Microsoft AZ-500 Microsoft Azure Security Technologies Exam Practice Test
Microsoft Azure Security Technologies Questions and Answers
You need to ensure that users can access VM0. The solution must meet the platform protection requirements.
What should you do?
You need to meet the identity and access requirements for Group1.
What should you do?
You need to ensure that you can meet the security operations requirements.
What should you do first?
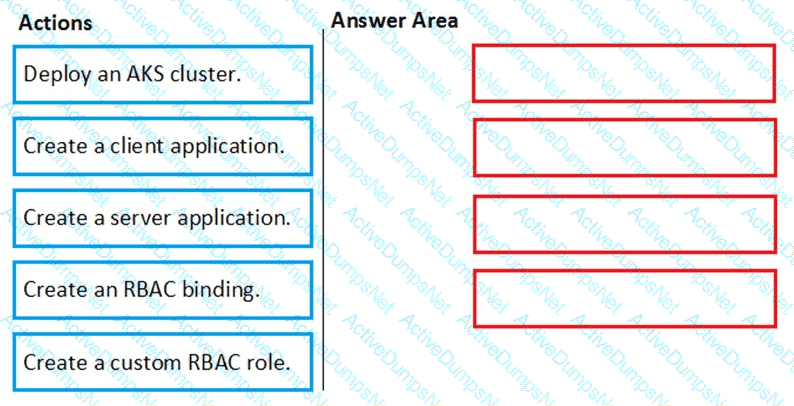
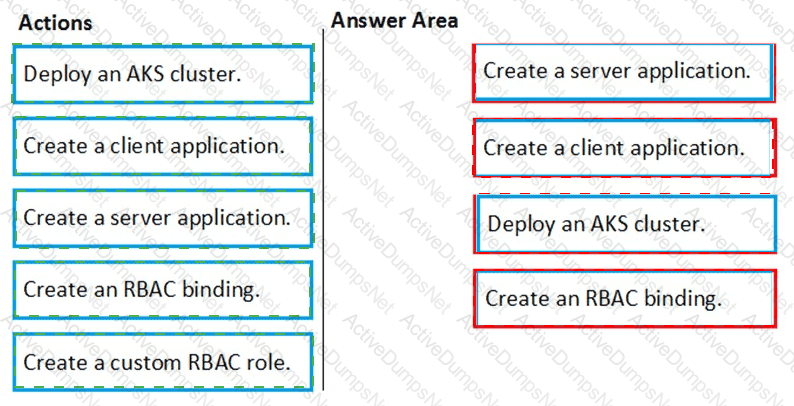
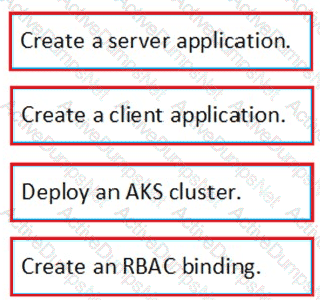
You need to deploy AKS1 to meet the platform protection requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
NOTE: More than one order of answer choices is correct. You will receive credit for any of the correct orders you select.
You need to deploy Microsoft Antimalware to meet the platform protection requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to configure WebApp1 to meet the data and application requirements.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
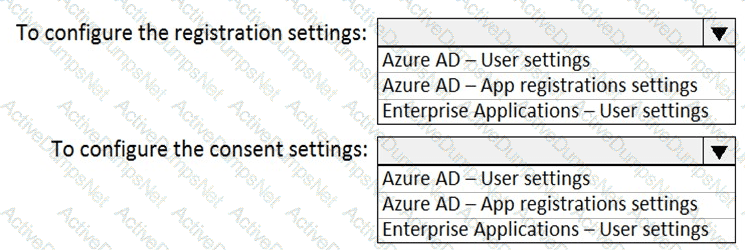
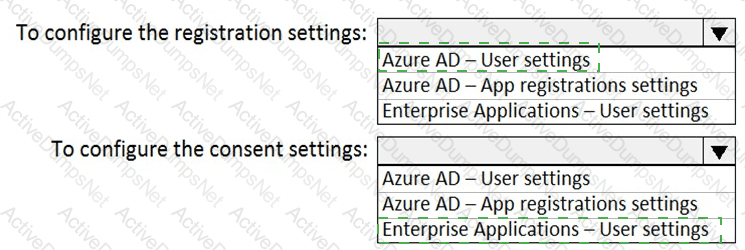
You need to ensure that the Azure AD application registration and consent configurations meet the identity and access requirements.
What should you use in the Azure portal? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
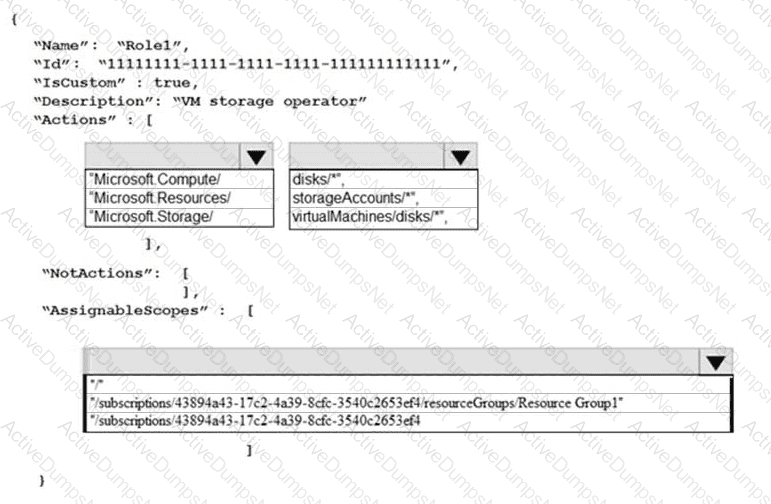
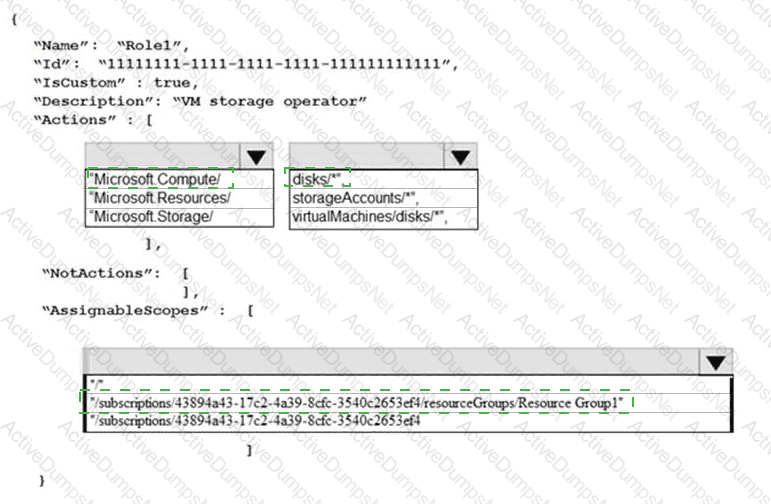
You need to create Role1 to meet the platform protection requirements.
How should you complete the role definition of Role1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
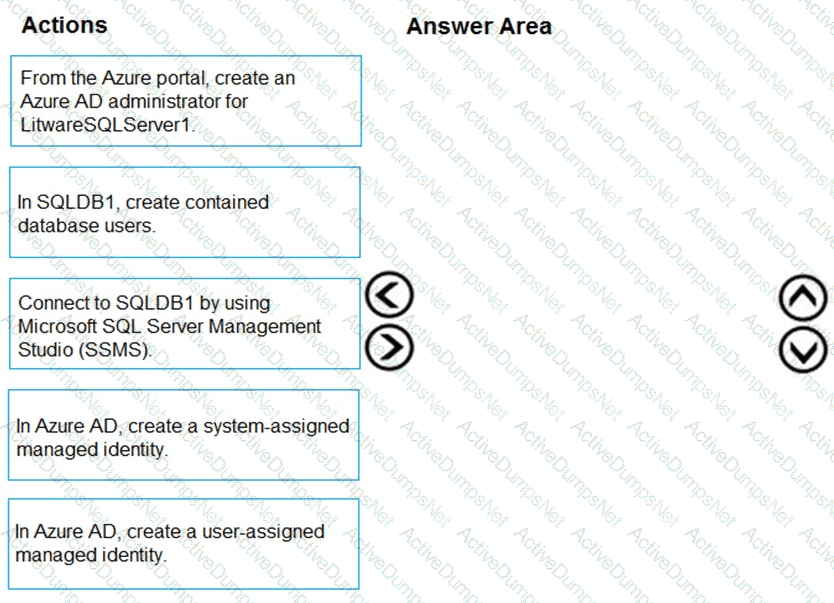
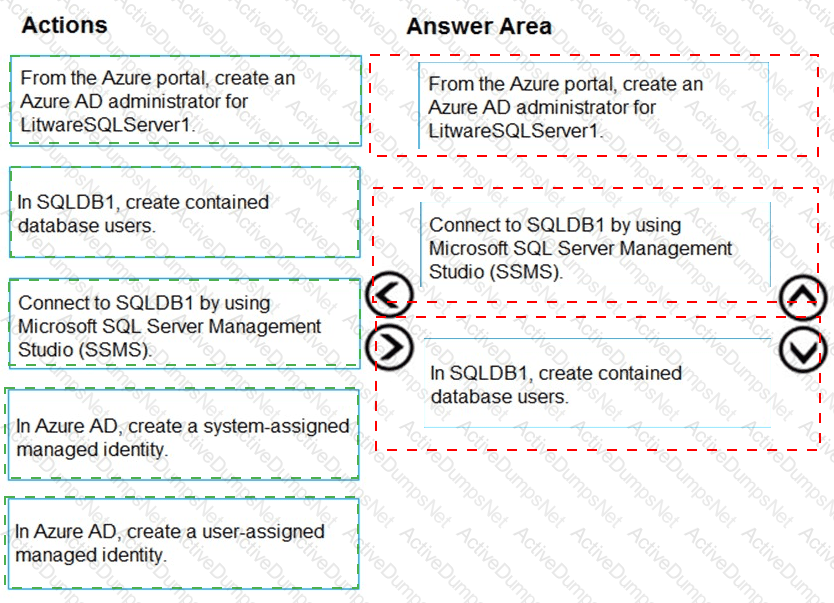
You need to configure SQLDB1 to meet the data and application requirements.
Which three actions should you recommend be performed in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You implement the planned changes for the key vaults.
To which key vaults can you restore AKV1 backups?
You need to implement the planned change for SQLdb1.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You need to implement the planned change for WAF1.
The solution must minimize administrative effort
What should you do?
You need to delegate a user to implement the planned change for Defender for Cloud.
The solution must follow the principle of least privilege.
Which user should you choose?
You need to implement the planned change for VM1 to access storage1.
The solution must meet the technical requirements.
What should you do first?
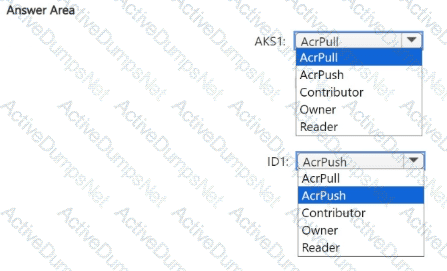
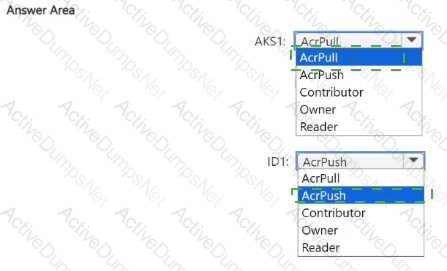
You need to configure the AKS1 and ID1 managed identities to meet the technical requirements. The solution must follow the principle of least privilege.
Which role should you assign to each identity? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
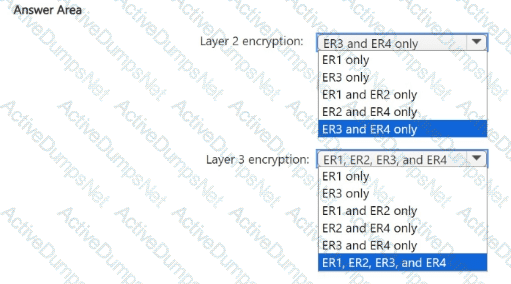
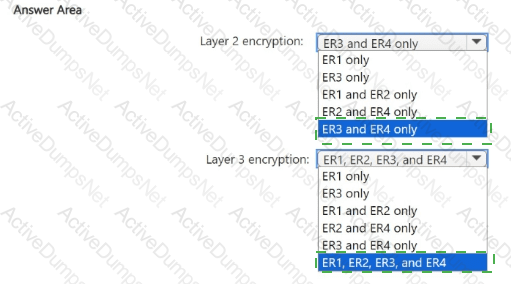
You need to recommend an encryption solution for the planned ExpressRoute implementation. The solution must meet the technical requirements.
Which ExpressRoute circuit should you recommend for each type of encryption? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
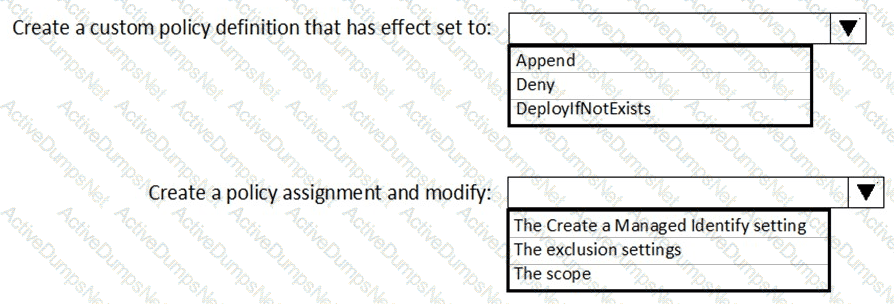
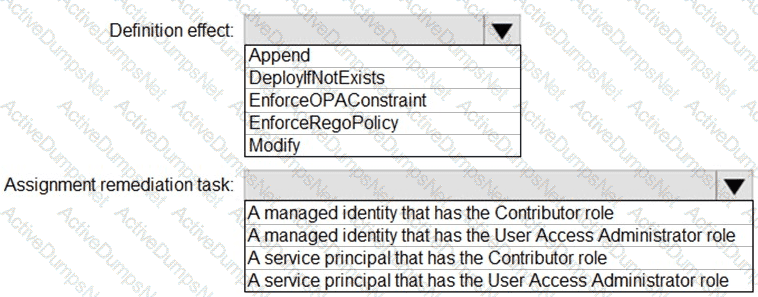
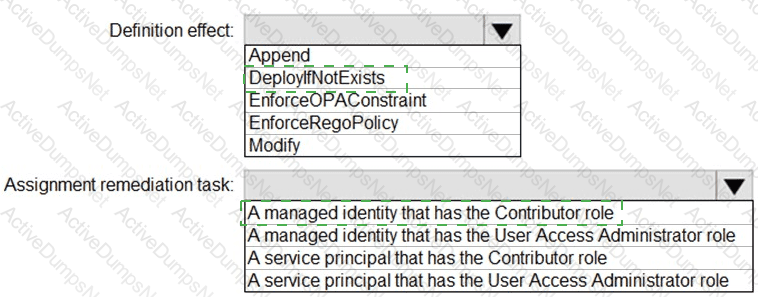
You have an Azure subscription.
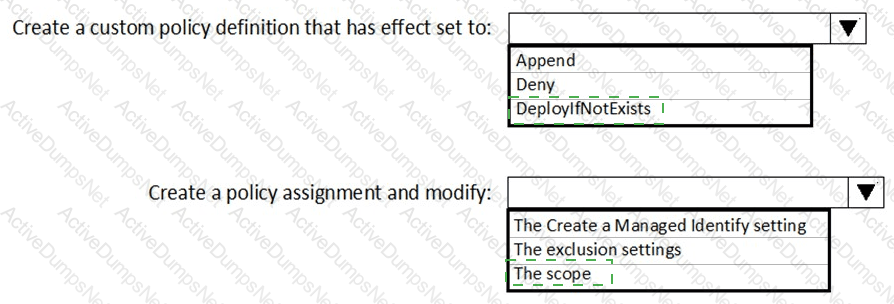
You need to create and deploy an Azure policy that meets the following requirements:
When a new virtual machine is deployed, automatically install a custom security extension.
Trigger an autogenerated remediation task for non-compliant virtual machines to install the extension.
What should you include in the policy? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
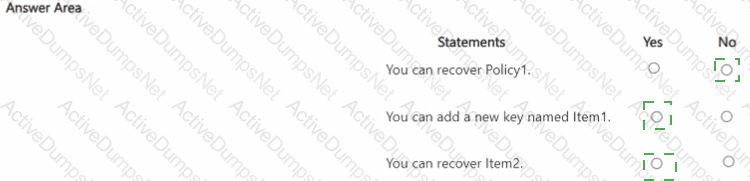
You have an Azure key vault named sk2311 configured as shown in the following exhibit.
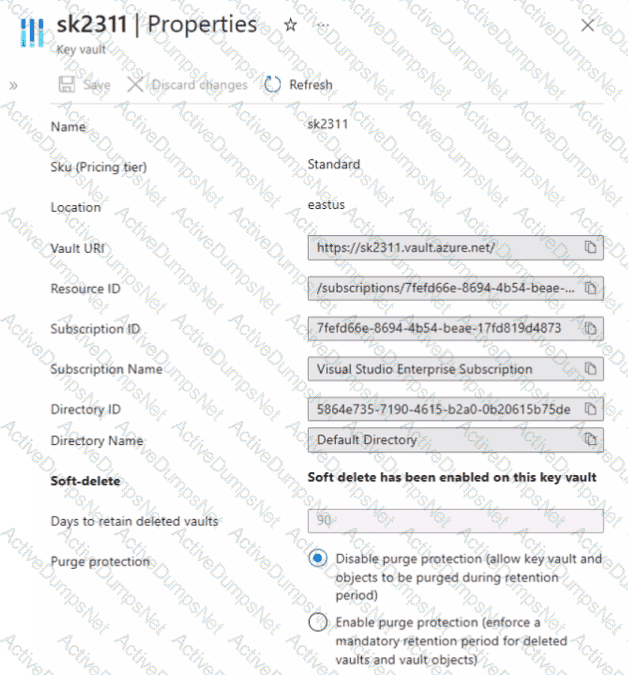
Sk2311 contains the items shown in the following table.
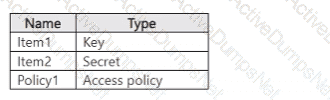
In sk2311, the following events occur in sequence:
• Item1 is deleted.
• Item2 and Policy1 ate deleted.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
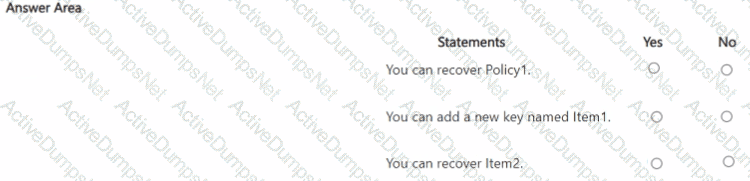
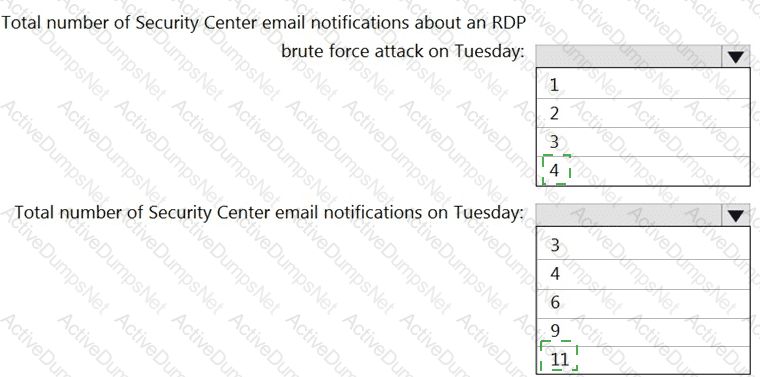
On Monday, you configure an email notification in Azure Security Center to notify user user1@contoso.com.
On Tuesday, Security Center generates the security alerts shown in the following table.
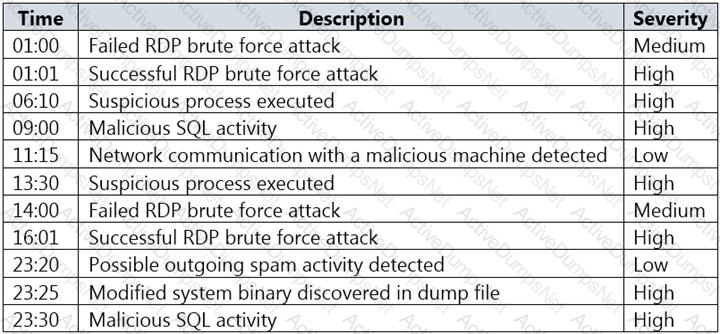
How many email notifications will user1@contoso.com receive on Tuesday? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have an Azure SQL database.
You implement Always Encrypted.
You need to ensure that application developers can retrieve and decrypt data in the database.
Nantes’s of information should you provide to the developers? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You have an Azure subscription named Subscription1 that contains the resources shown in the following table.
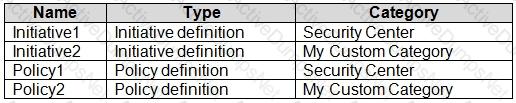
You need to identify which initiatives and policies you can add to Subscription1 by using Azure Security Center.
What should you identify?
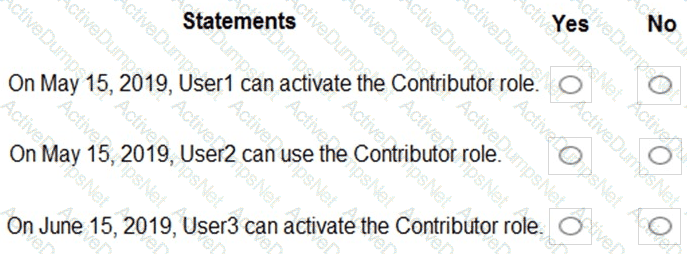
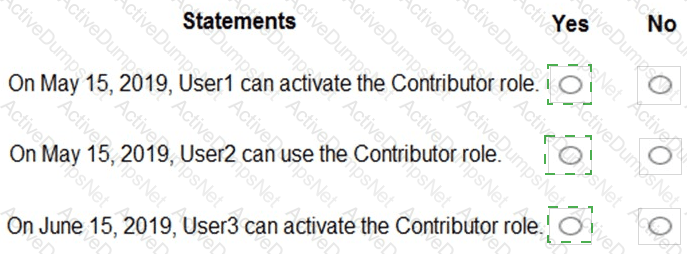
You have an Azure Active Directory (Azure AD) tenant that contains the users shown in the following table.
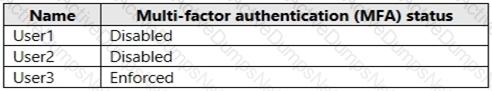
In Azure AD Privileged Identity Management (PIM), the Role settings for the Contributor role are configured as shown in the exhibit. (Click the Exhibit tab.)
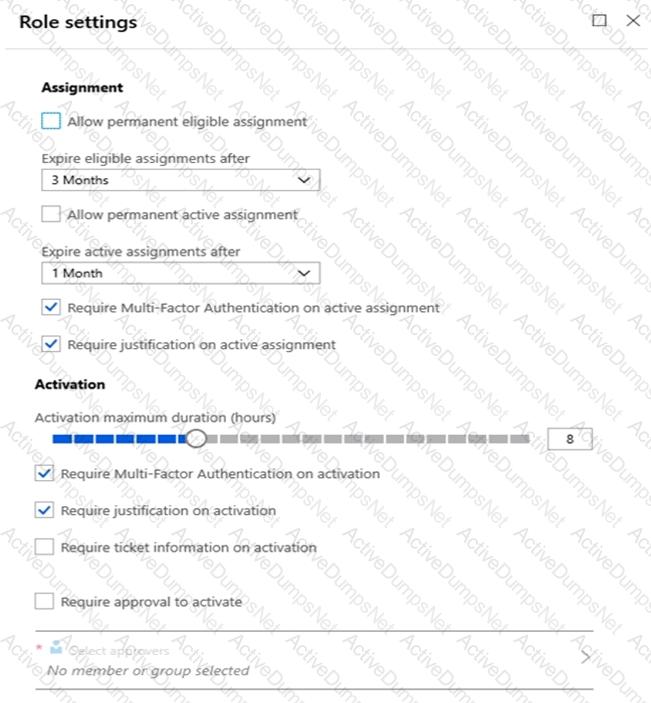
You assign users the Contributor role on May 1, 2019 as shown in the following table.
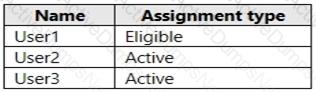
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have an Azure SQL Database server named SQL1.
You plan to turn on Advanced Threat Protection for SQL1 to detect all threat detection types.
Which action will Advanced Threat Protection detect as a threat?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these
questions will not appear in the review screen.
You use Azure Security Center for the centralized policy management of three Azure subscriptions.
You use several policy definitions to manage the security of the subscriptions.
You need to deploy the policy definitions as a group to all three subscriptions.
Solution: You create a policy initiative and assignments that are scoped to resource groups.
Does this meet the goal?
You have an Azure AD tenant.
You plan to implement an authentication solution to meet the following requirements:
• Require number matching.
• Display the geographical location when signing in.
Which authentication method should you include in the solution?
You have an Azure subscription that contains an Azure key vault named Vault1 and a virtual machine named VM1. VM1 has the Key Vault VM extension installed.
For Vault1, you rotate the keys, secrets, and certificates.
What will be updated automatically on VM1?
You have a Microsoft 365 tenant that uses an Azure Active Directory (Azure AD) tenant The Azure AD tenant syncs to an on-premises Active Directory domain by using an instance of Azure AD Connect.
You create a new Azure subscription
You discover that the synced on-premises user accounts cannot be assigned rotes in the new subscription.
You need to ensure that you can assign Azure and Microsoft 365 roles to the synced Azure AD user accounts.
What should you do first?
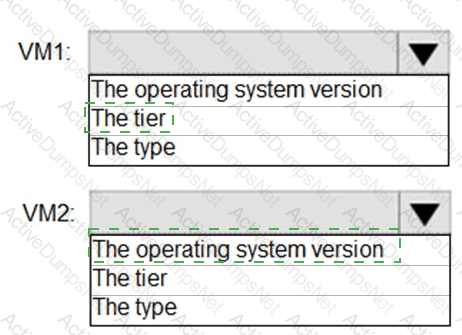
You have two Azure virtual machines in the East US2 region as shown in the following table.
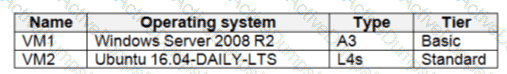
You deploy and configure an Azure Key vault.
You need to ensure that you can enable Azure Disk Encryption on VM1 and VM2.
What should you modify on each virtual machine? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
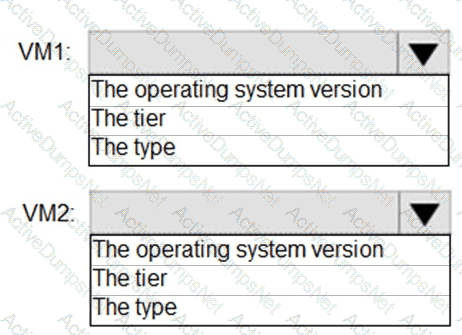
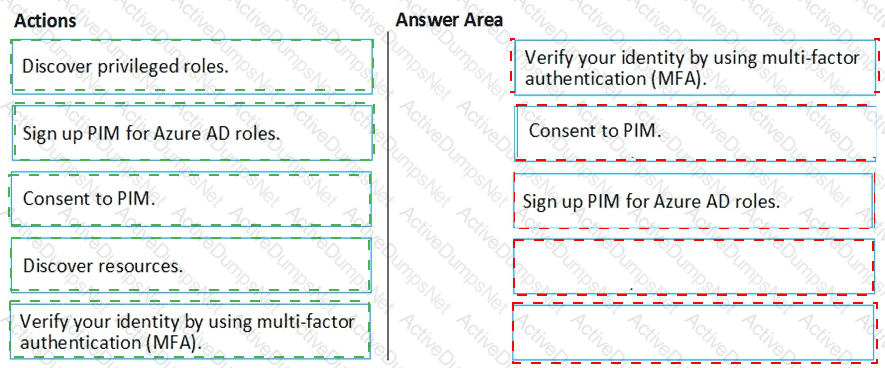
You create an Azure subscription with Azure AD Premium P2.
You need to ensure that you can use Azure Active Directory (Azure AD) Privileged Identity Management (PIM) to secure Azure roles.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You have an Azure subscription named Sub1.
In Azure Security Center, you have a security playbook named Play1. Play1 is configured to send an email message to a user named User1.
You need to modify Play1 to send email messages to a distribution group named Alerts.
What should you use to modify Play1?
You plan to configure Azure Disk Encryption for VM4. Which key vault can you use to store the encryption key?
You need to meet the technical requirements for the finance department users.
Which CAPolicy1 settings should you modify?
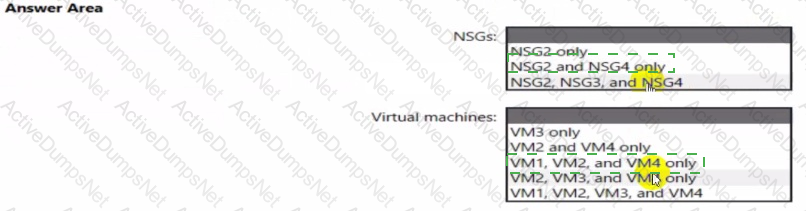
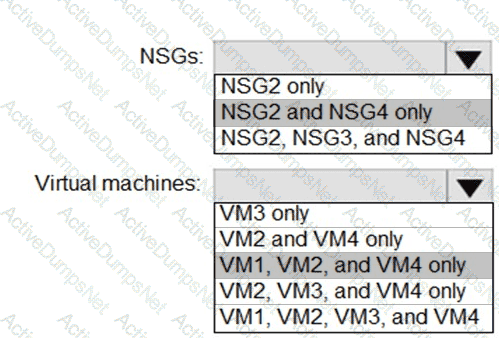
You implement the planned changes for ASG1 and ASG2.
In which NSGs can you use ASG1. and the network interfaces of which virtual machines can you assign to ASG2?
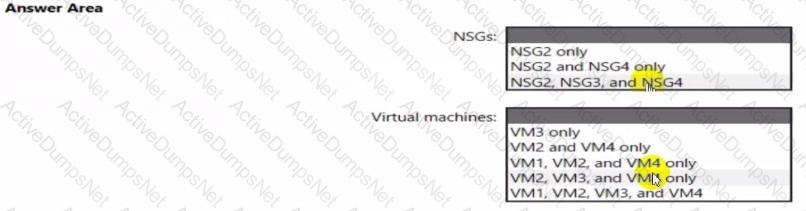
You plan to implement JIT VM access. Which virtual machines will be supported?
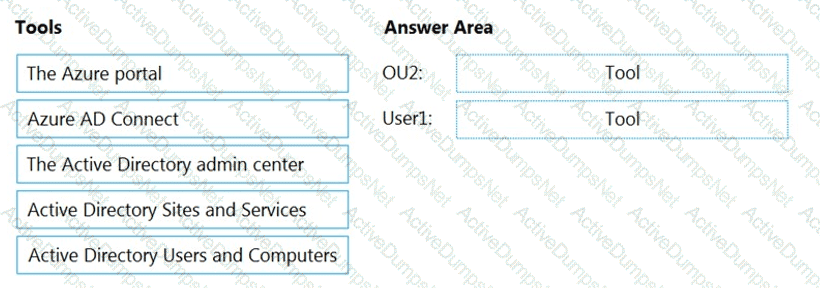
You need to perform the planned changes for OU2 and User1.
Which tools should you use? To answer, drag the appropriate tools to the correct resources. Each tool may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
From Azure Security Center, you need to deploy SecPol1.
What should you do first?
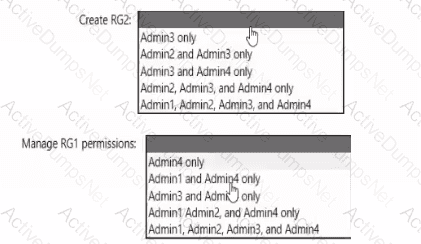
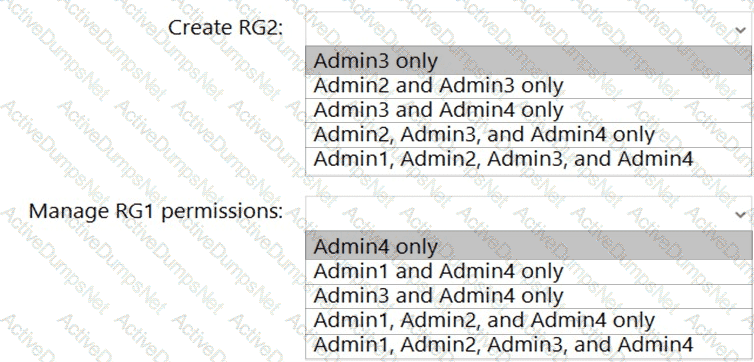
You need to delegate the creation of RG2 and the management of permissions for RG1. Which users can perform each task? To answer select the appropriate options in the answer area. NOTE: Each correct selection is worth one point
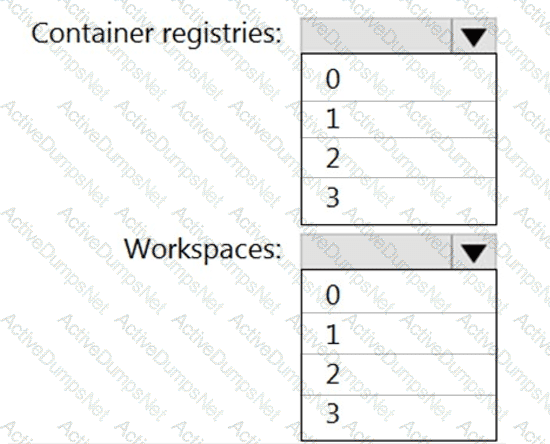
You need to configure support for Azure Sentinel notebooks to meet the technical requirements.
What is the minimum number of Azure container registries and Azure Machine Learning workspaces required?
You need to encrypt storage1 to meet the technical requirements. Which key vaults can you use?
You need to ensure that User2 can implement PIM.
What should you do first?
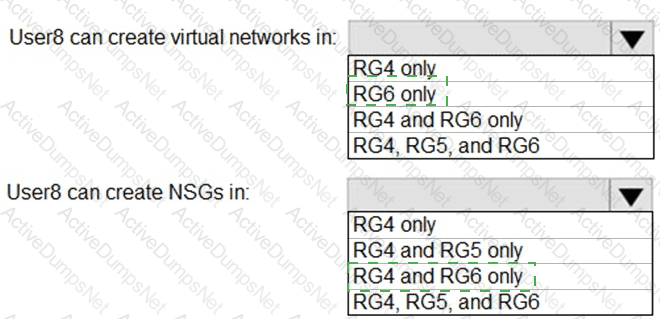
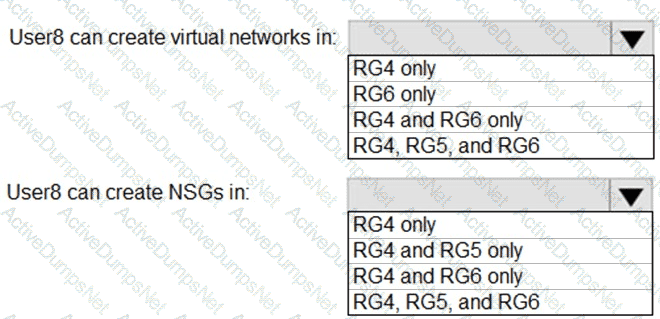
You assign User8 the Owner role for RG4, RG5, and RG6.
In which resource groups can User8 create virtual networks and NSGs? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to meet the technical requirements for VNetwork1.
What should you do first?
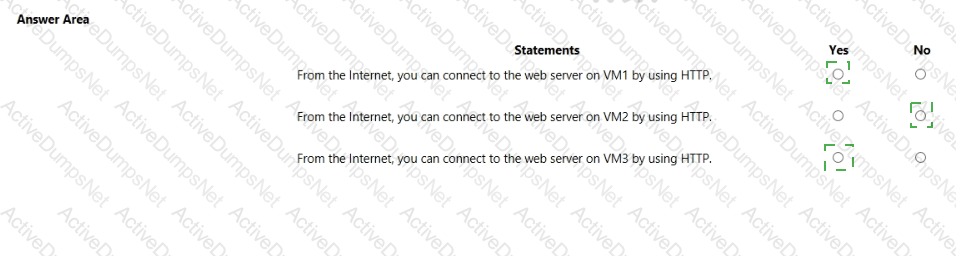
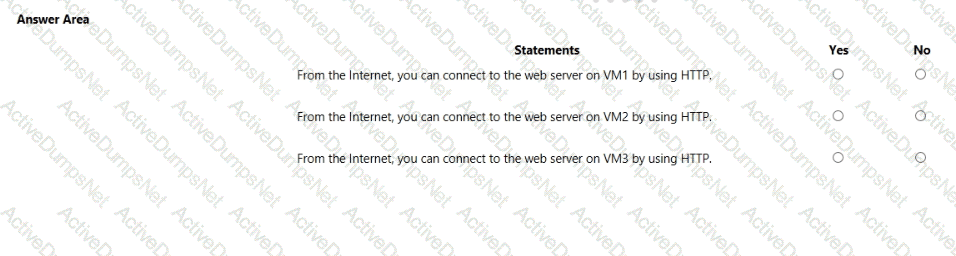
You are evaluating the security of VM1, VM2, and VM3 in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
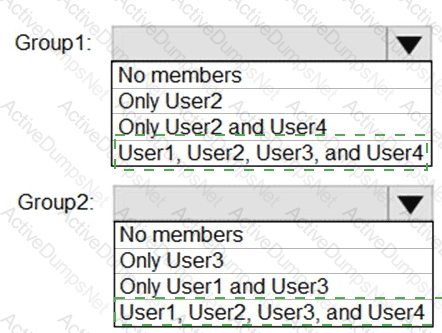
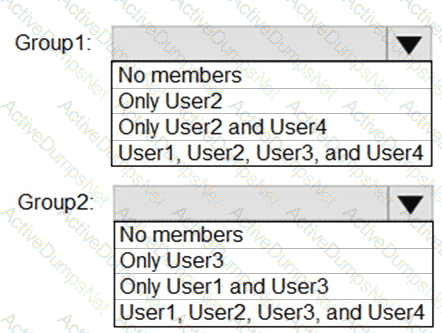
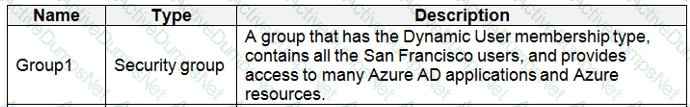
What is the membership of Group1 and Group2? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
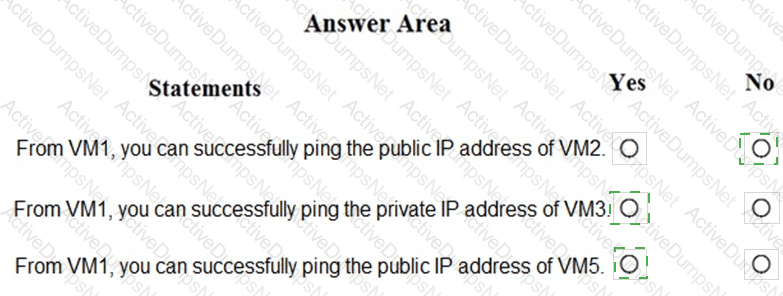
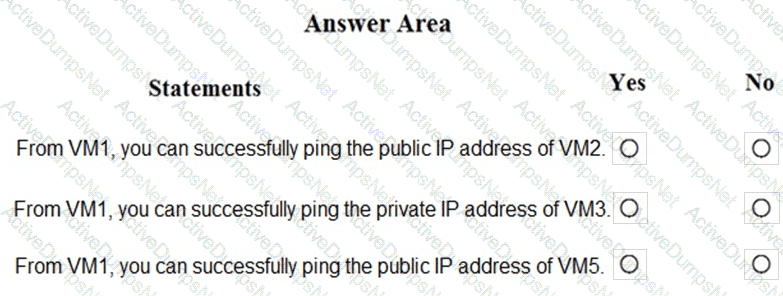
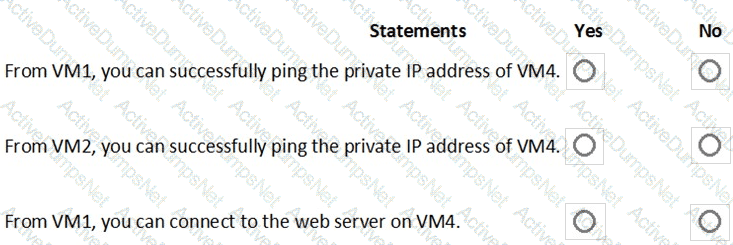
You are evaluating the security of the network communication between the virtual machines in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
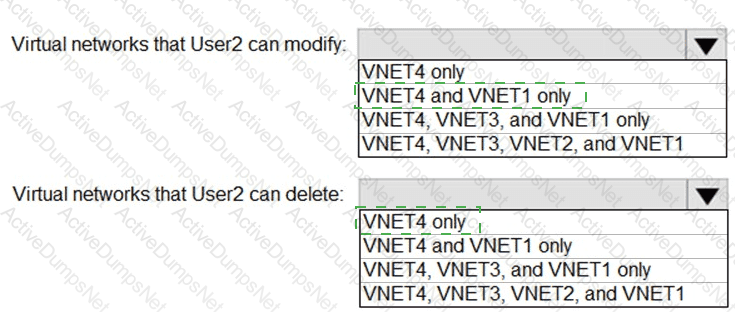
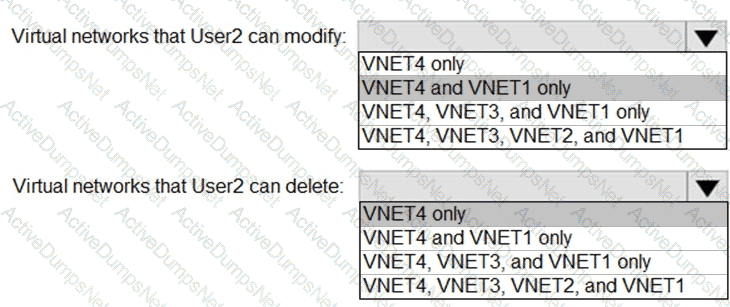
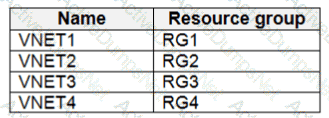
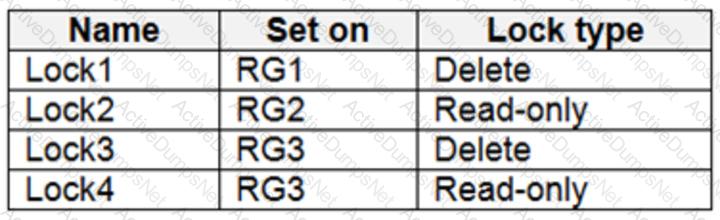
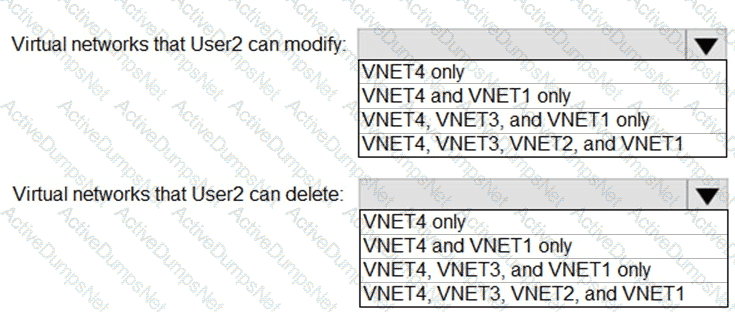
: 2 HOTSPOT
Which virtual networks in Sub1 can User2 modify and delete in their current state? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
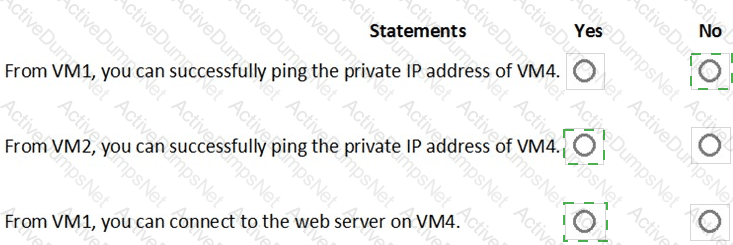
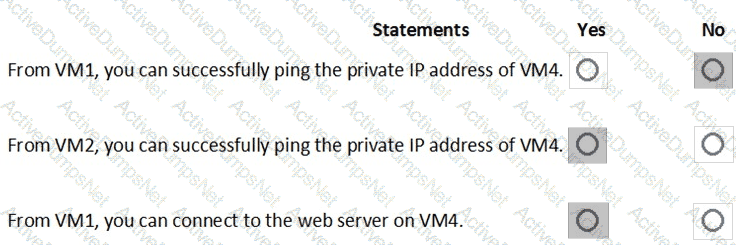
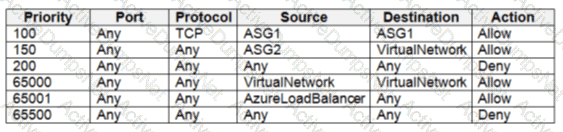
You are evaluating the effect of the application security groups on the network communication between the virtual machines in Sub2.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

 Graphical user interface, text, application, chat or text message Description automatically generated
Graphical user interface, text, application, chat or text message Description automatically generated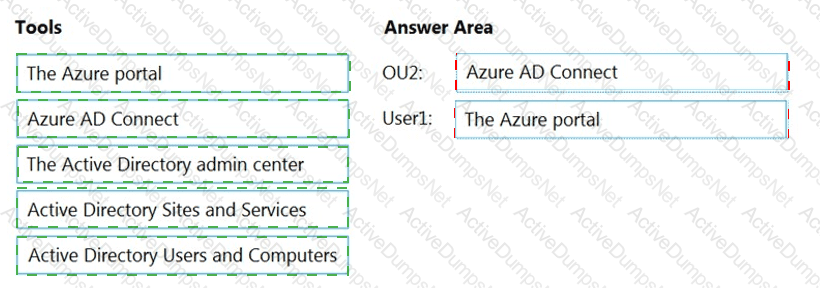
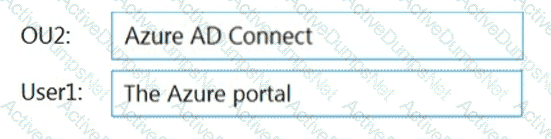 Table Description automatically generated
Table Description automatically generated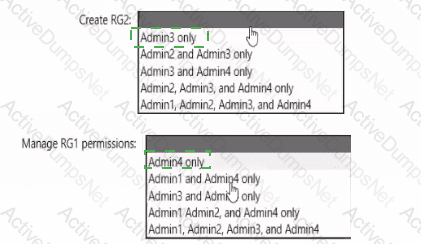
 Graphical user interface, text, application, chat or text message Description automatically generated
Graphical user interface, text, application, chat or text message Description automatically generated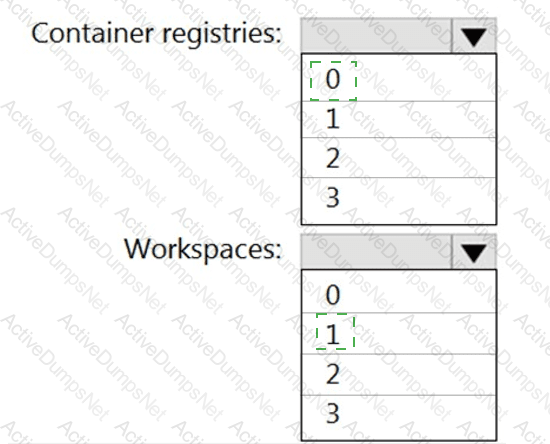
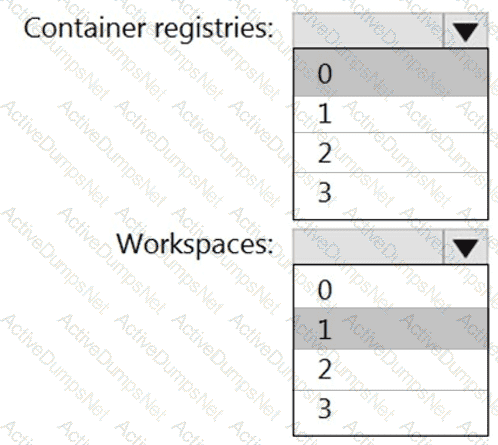 Table Description automatically generated with medium confidence
Table Description automatically generated with medium confidence