Nutanix NCP-NS-7.5 Nutanix Certified Professional - Network and Security (NCP-NS) 7.5 Exam Practice Test
Nutanix Certified Professional - Network and Security (NCP-NS) 7.5 Questions and Answers
An administrator has a requirement to capture application flow data for a policy in Monitor mode and export those events to an external SIEM for correlation with other logs. Which two actions are required to achieve this? (Choose two.)
When setting up a Network Function VM for Service Insertion, an administrator needs to configure the vNICs that will be used for redirecting traffic. What is the correct configuration for the vNICs on the Network Function VM?
A customer wants to migrate VMs from a VLAN Basic Subnet to an Overlay Subnet with the same IP prefix. Which migration approach ensures minimal disruption?
What entity is automatically created on the cluster hosting Prism Central when Microsegmentation is enabled?
An administrator creates a new VPC in No NAT mode to allow VMs in a web tier to reach an external firewall. After deployment... none of the VMs can reach external IP addresses... Which action should the administrator take to restore routed north-south connectivity from the VPC?
An administrator is configuring a Nutanix environment for Flow Network Security Next-Gen. Where should the MTU be set to ensure that Geneve encapsulation overhead is properly accounted for?
An administrator is building a VPC... VPC CIDR: 10.10.0.0/16 Subnet CIDR: 10.10.10.0/24 "Ext_Net_Ext" (NAT): 192.168.1.0/24 "Ext_Net_Internal" (Routed): 172.16.1.0/24 The on-premises application server has an IP address of 172.16.2.50/24. A VM (10.10.10.100) in the VPC Subnet can reach the internet but cannot reach the on-premises server. Which static route needs to be added to the VPC route table to resolve this?
During a security review, the administrator confirms that the existing security policy does not explicitly allow traffic from Environment: Development to Environment: Production. A VM in the Development category was still able to reach a Production VM over IPv6. What is the most likely cause of this behavior?
When cloning a Flow Network Security policy, what should be verified before enabling Enforce mode?
An administrator is deploying a new multi-tenant environment in Prism Central and has created a VPC named TenantVPC1. The administrator needs to enable external connectivity for this VPC so that some services inside the VPC can be accessed from the corporate network without NAT translation, while other services require Internet access through SNAT translation. The administrator plans to use an External Network(s) to provision this connectivity. Which configuration should the administrator apply to satisfy this requirement?
Which two statements are true with respect to Flow Network Security Policies? (Choose two.)
In Nutanix Flow, which action transitions a security policy from observing traffic to actively enforcing the rules?
What is the additional resource requirement for each Prism Central VM when enabling Flow Virtual Networking on a Small Prism Central deployment?
An administrator is designing a VPC for a three-tier application. The workloads must communicate with the Internet using source NAT and also communicate with on-premises networks 10.50.0.0/16 and 172.20.32.0/20 with no address translation. In the Create VPC dialog, the administrator can associate external subnets and specify destination prefixes. Which configuration satisfies the requirements?
While configuring third-party services (Service Insertion) in Flow Network Security Next-Gen, an administrator notices dropped packets when redirecting traffic through a network function. Which configuration change would address this issue?
After creating a BGP session in Flow Virtual Networking, the session status remains down. Which log should an administrator use first in Prism Central to troubleshoot the issue?
Which two options are supported as a Secured Entity in Flow Network Security Application Policies? (Choose two.)
Exhibit:
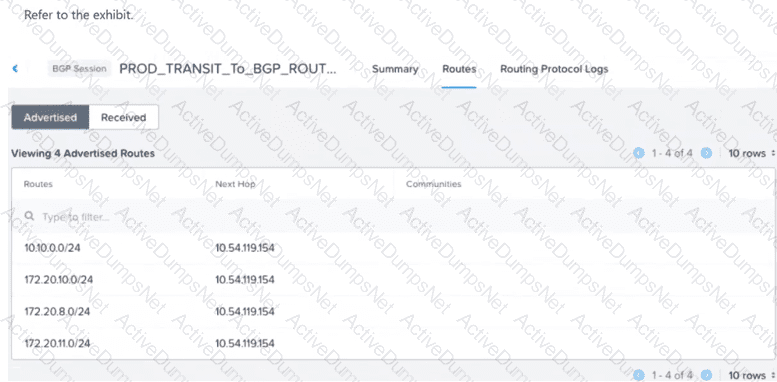
A VM with IP address 172.20.9.5 resides on a subnet with CIDR 172.20.9.0/24. The VPC is successfully peered via BGP with an external router... External networks outside the VPC are unable to reach the VM. What configuration change should be made to enable reachability for the VM?
Exhibit:
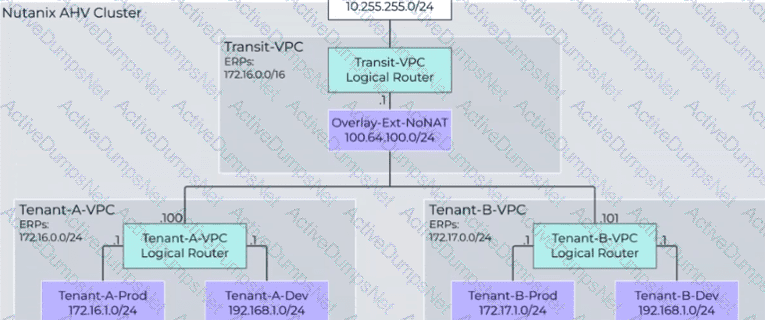
An administrator has just added a new VPC for Tenant-B... However, users are reporting that they are unable to access external resources from VMs created in the Tenant-B-Prod subnet. What should be done to correct the problem?
Which policy type takes highest precedence in Enforce mode?
What type of policy would be used to block all traffic between VMs in the category Environment:Sandbox and VMs in the category Environment:Production?
An administrator manages a four-node cluster Each node has a 4 available 10GB uplinks, and all four are configured as an Active/Active bundle. They want to use Flow Virtual Networking to provide networking to the VMs in the cluster with the following requirements: VMs should be in a single VPC. VMs should be reachable by their real IP addresses. The VPC should have access to the most north/south bandwidth possible. No changes can be made to the physical infrastructure. How can this best be achieved?
Which step is required before placing the Flow Network Security software bundle on a local web server?
An administrator has configured a VPC with multiple overlay subnets and attached a VPN gateway using IPSec. After enabling Jumbo Frames on the physical network, VMs are still experiencing packet drops. What is the most likely reason?
An administrator is deploying a multi-tier application on a Nutanix AHV cluster. The Web tier needs to be accessible from the internet, the App tier must communicate only with the Web tier and the Database tier, and the Database tier should accept traffic only from the App tier. The administrator must determine the correct configuration to ensure secure, reliable connectivity for the Web tier while maintaining isolation from the Internet for the App and Database tiers. Which connectivity option should the administrator implement to meet the requirements?
What must an administrator do before disabling the Network Controller?
An administrator has a VPC with multiple overlay subnets and a VPN gateway configured for site-to-site connectivity. During testing, the administrator noticed fragmented packets and poor performance. Which configuration change resolves this issue without disabling VPN?
Which step is required to prepare an AHV cluster for Flow Virtual Networking?
An administrator must delegate management of a single tenant VPC to a junior engineer. The engineer should be able to modify that VPC but must not see or change any other VPCs or networking configurations in Prism Central. The administrator wants to meet this requirement using RBAC. Which action should the administrator take to meet this requirement?
A new multi-tier application is being deployed across several subnets in a Nutanix environment. The security team wants to create a Flow Network Security Policy to restrict traffic between the tiers, but the complete matrix of required network ports and protocols is not fully documented. Which strategy should the team employ first to accurately capture the necessary communication patterns without risking application outage?
A junior network operator is assigned two predefined roles in Prism Central... Role A: Prism Viewer Role B: VPC Admin The operator reports being able to successfully create, update, and delete Virtual Private Clouds (VPCs). However, the operator is unable to create a VM into the VPC. How does Prism Central determine the operator's effective permissions?
