- Home
- Microsoft
- Microsoft Certified: Security Compliance and Identity Fundamentals
- SC-900
- SC-900 - Microsoft Security Compliance and Identity Fundamentals
Microsoft SC-900 Microsoft Security Compliance and Identity Fundamentals Exam Practice Test
Microsoft Security Compliance and Identity Fundamentals Questions and Answers
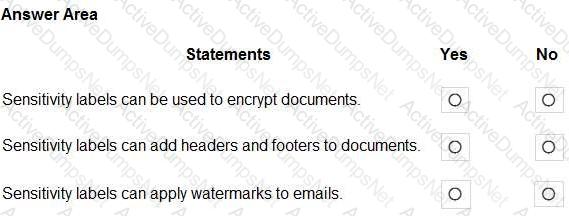
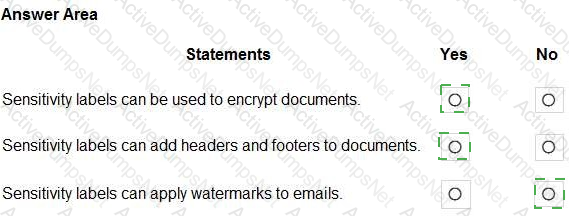
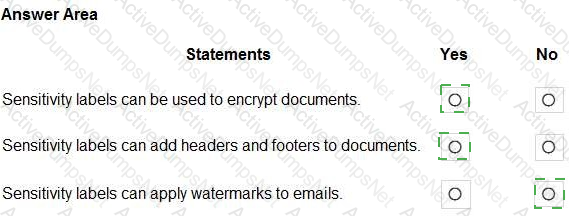
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Options:
Answer:
Explanation:
In Microsoft Purview Information Protection, sensitivity labels are the core mechanism to classify and protect content. The Microsoft SCI learning content explains that a sensitivity label can “apply protection such as encryption and rights restrictions to files and emails,” allowing you to define who can access the content and what they can do (view, edit, print, forward). When you configure a label with Encrypt settings, the service uses Azure Rights Management to enforce protection persistently, so the encryption travels with the file wherever it goes.
Labels can also apply content marking. The official guidance states that labels can “add visual markings—headers and footers—to Office files and email to make the sensitivity of content obvious.” This is commonly used to stamp messages and documents with text such as Confidential or Internal. SCI materials further clarify that labels can apply watermarks to Office documents (Word, Excel, PowerPoint) as part of content marking, but watermarks are not applied to email messages; only headers and footers are supported for email.
Putting it together: encryption (Yes) and headers/footers on documents (Yes) are supported label actions. Watermarks are supported for documents but not for email, so “Sensitivity labels can apply watermarks to emails” is No.
Which service includes the Attack simulation training feature?
Options:
Answer:
Microsoft Defender for Cloud Apps
Answer:Microsoft Defender for Office 365
Answer:Microsoft Defender for Identity
Answer:Microsoft Defender for SQL
Answer:BMicrosoft places Attack simulation training under the email and collaboration protection workloads of Microsoft Defender for Office 365 (MDO). The official product guidance describes it as a built-in capability that “lets you run realistic attack scenarios in your organization to identify vulnerable users and train users to recognize and report phishing and other social-engineering techniques.” Microsoft further notes that Attack simulation training “provides editable phishing payloads, credential-harvesting and attachment scenarios, landing pages, user training, and detailed reporting,” enabling security teams to measure compromise rates and improve user resilience over time. The service scope is explicit: “Attack simulation training is a feature of Microsoft Defender for Office 365 Plan 2,” and it is included in suites that contain MDO P2 such as Microsoft 365 E5 and Office 365 E5. In the Microsoft 365 Defender portal, you access it under Email & collaboration → Attack simulation training, where admins can create simulations, target groups, assign training, and review metrics like repeat offenders, resilience score, and simulation results. By design, this feature is not part of Microsoft Defender for Cloud Apps (cloud app security and CASB functions), not part of Microsoft Defender for Identity (on-prem AD identity threat detection), and not part of Defender for SQL. Therefore, the Microsoft SCI documentation aligns that the correct service hosting Attack simulation training is Microsoft Defender for Office 365 (Plan 2).
In the shared responsibility model for an Azure deployment, what is Microsoft solely responsible for managing?
Options:
the management of mobile devices
the permissions for the user data stored in Azure
the creation and management of user accounts
the management of the physical hardware
Answer:
DExplanation:
In Microsoft’s shared responsibility model for Azure, responsibilities are divided between Microsoft and the customer. Microsoft Learn explains that Microsoft is responsible for security of the cloud, while customers are responsible for security in the cloud. The platform owner’s scope includes the underlying facilities and infrastructure. As the documentation states: “Microsoft is responsible for the security OF the cloud, which includes protecting the infrastructure that runs all of the services offered in Microsoft Azure,” and this encompasses “physical datacenters, physical hosts, and the physical network.” The customer, by contrast, is responsible for items within their tenant and workloads, including “data, endpoints, accounts, and access management,” as well as configuration of services, identities, and devices.
Applied to the options given: managing mobile devices (A), setting permissions for user data (B), and creating/managing user accounts (C) fall under the customer’s responsibility because they relate to identity, access, data, and endpoint management within the tenant. The one item that Microsoft solely manages is the physical layer—the “physical hardware and facilities” that host Azure services. Therefore, the correct answer is D. the management of the physical hardware.
Which solution performs security assessments and automatically generates alerts when a vulnerability is found?
Options:
cloud security posture management (CSPM)
DevSecOps
cloud workload protection platform (CWPP)
security information and event management (SIEM)
Answer:
AExplanation:
In Microsoft’s cloud security terminology, Cloud Security Posture Management (CSPM) is the solution specifically designed to perform continuous security assessments of cloud resources and generate alerts when misconfigurations or vulnerabilities are detected. In Microsoft Defender for Cloud, the CSPM capabilities continuously analyze Azure, multi-cloud, and hybrid resources against built-in security benchmarks and regulatory standards. The platform evaluates configurations, detects insecure settings, missing protections, and exposure paths, then raises security recommendations and alerts so administrators can remediate issues that increase risk.
Microsoft’s security and SCI learning content describes CSPM as providing “continuous assessment, visibility, and guidance to improve the security posture of your cloud environment,” including automatic alerting when high-risk issues or vulnerabilities are found. These assessments are mapped to standards and best practices, helping organizations reduce risk proactively instead of waiting for an active attack.
By contrast, DevSecOps is a practice or methodology, not a specific product. A Cloud Workload Protection Platform (CWPP) focuses on runtime protection of workloads such as VMs, containers, and PaaS services. A SIEM solution (like Microsoft Sentinel) ingests and correlates logs and alerts from many sources but does not itself perform the core security posture assessments of cloud configurations. Therefore, the SCI domain clearly aligns this function with CSPM.
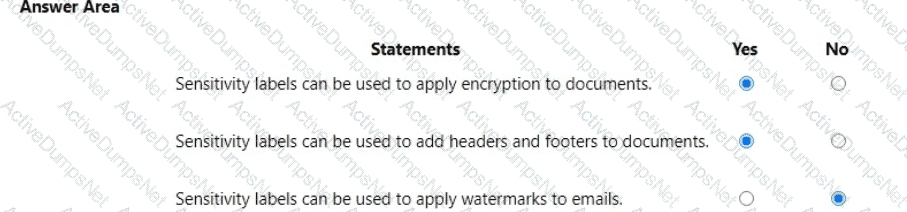
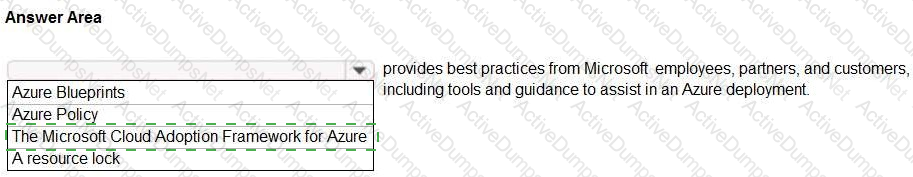
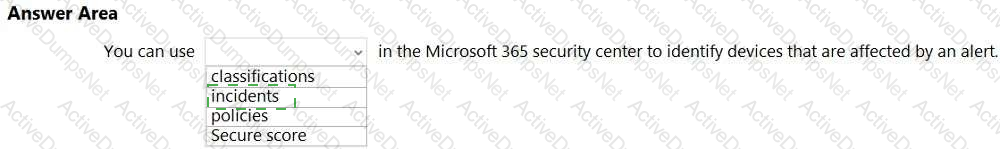
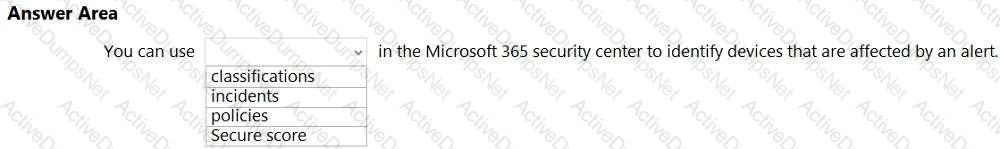
Select the answer that correctly completes the sentence.

Options:
Answer:
Explanation:

In Microsoft’s official guidance, the Microsoft Cloud Adoption Framework for Azure (CAF) is described as the end-to-end approach that “provides best practices, documentation, and tools” to help organizations create and implement business and technology strategies for cloud adoption. The framework aggregates field experience from “Microsoft employees, partners, and customers” and offers prescriptive guidance across strategy, planning, readiness, governance, security, and management to ensure a secure and compliant Azure landing zone. Within SCI-aligned materials, CAF is highlighted as the authoritative body of guidance that helps organizations reduce risk by aligning cloud architecture, identity, security, and compliance controls with Zero Trust principles and regulatory needs. It enables teams to map security baselines, identity governance (e.g., using Microsoft Entra and Conditional Access), and compliance controls (e.g., data protection and regulatory mappings) into deployment blueprints and policy-driven guardrails.
By contrast, Azure Blueprints package artifacts (policies, RBAC, templates) for consistent deployments; Azure Policy enforces and audits configuration through policy definitions; and resource locks prevent accidental modification or deletion. While these are important technical controls, the statement in the question explicitly refers to a body of best practices and guidance that assists an Azure deployment end to end—this is precisely the role of the Microsoft Cloud Adoption Framework for Azure.
What can you use to provision Azure resources across multiple subscriptions in a consistent manner?
Options:
Microsoft Defender for Cloud
Azure Blueprints
Microsoft Sentinel
Azure Policy
Answer:
BExplanation:
Azure Blueprints lets you define a repeatable set of artifacts—like ARM/Bicep templates, role assignments, and Azure Policy—that you can assign to multiple subscriptions to deploy resources and guardrails consistently.
Select the answer that correctly completes the sentence.

Options:
Answer:

When you enable Azure AD Multi-Factor Authentication (MFA), how many factors are required for authentication?
Options:
1
2
3
4
Answer:
BExplanation:
In Microsoft’s Security, Compliance, and Identity (SCI) learning content, Multi-Factor Authentication (MFA) is defined as requiring more than one verification method during sign-in. Microsoft states: “Multi-factor authentication (MFA) requires two or more verification methods” and Azure AD (Microsoft Entra ID) MFA “works by requiring two or more of the following: something you know (password), something you have (trusted device or token), something you are (biometrics).” The SCI fundamentals also explain that MFA strengthens authentication beyond a single password by combining distinct factor types, noting that “strong authentication uses at least two different factors to verify identity.”
When you enable Azure AD MFA, a user must successfully present two factors from those categories to complete the authentication—commonly a password (something you know) plus a second factor such as Microsoft Authenticator approval, a FIDO2 security key, SMS/voice code, or Windows Hello (something you have/are). This is the core of Azure AD’s risk-based and conditional access controls, which can require MFA based on conditions or risk signals. Therefore, the number of factors required after enabling Azure AD MFA is two, aligning with Microsoft’s definition and implementation of multi-factor authentication in Entra ID.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
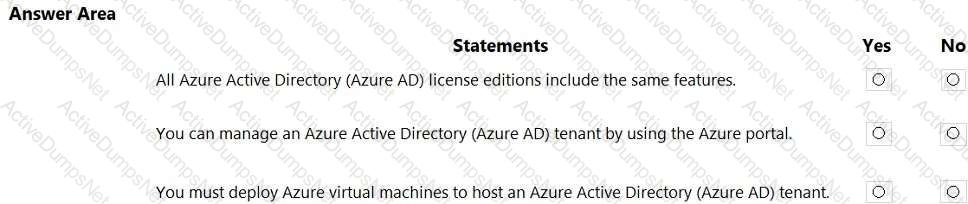
Options:
Answer:
Explanation:
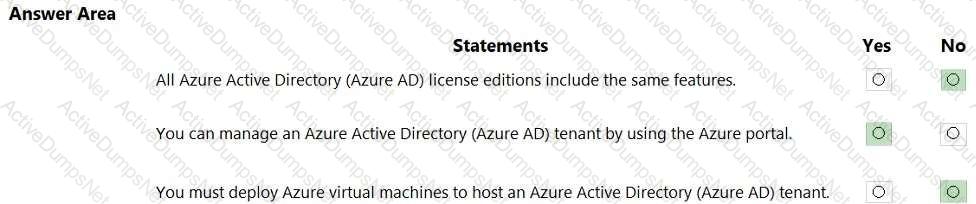
Microsoft Learn explains that Azure Active Directory (now Microsoft Entra ID) is a Microsoft-managed identity and access management service delivered from the cloud. It does not require you to provision or host infrastructure such as virtual machines; the directory is operated as a service by Microsoft, and tenants are created and administered within Microsoft’s cloud environment. The official learning paths further clarify that administration is performed through the Azure portal (the Entra/Microsoft Entra admin center and Azure portal blades), PowerShell, and Graph—so managing a tenant in the Azure portal is fully supported.
Regarding licensing, Microsoft’s SCI study materials detail that Azure AD/Entra ID is offered in multiple editions (Free, Microsoft 365 apps edition, Premium P1, and Premium P2). Each edition unlocks different capabilities: for example, features like Conditional Access are in Premium tiers; Identity Protection and Privileged Identity Management (PIM) are P2 capabilities. Because capabilities vary by tier, the statement that all license editions include the same features is incorrect.
Putting this together: feature parity across editions is not the case (No); tenant management in the Azure portal is supported (Yes); and you do not need to deploy Azure VMs to host an Azure AD/Entra ID tenant (No).
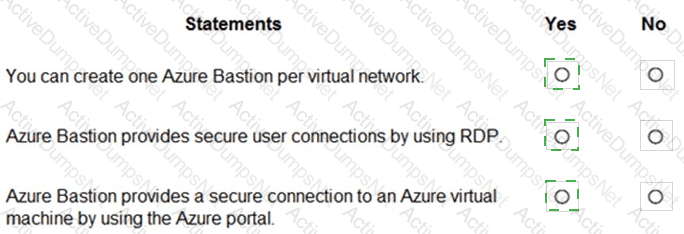
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
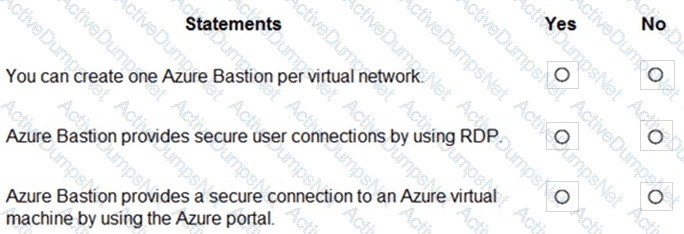
Options:
Answer:

Explanation:
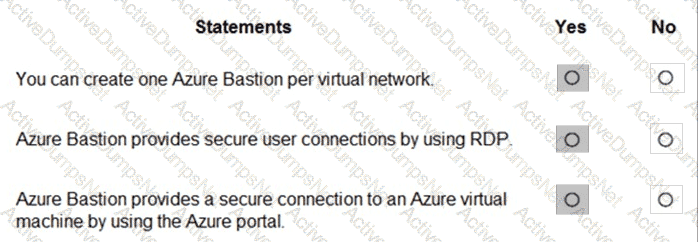
Microsoft documents describe Azure Bastion as a managed PaaS jump-host that’s deployed inside a virtual network to provide secure remote access: “Azure Bastion is deployed in your virtual network and provides seamless RDP and SSH connectivity to your virtual machines directly in the Azure portal over SSL.” The platform design is per-VNet, with the limit stated as: “One Bastion host can be deployed per virtual network,” ensuring a single managed entry point for that network. Connectivity is delivered using the native protocols while avoiding public exposure: “Bastion enables RDP and SSH sessions… without requiring a public IP on your virtual machines, using TLS (port 443).” Access is brokered through the web experience: “You connect to the VM directly from the Azure portal using your browser,” which provides an HTML5 client for RDP/SSH. These statements collectively validate that (1) deployment is one Bastion per VNet, (2) it provides secure user connections by using RDP (and SSH), and (3) it provides a secure connection to an Azure VM via the Azure portal, aligning with Zero Trust principles by eliminating inbound RDP/SSH exposure on public IPs.
Which two types of devices can be managed by using Endpoint data loss prevention (Endpoint DLP)? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
Options:
Windows 11
Linux
iOS
macOS
Android
Answer:
A, DExplanation:
Endpoint data loss prevention (Endpoint DLP), a feature in Microsoft Purview, supports Windows 10 and 11 and now also supports macOS for core DLP capabilities. It allows organizations to monitor and restrict actions like copying sensitive files to USBs, printing, or uploading to unapproved cloud services.
SCI Extract: " Endpoint DLP extends Microsoft Purview Data Loss Prevention to Windows 10, Windows 11, and macOS devices, allowing for monitoring and control of sensitive data usage at the endpoint. "
Other platforms like Linux, iOS, and Android are not currently supported for Endpoint DLP
Select the answer that correctly completes the sentence.
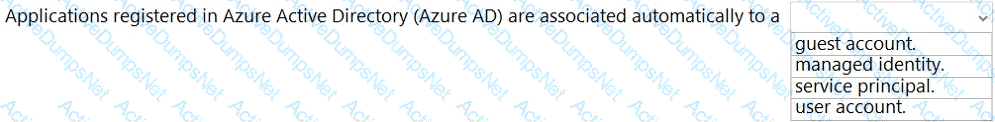
Options:
Answer:

Explanation:
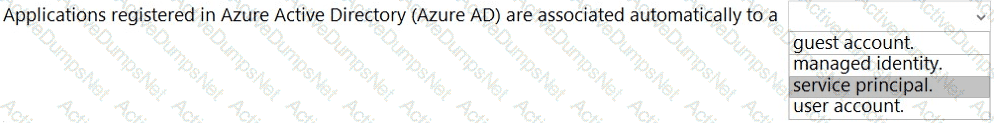
When you register an application through the Azure portal, an application object and service principal are automatically created in your home directory or tenant.
You need to identify which cloud service models place the most responsibility on the customer in a shared responsibility model.
in which order should you list the service models from the most customer responsibility (on the top) to the least customer responsibility (on the bottom)? To answer, move all models from the list of models to the answer area and arrange them in the correct order.
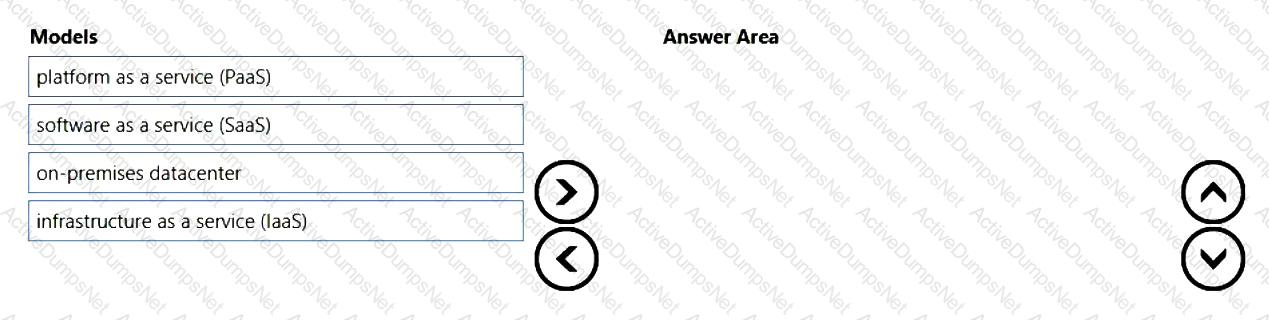
Options:
Answer:

Explanation:
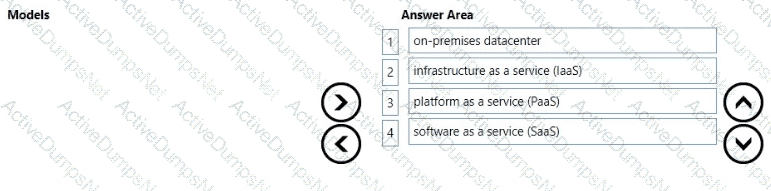
Microsoft’s shared responsibility guidance explains that the customer’s responsibility decreases as you move from on-premises to SaaS. In an on-premises datacenter, “you own the whole stack—applications, data, runtime, middleware, OS, virtualization, servers, storage, and networking.” With IaaS, the cloud provider operates the physical datacenter and virtualization, while “you’re responsible for configuring and managing the guest OS, network controls, identity, applications, and data.” With PaaS, the provider operates more of the stack so that “the cloud provider manages the platform (OS, middleware, and runtime) and you focus on your applications and data.” Finally, with SaaS, responsibility is minimized for customers because “the service provider manages the application and underlying infrastructure; customers primarily manage identity, data, and access/usage.”
These Microsoft Learn statements map directly to the requested order—from most customer responsibility (on-premises) to least (SaaS)—with IaaS and PaaS in between, reflecting the progressive shift of operational and security controls from the customer to the cloud provider as the service model moves up the stack.
What are three uses of Microsoft Cloud App Security? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
Options:
to discover and control the use of shadow IT
to provide secure connections to Azure virtual machines
to protect sensitive information hosted anywhere in the cloud
to provide pass-through authentication to on-premises applications
to prevent data leaks to noncompliant apps and limit access to regulated data
Answer:
A, C, EExplanation:
Microsoft Cloud App Security (now Microsoft Defender for Cloud Apps) is Microsoft’s CASB that “discovers and controls shadow IT,” integrates with identity and endpoint signals, and enforces data protection in SaaS and custom apps. SCI materials describe three core use cases relevant here: (1) Discovery and control of shadow IT by analyzing network logs and app usage, rating risk, and applying governance—matching A. (2) Protect sensitive information hosted anywhere in the cloud via policies such as DLP, information protection label awareness, and integration with apps through API connectors—matching C. (3) Prevent data leaks to noncompliant apps and limit access to regulated data using Conditional Access App Control and session controls that can block download, apply protections, or monitor in real time—matching E. In contrast, secure connections to Azure virtual machines are provided by Azure Bastion, not the CASB (eliminating B), and pass-through authentication to on-premises apps is delivered by Azure AD features such as Azure AD Application Proxy or PTA (not Cloud App Security), eliminating D.
Which Microsoft portal provides information about how Microsoft manages privacy, compliance, and security?
Options:
Microsoft Service Trust Portal
Compliance Manager
Microsoft 365 compliance center
Microsoft Support
Answer:
AExplanation:
The Service Trust Portal is Microsoft’s public-facing portal that centralizes how Microsoft manages privacy, compliance, and security for its cloud services. It provides independent audit reports, compliance guides, data protection resources, and details on Microsoft’s internal controls and practices. It’s the authoritative place to learn how Microsoft meets global, regional, and industry standards.
What can you protect by using the information protection solution in the Microsoft 365 compliance center?
Options:
computers from zero-day exploits
users from phishing attempts
files from malware and viruses
sensitive data from being exposed to unauthorized users
Answer:
DExplanation:
Microsoft Purview Information Protection (in the Microsoft 365 compliance center) enables you to discover, classify, label, and protect sensitive information across emails, documents, and other data stores. Labels and policies can enforce encryption, access restrictions, and visual markings, helping prevent unauthorized disclosure of sensitive data—inside or outside your organization.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point
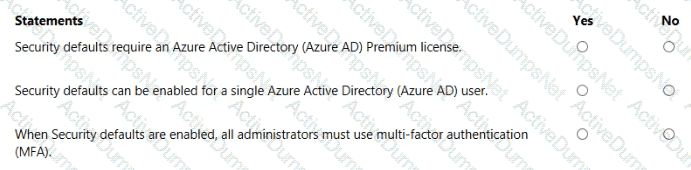
Options:
Answer:

Explanation:
Security defaults require an Azure Active Directory (Azure AD) Premium license. No
Security defaults can be enabled for a single Azure Active Directory (Azure AD) user. No
When Security defaults are enabled, all administrators must use multi-factor authentication (MFA). Yes
Microsoft explains that Security defaults are baseline identity protections that are “available to all tenants at no additional cost” and are intended to “help protect your organization from common identity-related attacks.” They are a tenant-wide setting: Microsoft states that security defaults are “either on or off for the entire tenant” and “can’t be customized or targeted to specific users or groups.” If you require per-user or granular targeting, Microsoft directs customers to use Conditional Access policies instead.
A core behavior of security defaults is enforcing MFA: “All users are required to register for Azure AD Multi-Factor Authentication,” and “administrators are required to perform MFA.” In addition, security defaults “block legacy authentication” and apply other baseline requirements, but they do not enable premium features such as Azure AD Identity Protection or PIM. Summarizing the implications for the statements: no premium license is required; you cannot enable security defaults for just one user because the control is global; and when enabled, administrators must use MFA, with Microsoft recommending exclusion only for a break-glass account if necessary.
Which Microsoft Purview feature allows users to identify content that should be protected?
Options:
Sensitivity Labels
Insider Risks
Data Loss prevention
eDiscovery
Answer:
AExplanation:
In Microsoft Purview, Sensitivity labels are the feature designed to let users identify and classify content that should be protected. Microsoft’s guidance explains that sensitivity labels “enable you to classify and protect your organization ' s data while ensuring that user productivity and collaboration aren ' t hindered.” Users can manually choose a label in Office apps and services to indicate the data’s sensitivity; as Microsoft notes, labels “can be applied by users or automatically,” and the label “persists with the content in its metadata.” Once identified with a label, protection settings can be enforced, including “encryption, content marking (headers, footers, watermarks), and access restrictions based on the label.”
By comparison, Data Loss Prevention (DLP) focuses on “monitoring and blocking the unintentional sharing of sensitive information” based on policy—DLP enforces handling rules after data is identified, rather than providing the user-centric classification mechanism. Insider Risk addresses “risky user activities and insider data security scenarios,” and eDiscovery is used to “find, preserve, collect, and review content for investigations or litigation.” Therefore, the feature that explicitly allows users to identify content that should be protected—by selecting and applying a classification that then drives protection—is Sensitivity labels.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
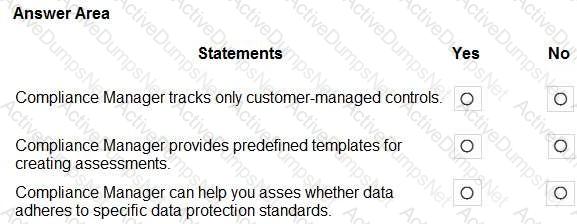
Options:
Answer:

Explanation:
Compliance Manager tracks only customer-managed controls. No
Compliance Manager provides predefined templates for creating assessments. Yes
Compliance Manager can help you assess whether data adheres to specific data protection standards. No
Microsoft Purview Compliance Manager is described as a feature that “helps you manage your organization’s compliance requirements” by giving you assessments, improvement actions, and a compliance score that “measures your progress in completing recommended actions” aligned to regulations and standards. The service does not track only customer-managed controls; Microsoft’s documentation clarifies that Compliance Manager includes “Microsoft-managed controls and customer-managed controls,” and it tracks both within each assessment to show overall posture. It also provides prebuilt (predefined) assessment templates for common regulations and industry standards so organizations can “create assessments from templates” such as GDPR, ISO/IEC 27001, and the Data Protection Baseline.
Importantly, Compliance Manager evaluates control implementation and improvement actions mapped to requirements; it does not scan or classify individual data to determine whether specific data items “adhere” to a standard. Instead, it helps you assess organizational compliance posture by tracking the status of controls, assigning actions, and recording evidence. Thus:
“Tracks only customer-managed controls” → No (it tracks Microsoft-managed and customer-managed).
“Provides predefined templates for creating assessments” → Yes (prebuilt templates are a core feature).
“Helps you assess whether data adheres to specific data protection standards” → No (it measures control/compliance posture, not data-level adherence).
Box 1: No
Compliance Manager tracks Microsoft managed controls, customer-managed controls, and shared controls. Box 2: Yes
Box 3: Yes
What should you use in the Microsoft 365 security center to view security trends and track the protection status of identities?
Options:
Attack simulator
Reports
Hunting
Incidents
Answer:
BExplanation:
In the Microsoft 365 security center/Microsoft 365 Defender portal, the Reports area is designed to provide organization-wide visibility into security posture and activity over time. Microsoft describes the Reports experience as enabling you to “view security trends and track the protection status across identities, endpoints, email & collaboration, and cloud apps.” Within Reports, the Identity section aggregates signals from Microsoft Entra ID protection and related identity defenses so security teams can monitor trends such as risky sign-ins, user risk, MFA adoption/registration, and other identity protection metrics. These curated, read-only dashboards are aimed at measuring protection status and changes over time, helping you validate the impact of controls and prioritize remediation.
By contrast, Attack simulator is used to run user training simulations (e.g., phishing) and is not intended for posture trend reporting. Hunting (Advanced hunting) lets analysts query raw telemetry for investigations, not to provide summarized trend dashboards. Incidents correlates alerts into incident records for triage and response, rather than showing long-term trends and protection status views. Therefore, to view security trends and track the protection status of identities, the correct place is Reports in the Microsoft 365 security center/Microsoft 365 Defender portal.
What feature supports email as a method of authenticating users?
Options:
Microsoft Entra ID Protection
Microsoft Entra Multi-Factor Authentication (MFA)
self-service password reset (SSPR)
Microsoft Entra Password Protection
Answer:
CExplanation:
In Microsoft Entra ID (formerly Azure AD), self-service password reset (SSPR) is the feature that explicitly supports email as an authentication method when users need to verify their identity to reset or unlock their password.
According to Microsoft’s identity and access documentation and the SCI learning content, SSPR lets administrators choose which verification methods are available to users, such as mobile phone, office phone, mobile app, security questions, and email. When email is enabled, a verification code can be sent to a registered alternate email address. The user proves their identity by entering this code, which is treated as an authentication step in the SSPR process.
By contrast:
Microsoft Entra Multi-Factor Authentication (MFA) does not support email as an MFA method; it focuses on methods like authenticator apps, phone calls, and text messages.
Microsoft Entra ID Protection detects and responds to risky sign-ins and users but does not provide email-based authentication.
Microsoft Entra Password Protection deals with banned and compromised passwords, not with email verification.
Therefore, the only option in the list that uses email as a supported authentication method is self-service password reset (SSPR).
What Microsoft Purview feature can use machine learning algorithms to detect and automatically protect sensitive items?
Options:
eDiscovery
Data loss prevention
Information risks
Communication compliance
Answer:
BExplanation:
Microsoft Purview Data Loss Prevention (DLP) is designed to “detect and protect sensitive items” across Microsoft 365 locations, endpoints, and cloud apps. Microsoft explains that Purview DLP policies use sensitive information types, exact data match (EDM), and machine learning–based trainable classifiers to identify content, and then automatically apply protective actions such as blocking or restricting sharing, notifying users with policy tips, auditing, or auto- quarantining/justifying activities. This fulfills the description “use machine learning algorithms to detect and automatically protect sensitive items.” While eDiscovery focuses on legal hold and content discovery, and Communication compliance monitors communications for policy violations (ethics/regulatory scenarios), they are not positioned to broadly and automatically protect sensitive data across services. “Information risks” is not a distinct Purview solution category. Therefore, the Purview capability that leverages machine learning classifiers and automatically enforces protections on sensitive data is Data loss prevention (DLP).
Select the answer that correctly completes the sentence.
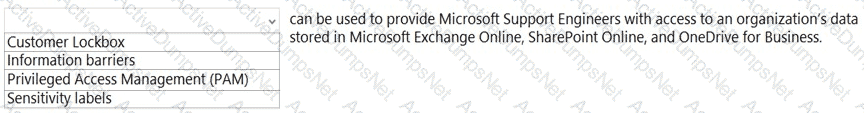
Options:
Answer:

Explanation:
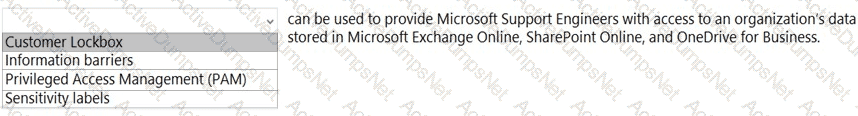
In Microsoft’s Security, Compliance, and Identity materials, Customer Lockbox is described as the feature that controls any Microsoft engineer access to your tenant content during support operations. Microsoft states that Customer Lockbox “ensures that Microsoft cannot access your content to perform a service operation without your explicit approval.” It is specifically applicable to Microsoft 365 workloads that store customer data, including “Exchange Online, SharePoint Online, and OneDrive for Business.” When a support case requires elevated access, “a lockbox request is created and routed to the customer for approval or rejection,” and access is only granted if the organization’s authorized admin approves the request within the defined window. The request contains who is requesting access, the reason, the scope, and the duration, and all actions are audited for compliance reporting. This capability aligns with Microsoft’s zero standing access principles by making engineer access time-bound, least-privileged, and customer-approved. By contrast, Information barriers segregate communications between groups, Privileged Access Management (PAM) governs privileged tasks inside Microsoft 365, and Sensitivity labels classify and protect data. Therefore, the feature that “can be used to provide Microsoft Support Engineers with access to an organization’s data stored in Microsoft Exchange Online, SharePoint Online, and OneDrive for Business” is Customer Lockbox.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
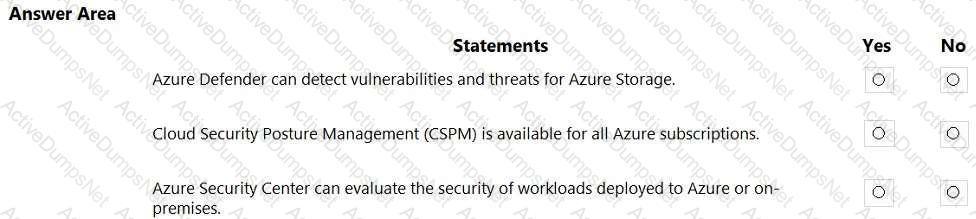
Options:
Answer:

Explanation:
Box 1: Yes
Azure Defender provides security alerts and advanced threat protection for virtual machines, SQL databases, containers, web applications, your network, your storage, and more
Box 2: Yes
Cloud security posture management (CSPM) is available for free to all Azure users.
Box 3: Yes
Azure Security Center is a unified infrastructure security management system that strengthens the security posture of your data centers, and provides advanced threat protection across your hybrid workloads in the cloud - whether they ' re in Azure or not - as well as on premises.
Which score measures an organization ' s progress in completing actions that help reduce risks associated to data protection and regulatory standards?
Options:
Microsoft Secure Score
Productivity Score
Secure score in Azure Security Center
Compliance score
Answer:
DExplanation:
The Compliance score in Microsoft Purview Compliance Manager is a measurement tool that evaluates an organization’s progress toward meeting data protection and regulatory compliance requirements. It is specifically designed to help organizations reduce risks related to data governance, privacy, and compliance with various standards such as GDPR, ISO 27001, NIST 800-53, and Microsoft Data Protection Baselines.
According to Microsoft’s official documentation on Compliance Manager, the Compliance score “helps organizations track, improve, and demonstrate their compliance posture by providing a quantifiable measure of compliance with regulations and standards.” Each action within Compliance Manager contributes a certain number of points to the overall score. These points are weighted based on risk, meaning that actions with a greater impact on reducing compliance risk contribute more significantly to the total score.
The score is not an absolute measure of legal compliance but rather an indicator of progress toward implementing recommended controls and risk-reducing actions. Microsoft emphasizes that Compliance score “assists organizations in identifying areas of improvement, prioritizing compliance tasks, and maintaining an auditable record of their compliance activities.”
By contrast, Microsoft Secure Score measures security posture related to identity, device, and application protection, while Productivity Score evaluates collaboration and technology experience. Thus, the metric that specifically assesses data protection and regulatory compliance progress is the Compliance score in Microsoft Purview Compliance Manager.
You have an Azure subscription that contains a Log Analytics workspace.
You need to onboard Microsoft Sentinel.
What should you do first?
Options:
Create a hunting query.
Correlate alerts into incidents.
Connect to your security sources.
Create a custom detection rule.
Answer:
CExplanation:
Onboarding Microsoft Sentinel starts by enabling Sentinel on an existing Log Analytics workspace and then connecting data sources so analytics can operate on ingested security data. Microsoft’s Sentinel onboarding guidance emphasizes that after you add Sentinel to a workspace, you must “connect Microsoft services, non-Microsoft solutions, and custom sources” using built-in data connectors. Microsoft also states that “you need data in your workspace before you can use Microsoft Sentinel’s analytics, hunting, and investigation capabilities.” Features such as custom analytics rules, hunting queries, and incident correlation depend on ingested telemetry from sources like Microsoft Entra ID sign-in logs, Microsoft 365, Defender products, firewalls, and other appliances. Because the question already gives you a Log Analytics workspace (the prerequisite for enabling Sentinel), the first action in the onboarding workflow that unlocks Sentinel’s value is to connect your security sources. Only after data is flowing should you proceed to create analytics rules, hunting queries, and incident processes. Therefore, the correct first step to onboard Microsoft Sentinel is connect to your security sources.
To which three locations can a data loss prevention (DLP) policy be applied? Each correct answer presents a complete solution.
NOTE: Each correct answer is worth one point.
Options:
Microsoft Exchange Online email
Microsoft OneDrive accounts
Microsoft Exchange Online public folders
Microsoft Teams chat and channel messages
Microsoft Viva Engage
Answer:
A, B, DExplanation:
Microsoft Purview Data Loss Prevention (DLP) defines supported service locations for policy enforcement. The Microsoft Learn/SCI materials state that DLP policies “help protect sensitive information across Microsoft 365 services” and can be scoped to common workloads. In the DLP overview, Microsoft explicitly lists the core cloud locations: “You can create DLP policies that protect content in Exchange Online, SharePoint Online, and OneDrive for Business.” The Teams workload is also included: “DLP can monitor and take protective actions on Microsoft Teams chat and channel messages.” These statements confirm that applying a DLP policy to Exchange Online email (A), OneDrive accounts (B), and Teams chat and channel messages (D) is supported.
By contrast, Exchange Online public folders (C) are not listed among supported DLP locations in the SCI documentation, and Viva Engage (formerly Yammer) (E) is not a standard Microsoft Purview DLP location in the core list above (Viva Engage has separate governance and communication compliance controls). Therefore, from the supported locations enumerated in Microsoft’s DLP guidance, the correct answers are Exchange Online email, OneDrive accounts, and Teams chat and channel messages.
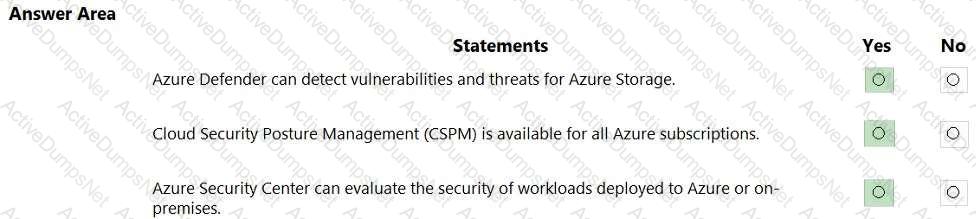
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Options:
Answer:

Explanation:
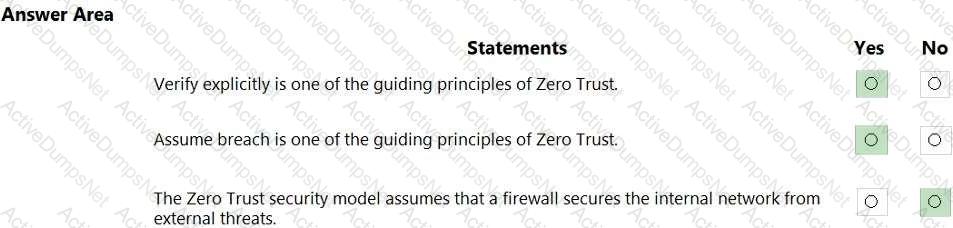
Microsoft’s Zero Trust guidance defines three core principles: “Verify explicitly, use least-privileged access, and assume breach.” In Microsoft’s SCI learning content and Zero Trust overview, the model is described as one that “treats every access attempt as though it originates from an open, untrusted network” and therefore requires explicit verification using all available signals (identity, device health, location, data sensitivity, and anomalies). This directly confirms the first statement as true: Verify explicitly is a guiding principle.
The same guidance states organizations must “assume breach”—designing controls so that if an attacker is already inside, blast radius is minimized through segmentation, Just-In-Time/Just-Enough-Access, continuous monitoring, and rapid detection and response. Microsoft’s Zero Trust materials repeatedly explain to “assume attackers are present” and to “contain and remediate” through defense-in-depth controls, which validates the second statement as true.
Finally, Zero Trust rejects perimeter-based implicit trust. Microsoft clarifies that the model does not rely on a trusted internal network protected by a firewall; instead it “never trusts, always verifies,” continuously enforcing policy regardless of network location (on-premises or internet). Therefore, the statement that Zero Trust assumes a firewall secures the internal network from external threats is false because Zero Trust presumes no inherent safety from being “inside” the network and requires continuous verification and least-privileged access everywhere.
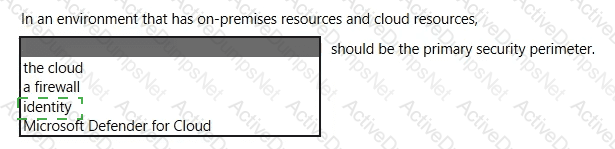
Select the answer that correctly completes the sentence.
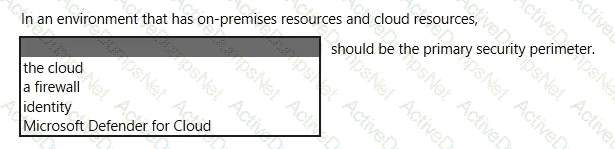
Options:
Answer:

Explanation:
Microsoft’s security guidance for hybrid and cloud environments adopts the Zero Trust approach, which explicitly positions identity as the primary boundary for access decisions. Microsoft states that in modern, distributed environments, “the traditional network perimeter is no longer sufficient” and that identity becomes the new security perimeter for protecting access to resources across on-premises and cloud. In Zero Trust, access is granted based on who the user or workload is, the risk of the sign-in, the device health, and the context of the session. Microsoft summarizes this shift as: “Identity is the control plane,” emphasizing that authentication, authorization, and continuous evaluation of trust are enforced through identity-centric controls such as Conditional Access, multifactor authentication, Privileged Identity Management, device compliance, and session controls.
While tools like firewalls and services such as Microsoft Defender for Cloud remain important layers in a defense-in-depth strategy, they are not the primary perimeter in a hybrid model. Because users, devices, and applications operate from anywhere, identity is the consistent, verifiable layer through which policy is enforced for both on-premises and cloud resources. Therefore, in an environment that spans on-premises and cloud, Microsoft recommends treating identity as the primary security perimeter, applying continuous verification and least-privilege access through identity-driven policies.
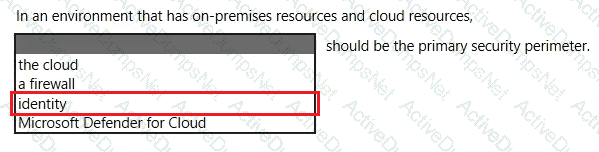
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Options:
Answer:
Explanation:
Microsoft Purview Insider Risk Management is designed to identify, investigate, and act on risky activities by internal users—for example data exfiltration, data theft, policy violations, and user sentiments/signals that may indicate insider risk. SCI documentation explains that Insider Risk policies analyze signals such as file downloads, copying to USB, sharing to personal cloud, printing, or anomalous activity following events like performance warnings or resignation notices. Because it focuses on insider behaviors, it is not used to detect external threat vectors like phishing scams; those are addressed by Microsoft Defender for Office 365 and related anti-phishing protections—hence statement 1 is No. The solution is accessed in the Microsoft Purview (formerly Microsoft 365) compliance center under Insider risk management, where admins configure policies, alerts, and workflows—so statement 2 is Yes. Finally, its core purpose includes detecting and investigating potential data leaks by disgruntled or departing employees, using built-in policy templates (e.g., Data theft by departing employee, Data leaks), making statement 3 Yes.
Which three statements accurately describe the guiding principles of Zero Trust? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
Options:
Define the perimeter by physical locations.
Use identity as the primary security boundary.
Always verity the permissions of a user explicitly.
Always assume that the user system can be breached.
Use the network as the primary security boundary.
Answer:
B, C, DExplanation:
Microsoft’s Zero Trust guidance in the Security, Compliance, and Identity (SCI) materials frames three core principles: “Verify explicitly,” “Use least-privilege access,” and “Assume breach.” The guidance explains that identity is the new control plane in cloud-based environments: identity becomes the primary security boundary, with access decisions evaluated continuously using signals such as user identity, device health, location, and risk. In Zero Trust, organizations must “verify explicitly”—that is, require strong authentication and explicit authorization for every access request, not just initial logon, and base decisions on the permissions and context presented. The model also directs organizations to “assume breach”, operating with the expectation that an attacker may already be inside the environment and therefore applying containment practices such as micro-segmentation, telemetry, and rapid detection and response. Conversely, the traditional notion of defining the perimeter by physical locations or network boundaries is explicitly rejected; the documentation emphasizes that network location is no longer a reliable trust signal and should not be treated as the primary boundary. Therefore, the statements that align with Microsoft’s Zero Trust principles are: Use identity as the primary security boundary (B), Always verify user permissions explicitly (C), and Always assume the user/system can be breached (D).
What is an example of encryption at rest?
Options:
encrypting communications by using a site-to-site VPN
encrypting a virtual machine disk
accessing a website by using an encrypted HTTPS connection
sending an encrypted email
Answer:
BExplanation:
In Microsoft’s SCI guidance, encryption at rest is defined as protecting data when it is stored on a disk or other persistent media. Microsoft describes it as controls that “help safeguard your data to meet your organizational security and compliance commitments by encrypting data when it is persisted,” distinguishing it from protections for data in transit. Within Azure and Microsoft 365, examples include Azure Disk Encryption for IaaS VMs (using BitLocker for Windows and DM-Crypt for Linux), server-side encryption for storage accounts, and Transparent Data Encryption for databases. A virtual machine’s OS and data disks encrypted with BitLocker or DM-Crypt are canonical cases of at-rest encryption because the encryption keys protect the physical media; the data becomes unreadable if the disks are accessed outside the authorized context. By contrast, site-to-site VPN, HTTPS web sessions, and encrypted email protect data in transit—they secure network communications but do not encrypt the data where it is stored. Therefore, among the options provided, encrypting a virtual machine disk is the correct example of encryption at rest in Microsoft’s security model.
For each of the following statement, select Yes if the statement is true Otherwise, select No.
NOTE: Each connect selection a worth one point.
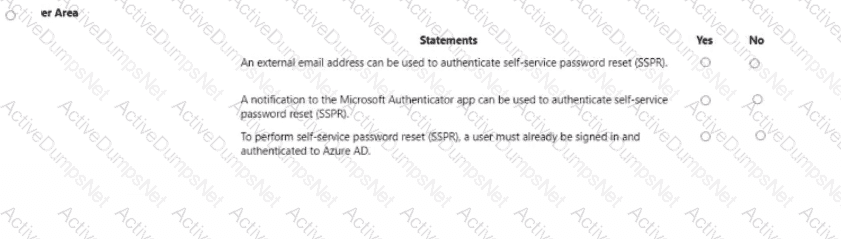
Options:
Answer:

Explanation:
An external email address can be used to authenticate self-service password reset (SSPR). → Yes
A notification to the Microsoft Authenticator app can be used to authenticate self-service password reset (SSPR). → Yes
To perform self-service password reset (SSPR), a user must already be signed in and authenticated to Azure AD. → No
For Microsoft Entra self-service password reset (SSPR), users must register one or more authentication methods that can later be used when they forget their password or are locked out. Microsoft’s end-user guidance states that an email address option lets users configure “an alternate email address that can be used without requiring your forgotten or missing password,” and that this method is available only for password reset. In practice, this alternate address is typically a personal or external email (for example, Gmail), so using an external email to authenticate SSPR is valid.
SSPR can also use the Microsoft Authenticator app as an authentication method. Microsoft documents that Authenticator push notifications, including number matching, are supported for several scenarios, explicitly listing self-service password reset (SSPR) among them. This means a push notification to the app on the user’s device can be used to verify identity during SSPR.
Finally, SSPR is designed for situations where the user cannot sign in. Official SSPR process descriptions explain that users start from the “Can’t access your account?” or password-reset page, provide their username, and then use their registered methods to prove identity. They do not need to be already authenticated to Azure AD; SSPR exists precisely to recover access when sign-in fails.
Which portal contains the solution catalog?
Options:
Microsoft 365 Apps admin center
Microsoft 365 Defender portal
Microsoft 365 admin center
Microsoft Purview compliance portal
Answer:
DExplanation:
In Microsoft’s SCI materials, the Solutions catalog is described as part of the Microsoft Purview experience: “The Microsoft Purview compliance portal is the home for solutions to manage your organization’s data security and compliance needs.” Within this portal, Microsoft states that “the Solutions catalog provides a single place to discover, learn about, and set up Microsoft Purview solutions.” The catalog organizes capabilities across compliance domains, for example “Information Protection, Data Lifecycle Management, Data Loss Prevention, Insider Risk Management, eDiscovery, Audit, and Compliance Manager,” and from the catalog “administrators can open setup guides and configuration wizards for each solution.” This positioning makes the Purview compliance portal the correct portal when you are asked where the solution catalog lives.
By comparison, the Microsoft 365 admin center focuses on tenant administration and licensing, the Microsoft 365 Defender portal consolidates threat protection and security operations, and the Microsoft 365 Apps admin center targets Office app management and servicing. None of these are identified as the home of the Purview Solutions catalog. Therefore, the portal that contains the solution catalog is the Microsoft Purview compliance portal.
Select the answer that correctly completes the sentence.
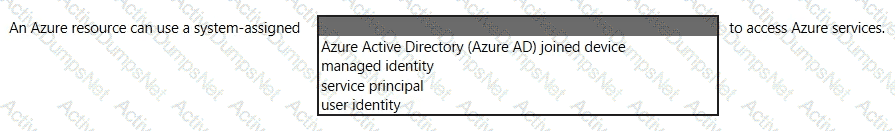
Options:
Answer:

Explanation:
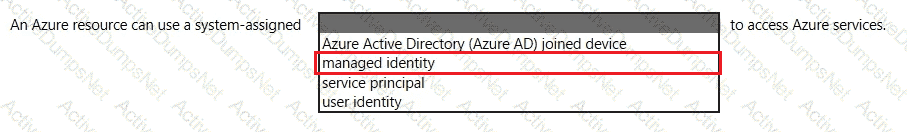
In Microsoft Entra ID (formerly Azure AD), Managed Identities for Azure resources are the built-in way for an Azure resource to authenticate to other Azure services without storing credentials. Microsoft’s documentation states: “Managed identities for Azure resources provide Azure services with an automatically managed identity in Azure Active Directory.” It further distinguishes the two types and clarifies the one used here: “A system-assigned managed identity is enabled directly on an Azure service instance. When enabled, Azure creates an identity for the instance in Azure AD.” Microsoft also emphasizes the lifecycle binding: “This identity is tied to the lifecycle of that service instance and is deleted when the resource is deleted.” Once enabled, the resource can call Azure services by requesting tokens: “You can use this identity to obtain Azure AD tokens for authentication to services that support Azure AD authentication.”
Because the prompt explicitly says “system-assigned”, the correct completion is managed identity. The other options do not match Microsoft’s definition: a user identity refers to a human user; a service principal is the underlying object applications use but isn’t what Azure terms “system-assigned”; and an Azure AD–joined device pertains to device registration, not resource-to-service authentication. Therefore, the sentence correctly reads: “An Azure resource can use a system-assigned managed identity to access Azure services.”
Match the types of Conditional Access signals to the appropriate definitions.
To answer, drag the appropriate Conditional Access signal type from the column on the left to its definition on the right. Each signal type may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
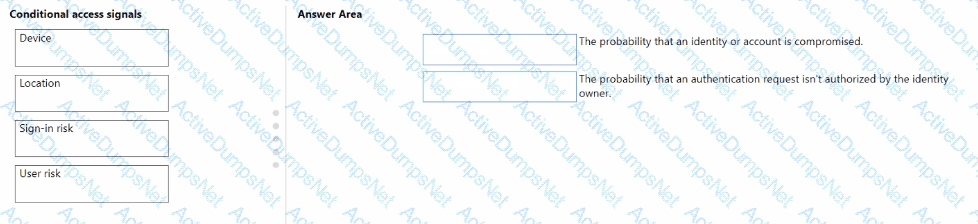
Options:
Answer:

Explanation:
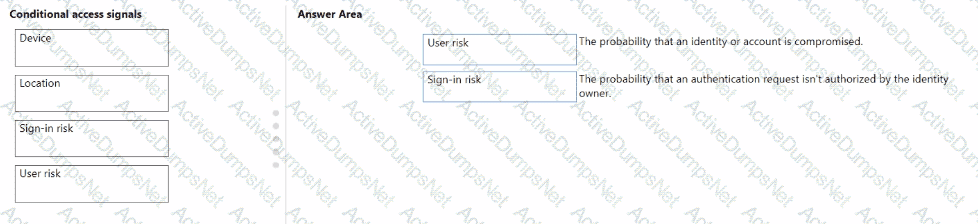
In Microsoft Entra ID Protection, risk-based Conditional Access policies use signals such as User risk and Sign-in risk to evaluate potential threats during authentication and identity usage. These are core to adaptive access and identity protection features taught in Microsoft’s SC-300 and SC-900 learning paths.
User risk:
Defined by Microsoft as: “The probability that a specific identity or account is compromised.”
User risk is assessed based on activities and behaviors that indicate the account may have been compromised—such as leaked credentials or atypical user activity over time.
Sign-in risk:
Defined as: “The probability that the authentication request is not performed by the legitimate identity owner.”
Sign-in risk is calculated at the time of authentication based on indicators such as unfamiliar locations, anonymous IP addresses, impossible travel, or malware-linked sign-ins.
These signals help automate access decisions, such as requiring MFA or blocking access, based on real-time risk assessments.
Select the answer that correctly completes the sentence.
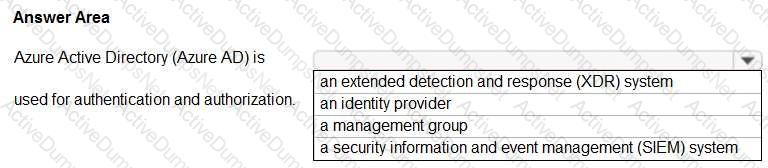
Options:
Answer:
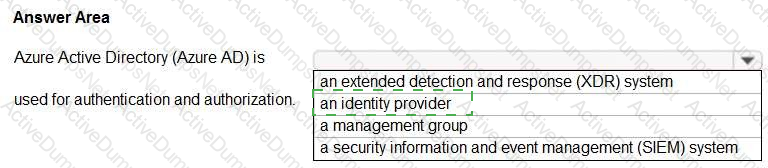
Explanation:
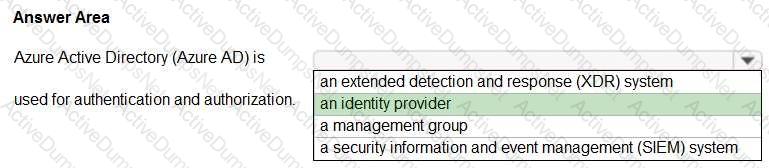
Azure Active Directory (Azure AD) is a cloud-based user identity and authentication service. Reference:
https://docs.microsoft.com/en-us/microsoft-365/enterprise/about-microsoft-365-identity?view=o365-worldwide
Which type of identity is created when you register an application with Active Directory (Azure AD)?
Options:
a user account
a user-assigned managed identity
a system-assigned managed identity
a service principal
Answer:
DExplanation:
When you register an application through the Azure portal, an application object and service principal are automatically created in your home directory or tenant.
Select the answer that correctly completes the sentence.

Options:
Answer:

Explanation:
Azure AD Identity Protection (now part of Microsoft Entra ID) is the Microsoft service that “automates the detection and remediation of identity-based risks.” It continuously evaluates user risk and sign-in risk using signals such as leaked credentials, atypical travel, unfamiliar sign-in properties, and malware-linked IPs. Microsoft documentation clarifies that Identity Protection “uses adaptive machine learning and heuristics to detect risky behaviors and sign-ins” and enables administrators to configure risk-based policies (for example, require MFA or block access) to automatically respond. It also provides rich investigations through risk reports so security teams can triage and remediate compromised identities. This distinctly differs from other Entra capabilities: Privileged Identity Management (PIM) governs just-in-time privileged access and role activation, while MFA is an authentication method enforced by policies. Because the service that specifically detects risk and applies automated protection based on risk is Azure AD Identity Protection, it is the correct completion for the sentence about identity risk detection and remediation.QUESTION NO: 148 HOTSPOT
Select the answer that correctly completes the sentence.
Answer: < map > < m x1= " 491 " x2= " 699 " y1= " 63 " y2= " 79 " ss= " 0 " a= " 0 " / > < /map >
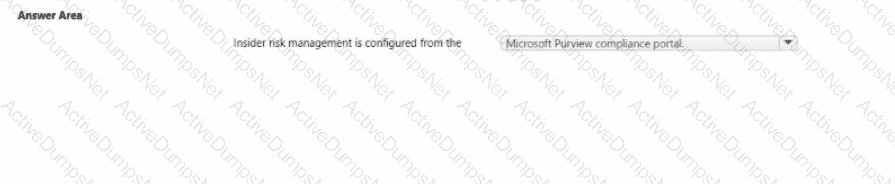
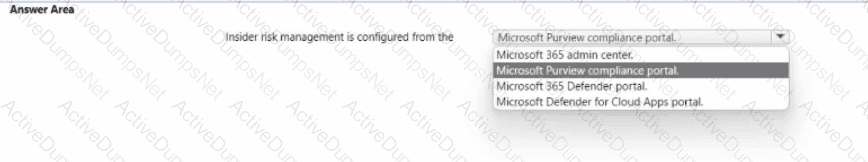
In Microsoft’s SCI guidance, Insider risk management is a Microsoft Purview capability surfaced and administered from the Microsoft Purview compliance portal. The official description states that Insider risk management “helps you minimize internal risks by enabling you to detect, investigate, and act on risky activities in your organization.” Microsoft further clarifies access and configuration by directing admins to “use the Microsoft Purview compliance portal to configure and manage insider risk policies, alerts, and investigations,” and that you can “go to the Microsoft Purview compliance portal and select Insider risk management” to start. These statements place the feature squarely in the compliance plane—not the Microsoft 365 admin center (tenant-wide service management), not the Microsoft 365 Defender portal (threat protection and incident response), and not Microsoft Defender for Cloud Apps (app discovery and cloud app protection). In the SCI learning path, Insider risk is consistently grouped with Microsoft Purview solutions (Information Protection, DLP, eDiscovery, and Audit), emphasizing compliance workflows, risk indicators, policy tuning, and case management. Therefore, the correct completion of the sentence “Insider risk management is configured from the” is the Microsoft Purview compliance portal, where administrators create policies, review alerts, investigate user activity timelines, and take appropriate remediation actions within a compliance-centric experience.
Select the answer that correctly completes the sentence.

Options:
Answer:

Explanation:

In Microsoft’s security portfolio, Microsoft Defender for Cloud is the service that provides cloud workload protection for Azure and hybrid cloud resources. Microsoft describes it as a “cloud-native application protection platform (CNAPP) that helps strengthen the security posture of your cloud resources and protect workloads across multicloud and hybrid environments.” The service delivers Cloud Security Posture Management (CSPM) and Cloud Workload Protection (CWP) by continuously assessing configurations and protecting workloads such as virtual machines, containers, databases, and storage. Documentation further states that Defender for Cloud “provides threat protection for workloads running in Azure, on-premises, and in other clouds,” giving a single pane to harden resources, detect active threats, and remediate.
By contrast, Azure Monitor focuses on telemetry and observability; the Microsoft cloud security benchmark is a set of prescriptive best practices; and Microsoft Secure Score is an aggregate metric reflecting security posture. None of those deliver the workload protection and active defense capabilities (e.g., recommendations, hardening, and threat detection for servers, containers, and PaaS services) that Defender for Cloud offers. Therefore, the sentence correctly completes as: Microsoft Defender for Cloud provides cloud workload protection for Azure and hybrid cloud resources.
Which Microsoft 365 compliance center feature can you use to identify all the documents on a Microsoft SharePoint Online site that contain a specific key word?
Options:
Audit
Compliance Manager
Content Search
Alerts
Answer:
CExplanation:
The Content Search tool in the Security & Compliance Center can be used to quickly find email in Exchange mailboxes, documents in SharePoint sites and OneDrive locations, and instant messaging conversations in Skype for Business.
The first step is to starting using the Content Search tool to choose content locations to search and configure a keyword query to search for specific items.
Which two cards are available in the Microsoft 365 Defender portal? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
Options:
Users at risk
Compliance Score
Devices at risk
Service Health
User Management
Answer:
A, CExplanation:
Microsoft’s SCI learning content describes the Microsoft 365 Defender portal as a unified security operations experience that surfaces security posture and active threats on a card-based dashboard. In the overview of the portal, Microsoft explains that the home page “presents key security information in dashboard cards,” and that among these cards are summaries that highlight risky entities such as “Users at risk” and “Devices at risk.” These cards provide quick, actionable visibility for analysts by aggregating detections and exposure data across Microsoft Defender services (for identities and endpoints). The guidance emphasizes that the portal “correlates signals across identities, endpoints, email, and applications” and that security teams can use the dashboard cards to pivot directly into incidents and investigations from “Users at risk” or “Devices at risk” to take containment or remediation actions.
By contrast, Compliance Score is part of Microsoft Purview Compliance Manager, not the Microsoft 365 Defender portal; Service Health and User Management are functions of the Microsoft 365 admin center. Therefore, the cards you’ll find on the Microsoft 365 Defender portal that match the choices provided are Users at risk and Devices at risk.
You company is evaluating various security products, including a security information and event management (SIEM) solution. You need to provide information about the functionality of SIEM solutions. What is a function of a SIEM solution?
Options:
the ability to review network activity and provide reports about which applications and services can communicate
an alerting system that triggers an alert when users reach their Azure spending limit
the ability to review logs and provide reports about malicious activity
automated incident remediation
Answer:
CWhat can be created in Active Directory Domain Services (AD DS)?
Options:
line-of-business (106) applications that require modem authentication
mob devices
computer accounts
software as a service (SaaS) applications that require modem authentication
Answer:
CExplanation:
In Microsoft’s identity platform, Active Directory Domain Services (AD DS) is the on-premises directory that maintains directory objects such as users, groups, and computers. Microsoft documentation describes AD DS as a service that “stores information about objects on the network and makes this information easy for administrators and users to find and use.” It further explains that AD DS contains objects like “users, groups, computers, and other resources,” and that administrators use tools such as Active Directory Users and Computers to create and manage these objects. A key object type is the computer account; Microsoft states that “a computer that’s joined to a domain has a corresponding computer account object in Active Directory” and that these accounts are created and managed within AD DS to enable secure authentication and authorization for domain-joined devices.
By contrast, mobile devices are typically enrolled and managed through Microsoft Intune/Endpoint Manager and Azure AD device objects, not created in AD DS. Likewise, SaaS applications that require modern authentication integrate with Microsoft Entra ID (Azure AD) using OpenID Connect/OAuth 2.0—not with AD DS. Line-of-business apps that rely on modern authentication are also registered in Entra ID, while AD DS supports traditional Kerberos/NTLM for domain resources. Therefore, among the options provided, the object you can create in AD DS is computer accounts.
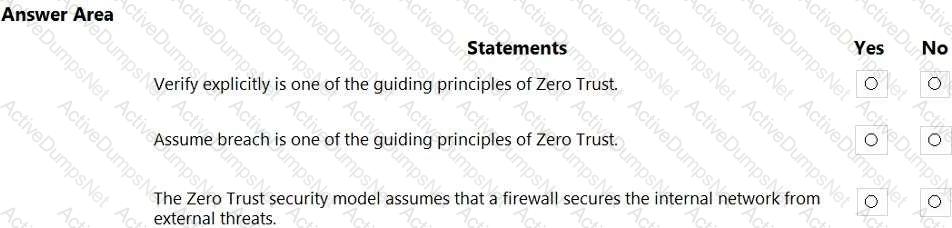
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
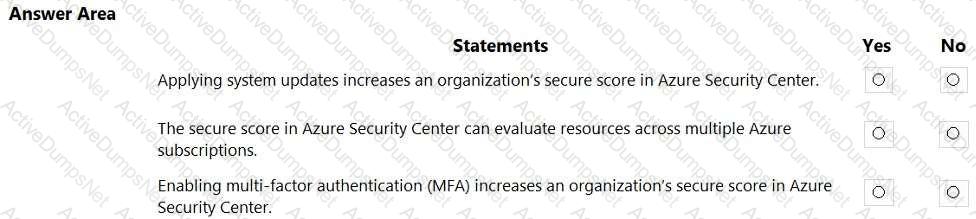
Options:
Answer:

Explanation:
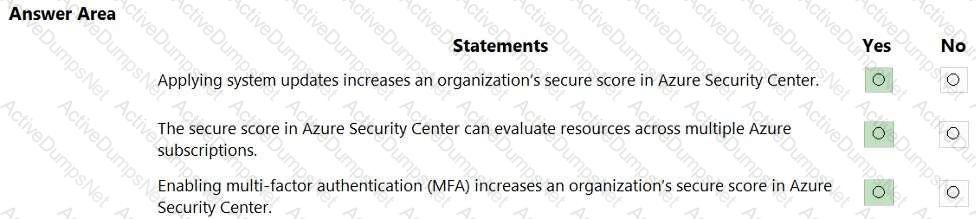
In Microsoft Defender for Cloud (formerly Azure Security Center), Secure score is defined as “a measurement of an organization’s security posture; the higher the score, the lower the identified risk.” Microsoft states that Defender for Cloud provides security recommendations that “help you harden your resources and increase your secure score.” Among these recommendations is “Apply system updates” for virtual machines—Microsoft describes it as ensuring that “machines should have the latest security updates installed”, and completing this action adds points to your secure score because it remediates a vulnerability class (missing patches).
Defender for Cloud also supports wide scope evaluation: you can “view and manage the secure score across subscriptions and management groups,” allowing organizations with multiple Azure subscriptions to see an aggregated and per-scope score and track improvement actions consistently.
Identity protections are part of Defender for Cloud’s recommendations as well. Under the Azure Security Benchmark controls, Defender for Cloud includes the recommendation that “MFA should be enabled on accounts with owner permissions on your subscription.” Implementing this MFA control earns secure-score points because it mitigates high-impact identity risks.
Therefore, applying system updates (Yes), evaluating across multiple subscriptions (Yes), and enabling MFA (Yes) all increase or contribute to an organization’s secure score in Azure Security Center/Defender for Cloud.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point
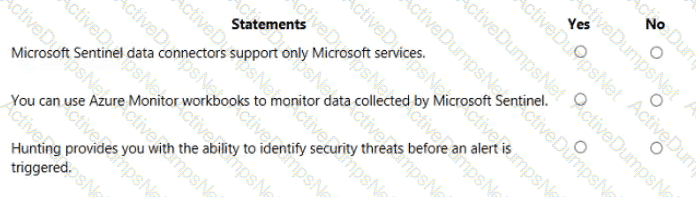
Options:
Answer:
Explanation:
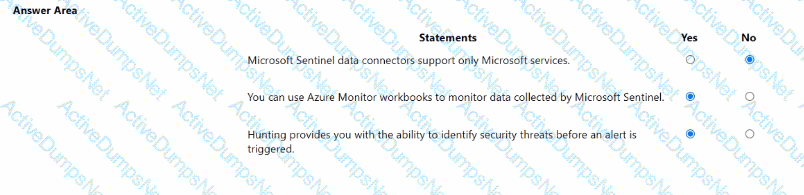
Microsoft states that Microsoft Sentinel includes connectors for both Microsoft and non-Microsoft sources. The product overview explains that Sentinel “comes with built-in connectors” for services such as Microsoft 365, Defender, and Azure sources, and also built-in connectors for non-Microsoft solutions like firewalls and other security products. Therefore, the claim that data connectors support only Microsoft services is false.
For visualization and monitoring, the documentation clarifies that “Microsoft Sentinel uses Azure Monitor workbooks to provide rich visualizations of your data.” Workbooks are the native dashboarding framework in Sentinel and can be customized to monitor logs, incidents, and telemetry that Sentinel ingests. Hence, using Azure Monitor Workbooks to monitor data collected by Sentinel is true.
Regarding threat hunting, Microsoft describes the Hunting capability as a proactive feature: “Hunting lets you proactively hunt for security threats,” using Kusto Query Language queries and analytic patterns to find indicators of compromise before alerts are generated. Analysts can run, save, and schedule hunts to uncover suspicious activity that hasn’t yet raised an alert, making the statement about identifying threats before an alert is triggered true.
Select the answer that correctly completes the sentence.
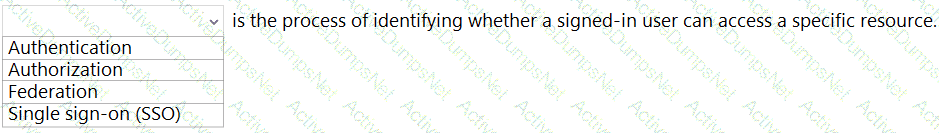
Options:
Answer:
Explanation:
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
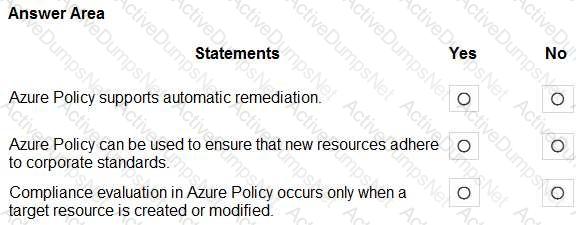
Options:
Answer:

Explanation:
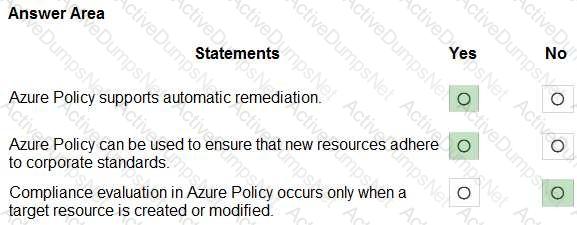
Microsoft’s Security, Compliance, and Identity materials describe Azure Policy as the governance service that lets you “create, assign, and manage policies” so resources “stay compliant with your corporate standards and service level agreements.” Policies are enforced through effects such as Deny, Audit, Append, AuditIfNotExists, DeployIfNotExists, and Modify, which enable organizations to block non-compliant creations, append required settings, or deploy configuration automatically at the time of creation. The documentation further explains that Azure Policy “supports remediation of existing resources” by running remediation tasks for policies that use DeployIfNotExists or Modify, allowing Azure Policy to automatically bring resources into compliance without manual intervention.
Evaluation is continuous, not only at create or update time. Azure Policy “evaluates resources at deployment and regularly re-evaluates compliance,” and admins can also trigger on-demand scans. This means compliance state is updated both when a resource is created/changed and during periodic background assessments, ensuring drift is detected and corrected. Together, these capabilities allow Azure Policy to enforce standards for new resources, auto-remediate existing ones, and provide ongoing compliance posture—which is why the first two statements are Yes, while the claim that evaluation occurs only on create/modify is No.
What are two reasons to deploy multiple virtual networks instead of using just one virtual network? Each correct answer presents a complete solution.
NOTE; Each correct selection is worth one point.
Options:
to separate the resources for budgeting
to meet Governance policies
to isolate the resources
to connect multiple types of resources
Answer:
B, CExplanation:
In Microsoft guidance, network segmentation and isolation are core security principles. Azure virtual networks (VNets) are “a fundamental building block… that enable isolation and segmentation of resources,” and multiple VNets are commonly used to separate environments, business units, or security boundaries. This aligns with Zero Trust and SCI guidance that recommends isolating workloads to reduce blast radius and to apply least privilege and policy-based controls per boundary. Microsoft also emphasizes governance alignment, stating that enterprises should structure Azure resources so that policies, RBAC, and compliance requirements can be applied at appropriate scopes (management group, subscription, resource group, or network boundary). Deploying multiple VNets supports these goals by enabling per-environment policy assignment (for example, dev/test vs. production), differentiated security controls (such as NSGs, ASGs, and firewalls), and independent address spaces to prevent overlap across organizations or regions. Options A and D are not primary drivers: budgeting is handled at subscription/resource group scopes rather than VNet count, and a single VNet can already host and connect many resource types; creating multiple VNets is therefore primarily about governance and isolation that reduce risk and enforce organizational policies.
Select the answer that correctly completes the sentence.
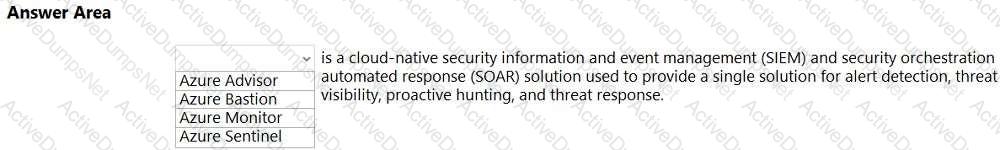
Options:
Answer:

Explanation:
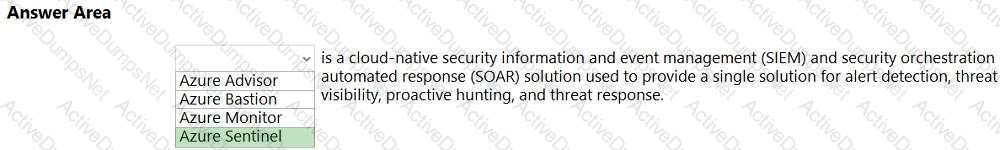
Microsoft Azure Sentinel is a scalable, cloud-native, security information event management (SIEM) and security orchestration automated response (SOAR) solution.
Select the answer that correctly completes the sentence.

Options:
Answer:

Explanation:
Compliance score
In Microsoft Purview Compliance Manager, the Compliance score is the metric that measures an organization’s progress in completing improvement actions that help reduce compliance and data-protection risk. Microsoft describes this score as a quantifiable indicator of your compliance posture across regulatory standards and data-protection baselines. Each recommended improvement action in Compliance Manager is assigned points; completing, testing, and attesting to those actions increases your score. Points are weighted by risk, so implementing controls with greater impact on reducing risk contributes more to the overall score. Microsoft also clarifies that the Compliance score is an operational progress indicator, not a certification or a legal determination of compliance, but it enables organizations to track, prioritize, and demonstrate the implementation of controls across frameworks such as GDPR, ISO/IEC 27001, NIST 800-53, and Microsoft Data Protection Baselines.
By contrast, Microsoft Purview compliance portal reports provide reporting and insights (for example, DLP, Insider Risk, Audit) but do not calculate a unified risk-reduction progress metric. The Trust Center is Microsoft’s public site for transparency about security, privacy, and compliance commitments, and Trust Documents (auditor reports, certifications, and white papers) supply evidence and reference materials. Neither of these provide an in-product, points-based measure of progress—Compliance score does.
Which two tasks can you implement by using data loss prevention (DLP) policies in Microsoft 365? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
Options:
Display policy tips to users who are about to violate your organization’s policies.
Enable disk encryption on endpoints.
Protect documents in Microsoft OneDrive that contain sensitive information.
Apply security baselines to devices.
Answer:
A, CExplanation:
Microsoft Purview Data Loss Prevention (DLP) is designed to prevent the inadvertent or inappropriate sharing of sensitive data across Microsoft 365 services. Microsoft’s guidance states that DLP “helps you discover, monitor, and protect sensitive items across Microsoft 365,” and that with DLP policies you can “identify, monitor, and automatically protect sensitive items in Exchange Online, SharePoint Online, OneDrive for Business, and Microsoft Teams.” This directly supports option C, because DLP can detect sensitive info in OneDrive documents and automatically apply protective actions such as blocking external sharing, restricting access, or auditing the event.
DLP also provides end-user coaching through policy tips: “Policy tips are informative notices that appear when users are working with content that contains sensitive info … to help prevent data loss.” When a user is about to send or share sensitive data in violation of policy, these tips surface in Outlook and Office apps (including when files are stored in SharePoint/OneDrive), aligning with option A.
By contrast, enabling disk encryption (e.g., BitLocker) and applying device security baselines are endpoint/device management tasks handled through Microsoft Intune or Group Policy—not by DLP. Therefore, A and C are the correct tasks you can implement with Microsoft 365 DLP policies.
Which feature provides the extended detection and response (XDR) capability of Azure Sentinel?
Options:
integration with the Microsoft 365 compliance center
support for threat hunting
integration with Microsoft 365 Defender
support for Azure Monitor Workbooks
Answer:
CExplanation:
Microsoft positions Microsoft Sentinel as a cloud-native SIEM and SOAR that “collects data at cloud scale” and “detects, investigates, and responds to threats.” The extended detection and response (XDR) layer in Microsoft’s security stack is delivered by Microsoft 365 Defender, which “correlates signals across endpoints, identities, email, and apps to automatically detect, investigate, and remediate attacks.” Sentinel’s XDR capability is realized through its integration with Microsoft 365 Defender, enabling incident synchronization, alert enrichment, and bi- directional actions. Documentation explains that this integration “brings Microsoft 365 Defender incidents into Microsoft Sentinel,” unifying SIEM/SOAR analytics with the cross-domain XDR detections from Defender. Features such as automatic incident grouping, advanced hunting, and entity behavior flow from Microsoft 365 Defender to Sentinel, giving analysts an end-to-end XDR view. By contrast, threat hunting and workbooks are valuable Sentinel features, and compliance center is unrelated to XDR. The specific capability that provides Sentinel’s XDR experience is its integration with Microsoft 365 Defender.
Select the answer that correctly completes the sentence.

Options:
Answer:

Explanation:
Assessments
In Microsoft Purview Compliance Manager, assessments are the core components used to track compliance with groupings of controls from specific regulations, standards, or requirements.
According to official Microsoft Security, Compliance, and Identity (SCI) learning content, particularly within the SC-400 and SC-900 certification tracks, the role of assessments is explicitly defined as:
“Assessments in Compliance Manager help you track, implement, and improve compliance with requirements from standards and regulations. Each assessment maps to a specific regulation or control framework, such as ISO 27001, NIST, GDPR, or HIPAA, and includes a set of controls and recommended improvement actions.”
Further extracted content from SCI documentation confirms:
“An assessment is used to measure your compliance posture against a particular regulation or standard. It includes control mappings and provides insight into what’s in place and what still needs to be addressed to meet the compliance goals.”
The other options in the dropdown — Templates, Improvement actions, and Solutions — serve different functions:
Templates provide a blueprint for creating assessments.
Improvement actions are actionable steps generated within assessments.
Solutions in Microsoft Purview refer to bundled capabilities like Insider Risk Management, Information Protection, etc.
Therefore, to track compliance with groupings of controls from a specific regulation or requirement, the correct and Microsoft-verified term is " Assessments. "
Microsoft 365 Endpoint data loss prevention (Endpoint DLP) can be used on which operating systems?
Options:
Windows 10 and newer only
Windows 10 and newer and Android only
Windows 10 and newer and macOS only
Windows 10 and newer, Android, and macOS
Answer:
CExplanation:
Microsoft 365 Endpoint Data Loss Prevention (Endpoint DLP) extends DLP controls directly to supported desktops. Microsoft states: “Endpoint DLP extends the activity monitoring and protection capabilities of DLP to Windows 10 (and later) devices.” The platform coverage is explicitly broadened to Apple desktops: “Endpoint DLP for macOS enables the same set of DLP capabilities on macOS devices (supported versions) so you can monitor and protect sensitive items across Windows and Mac endpoints.” At the same time, Microsoft clarifies the mobile scope: “Endpoint DLP is supported on Windows and macOS devices.” This means Android is not a supported operating system for Endpoint DLP (mobile data protection on Android uses different controls such as app protection policies via Microsoft Intune and conditional access). Therefore, the correct pairing of operating systems for Endpoint DLP support is Windows 10 and newer, and macOS—not Android. This aligns with Microsoft’s Endpoint DLP platform support guidance and the intended desktop-focused endpoint protections for activities such as file copy, print, upload, and removable media interactions.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
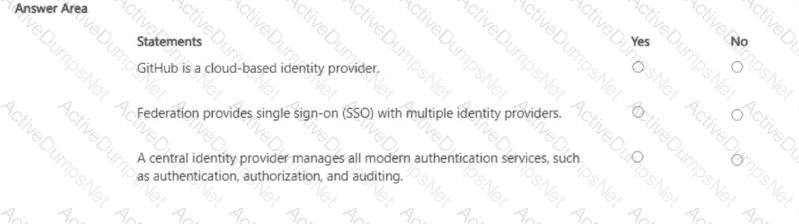
Options:
Answer:

Explanation:
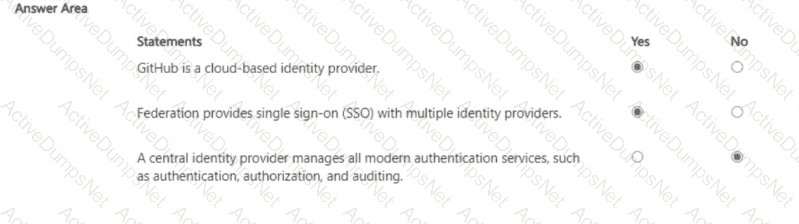
Microsoft’s identity guidance classifies social identity services (e.g., GitHub, Google, Facebook) as cloud-based identity providers that can be used for external identities with Microsoft Entra ID. In this model, GitHub functions as an IdP using OAuth/OpenID Connect to authenticate users and issue tokens that applications or Entra ID can accept. Federation in Microsoft terms is the trust relationship that allows SSO across organizational boundaries and with multiple identity providers, such as Active Directory Federation Services (AD FS), SAML, or OpenID Connect providers, so users can authenticate once and access multiple apps without repeated sign-ins.
Crucially, SCI materials distinguish roles: an identity provider primarily handles authentication (proving who the user is and issuing claims/tokens). Authorization—deciding what the user can do—is enforced by the application or resource (often using roles/claims from the IdP). Auditing spans multiple planes: the IdP provides sign-in and audit logs, while applications and other services maintain their own activity logs. Therefore, it is incorrect to say a central IdP “manages all modern authentication services” including authorization and auditing; those responsibilities are shared across the identity platform and the relying applications/resources.
Select the answer that correctly completes the sentence.
Options:
Answer:

Explanation:
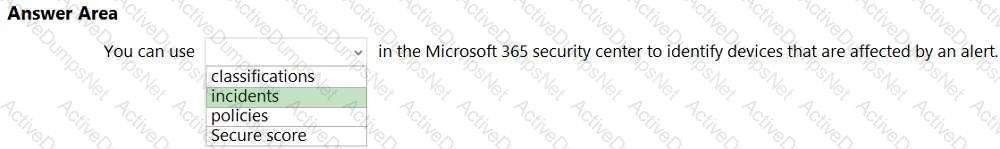
In the Microsoft 365 security center (now Microsoft 365 Defender), incidents are used to triage and investigate threats across the tenant. Microsoft’s security documentation explains that “an incident is a collection of related alerts” that are automatically correlated to give analysts a single, end-to-end view of an attack. Within each incident, the portal surfaces impacted assets such as devices, users, mailboxes, and applications, enabling responders to quickly identify which endpoints are affected by a given alert and to take response actions (isolate device, collect investigation package, run AV scan, etc.). This design allows security teams to move beyond individual alerts and instead work a consolidated investigation that lists affected devices in the incident’s Evidence & Response/Assets sections, complete with alert timelines and device details.
By comparison, Secure Score measures the organization’s security posture and recommendations; policies are configuration/enforcement objects (e.g., Defender or compliance policies) and are not the investigative view for alerts; classifications relate to information protection labeling rather than alert investigation. Therefore, to identify devices that are affected by an alert, you use the Incidents experience in Microsoft 365 Defender, where correlated alerts show the devices involved alongside the entities and evidence connected to the threat.
Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
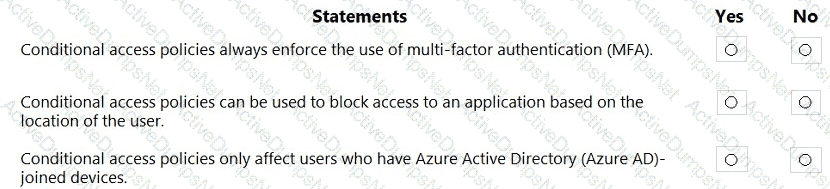
Options:
Answer:

Explanation:
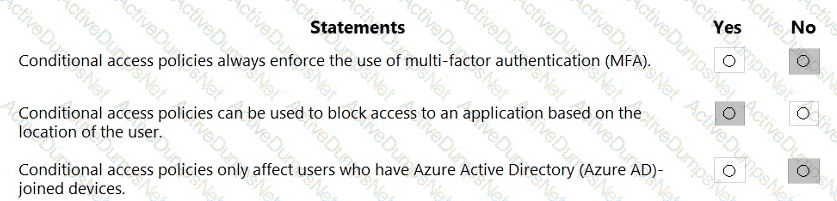
Microsoft Entra Conditional Access evaluates signals to make real-time access decisions. Microsoft describes it as bringing “signals together to make decisions and enforce organizational policies,” where administrators choose controls such as Block access, Require multi-factor authentication, Require device to be marked as compliant, or Require hybrid Azure AD joined device. Because MFA is only one of several grant controls, it is incorrect that policies always enforce MFA; they can also simply block, allow, or require other conditions.
Location is a first-class condition. Microsoft states you can define named locations (by countries/regions or IP ranges) and then use them in policy conditions to block or grant access. A common scenario is “Block access from specific locations” or require additional controls when a sign-in originates from an untrusted network. Therefore, Conditional Access can block access to an application based on user location.
Finally, Conditional Access targets users, groups, workload identities, and cloud apps regardless of device join state. Device-related conditions and filters are optional; policies are not limited to “Azure AD-joined devices.” Controls like Require device to be marked as compliant or Require Hybrid Azure AD joined device are only enforced if configured. Hence, Conditional Access does not only affect users on Azure AD-joined devices.
What should you create to search and export content preserved in an eDiscovery hold?
Options:
a Microsoft SharePoint Online site
a case
a Microsoft Exchange Online public folder
Azure Files
Answer:
BExplanation:
In Microsoft Purview eDiscovery, to search, preserve, analyze, and export content, you must first create a case. A case acts as a container for all eDiscovery activities, including placing users and content locations on litigation hold, running content searches, and exporting results for legal or compliance review.
SCI Extract: " Cases are used in Microsoft Purview eDiscovery (Standard and Premium) to manage, organize, and execute the various tasks associated with identifying and delivering content during an investigation or litigation. "
Select the answer that correctly completes the sentence.
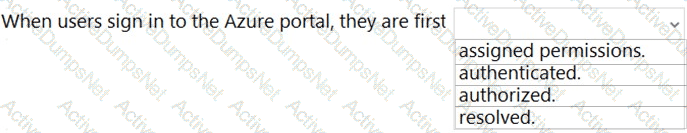
Options:
Answer:
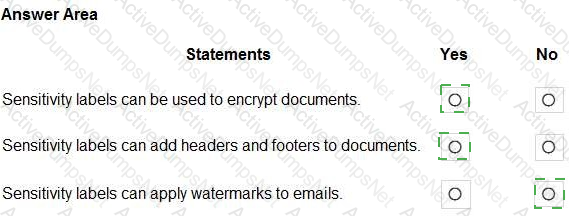
Explanation:
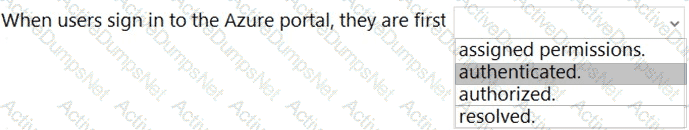
In Microsoft cloud identity, access to Azure resources follows the classical order of authenticate, then authorize. Microsoft Learn defines the two steps clearly: “Authentication is the process of establishing the identity of a person or service,” while “Authorization is the process of determining what a person or service can do.” In an Azure sign-in, Microsoft Entra ID (formerly Azure AD) first validates the user’s credentials (password, MFA, Conditional Access, device compliance, risk evaluation). Upon success, a security token is issued that proves the user’s identity. Only after this identity is established does Azure proceed to authorization, where the Azure Resource Manager evaluates role-based access control (RBAC) assignments to decide what actions are allowed. SCI guidance emphasizes this sequence for Zero Trust: “Verify explicitly” (authenticate with strong signals) and then “use least privilege access” (authorize by RBAC or Privileged Identity Management). Therefore, when users sign in to the Azure portal, the first step is authentication—verifying who they are. The subsequent step is authorization, which determines what resources and operations they can access based on roles, scope, and policy. This ordering underpins secure identity and access management across Microsoft 365 and Azure.
Which Azure Active Directory (Azure AD) feature can you use to evaluate group membership and automatically remove users that no longer require membership in a group?
Options:
access reviews
managed identities
conditional access policies
Azure AD Identity Protection
Answer:
AExplanation:
Explanation
Azure Active Directory (Azure AD) access reviews enable organizations to efficiently manage group memberships, access to enterprise applications, and role assignments.
In a Core eDiscovery workflow, what should you do before you can search for content?
Options:
Create an eDiscovery hold.
Run Express Analysis.
Configure attorney-client privilege detection.
Export and download results.
Answer:
AExplanation:
In the Core eDiscovery (Microsoft Purview) workflow, you first create a case, add case members, and then (typically) apply eDiscovery holds to relevant locations to preserve potentially responsive content before you run searches. While a hold isn’t strictly required to execute a search, Microsoft’s documented workflow shows holds occur prior to creating and running content searches so that items aren’t altered or deleted during the investigation. After holds, you create searches, review, and export.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
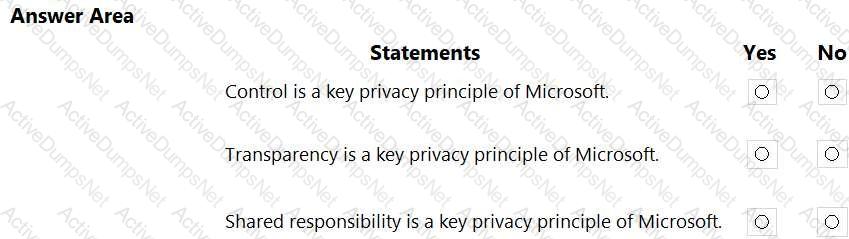
Options:
Answer:

Explanation:
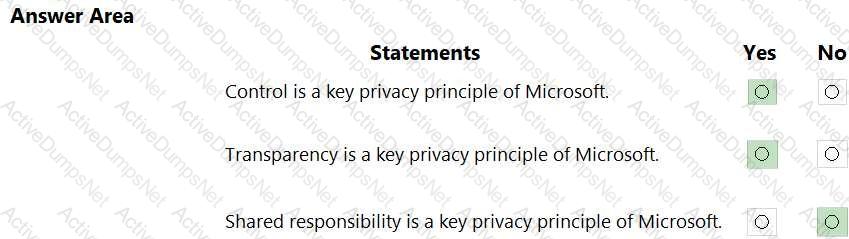
Microsoft sets out clear privacy principles for Microsoft 365 and Microsoft cloud services. In Microsoft’s privacy commitments, Microsoft states that customers control their data: “You control your data.” Microsoft also pledges transparency about data practices: “We are transparent about data collection and use.” These two commitments are among the core privacy principles articulated across Microsoft 365 privacy and Microsoft Purview documentation, which emphasize customer choice, clear explanations of data processing, and admin capabilities to access, export, and delete data. Additional Microsoft privacy principles often listed alongside these include security of your data, strong legal protections, no content-based targeting, and benefits to you, but the key point for this question is that Control and Transparency are explicitly called out as privacy principles.
By contrast, shared responsibility is not a privacy principle; it is a cloud security model used in Azure/Microsoft cloud guidance. That model explains that security is a shared responsibility between Microsoft (for the cloud infrastructure) and the customer (for their data, identities, endpoints, and configurations). It describes how duties are divided for protecting services and workloads, not a privacy promise to end users. Therefore, the correct selections are Yes for Control and Transparency, and No for Shared responsibility.
Unlock SC-900 Features
- SC-900 All Real Exam Questions
- SC-900 Exam easy to use and print PDF format
- Download Free SC-900 Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet
Questions & Answers PDF Demo
- SC-900 All Real Exam Questions
- SC-900 Exam easy to use and print PDF format
- Download Free SC-900 Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet
