Trend Micro Deep-Security-Professional Trend Micro Certified Professional for Deep Security Exam Exam Practice Test
Total 73 questions
Trend Micro Certified Professional for Deep Security Exam Questions and Answers
Based on the Malware Scan Configuration displayed in the exhibit, which of the following statements is false.

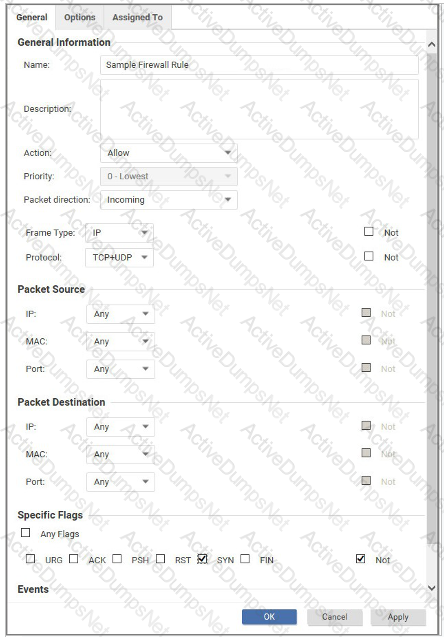
What is the effect of the Firewall rule displayed in the following exhibit?
Which of the following operations makes use of the Intrusion Prevention Protection Module?
An administrator attempts to activate the Deep Security Agent installed on a server by typing the following command in the Command Prompt on the Deep Security Agent computer:
dsa_control -a dsm://server1.acme.com:4120
The Agent does not activate as expected. What is a valid reason for this issue?
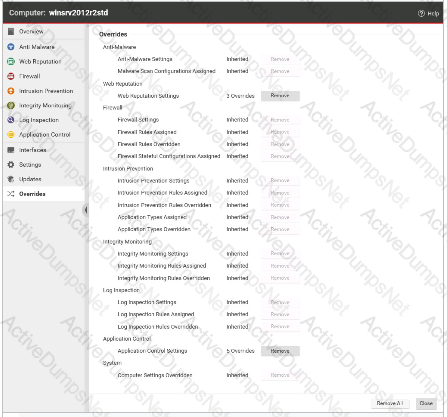
The Overrides settings for a computer are displayed in the exhibit. Which of the following statements is true regarding the displayed configuration?
The Intrusion Prevention Protection Module is enabled, but the traffic it is trying to analyze is encrypted through https. How is it possible for the Intrusion Prevention Protection Module to monitor this encrypted traffic against the assigned rules?
Which of the following is not an operation that is performed when network traffic is intercepted by the network driver on the Deep Security Agent?
Which of the following statements is FALSE regarding Firewall rules using the Bypass action?
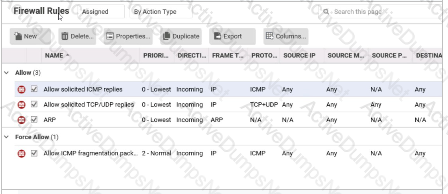
While viewing the details of the Firewall Protection Module, as displayed in the exhibit, you note that a few rules have already been assigned. You try to disable these rules, but they can not be unassigned. Why can the displayed rules not be unassigned?
Which of the following statements is true regarding Event Tagging?
Which of the following correctly describes the Firewall rule Action of Force Allow?
As the administrator in a multi-tenant environment, you would like to monitor the usage of security services by tenants? Which of the following are valid methods for monitoring the usage of the system by the tenants?
Total 73 questions
