ISC CC CC - Certified in Cybersecurity Exam Practice Test
CC - Certified in Cybersecurity Questions and Answers
Why is an asset inventory so important?
An organization’s security system that prevents, detects, analyzes, and responds to cybersecurity incidents is called:
Scans networks to determine connected devices and services:
Example of token-based authentication:
A security event does not affect confidentiality, integrity, or availability. What is it?
A security model where no network is trusted by default is called:
Permitting authorized access while preventing improper disclosure.
The purpose of risk identification is:
Which security control is most commonly used to prevent data breaches?
What is the focus of disaster recovery planning after a data center outage?
A set of security controls or system settings used to ensure uniformity of configuration through the IT environment?
What is the highest priority during incident response?
A method for risk analysis that is based on the assignment of a descriptor such as low, medium, or high.
What is the best practice to clear SSD storage after use?
Raj wants aphysical deterrent controlto discourage unauthorized entry. Which option best serves this purpose?
Which type of application can intercept sensitive information such as passwords on a network segment?
What drove the introduction of IPv6?
Which technology should be implemented to increase the work effort required for buffer overflow attacks?
Exhibit.
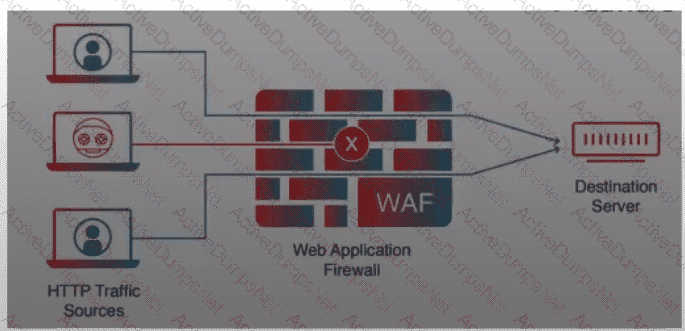
What is the PRIMARY purpose of a web application firewall (WAF)?
An IP network protocol standardized by the IETF through RFC 792 to determine if a host is available is:
Which plan is activated when Incident Response and BCP fail?
What is the difference between Business Continuity Planning (BCP) and Disaster Recovery Planning (DRP)?
An employee unintentionally shares confidential information with an unauthorized party. What term best describes this?
Which of the following is often associated with Disaster Recovery planning?
What is the purpose of the CIA triad?
What is the importance of non-repudiation in today’s world of e-commerce?
Which is NOT a function of an Intrusion Prevention System (IPS)?
Which is the most efficient and effective way to test a business continuity plan?
Which concept prevents crime by designing a physical environment that positively influences human behavior?
Which uses encrypted, machine-generated codes to verify a user's identity?
Hashing safeguards which CIA triad principle?
Software that creates and manages virtual machines (VMM) is called:
Which principle requires that all instances of data be identical?
Events with negative consequences such as crashes, floods, defacement, or malicious code execution are called:
A power outage disrupts operations. Which plan helps sustain operations?
Which principle states that users should have access only to the specific data and resources needed to perform required tasks?
Security commensurate with risk and magnitude of harm is known as:
The amount of risk an organization is willing to accept in pursuit of objectives is called:
COVID-19 is an example where which plan sustains business?
What principle states that individuals should only have the minimum set of permissions necessary to carry out their job functions?
Example of a deterrent control:
When the ISC2 mail server sends mail to other mail servers, it becomes a —?
Which of the following properties is NOT guaranteed by digital signatures?
Critical business functions are disrupted due to a system outage. Which plan sustains operations?
The primary functionality of Privileged Access Management (PAM) is:
VLAN hopping belongs to which OSI layer?
During an ISC2 CC exam, you observe another candidate cheating. What should you do?
What is an IP address?
255.255.255.0 represents:
A team activates procedures to mitigate a cyberattack. What plan is this?
Which type of control minimizes the impact of an attack and restores normal operations as quickly as possible?
Ensuring a process cannot be completed by a single person is known as:
What is the process of verifying a user’s identity called?
Which cloud service model provides the most suitable environment for customers to build and operate their own software?
An employee launched a privilege escalation attack to gain root access on one of the organization’s database servers. The employee has an authorized user account on the server. What log file would MOST likely contain relevant information?
Mark is configuring an automated data transfer between two hosts and needs an authentication method. What approach is best suited?
What does internal consistency of information refer to?
Which protocol is used for secure email?
The process of how an organization is managed and how decisions are made is called:
What is the primary goal of a risk management process in cybersecurity?
A popular way of implementing the principle of least privilege is:
What is the recommended temperature range for optimal data center uptime?
Is defined as the process of identifying, estimating, and prioritizing risks.
An attacker places themselves between two communicating devices is known as:
Which is an example of a deterrent control?
A system crash results in loss of data. What term best describes this?
An unknown person obtains unauthorized access to the company file system. This is an example of:
What is the end goal of a Disaster Recovery Plan (DRP)?
A type of malware capable of self-propagation and infecting multiple systems without human intervention is called:
What is the term used to denote the inherent set of privileges assigned to a user upon the creation of a new account?
What kind of control is it when we add a backup firewall that takes over if the main one stops working?
Why is identifying roles and responsibilities important in IR planning?
Which IR phase involves identifying critical data and systems?
A ________ creates an encrypted tunnel to protect your personal data and communications.
Who is responsible for publishing and signing the organization’s policies?
The practice of sending fraudulent communications that appear to come from a reputable source is known as:
Who should participate in creating a BCP?
The evaluation of security controls to determine whether they are implemented correctly and operating as intended is known as:
What is an incident in cybersecurity?
Communication between end systems is encrypted using a key, often known as ________?
A centralized organizational function that monitors, detects, and analyzes security events to prevent disruptions is called:
Which plan provides immediate response procedures and management guidance?
Faking the sender address of a transmission to gain illegal entry is called:
What is the potential impact of an IPSec replay attack?
Which organization defines Internet protocol standards?
What is the shortened form of
2001:0db8:0000:0000:0000:ffff:0000:0001?
DNS operates at which OSI layer?
A structured way to align IT with business goals while managing risk and regulations:
The Bell–LaPadula access control model is a form of:
What is the primary purpose of a honeytoken in cybersecurity?
Flooding a server with traffic to make services unavailable is called:
XenServer, LVM, Hyper-V, and ESXi are:
Which of the following is NOT one of the four typical ways of managing risk?
What is the purpose of immediate response procedures in a BCP?
What is the focus of disaster recovery planning after a data center failure?
An authorized simulated attack to evaluate security is called:
What is the main objective of DRP after a breach shuts down systems?
Who must follow HIPAA compliance?
A DDoS attack flooding ICMP packets is called:
Which type of attack takes advantage of vulnerabilities in validation?
A measure of the degree to which an organization depends on information or systems to achieve its mission is called:
What is an IPSec replay attack?
Often offered by third-party organizations and covering advisory or compliance objectives:
Which can be considered a fingerprint of a file or message?
Information should be consistently and readily accessible for authorized parties.
In cybersecurity, typical threat actors include:
Which document provides a high-level overview of a Disaster Recovery Plan?
Port forwarding is also known as:
A company’s servers are down due to malware. What is the FIRST step the DR team should take?
Finance Server and Transaction Server have restored their original facility after a disaster. What should be moved in FIRST?
TCP and UDP reside at which layer of the OSI model?
Methods or mechanisms used to gain unauthorized access are called:
Which of the following is a characteristic of cloud computing?
Which provides confidentiality by hiding or obscuring a message so it cannot be understood by unauthorized parties?
Exhibit.
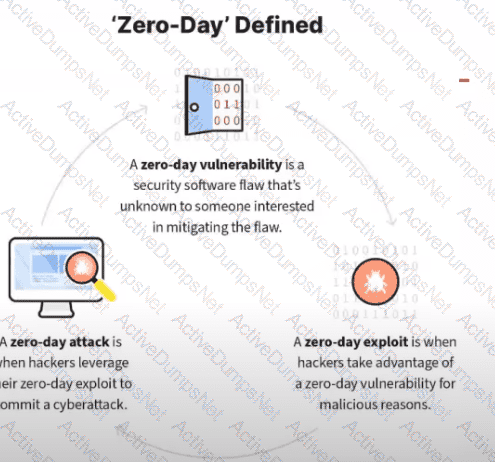
What kind of vulnerability is typically not identifiable through a standard vulnerability assessment?
Embedded systems and network-enabled devices that communicate with the Internet are considered:
The documented set of procedures to detect, respond to, and limit the consequences of cyberattacks is called:
When operating in a cloud environment, which cloud deployment model provides security teams with the greatest access to forensic information?
A LAN-based attack involving malicious packets sent to the default gateway:
If a device is found to be non-compliant with the security baseline, what action should the security team take?
