Juniper JN0-106 Junos - Associate (JNCIA-Junos) Junos OS 21.2 Exam Practice Test
Junos - Associate (JNCIA-Junos) Junos OS 21.2 Questions and Answers
A security policy requires that a user account be created for auditing purposes. This user should only view configuration and operational data without making any changes. Which predefined login class would satisfy this requirement?
Options:
operator
unauthorized
read-only
super-user
Answer:
CExplanation:
Junos OS provides several predefined login classes to implement Role-Based Access Control (RBAC) efficiently. For an auditor who needs to verify the current state of the device without the risk of altering it, the read-only class is the ideal choice.
The read-only class allows a user to log in and execute show commands to view the running configuration and operational statistics. However, it strictly prohibits the user from entering configuration mode (using the configure command) or executing any " impactful " operational commands that could reset counters, clear log files, or affect traffic flow.
It is important to distinguish this from the operator class. While the operator class also cannot change the configuration, it does have permissions to clear interface statistics, reset routing protocol neighbors, and perform other " clear " or " reset " actions. For a pure auditing role where even resetting a counter would be considered a breach of policy, read-only provides the necessary " look but don ' t touch " environment. The super-user class, conversely, has full unrestricted access, and unauthorized is not a standard functional class. Using the read-only class ensures compliance with security best practices by granting the minimum necessary privileges required for the auditing task.
Which statement describes the purpose of configuring traceoption log files in Junos OS?
Options:
The traceoption log files automatically optimize routing decisions based on traffic patterns.
The traceoption log files enable detailed debugging of specific protocols or processes.
The traceoption log files allow permanent storage of all system logs for compliance purposes.
The traceoption log files provide real-time monitoring of interface bandwidth utilization.
Answer:
BExplanation:
Traceoptions represent an essential diagnostic facility within Junos OS, primarily used by network engineers for deep-level troubleshooting and protocol analysis. The fundamental purpose of configuring traceoption log files is to enable detailed debugging of specific protocols—such as BGP, OSPF, or IS-IS—or specific system processes like the Routing Protocol Process (rpd). When enabled, the system captures detailed information about the internal operations of the protocol, including the exchange of packets, state machine transitions, and error conditions, writing this data to a dedicated file in the /var/log directory.
Unlike standard system logging (syslog), which captures high-level events and warnings, traceoptions provide a granular, " behind-the-scenes " view of how a protocol is interacting with its neighbors. This is particularly useful for identifying the root cause of complex adjacency issues or route instability that standard show commands may not reveal. However, because tracing can be resource-intensive, it is typically configured with specific flags to limit the output to relevant events and is disabled once the troubleshooting task is complete. Traceoptions do not serve to optimize routing automatically , nor are they intended for permanent compliance storage or simple bandwidth monitoring. Instead, they remain the premier tool for clinical debugging and protocol verification within the Junos environment. Reference: Operational Monitoring and Maintenance, Troubleshooting Tools and Traceoptions.
==========
Which two statements about route preference in Junos are correct? (Choose two.)
Options:
Both direct and static routes have the same preference.
Both direct and local routes have the same preference.
Both OSPF internal and OSPF AS external routes have the same preference.
Both EBGP and IBGP routes have the same preference.
Answer:
B, DExplanation:
Route preference is the quantitative value Junos OS uses to rank the trustworthiness of different routing sources when multiple protocols provide a path to the same destination. A critical architectural distinction in Junos is that both direct and local routes share the same default preference value of 0. Direct routes represent subnets physically connected to an interface, while local routes represent the specific IP address assigned to the device interface itself. Because a value of 0 is the lowest possible numerical value, these routes are always preferred over any learned via dynamic protocols or static configuration.
Additionally, Junos OS treats External BGP (EBGP) and Internal BGP (IBGP) differently than other vendors by assigning both an identical default preference of 170. This means that if the same prefix is learned via both EBGP and IBGP, the preference value alone will not determine the active route; the system must instead proceed to the standard BGP path selection algorithm (evaluating attributes like Local Preference, AS Path, and Origin) to break the tie. In contrast, OSPF distinguishes between its route types, assigning a preference of 10 to internal routes and 150 to AS external routes. Understanding these default values—specifically the parity between direct/local and the unified preference for BGP variants—is foundational for predicting how the Routing Engine populates the forwarding table. Reference: Routing Fundamentals, Default Route Preference Values.
==========
What are two characteristics of transit traffic in Junos OS? (Choose two.)
Options:
It includes routing protocol packets.
It is traffic destined for the Routing Engine.
It does not require control plane processing.
It is forwarded by the Packet Forwarding Engine.
Answer:
C, DExplanation:
Transit traffic represents the primary " workload " of a Junos device; it is the data that enters one network interface and exits another, destined for a remote host. Unlike exception traffic, transit traffic is forwarded exclusively by the Packet Forwarding Engine (PFE) . The PFE uses specialized Application-Specific Integrated Circuits (ASICs) or programmable NPUs to perform lookups in the hardware-based forwarding table (FIB) at wire speed.
A defining characteristic of transit traffic is that it does not require control plane processing . Once the Routing Engine (RE) has populated the PFE with the necessary forwarding instructions, the RE steps out of the way. The packets pass through the PFE ' s ingress processing, lookups, and egress queuing without ever consuming CPU cycles on the Routing Engine. This bypass is what allows Junos devices to maintain massive throughput and low latency, even if the RE is busy recalculating a complex BGP table. Routing protocol packets (like OSPF updates) and traffic destined for the router ' s own management IP address are explicitly not transit traffic; they are control plane traffic because they terminate at the device ' s " brain. " Transit traffic is strictly " pass-through " data.
Which statement is correct when Router R1 receives a packet from User A destined for User B as shown in the exhibit?

Options:
Router R1 replaces the destination IP address in the packet with the IP address of Router R2.
Router R1 leaves the packet unchanged.
Router R1 replaces the destination MAC address in the packet with the MAC address of Router R2.
Router R1 replaces the destination MAC address in the packet with the MAC address of User B.
Answer:
CExplanation:
Comprehensive and Detailed 150 to 250 words of Explanation From: In a routed environment like the one shown in the exhibit, traffic forwarding involves a constant interaction between Layer 3 (Network) and Layer 2 (Data Link) addressing. When User A generates a packet destined for User B, the source and destination IP addresses remain static throughout the entire journey across the network (assuming no Network Address Translation is performed). However, the Layer 2 Ethernet headers must be rewritten at every hop because MAC addresses have only local significance on a physical segment.
As Router R1 receives the packet from User A, it performs a lookup in its Forwarding Information Base (FIB) and identifies that the path to User B requires forwarding the packet to Router R2. R1 decapsulates the incoming frame, stripping away the original Ethernet header that contained User A ' s source MAC and R1 ' s own destination MAC. To forward the packet to the next hop, R1 creates a new Ethernet header. The source MAC address becomes the MAC address of R1’s egress interface, and the destination MAC address is replaced with the MAC address of Router R2 . R1 cannot use User B ' s MAC address at this point because User B is not on a directly connected segment. This hop-by-hop MAC address replacement is essential for the Packet Forwarding Engine to successfully deliver the frame to the next Layer 3 device in the path. Reference: Networking Fundamentals, Packet Forwarding, Layer 2 and Layer 3 Addressing.
What information would you find using the CLI help command?
Options:
a URL for accessing the technical documentation
message of the day
hyperlinks for remediation actions
an explanation for specific system log error messages
Answer:
DExplanation:
The Junos OS CLI is engineered with an extensive, self-contained help subsystem designed to provide immediate technical guidance without requiring constant reference to external manuals. The help command is a versatile tool that operates through several key sub-commands: topic, reference, and log. While help topic provides conceptual overviews and help reference displays specific configuration syntax and hierarchical requirements, the help log command is specifically tailored for system maintenance and troubleshooting.
The primary purpose of help log is to provide a detailed explanation for specific system log error messages generated by the device. When a Junos daemon or process writes an entry to the syslog, it includes a unique message identifier or " tag. " By executing help log < message-tag > , an architect can retrieve a clinical breakdown of why the message was generated, the severity of the event, and often the recommended action to resolve the underlying issue. This capability is vital for rapid interpretation of complex system events in real-time. It ensures that administrators have authoritative, context-aware information directly at the terminal, effectively bridging the gap between raw diagnostic output and actionable technical intelligence within the Junos environment. Reference: User Interfaces, CLI Help Facilities, help log.
==========
Which two traffic types are processed by a Routing Engine using Junos OS? (Choose two.)
Options:
traffic with CoS markings
transit traffic
routing updates
local management traffic
Answer:
C, DExplanation:
The Routing Engine (RE) in a Junos device serves as the centralized intelligence and management hub, primarily responsible for the control and management planes of the system. In this capacity, the RE is tasked with processing routing updates, such as OSPF Link State Advertisements (LSAs) or BGP Update messages. These updates are vital for the RE to maintain the Routing Information Base (RIB), calculate the shortest paths, and subsequently populate the Forwarding Information Base (FIB) which is then pushed to the Packet Forwarding Engine (PFE).
Furthermore, the Routing Engine handles all local management traffic. This category encompasses administrative access through the Command Line Interface (CLI) via SSH or Telnet, SNMP queries from network management systems, and system logging processes. Because the RE runs the Junos OS kernel, it must directly interpret and respond to these management-level requests to ensure the device remains configurable and observable. Conversely, transit traffic—the data passing through the device from one ingress port to an egress port—is offloaded to the PFE to be handled at wire speed. While the PFE manages the heavy lifting of data forwarding and Class of Service (CoS) application, the RE remains focused on high-level protocol maintenance and system administration, ensuring that control plane stability is maintained even under heavy traffic loads. Reference: Junos OS Fundamentals, Control Plane Functions, Routing Engine Traffic.
==========
Which two tasks should be performed when creating a new user account on a Junos device? (Choose two.)
Options:
Assign the user to a login class.
Enable SSH for the user explicitly.
Configure a password for the user.
Configure the user to bypass authentication.
Answer:
A, CExplanation:
Creating a new user account in Junos OS involves several specific steps within the [edit system login] configuration hierarchy. To establish a functional and secure user account, an administrator must first define the username and assign that user to a login class. Login classes are essential because they define the permissions and access levels for the user, such as super-user, read-only, or operator. Without a login class, a user would have no permissions to perform tasks within the CLI.
The second mandatory task is to configure an authentication method for the user, most commonly a password. This is typically done using the authentication plain-text-password command, which prompts the administrator to enter and confirm the secret string that the system then hashes and stores. While Junos also supports public-key authentication for SSH, a local password remains the standard for basic access control. It is important to note that SSH access is generally controlled at the system level under [edit system services] and does not need to be enabled on a per-user basis individually. Furthermore, allowing a user to bypass authentication is contrary to the Junos security model and is not a standard task in user account creation. Reference: User Interfaces, User Management, Login Classes.
When troubleshooting a problem, you issue the following commands in sequence:
show chassis alarms
show chassis fpc
show chassis fpc detail
show chassis errors fpc-slot 0
In this scenario, what happens when you press the up arrow key twice at the prompt?
Options:
The show chassis fpc command is displayed at the prompt.
The show chassis errors fpc-slot 0 command is displayed at the prompt.
The show chassis alarms command is displayed at the prompt.
The show chassis fpc detail command is displayed at the prompt.
Answer:
DExplanation:
The Junos OS Command Line Interface (CLI) utilizes an advanced command-line editing environment influenced by standard Emacs and Unix terminal behaviors. One of the most critical features for operational efficiency is the command history buffer. This buffer automatically records a sequence of previously executed commands, allowing administrators to recall, modify, and re-execute them without manual re-entry.
The navigation of this history buffer is strictly chronological and operates as a stack. When the up arrow key is pressed once, the CLI retrieves the most recent command that was successfully entered—in this scenario, show chassis errors fpc-slot 0. Pressing the up arrow key a second time moves the cursor one step further back into the history stack to the command that preceded the most recent one. Following the provided sequence, the command executed prior to the " errors " check was show chassis fpc detail. Consequently, the second press of the up arrow key will display show chassis fpc detail at the prompt. This mechanism is essential for architects during intensive troubleshooting sessions, enabling them to cycle through relevant diagnostic commands rapidly while maintaining focus on the hardware output rather than syntax repetition. Reference: User Interfaces, CLI Editing Features, Command History.
==========
You committed a new configuration on a Junos router, but users report connectivity issues. You must quickly restore the previous working configuration without manually editing the candidate configuration. Which command should you use to load the required configuration into the candidate configuration?
Options:
rollback 0
show | compare rollback
rollback 1
load override
Answer:
CExplanation:
In Junos OS, the configuration database is designed with a robust versioning system that facilitates rapid recovery from administrative errors. Every time a commit command is successfully executed, the system automatically archives the previous active configuration and assigns it a " rollback " index. The rollback command is used within configuration mode to revert the candidate configuration to a previously saved state.
The indices are zero-based, where rollback 0 represents the currently active configuration that was just committed. To restore the configuration that was functional immediately before the most recent, problematic commit, the administrator must use rollback 1. This command replaces the current candidate configuration with the contents of the last known working state. It is important to note that executing rollback 1 only populates the candidate buffer; to make this previous configuration active and restore connectivity, the administrator must subsequently issue the commit command. This mechanism is a cornerstone of Junos OS ' s commitment to high availability and operational resilience, allowing for nearly instantaneous restoration of services without the need for manual line-by-line configuration edits during a network outage.
Which two characteristics describe Junos OS software? (Choose two.)
Options:
Junos OS is a monolithic code base.
Junos OS supports automation features.
Junos OS runs only on routers.
Junos OS uses a modular architecture with independent processes.
Answer:
B, DExplanation:
Junos OS is distinguished from legacy network operating systems by its modern, modular architecture . Unlike a monolithic system where a single failure can crash the entire kernel, Junos runs various software functions—such as the routing protocol process (rpd), the interface process (dcd), and the management daemon (mgd)—as independent processes in their own protected memory spaces. This modularity ensures high availability; if one daemon encounters an error, it can be restarted without impacting the overall system stability or traffic forwarding.
Furthermore, Junos OS is a leader in automation features . It was built with a programmable foundation, utilizing an XML-based configuration database and supporting NETCONF for standardized remote management. This allows network architects to utilize modern DevOps tools like Ansible, Python (PyEZ), and SaltStack to automate complex configuration tasks, perform bulk upgrades, and enforce state compliance. By treating the network as code, Junos enables high-velocity operations that reduce human error. While Junos originally powered routers, it now runs across a vast portfolio including EX/QFX switches and SRX firewalls, proving its versatility far beyond just routing platforms.
Which interface type prefix represents a 10-Gigabit Ethernet interface?
Options:
ge
xe
et
fe
Answer:
BExplanation:
In Junos OS, the naming convention for physical interfaces is highly structured, providing immediate information regarding the media type, hardware location, and port number. The prefix of an interface name is a two-letter or three-letter code that identifies the speed and physical transmission characteristics of the interface. For 10-Gigabit Ethernet (GbE) interfaces, the correct prefix is xe. This prefix is a standard identifier across Junos platforms, regardless of whether the interface is fixed or modular.
Understanding these prefixes is essential for navigating the Junos configuration hierarchy and performing operational monitoring. For comparison, other common prefixes include fe for Fast Ethernet (10/100 Mbps), ge for Gigabit Ethernet (1 Gbps), and et for higher-speed interfaces such as 40-GbE or 100-GbE. When an administrator views the output of commands like show interfaces terse, identifying the xe prefix allows for the quick verification of high-bandwidth links within the network fabric. This standardized nomenclature ensures consistency across different hardware families, such as the EX, MX, and QFX series, facilitating easier management and troubleshooting for network architects. This concludes the provided set of questions from the Junos Associate (JNCIA-Junos) curriculum. Reference: Junos OS Fundamentals, Interface Naming Conventions.
Which two statements about prefix lists in Junos are correct? (Choose two.)
Options:
Prefix lists can be re-used in multiple routing policies.
Prefix lists can be used in both firewall filters and routing policies.
Prefix lists cannot be used in routing policies.
Prefix lists cannot be used in firewall filters.
Answer:
A, BExplanation:
Prefix lists in Junos OS are named collections of IP addresses or network prefixes defined under the [edit policy-options] hierarchy. One of their most powerful features is their versatility and reusability. Because they are defined as independent objects, a single prefix list can be referenced in multiple different routing policies across the device. This modularity ensures consistency; for instance, if a set of " internal " prefixes changes, an administrator only needs to update the list in one location for those changes to propagate to every policy that utilizes it.
Furthermore, prefix lists are designed to be used across different functional areas of the Junos architecture. They are equally valid for use in routing policies (to control the import or export of routes between protocols like BGP or OSPF) and in firewall filters (to match source or destination addresses for transit or management traffic). When used in a routing policy, the prefix list typically performs an exact match on the prefix length unless modified by a match type like orlonger. In a firewall filter, it acts as a high-speed lookup table for the Packet Forwarding Engine. This dual-purpose capability makes prefix lists a foundational tool for architects seeking to implement scalable, automated security and routing logic within a unified configuration framework.
Which two statements about route preference in Junos OS are correct? (Choose two.)
Options:
Higher route preference values indicate higher priority.
Route preference is considered after evaluating the longest prefix match.
Lower route preference values indicate higher priority.
Route preference determines the forwarding table size.
Answer:
B, CExplanation:
In Junos OS, route preference (often referred to as administrative distance in other operating systems) is the mechanism used to select the " best " path when the routing table receives multiple advertisements for the exact same destination prefix from different routing sources. The core rule for preference is that lower values indicate a more preferred or " higher priority " route . For example, a direct route has a default preference of 0, a static route is 5, and OSPF internal routes are 10. If a router learns about the same network from both OSPF and a static entry, it will select the static route because 5 is lower than 10.
Crucially, route preference is only evaluated after the longest prefix match (LPM) has been determined. LPM is the absolute first step in packet forwarding; the router will always choose the most specific route available (e.g., a /28 over a /24). Only if there are multiple entries for that same /28 does the router look at preference to break the tie. It is a common misconception that a lower preference value can override a more specific prefix; in reality, a /32 route with a preference of 170 (BGP) will always win over a /24 route with a preference of 5 (Static). Understanding this hierarchy is vital for network architects when designing redundant paths and predictable failover behaviors.
You are asked to subnet the broadcast domains but need to support 50 hosts. In this scenario, which subnet mask would satisfy this requirement?
Options:
/26
/27
/28
/29
Answer:
AExplanation:
Determining the appropriate subnet mask for a specific host requirement is a core task in designing Junos-based network infrastructures. The number of usable hosts in an IPv4 subnet is calculated using the formula $2^n - 2$, where $n$ represents the number of host bits remaining after the network prefix. In this scenario, the requirement is to support 50 hosts within a single broadcast domain.
Evaluating the options:
A /29 mask provides 3 host bits ($2^3 - 2 = 6$ hosts), which is insufficient.
A /28 mask provides 4 host bits ($2^4 - 2 = 14$ hosts), which is insufficient.
A /27 mask provides 5 host bits ($2^5 - 2 = 30$ hosts), which still fails to meet the 50-host threshold.
A /26 mask provides 6 host bits. Applying the formula: $2^6 - 2 = 64 - 2 = 62$ usable host addresses.
Since a /26 mask provides 62 usable addresses, it is the smallest standard subnet mask that fully satisfies the requirement of 50 hosts. Using a /26 mask allows for the 50 required hosts while providing a small buffer for future growth (12 additional addresses) without wasting the excessive address space associated with a /25 or /24 mask. This efficient allocation of address space is a best practice for maintaining scalable and organized routing tables on Juniper devices.
How are the Routing Engine and the Packet Forwarding Engine components connected?
Options:
They use shared memory access.
They use external breakout cables.
They use an MPLS connection.
They use an internal Ethernet link.
Answer:
DExplanation:
The fundamental architecture of Junos OS is built upon the clean separation of the Control Plane (Routing Engine or RE) and the Forwarding Plane (Packet Forwarding Engine or PFE). While these two components perform vastly different tasks, they must maintain a high-speed, reliable communication channel to synchronize the state of the device. This connection is achieved through an internal Ethernet link .
This internal link serves several critical functions. First, it allows the Routing Engine to " push " the distilled forwarding table (FIB) to the PFE, ensuring that the hardware knows exactly how to handle incoming transit traffic at wire speed. Second, it acts as a conduit for exception traffic . If the PFE receives a packet that it cannot handle alone—such as an OSPF hello, a BGP update, or an ICMP " Time Exceeded " message—it sends that packet over the internal Ethernet link to the RE for processing. This link is carefully policed by built-in rate limiters to ensure that a flood of transit-related exception traffic cannot overwhelm the Routing Engine ' s CPU, a mechanism known as control plane protection. By using a standard Ethernet-based internal fabric, Junos ensures a scalable and modular design where the RE can focus on complex protocol calculations while the PFE focuses on the heavy lifting of packet switching.
Which two statements accurately describe the relationship between the routing table and the forwarding table on a Junos device? (Choose two.)
Options:
The routing table resides in the data plane for fast lookups.
The routing table selects the best route based on routing information.
The forwarding table is built from the routing table.
The routing table is built from the forwarding table.
Answer:
B, CExplanation:
The relationship between the routing table (Routing Information Base or RIB) and the forwarding table (Forwarding Information Base or FIB) is the cornerstone of the Junos OS architectural separation between the control and data planes. The routing table resides in the control plane on the Routing Engine (RE). Its primary role is to aggregate all reachability information from every configured protocol and select the best route for each destination prefix based on criteria like preference and metrics.
Once the Routing Engine has identified the single " active " best path for a destination, it distills this complex routing data into a simplified, streamlined version called the forwarding table . The forwarding table contains only the essential information needed to move a packet: the destination prefix, the egress interface, and the Layer 2 next-hop MAC address. The RE then " pushes " this forwarding table to the Packet Forwarding Engine (PFE) in the data plane. By having the PFE use a table built from the routing table , Junos ensures that transit traffic can be processed at wire speed without the overhead of complex routing logic. This one-way flow—from the comprehensive RIB on the RE to the optimized FIB on the PFE—allows the device to maintain high performance even while routing protocols are recalculating or the management plane is under heavy load.
You want to redeploy a Junos device by clearing the existing configuration and resetting it to factory defaults. In this scenario, which command would help to accomplish this task?
Options:
show system storage
request system storage cleanup dry-run
request system zeroize
request system storage cleanup
Answer:
CExplanation:
When a network architect needs to completely sanitize a Junos device for redeployment or decommissioning, the request system zeroize command is the most thorough tool available. Unlike simply loading the factory default configuration, which only resets the configuration database, the zeroize command performs a deep wipe of the system.
Specifically, this command removes all user-created data, including all configuration files (active and rollback), log files, license keys, and any locally stored files in the /var/tmp or /home directories. It essentially restores the device to its " pristine " out-of-box state. Once the command is initiated, the device reboots and goes through a sanitization process. This is a critical security measure to ensure that sensitive information—such as encrypted passwords, proprietary routing policies, or SNMP community strings—does not leave the organization when hardware is transferred.
In contrast, the request system storage cleanup command is a maintenance utility used to delete temporary files and old log entries to free up disk space, but it does not affect the running configuration or user accounts. Therefore, for a total system reset that includes configuration deletion, zeroize is the mandatory operational command.
Which two statements describe rollback configuration behavior in Junos OS? (Choose two.)
Options:
Rollback configurations are applied automatically after a commit confirmed timeout.
Rollback 0 always refers to the factory default configuration.
Rollback files are stored automatically after each commit.
Up to 100 rollback configurations are maintained by default.
Answer:
A, CExplanation:
Junos OS incorporates a robust configuration versioning and recovery system designed to protect against configuration errors and human oversight. A key feature of this system is that rollback files are stored automatically by the device after each successful commit. These files represent a historical record of previous active configurations. By default, the system maintains a set number of these files, allowing an administrator to revert to a previous state (e.g., rollback 1) if the most recent changes result in unexpected network instability.
Another critical safety mechanism is the behavior associated with the commit confirmed command. If an administrator issues this command but fails to provide a subsequent confirmation within a designated timeframe (defaulting to 10 minutes), the system assumes a loss of management connectivity. Consequently, the rollback configurations are applied automatically after the commit confirmed timeout to restore the previous known-good state. This is an essential best practice for remote configuration management. It is important to note that rollback 0 refers to the currently active configuration, not the factory default, and that while Junos supports maintaining a large number of rollback files, the primary operational benefit lies in the automated storage and confirmation-based recovery processes that ensure the device remains reachable and stable. Reference: Configuration Basics, Rollback Configurations, Commit Confirmed Logic.
==========
Click the Exhibit button.
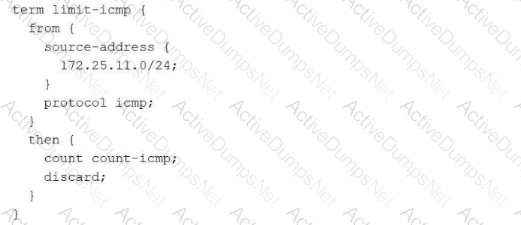
Referring to the exhibit, which two actions will occur when a packet matches the firewall filter? (Choose two.)
Options:
A counter will be incremented.
The packet will be discarded.
The packet will be forwarded.
An ICMP destination unreachable message will be returned.
Answer:
A, BExplanation:
In Junos OS, firewall filters are constructed using terms that specify match criteria (the from statement) and actions to be taken (the then statement). When a packet enters an interface where this filter is applied, the Packet Forwarding Engine (PFE) evaluates it against the defined terms. In this exhibit, the term limit-icmp targets packets sourced from the 172.25.11.0/24 network that specifically use the ICMP protocol.
When a packet meets both criteria, the actions defined in the then block are triggered:
count count-icmp; : This is a non-terminating action . It instructs the system to increment a specific software counter named count-icmp. This allows administrators to monitor exactly how many packets are hitting this specific term using the show firewall command.
discard; : This is a terminating action . It immediately stops any further evaluation of the packet and drops it. A key characteristic of the discard action in Junos is that it is a " silent " drop; the router simply deletes the packet from its buffer without notifying the sender.
Option D is incorrect because returning an ICMP destination unreachable message is the specific behavior of the reject action, not the discard action. Option C is incorrect because discard explicitly prevents the packet from being forwarded. Understanding the distinction between silent discards and active rejections is essential for architects when designing security policies that balance stealth with network transparency.
Exhibit:
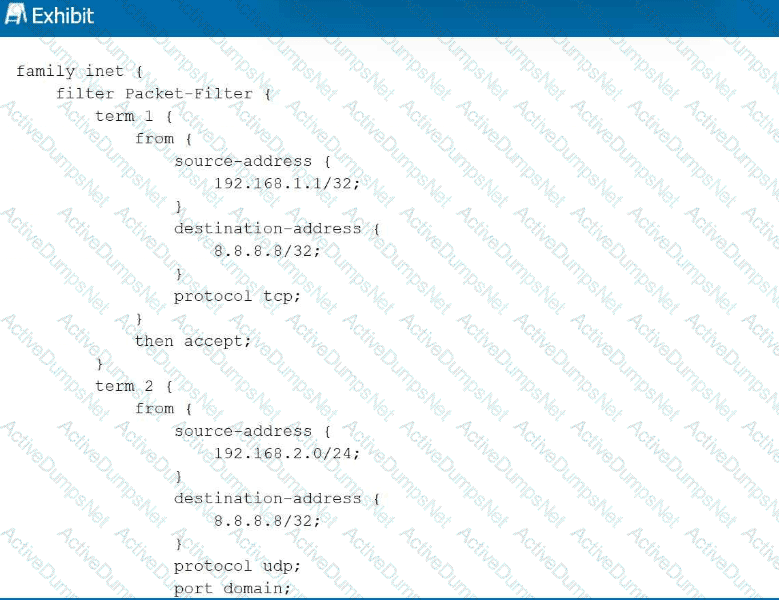
Referring to the exhibit, with firewall filter Packet-Filter attached to an interface, if traffic is sent from 192.168.1.1 to 8.8.8.8 for a UDP DNS query, what will happen to the traffic?
Options:
The traffic will match term 1 and be forwarded.
The traffic will match the default last term and be forwarded.
The traffic will match the default last term and be discarded.
The traffic will match term 3 and be forwarded.
Answer:
CExplanation:
Junos OS firewall filters operate on a first-match basis, evaluating terms sequentially from top to bottom. In this scenario, a UDP DNS packet (destination port 53) is sent from 192.168.1.1 to 8.8.8.8. Evaluation begins with term 1 , which matches the correct source and destination IP addresses but specifies protocol tcp . Because the actual traffic uses UDP, term 1 is not a match. Evaluation then moves to term 2 . While term 2 correctly identifies protocol udp and port domain (port 53), it requires the source-address to reside within the 192.168.2.0/24 subnet. Since the source is 192.168.1.1 , term 2 also fails to match.
When a packet fails to match any explicitly defined terms in a Junos firewall filter, it is subject to the implicit deny action. This default " last term " is a hardcoded safety mechanism that automatically discards all traffic that has not been explicitly permitted. Consequently, because neither term provides a match for the specific combination of source IP, protocol, and destination port, the DNS query is silently dropped by the Packet Forwarding Engine. This behavior ensures that Junos devices maintain a " deny-by-default " security posture, requiring administrators to define precise permit statements for all required transit or management traffic. Reference: Routing Policy and Firewall Filters, Firewall Filter Evaluation, Implicit Discard.
==========
What is the main function of the forwarding table on a Junos device?
Options:
It contains only active routes used to forward packets through the PFE.
It advertises routes to neighboring routers.
It stores all learned routes from routing protocols.
It determines the best route based on route preference.
Answer:
AExplanation:
The architecture of Junos OS is designed with a strict functional separation between the control plane and the data plane. The Routing Engine (RE) maintains the master Routing Information Base (RIB), which acts as a comprehensive database storing all potential paths learned from various routing protocols, static configurations, and direct connections. However, to achieve wire-speed performance, the device does not consult the RIB for every packet. Instead, the RE identifies the " active " or best routes for each destination based on route preference and metrics.
Once these active routes are selected, the RE distills them into a streamlined Forwarding Information Base (FIB), commonly referred to as the forwarding table, and pushes this table to the Packet Forwarding Engine (PFE). The main function of the forwarding table is to provide a high-speed, local lookup mechanism that allows the PFE to forward transit traffic across the switch fabric with minimal latency. This table contains only the specific exit interface and Layer 2 next-hop information required for packet delivery. By isolating the PFE from the overhead of complex routing protocol state machines and all inactive redundant paths, Junos OS ensures that forwarding performance remains consistent even during control plane re-convergence. Reference: Junos OS Fundamentals, Control Plane and Forwarding Plane functions.
==========
According to HPE Juniper Networking, what are two recommended tasks you should perform before upgrading Junos OS on a device? (Choose two.)
Options:
Delete all rollback configurations.
Verify available storage space using the show system storage command.
Disable all interfaces to prevent traffic during the upgrade.
Back up the active current configuration.
Answer:
B, DExplanation:
Upgrading the Junos OS is a high-impact operation that requires thorough preparation to minimize risk and potential downtime. According to Juniper ' s best practices, one of the most critical preliminary steps is to verify that the device has sufficient available storage space. Using the show system storage command, an administrator can inspect the /var partition, which is the primary directory where software packages are temporarily stored and expanded during the installation process. If the storage is nearly full, the upgrade may fail midway, potentially leaving the device in an inconsistent state or requiring manual intervention via the boot loader.
The second mandatory task is to back up the active configuration . While Junos automatically maintains rollback files locally, these could be lost if the storage media fails or if a " clean install " (format install) becomes necessary. Having an external backup on a remote server or a local workstation ensures that the device ' s identity, policies, and interface settings can be restored quickly regardless of the upgrade outcome. Other tasks, such as creating a rescue configuration or performing a file system cleanup, are also highly recommended to ensure the " last known good " state is preserved. Disabling interfaces is generally unnecessary as Junos manages the transition gracefully, and deleting rollbacks would counterproductively remove historical recovery points. Ensuring these two pillars—storage availability and off-box backups—provides the safest foundation for a successful software lifecycle management event.
What are two requirements for root password recovery in Junos? (Choose two.)
Options:
You must have console access to the device.
You must have saved the rescue configuration in advance.
You must load the factory default configuration.
You must reboot the device.
Answer:
A, DExplanation:
Root password recovery in Junos OS is a critical administrative procedure designed to regain access to the management plane when the root credentials are lost. This process is fundamentally tied to the physical security of the device, as it requires two specific conditions that cannot be met over a standard network connection. First, the administrator must have direct console access to the device. Because the recovery process involves interrupting the Junos boot sequence before the operating system kernel and its associated security services (such as SSH) are fully initialized, it must be performed through the serial management port.
Second, a system reboot is mandatory. The recovery mechanism is triggered by interrupting the boot loader (typically the " Loader " or " U-Boot " stage) by pressing the Space bar or a specific key sequence during power-on. This allows the administrator to enter " single-user mode " or boot into a " recovery " state. Once in this restricted environment, the device mounts its internal storage in a way that permits the modification of the root authentication parameters without requiring the existing password. This workflow intentionally bypasses the standard authentication database to restore management control while preserving the rest of the device configuration. This procedure underscores the importance of securing physical access to the chassis, as anyone with console access and the ability to cycle power can eventually gain root-level authority over the system.
What is the primary purpose of an IPv6 link-local address?
Options:
to provide Layer 2 connectivity
to assign a unique address for multicast traffic
to enable communication between devices on the same segment
to replace the default gateway in IPv6 networks
Answer:
CExplanation:
IPv6 link-local addresses, which are identified by the fe80::/10 prefix, are a mandatory component of the IPv6 architecture. The primary purpose of a link-local address is to enable immediate communication between devices located on the same local network segment (the same " link " ) without the requirement for a global unicast address or an external routing infrastructure. These addresses are non-routable, meaning they are never forwarded by a router to another network segment.
Every IPv6-enabled interface on a Junos device automatically generates a link-local address, typically derived from the interface ' s MAC address using the EUI-64 format or a stable privacy algorithm. These addresses are essential for several core functions: they are used by the Neighbor Discovery Protocol (NDP) to resolve MAC addresses, they serve as the source address for routing protocol adjacency formation (such as OSPFv3 or RIPng), and they are frequently used as the next-hop address in IPv6 routing tables. While they do not provide Layer 2 connectivity themselves (which is the role of the MAC address), they provide the necessary Layer 3 link-level presence required for nodes to discover one another and communicate across the physical medium before any global addressing is configured.
Which two tasks are performed by the Routing Engine in a Junos device? (Choose two.)
Options:
The Routing Engine runs routing protocols.
The Routing Engine evaluates transit traffic against firewall filters.
The Routing Engine manages the device configuration.
The Routing Engine forwards transit traffic.
Answer:
A, CExplanation:
The Routing Engine (RE) functions as the centralized processor and administrative core of any Junos OS-based platform. Its primary responsibility involves the execution and maintenance of the control plane, which includes running all active routing protocols such as OSPF, BGP, and IS-IS. Through these protocols, the RE exchanges topology information with neighboring routers, builds the Routing Information Base (RIB), and calculates the optimal paths for traffic. Once these paths are determined, the RE distributes the resulting Forwarding Information Base (FIB) to the Packet Forwarding Engine (PFE) for hardware-level execution.
In addition to its protocol duties, the Routing Engine manages the device configuration and the overall system environment. This includes providing the user interface (CLI or J-Web), managing the candidate and active configuration databases, and handling the commit process. While the PFE is specifically designed to forward transit traffic and evaluate that traffic against firewall filters at line rate, the RE focuses on the higher-level logic and management tasks. This architectural separation ensures that management functions—such as a complex configuration commit or a protocol re-convergence event—do not degrade the performance of the data plane, allowing the device to continue forwarding user traffic without interruption. Reference: Junos OS Fundamentals, Routing Engine Functions, Management and Control Planes.
==========
Which Junos tool should you use to identify the path that packets take through the network to a destination?
Options:
monitor interface traffic
traceroute
SNMP
ping
Answer:
BExplanation:
When you need to visualize the hop-by-hop journey of a packet across a multi-vendor or Junos-based network, traceroute is the definitive operational tool. Unlike ping , which merely confirms end-to-end reachability by eliciting an Echo Reply, traceroute provides a clinical breakdown of every Layer 3 device (router or switch) in the path.
The mechanics of this tool are quite clever: it sends out a sequence of packets (usually UDP or ICMP) with an increasing Time-to-Live (TTL) value, starting at 1. When the first router receives the packet, it decrements the TTL to 0, discards the packet, and sends an ICMP " Time Exceeded " message back to the source. This informs your Junos device of the first hop ' s identity. This process repeats, incrementing the TTL each time, until the packet reaches the final destination. This path discovery is vital for identifying where traffic might be diverted by a misconfigured routing policy or where latency is being introduced in the network fabric. While monitor interface traffic gives you real-time throughput on a local port and SNMP provides historical telemetry to a management station, neither can map the external topological path like traceroute. In the Junos CLI, you can even specify the source address or bypass the routing table to test specific egress paths.
Which two statements are correct about logical units? (Choose two.)
Options:
A physical interface can host multiple logical units.
Logical units can have multiple IP addresses.
Logical units are used only for management interfaces.
A physical interface can host only one logical unit.
Answer:
A, BExplanation:
In the Junos OS architecture, interfaces are strictly divided into physical and logical components. The physical interface represents the actual hardware port (e.g., ge-0/0/0), while logical units (e.g., ge-0/0/0.0) define the protocol-specific parameters and logical segmentation required for traffic processing. A fundamental characteristic of this model is that a single physical interface can host multiple logical units. This is a mandatory requirement for technologies such as 802.1Q VLAN tagging, where each logical unit corresponds to a different VLAN ID on the same physical link, allowing for efficient micro-segmentation of traffic.
Furthermore, Junos OS allows logical units to have multiple IP addresses assigned to them within the same address family or across different families (such as inet and inet6). This flexibility enables a single logical interface to reside on multiple subnets simultaneously, which is essential for complex routing scenarios, multi-homing, or transitional dual-stack environments. It is a common misconception that logical units are reserved for management; in reality, every physical interface must have at least one logical unit (typically unit 0) configured for the device to process any transit or local traffic. Understanding the hierarchical relationship between the physical port and its logical subdivisions is critical for successful interface management and protocol deployment on Junos platforms. Reference: Junos OS Fundamentals, Interface Naming and Hierarchy.
==========
Unlock JN0-106 Features
- JN0-106 All Real Exam Questions
- JN0-106 Exam easy to use and print PDF format
- Download Free JN0-106 Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet
Questions & Answers PDF Demo
- JN0-106 All Real Exam Questions
- JN0-106 Exam easy to use and print PDF format
- Download Free JN0-106 Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet
