Symantec 250-587 Symantec Data Loss Prevention 16.x Administration Technical Specialist Exam Practice Test
Symantec Data Loss Prevention 16.x Administration Technical Specialist Questions and Answers
Which two (2) actions are available for a “Network Prevent: Remove HTTP/HTTPS content” response rule when the content is unable to be removed? (Choose two.)
Why is it important for an administrator to utilize the grid scan feature?
A DLP administrator is preparing to install Symantec DLP and has been asked to use an Oracle database provided by the Database Administration team.
Which SQL *Plus command should the administrator utilize to determine if the database is using a supported version of Oracle?
What detection server type requires a minimum of two physical network interface cards?
A DLP administrator is attempting to add a new Network Discover detection server from the Enforce management console. However, the only available options are Network Monitor and Endpoint servers.
What should the administrator do to make the Network Discover option available?
What detection method utilizes Data Identifiers?
Which two Network Discover/Cloud Storage targets apply Information Centric Encryption as policy response rules?
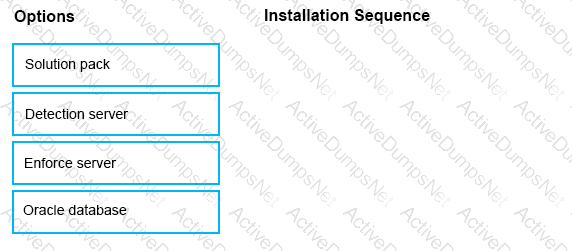
What is the correct installation sequence for the components shown here, according to the Symantec Installation Guide?
Place the options in the correct installation sequence.
An organization wants to restrict employees to copy files only a specific set of USB thumb drives owned by the organization.
Which detection method should the organization use to meet this requirement?
How should a DLP administrator change a policy that it retains the original file when an endpoint incident has detected a “copy to USB device” operation?
How should a DLP administrator change a policy so that it retains the original file when an endpoint incident has detected a “cope to USB device” operation?
Which option is an accurate use case for Information Centric Encryption (ICE)?
Which tool must a DLP administrator run to certify the database prior to upgrading DLP?
A divisional executive requests a report of all incidents generated by a particular region, summarized by department.
What does the DLP administrator need to configure to generate this report?
Which two actions are available for a “Network Prevent: Remove HTTP/HTTPS content” response rule when the content is unable to be removed? (Choose two.)
What are two reasons an administrator should utilize a manual configuration to determine the endpoint location? (Choose two.)
Which two automated response rules will be active in policies that include Exact Data Matching (EDM) detection rule? (Choose two.)
A customer needs to integrate information form DLP incidents into external Governance, Risk, and Compliance dashboards.
Which feature should a third-party component integrate with to provide dynamic reporting, create custom incident remediation processes, or support business processes?
What is the correct order for data in motion when a customer has integrated their CloudSOC and DLP solutions?
A DLP administrator has added several approved endpoint devices as exceptions to an Endpoint Prevent policy that blocks the transfer of sensitive data. However, data transfers to these devices are still being blocked.
What is the first action an administrator should take to enable data transfers to the approved endpoint devices?
A company needs to secure the content of all mergers and Acquisitions Agreements/ However, the standard text included in all company literature needs to be excluded.
How should the company ensure that this standard text is excluded from detection?
Which two (2) detection servers are available as virtual appliances? (Choose two.)
A DLP administrator needs to stop the PacketCapture process on a detection server. Upon inspection of the Server Detail page, the administrator discovers that all processes are missing from the display.
What are the processes missing from the Server Detail page display?
Where should an administrator set the debug levels for an Endpoint Agent?
Which Network Prevent action has taken place when a Network incident snapshot indicates the message has been “Modified”?
Which two DLP products support the new Optical Character Recognition (OCR) engine in Symantec DLP 15.0? (Choose two.)
Which two (2) DLP products support Optical Character Recognition (OCR)? (Choose two.)
An administrator is unable to log in to the Enforce management console as “sysadmin”. Symantec DLP is configured to use Active Directory authentication. The administrator is a member of two roles: “sysadmin” and “remediator.”
How should the administrator log in to the Enforce console with the “sysadmin” role?
Which two (2) detection technology options run on the DLP agent? (Choose two.)
Which two detection servers are available as virtual appliances? (Choose two.)

