Refer to the exhibit.
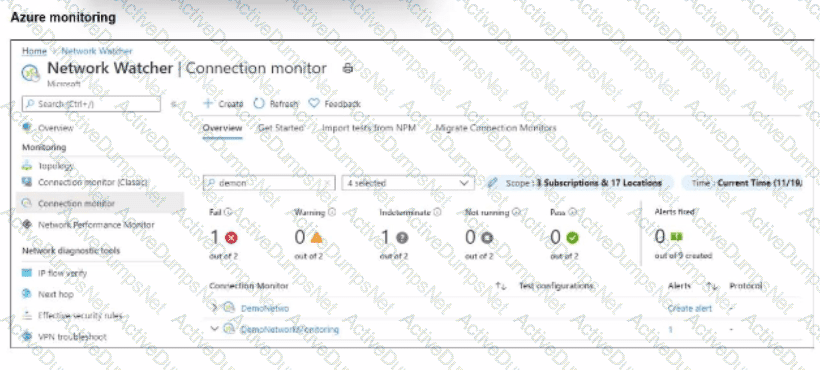
After analyzing the native monitoring tools available in Azure, an administrator decides to use the tool displayed in the exhibit.
Why would an administrator choose this tool?
Refer to the exhibit.
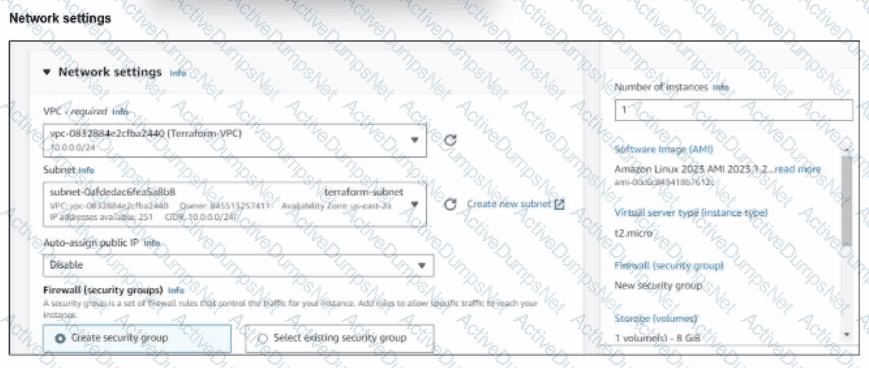
You have deployed a Linux EC2 instance in Amazon Web Services (AWS) with the settings shown on the exhibit.
What next step must the administrator take to access this instance from the internet?
The cloud administration team is reviewing an AWS deployment that was done using CloudFormation.
The deployment includes six FortiGate instances that required custom configuration changes after being deployed. The team notices that unwanted traffic is reaching some of the FortiGate instances because the template is missing a security group.
To resolve this issue, the team decides to update the JSON template with the missing security group and then apply the updated template directly, without using a change set.
What is the result of following this approach?
You areusing Ansible to modify the configuration ofseveral FortiGate VMs.
What is the minimum number of files you need to creat,and in which file should you configure the target FortiGate IP addresses?
Your monitoring team reports performance issues with a web application hosted in Azure. You suspect that the bottleneck might be due to unexpected inbound traffic spikes.
Which method should you use to identify and analyze the traffic pattern?
Refer to the exhibit.
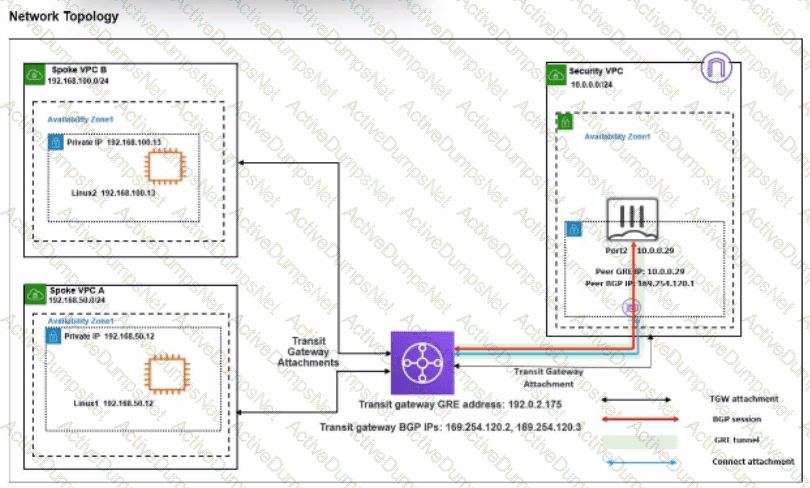
You attempted to access the Linux1 EC2 instance directly from the internet using its public IP address in AWS. However, your connection is not successful.
Given the network topology, what can be the issue?
You have deployed a FortiGate HA cluster in Azure using a gateway load balancer for traffic inspection. However, traffic is not being routed correctly through the firewalls.
What can be the cause of the issue?
Refer to the exhibit.

You are troubleshooting a Microsoft Azure SDN connector issue on your FortiGate VM in Azure.
Which command can you use to examine details about API calls sent by the connector?
Exhibit.
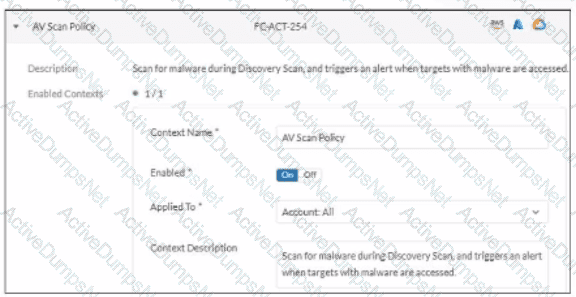
In which type of FortiCNP insights can an administrator examine the findings triggered by this policy?
Refer to the exhibit.
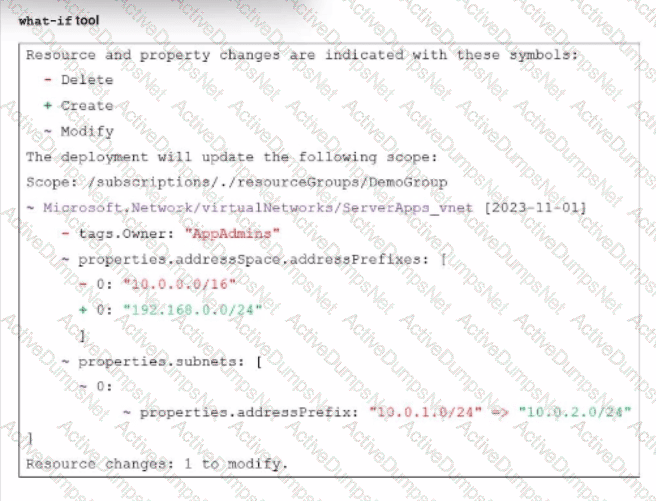
An administrator used the what-if tool to preview changes to an Azure Bicep file.
What will happen if the administrator decides to apply these changes in Azure?
Refer to the exhibit.
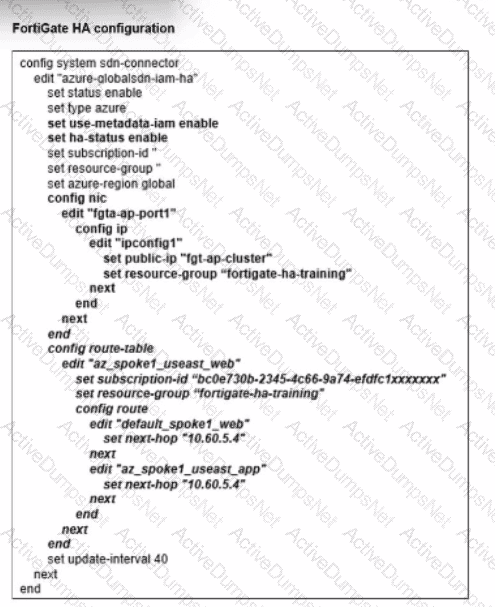
You deployed a FortiGate HA active-passive cluster in Microsoft Azure.
Which two statements regarding this particular deployment are true? (Choose two.)
