Proofpoint PPAN01 Certified Threat Protection Analyst Exam Exam Practice Test
Certified Threat Protection Analyst Exam Questions and Answers
Why do some domains generate a warning when they are added to the custom blocklist in TAP?
An analyst is reviewing a quarantined threat within Threat Protection Workbench.
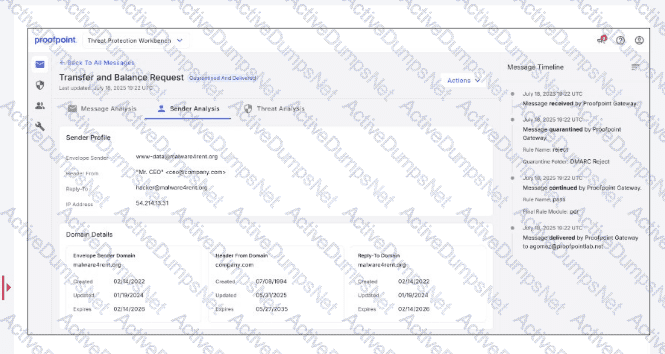
Based on the indicators shown in the exhibit, what is the most likely reason the threat was quarantined?
Which TAP condemnation results from an analysis of emails submitted via Proofpoint ZenGuide Report Suspicious (formerly PhishAlarm)?
Which activity is part of the Preparation phase in the NIST lifecycle?
What is the first action a security analyst should take when beginning to review and prioritize alerts from Targeted Attack Protection (TAP)?
Which of the following is an item that should be included in an incident report as part of the post-incident debrief?
Which TAP Reports tab provides a view of the distribution of threats against your organization, including quantity of messages, variation of threat campaigns seen, and the number of individual threats that weren’t part of a campaign?
As a new analyst, you need to review threat intelligence related to threats in your environment. Which Proofpoint product provides this data?
When filtering for threats on the TAP People page, which two filters have the highest chance of finding compromises? (Select two.)
Refer to the exhibit.
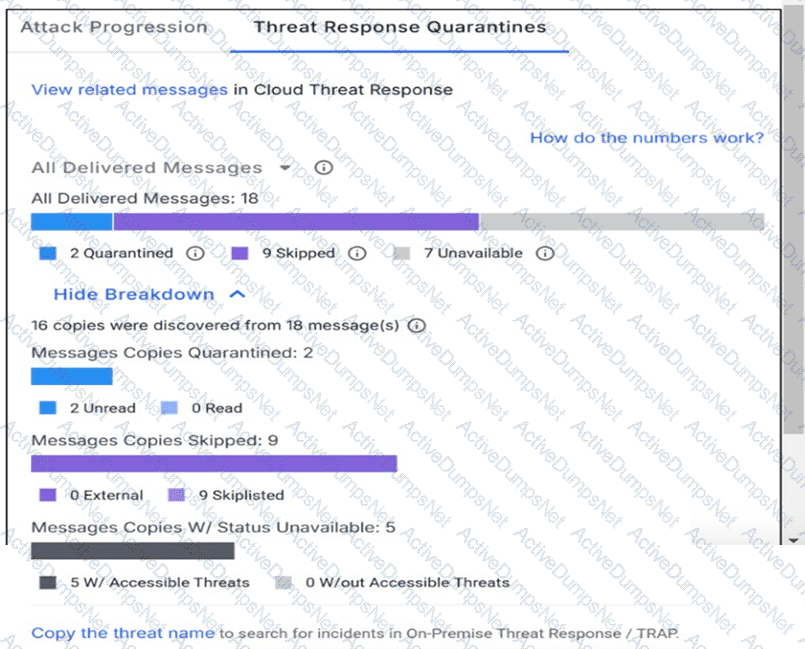
How many messages were sent to a mailbox configured to bypass quarantine for monitoring purposes?
What best describes the nature of the NIST incident response lifecycle?
What is a defining characteristic of Advanced Persistent Threat (APT) actors?
Refer to the exhibit.
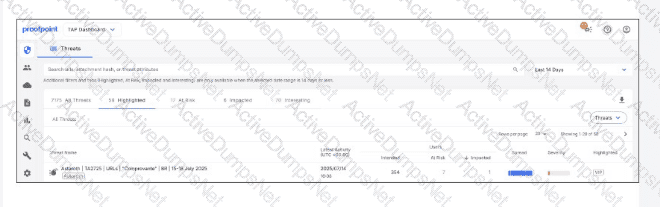
Which two determinations can be made by the data shown on the TAP Dashboard in the exhibit? (Select two.)
Based on the exhibit,
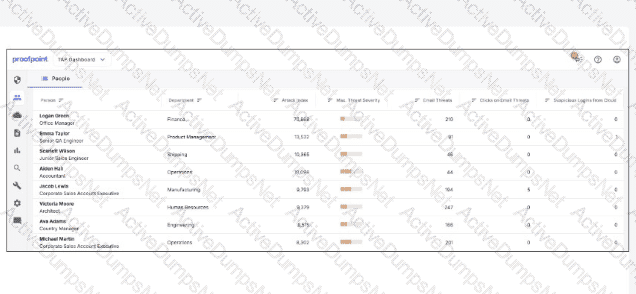
which user would most benefit from attending security awareness training based on their behavior?
An analyst is reviewing the Threat Response Quarantines card for a message in TAP Dashboard, as shown in the exhibit.
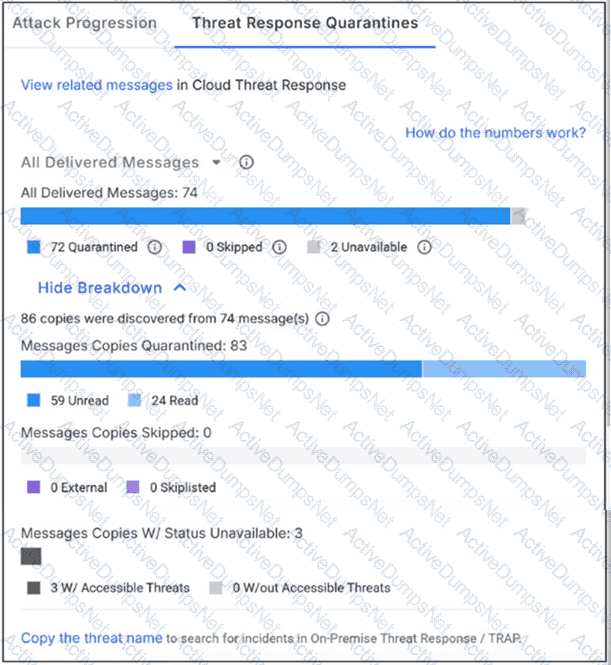
Why might a message be flagged with status “unavailable”?
