Cisco 300-745 Designing Cisco Security Infrastructure (300-745 SDSI) v1.0 Exam Practice Test
Designing Cisco Security Infrastructure (300-745 SDSI) v1.0 Questions and Answers
A company recently discovered that a former employee, who left to join a competitor, continued to access and exfiltrate sensitive data over several weeks after leaving. The breach highlighted vulnerabilities in the organization’s data security and access management practices. To prevent such incidents in the future, the organization must adopt measures that detect and restrict unauthorized data access and transfer. Which mitigation strategy must be implemented to address the issue?
An oil and gas company recently faced a security breach when an employee’s notepad, which contained critical login credentials, was stolen. The incident led to unauthorized access to a user account, which posed a significant risk to sensitive company data and operations. The company wants to adopt a security measure that enhances user account protection. Which action must be taken to prevent breaches like this from happening in the future?
An agricultural company wants to enhance the cybersecurity posture by implementing a defense-in-depth strategy to protect against polymorphic malware threats. Currently, the company’s security infrastructure relies solely on a stateful traditional edge firewall that does not provide adequate protection against malware variants. Which technology must be added to the company’s security architecture to achieve the goal?
A global hotel chain is using Cisco ISE and Cisco switches to manage the network. The hotel company wants to enhance network security by segmenting users and endpoints. The company must ensure that devices within the same VLAN cannot communicate with each other. The goal is to prevent cross-communication without the use of dynamic access control lists. Which action must be taken using Cisco ISE to meet the requirement?
Which financial reporting regulatory framework must a publicly traded company doing business in the US comply with?
A technology company has many remote workers who access corporate resources from various locations. The company must ensure that security policies are managed and enforced directly on endpoints, and endpoints are protected from threats regardless of location. Which firewall architecture meets the requirements?
A developer company recently implemented a testing environment based on Linux operating system. The company needs a technology solution that produces tracing and filtering capabilities in the Linux kernel. Which technology meets these requirements without modifying the kernel source code?
A global marketing firm, based in California with customers on every continent, suffered a data breach that exposed employee and customer PII. Which regulations is the company in danger of violating?
Employees in a healthcare organization could not access their devices when they returned to work after the weekend. The security team discovered that a threat actor had encrypted the devices. Which security solution would mitigate the risk in future?
A technology company recently onboarded a new customer in the medical space. The customer needs a solution to provide data integrity across remote sites. Which solution must be used to meet this requirement?
Refer to the exhibit.
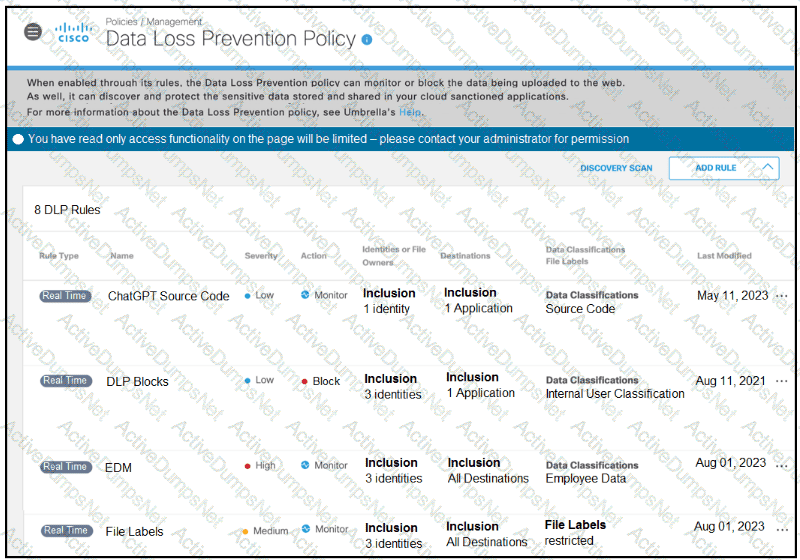
A software developer noticed that the application source code had been found on the internet. To avoid such an incident from happening again, the developer applied a DLP policy to prevent from uploading source code into generative AI tool like ChatGPT. When testing the policy, the developer noticed that it is still possible for the source code to be uploaded. Which action must the developer take to prevent this issue?
A company published software that had a security vulnerability, and an attacker used the vulnerability to steal critical information from the environment. The issue was reported by the security team, and the administrator was instructed to run shift-left security tests before publishing the software. Which component of the software development pipeline must be recommended to run the tests?
A financial company uses a remote access solution that directs all traffic over a secure tunnel. The company recently received some large ISP bills from the headquarter location. According to traffic analysis during the investigation, most of the network traffic was due to employees spending a lot of time on video conferences provided by a SaaS collaboration company. What must the company modify to reduce the cost without negatively impacting security or employee experience?
An IT company experienced the spread of malicious content between user endpoints, which impacted business critical resources. The company wants to implement a solution to control communication between individual endpoints on the network. Which approach achieves the goal?
Which generative AI impact is addressed by a human-in-the-loop design policy?
A developer is building new API functions for a cloud-based application. Before writing the code, the developer wants to ensure that destructive actions, including deleting and updating data, are properly protected by access control identifying sensitive fields such as those that contain passwords or personally identifiable information. Which approach must be used to score the risks proactively?
Which tool must be used to prioritize incidents by a SOC?
