- Home
- IIA
- CIA
- IIA-CIA-Part3
- IIA-CIA-Part3 - Internal Audit Function
IIA IIA-CIA-Part3 Internal Audit Function Exam Practice Test
Internal Audit Function Questions and Answers
When evaluating the help desk services provided by a third-party service provider which of the following is likely to be the internal auditor's greatest concern?
Options:
Whether every call that the service provider received was logged by the help desk.
Whether a unique identification number was assigned to each issue identified by the service provider
Whether the service provider used its own facilities to provide help desk services
Whether the provider's responses and resolutions were well defined according to the service-level agreement.
Answer:
DExplanation:
An internal auditor's primary concern in evaluating third-party help desk services is ensuring that the provider meets Service-Level Agreement (SLA) requirements, particularly regarding response times, issue resolution, and service quality.
Correct Answer (D - Whether the provider's responses and resolutions were well defined according to the SLA)
The SLA defines expected service levels, including:
Response and resolution times.
Performance metrics (e.g., first-call resolution rate).
Escalation procedures.
Compliance with contractual obligations.
The IIA Practice Guide: Auditing Third-Party Relationships states that internal auditors must assess SLA compliance as a key control in outsourcing arrangements.
Why Other Options Are Incorrect:
Option A (Whether every call was logged):
While logging all calls is good practice, the focus should be on meeting SLA requirements, not just documentation.
The IIA GTAG 7: Continuous Auditing emphasizes measuring performance, not just recording activities.
Option B (Whether a unique ID was assigned to each issue):
Issue tracking is important, but an ID alone does not guarantee service quality or SLA compliance.
Option C (Whether the provider used its own facilities):
The location of the service provider’s facilities does not impact SLA compliance.
IIA Practice Guide: Auditing Third-Party Relationships – Outlines how auditors should evaluate SLAs and vendor performance.
IIA GTAG 7: Continuous Auditing – Highlights the importance of performance measurement in outsourced services.
Step-by-Step Explanation:IIA References for Validation:Thus, ensuring the provider meets SLA-defined response and resolution times (D) is the internal auditor's greatest concern.
Which of the following is true of bond financing, compared to common stock, when alJ other variables are equal?
Options:
Lower shareholder control
lower indebtedness
Higher company earnings per share.
Higher overall company earnings
Answer:
CExplanation:
When a company finances through bonds (debt) instead of issuing common stock (equity), it increases earnings per share (EPS) because bond financing does not dilute ownership, whereas issuing new stock does.
Impact on Earnings Per Share (EPS):
EPS formula: EPS=Net Income−Preferred DividendsNumber of Outstanding Shares\text{EPS} = \frac{\text{Net Income} - \text{Preferred Dividends}}{\text{Number of Outstanding Shares}}EPS=Number of Outstanding SharesNet Income−Preferred Dividends
Since bond financing does not increase the number of shares outstanding, net income is distributed among fewer shareholders, increasing EPS.
If the company issues more stock instead of bonds, EPS decreases because the same earnings are divided among more shares.
Why Bond Financing Affects EPS Favorably:
Interest on bonds is tax-deductible, reducing taxable income and increasing net profits.
Unlike dividends, which are paid on common stock and reduce retained earnings, bondholders receive fixed interest payments that do not dilute equity ownership.
A. Lower shareholder control: ❌
Bondholders do not get voting rights, whereas issuing more stock reduces existing shareholders’ control.
This statement would be true for stock financing, not bond financing.
B. Lower indebtedness: ❌
Bonds increase a company’s debt obligations, not reduce them.
If a company uses stock financing instead of bonds, it avoids taking on debt.
D. Higher overall company earnings: ❌
While bonds increase EPS, they do not necessarily increase total earnings.
The company must pay interest on bonds, which could reduce net income if not managed properly.
IIA Standard 2110 (Governance): Ensures management selects financing strategies that align with financial stability.
COSO ERM Framework – Financial Risk Management: Evaluates how financing choices impact shareholder value and risk exposure.
IFRS & GAAP Accounting Standards on Debt vs. Equity Financing: Explain how bond financing increases EPS compared to issuing new shares.
Step-by-Step Justification:Why Not the Other Options?IIA References:
Which of the following would most likely serve as a foundation for individual operational goats?
Options:
Individual skills and capabilities.
Alignment with organizational strategy.
Financial and human resources of the unit.
Targets of key performance indicators
Answer:
BExplanation:
Individual operational goals must align with an organization's overall strategy to ensure that employee efforts contribute to corporate success. Operational goals are specific, measurable objectives that support the broader strategic direction.
Why Option B (Alignment with organizational strategy) is Correct:
Organizational strategy defines the long-term vision, mission, and objectives.
Individual operational goals should align with this strategy to ensure consistency and effectiveness.
Strategic alignment ensures resources are used efficiently and performance contributes to corporate success.
Why Other Options Are Incorrect:
Option A (Individual skills and capabilities):
While important, skills alone do not define operational goals—they are tools to achieve goals.
Option C (Financial and human resources of the unit):
These resources support operational goals, but they do not serve as the foundation. Goals are set based on strategy first.
Option D (Targets of key performance indicators - KPIs):
KPIs measure performance but are not the basis for setting operational goals. Goals should align with strategy first, then KPIs track progress.
IIA Practice Guide – "Performance Management Auditing": Highlights strategic alignment as a basis for setting operational goals.
COSO ERM Framework – "Strategic and Performance Integration": Emphasizes aligning individual goals with organizational strategy.
IIA's Global Perspectives & Insights – "Auditing Organizational Performance": Discusses the role of strategy in goal-setting.
IIA References:Thus, the correct answer is B. Alignment with organizational strategy.
An internal auditor has finalized an engagement of the vendor master file. The results of the current engagement do not differ significantly from that of last year, in which several significant weaknesses in internal controls were reported. The internal auditor states in the final communication that the internal controls are as effective as that of the previous year. Which of the following elements of quality of communication could be improved?
Options:
Conciseness
Constructiveness
Objectivity
Accuracy
Answer:
DExplanation:
According to the IIA Standards, audit communications must be accurate, objective, clear, concise, constructive, and timely. In this case, the auditor’s statement that “controls are as effective as last year” is inaccurate, because the prior year’s report identified significant weaknesses. Equating ineffective controls with effectiveness misrepresents the actual condition, thereby compromising accuracy.
Objectivity (Option C), conciseness (Option A), and constructiveness (Option B) are not the main issue here. The primary weakness is accuracy (Option D).
Which of the following statements is accurate when planning for an external quality assurance assessment of the internal audit function?
Options:
The external assessment would include the audit function’s compliance with laws and regulations
The selected qualified assessor can be from the organization’s shared services team
The external assessment team members must work for an accounting firm
The frequency of the performance of assessments should be considered by the assessor
Answer:
DExplanation:
The external quality assessment must be performed at least once every five years. Therefore, the assessor must consider the frequency requirement when planning the review.
Option A is too narrow; the assessment evaluates conformance with the Standards, not just laws/regulations. Option B is incorrect because assessors must be independent of the organization. Option C is incorrect; assessors may come from various professional backgrounds, not just accounting firms.
Which of the following principles is shared by both hierarchical and open organizational structures?
A superior can delegate the authority to make decisions but cannot delegate the ultimate responsibility for the results of those decisions.
A supervisor's span of control should not exceed seven subordinates.
Responsibility should be accompanied by adequate authority.
Employees at all levels should be empowered to make decisions.
Options:
1 and 3 only
1 and 4 only
2 and 3 only
3 and 4 only
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
Two key management principles apply to both hierarchical and open organizational structures:
Delegation of authority, but not responsibility (Principle 1) – Managers can delegate tasks but remain accountable for outcomes.
Authority must accompany responsibility (Principle 3) – Employees must have the authority to act in accordance with their responsibilities to be effective.
Option 2 (Span of control should not exceed seven subordinates) is not a universal rule, as span of control varies by industry and organization.
Option 4 (Employees should be empowered at all levels) is more applicable to open structures but not a core principle of hierarchical organizations.
Thus, the correct answer is A (1 and 3 only).
Senior management of a dairy organization asks the internal audit function to undertake an advisory service within the finance function and the internal audit function subsequently issues a report. Which of the following is aligned with IIA guidance on monitoring the results of such an engagement?
Options:
Senior management should dedicate a team to carry out a follow-up audit
A member of the finance function should undertake follow-up in line with the scope
Follow-up on the outcome of advisory services is not required
The internal audit function should agree with senior management on the scope of a follow-up
Answer:
CExplanation:
According to the IIA Standards, follow-up is mandatory only for assurance engagements, where corrective action plans are agreed and tracked. Advisory services are intended to add value and offer recommendations but do not require formal follow-up by internal audit. Responsibility for implementing recommendations lies with management.
Options A and B improperly delegate follow-up responsibilities, and Option D incorrectly suggests mandatory follow-up for advisory engagements.
According to IIA guidance, which of the following statements is true with regard to workstation computers that access company information stored on the network?
Options:
Individual workstation computer controls are not as important as companywide server controls
Particular attention should be paid to housing workstations away from environmental hazards
Cybersecurity issues can be controlled at an enterprise level, making workstation-level controls redundant
With security risks near an all-time high, workstations should not be connected to the company network
Answer:
BExplanation:
An intruder posing as the organization's CEO sent an email and tricked payroll staff into providing employees' private tax information. What type of attack was perpetrated?
Options:
Boundary attack.
Spear phishing attack.
Brute force attack.
Spoofing attack.
Answer:
BExplanation:
A spear phishing attack is a highly targeted email-based attack where an attacker impersonates a trusted individual (e.g., the CEO) to trick recipients into providing sensitive information.
In this scenario, an intruder posed as the CEO and deceived payroll staff into sharing employees' private tax information.
Spear phishing is more targeted than general phishing, often using personal details to make the fraudulent request seem legitimate.
A. Boundary attack. (Incorrect)
A boundary attack refers to attempts to breach an organization’s network perimeter defenses, such as firewalls and intrusion detection systems.
This scenario describes a social engineering attack, not a technical boundary attack.
B. Spear phishing attack. (Correct)
Spear phishing attacks are highly personalized email attacks, usually targeting specific employees within an organization.
Attackers research their targets and use realistic messages to trick them into divulging sensitive data.
This fits the scenario, as the attacker impersonated the CEO to steal tax information.
C. Brute force attack. (Incorrect)
A brute force attack involves systematically guessing passwords to gain unauthorized access to systems.
This attack was based on deception, not password cracking.
D. Spoofing attack. (Incorrect, but closely related)
Email spoofing is a technique where an attacker falsifies the sender’s email address.
While spear phishing often includes spoofing, the broader technique used here is spear phishing, as it involved social engineering and deception.
IIA GTAG 16 – Security Risk: IT and Cybersecurity discusses phishing and social engineering threats, emphasizing internal controls to mitigate them.
IIA Standard 2120 – Risk Management highlights the need for risk assessments in cybersecurity, including employee awareness training for phishing attacks.
National Institute of Standards and Technology (NIST) Special Publication 800-61 classifies spear phishing as a high-risk cyber threat to organizations.
Explanation of Answer Choices:IIA References:
When using data analytics during a review of the procurement process, what is the first step in the analysis process?
Options:
Identify data anomalies and outliers
Define questions to be answered
Identify data sources available
Determine the scope of the data extract
Answer:
BExplanation:
Which of the following authentication device credentials is the most difficult to revoke when an employee's access rights need to be removed?
Options:
A traditional key lock.
A biometric device.
A card-key system.
A proximity device.
Answer:
BExplanation:
Comprehensive and Detailed In-Depth Explanation:
Biometric authentication (e.g., fingerprint, retina scan) is the most difficult to revoke because it is linked to an individual’s physical attributes, which cannot be changed like passwords or physical devices.
Option A (Traditional key lock) – Can be revoked by retrieving the key or changing the lock.
Option C (Card-key system) – Can be revoked by deactivating the card.
Option D (Proximity device) – Can be revoked by disabling the device.
Since biometric data is permanently tied to an individual, revoking access is complex, making Option B the correct answer.
When should the results of internal quality assessments be communicated to senior management and the board?
Options:
At least once every five years
At least annually
Periodically, at the discretion of the chief audit executive
Only after the results have been validated by an external assessment
Answer:
BExplanation:
The CAE must communicate the results of the quality assurance and improvement program (QAIP), including internal assessments, to senior management and the board at least annually. This ensures that oversight bodies remain informed about the internal audit activity’s conformance with the Standards and opportunities for improvement.
Option A refers to external assessments, not internal quality reviews. Option C is too vague. Option D is incorrect, as validation is not required before reporting internal assessment results.
According to Herzberg's Two-Factor Theory of Motivation, which of the following is a factor mentioned most often by satisfied employees?
Options:
Relationship with supervisor
Salary
Security.
Achievement
Answer:
CManagement is designing its disaster recovery plan. In the event that there is significant damage to the organization's IT systems this plan should enable the organization to resume operations at a recovery site after some configuration and data restoration. Which of the following is the ideal solution for management in this scenario?
Options:
A warm recovery plan.
A cold recovery plan.
A hot recovery plan.
A manual work processes plan
Answer:
AExplanation:
A disaster recovery plan (DRP) ensures that an organization can restore operations after a major IT system failure. The level of readiness depends on the type of recovery site used:
Correct Answer (A - A Warm Recovery Plan)
A warm site is a partially configured recovery site with some hardware and network infrastructure in place.
In the event of a disaster, some configuration and data restoration are required before full operation can resume.
This solution balances cost and recovery speed, making it ideal for moderate-risk scenarios.
The IIA GTAG 10: Business Continuity Management discusses warm sites as an effective disaster recovery solution.
Why Other Options Are Incorrect:
Option B (A Cold Recovery Plan):
A cold site has minimal infrastructure and requires significant time for setup and data restoration.
This is not ideal for organizations needing faster recovery.
Option C (A Hot Recovery Plan):
A hot site is a fully operational backup system that allows instant recovery, but it is very costly.
The scenario mentions "some configuration and data restoration", which suggests a warm site, not a hot site.
Option D (A Manual Work Processes Plan):
A manual plan involves non-IT solutions, which would not address IT system restoration.
IIA GTAG 10: Business Continuity Management – Describes warm, cold, and hot sites for disaster recovery.
IIA Practice Guide: Auditing Business Continuity Plans – Recommends warm recovery sites for balancing cost and recovery time.
Step-by-Step Explanation:IIA References for Validation:Thus, A is the correct answer because a warm recovery plan allows partial system readiness with minimal downtime.
While conducting an audit of the accounts payable department, an internal auditor found that 3% of payments made during the period under review did not agree with the submitted invoices. Which of the following key performance indicators (KPIs) for the department would best assist the auditor in determining the significance of the test results?
Options:
A KPI that defines the process owner's tolerance for performance deviations.
A KPI that defines the importance of performance levels and disbursement statistics being measured.
A KPI that defines timeliness with regard to reporting disbursement data errors to authorized personnel.
A KPI that defines operating ratio objectives of the disbursement process.
Answer:
AExplanation:
Key Performance Indicators (KPIs) are used to measure and monitor the effectiveness of a process within an organization. In this case, the internal auditor found that 3% of payments did not match submitted invoices, which indicates a potential control weakness in the accounts payable process.
Process Owner’s Tolerance for Performance Deviations (Correct Answer: A)
The most relevant KPI would be one that sets acceptable error limits for invoice payments.
IIA Standard 2120 – Risk Management states that auditors should assess management's risk tolerance and evaluate whether processes are operating within acceptable limits.
If the organization's threshold for errors is 1% and the audit found 3%, it indicates a significant issue requiring corrective action.
This KPI helps the auditor assess materiality and determine the significance of the 3% deviation.
Why the Other Options Are Incorrect:
B. KPI defining the importance of performance levels and disbursement statistics (Incorrect)
While understanding performance levels and disbursement statistics is useful, this KPI does not directly address error tolerance or the impact of deviations.
C. KPI defining timeliness of reporting disbursement errors (Incorrect)
Reporting errors quickly is important, but this KPI does not help in determining whether a 3% error rate is acceptable or excessive.
D. KPI defining operating ratio objectives (Incorrect)
Operating ratio objectives focus on financial efficiency rather than error tolerance or accuracy in invoice processing.
IIA Standard 2120 – Risk Management (Assessing risk tolerance in financial processes)
IIA Standard 2210 – Engagement Objectives (Evaluating process performance against defined thresholds)
IIA Standard 2130 – Compliance (Ensuring adherence to financial control policies)
Step-by-Step Justification:IIA References for This Answer:Thus, the best answer is A. A KPI that defines the process owner's tolerance for performance deviations, as it directly helps the auditor assess the materiality of the 3% error rate in accounts payable.
For which of the following scenarios would the most recent backup of the human resources database be the best source of information to use?
Options:
An incorrect program fix was implemented just prior to the database backup.
The organization is preparing to train all employees on the new self-service benefits system.
There was a data center failure that requires restoring the system at the backup site.
There is a need to access prior year-end training reports for all employees in the human resources database
Answer:
CExplanation:
The most recent backup is primarily used to restore lost data in the event of a system failure, data corruption, or cyberattack. If a data center failure occurs, the latest backup is the best source to recover the human resources database and resume operations.
(A) Incorrect – An incorrect program fix was implemented just prior to the database backup.
If an incorrect fix was applied before the backup, restoring the latest backup would still contain the error.
The organization would need to restore an earlier version before the faulty update.
(B) Incorrect – The organization is preparing to train all employees on the new self-service benefits system.
The latest backup is not needed for training; the live system or historical data would be used instead.
(C) Correct – There was a data center failure that requires restoring the system at the backup site.
In the event of a system failure, restoring from the most recent backup minimizes data loss and downtime.
This is the primary reason for maintaining regular backups.
(D) Incorrect – There is a need to access prior year-end training reports for all employees in the human resources database.
Historical records would likely be stored in archived backups or reports, not the latest backup.
The most recent backup contains current data, not old reports.
IIA’s GTAG (Global Technology Audit Guide) – IT Disaster Recovery and Backup Strategies
Covers the importance of backups in system restoration.
NIST Cybersecurity Framework – Data Recovery and Business Continuity
Recommends frequent backups to protect against system failures.
ISO 22301 – Business Continuity Management
Defines recovery procedures and best practices for backup site restoration.
Analysis of Answer Choices:IIA References and Internal Auditing Standards:
Which of the following is a limitation of the remote wipe for a smart device?
Options:
Encrypted data cannot be locked to prevent further access
Default settings cannot be restored on the device.
All data, cannot be completely removed from the device
Mobile device management software is required for successful remote wipe
Answer:
CExplanation:
Remote wipe is not always 100% effective: While remote wiping can delete most user data, some residual data may remain on the device, especially in cases where:
The device has built-in storage redundancies.
Deleted data can be recovered using forensic tools.
The remote wipe command fails to execute properly due to network issues or device settings.
Security Risk: This limitation poses a risk for organizations handling sensitive or confidential data, as unauthorized individuals may recover wiped data.
IIA Standard 2110 - Governance: Internal auditors must assess how organizations manage IT security risks, including risks related to mobile devices and data protection.
IIA Practice Guide: Auditing Cybersecurity Risks highlights the need to evaluate mobile security controls and limitations of data removal techniques.
A. Encrypted data cannot be locked to prevent further access (Incorrect)
Encrypted data remains secure even if the device is lost.
Many enterprise security solutions allow organizations to revoke encryption keys remotely, making data inaccessible.
IIA Standard 2120 - Risk Management advises that effective encryption reduces the impact of data loss.
B. Default settings cannot be restored on the device. (Incorrect)
Most remote wipe solutions allow factory reset, restoring the device to default settings.
Many mobile device management (MDM) tools support full device restoration.
D. Mobile device management software is required for a successful remote wipe. (Incorrect)
While MDM enhances remote wiping capabilities, it is not strictly required.
Some consumer and enterprise mobile operating systems (e.g., iOS, Android) provide built-in remote wipe functionality without MDM.
Explanation of Answer Choice C (Correct Answer):Explanation of Incorrect Answers:Conclusion:Remote wipe has limitations, and the inability to completely remove all data from the device (Option C) is a primary concern.
IIA References:
IIA Standard 2110 - Governance
IIA Standard 2120 - Risk Management
IIA Practice Guide: Auditing Cybersecurity Risks
A third party who provides payroll services to the organization was asked to create audit or “read-only 1 functionalities in their systems. Which of the following statements is true regarding this request?
Options:
This will support execution of the right-to-audit clause.
This will enforce robust risk assessment practices
This will address cybersecurity considerations and concerns.
This will enhance the third party's ability to apply data analytics
Answer:
AExplanation:
A right-to-audit clause in a contract allows an organization to review and assess the operations, controls, and security measures of a third-party service provider (such as payroll service providers). Providing "read-only" functionalities supports this clause by enabling internal auditors to access and review relevant data without modifying it.
Read-only access allows auditors to verify transactions, data integrity, and compliance without affecting system operations.
This ensures that internal audit functions can review third-party controls without interference, supporting contractual audit rights.
The IIA’s Standard 2070 – External Service Provider Relationships states that organizations should retain the right to audit outsourced functions to ensure compliance with internal control policies.
B. This will enforce robust risk assessment practices → Incorrect. While read-only access can contribute to risk assessment, it does not directly enforce risk management policies.
C. This will address cybersecurity considerations and concerns. → Incorrect. Cybersecurity concerns involve encryption, authentication, and intrusion detection—not just read-only access.
D. This will enhance the third party's ability to apply data analytics → Incorrect. The request is for audit purposes, not to improve the third party’s analytics capabilities.
IIA’s Global Technology Audit Guide (GTAG) 7: IT Outsourcing recommends a right-to-audit clause in third-party agreements.
IIA Standard 1312 emphasizes that external audits should have transparent access to outsourced functions.
ISACA's COBIT Framework highlights the importance of audit access in managing third-party risks.
Why Option A is Correct?Explanation of the Other Options:IIA References & Best Practices:Thus, the correct answer is A. This will support execution of the right-to-audit clause.
Which of the following statements is most accurate concerning the management and audit of a web server?
Options:
The file transfer protocol (FTP) should always be enabled
The simple mail transfer protocol (SMTP) should be operating under the most privileged accounts
The number of ports and protocols allowed to access the web server should be maximized
Secure protocols for confidential pages should be used instead of clear-text protocols such as HTTP or FTP
Answer:
DExplanation:
In reviewing an organization's IT infrastructure risks, which of the following controls is to be tested as pan of reviewing workstations?
Options:
Input controls
Segregation of duties
Physical controls
Integrity controls
Answer:
CExplanation:
Understanding IT Infrastructure Risks and Workstation Security:
Reviewing an organization’s IT infrastructure risks includes assessing the security of workstations (desktops, laptops, and terminals) that connect to the organization's network.
Workstations are vulnerable to physical theft, unauthorized access, and malware attacks, making physical controls a critical security measure.
Why Physical Controls Are the Most Relevant for Workstations:
Physical controls prevent unauthorized physical access, theft, tampering, and damage to workstations.
Examples include:
Locked office spaces or workstation enclosures to restrict access.
Security badges or biometric authentication to prevent unauthorized use.
Cable locks for laptops and desktop computers to deter theft.
Surveillance cameras and security guards to monitor access.
Why Other Options Are Incorrect:
A. Input controls – Incorrect.
Input controls ensure accuracy and completeness of data entry, which applies more to application security, not workstation security.
B. Segregation of duties – Incorrect.
Segregation of duties prevents fraud and conflicts of interest, but it does not directly address workstation security risks.
D. Integrity controls – Incorrect.
Integrity controls ensure data consistency and accuracy in databases and transactions, not workstation security.
IIA’s Perspective on IT Risk and Physical Security Controls:
IIA Standard 2110 – Governance requires organizations to implement physical security measures for IT assets, including workstations.
IIA GTAG (Global Technology Audit Guide) on IT Risks highlights the importance of restricting physical access to IT devices to prevent unauthorized use or data breaches.
ISO 27001 Information Security Standard recommends physical controls to secure IT infrastructure and prevent workstation-related risks.
IIA References:
IIA Standard 2110 – IT Security & Physical Access Control
IIA GTAG – Physical Security of IT Assets
ISO 27001 – Physical Security and IT Risk Management
Thus, the correct and verified answer is C. Physical controls.
An organization has an agreement with a third-party vendor to have a fully operational facility, duplicate of the original site and configured to the organization's needs, in order to quickly recover operational capability in the event of a disaster, Which of the following best describes this approach to disaster recovery planning?
Options:
Cold recovery plan,
Outsourced recovery plan.
Storage area network recovery plan.
Hot recovery plan
Answer:
DExplanation:
A hot recovery plan (hot site) is a fully operational, duplicate site that is pre-configured and ready for immediate use in case of a disaster. This approach allows an organization to recover critical operations quickly with minimal downtime.
(A) Cold recovery plan.
Incorrect: A cold site is a facility that has infrastructure but no active IT systems or data until set up after a disaster, resulting in longer recovery times.
(B) Outsourced recovery plan.
Incorrect: Outsourcing recovery refers to third-party disaster recovery services, but does not specifically describe a fully operational duplicate site.
(C) Storage area network recovery plan.
Incorrect: A storage area network (SAN) recovery plan focuses on data storage redundancy, not a fully operational duplicate facility.
(D) Hot recovery plan. (Correct Answer)
A hot site is the fastest and most effective disaster recovery solution, ensuring immediate failover with minimal downtime.
IIA GTAG 10 – Business Continuity Management highlights hot sites as the most effective for mission-critical operations.
IIA GTAG 10 – Business Continuity Management: Recommends hot sites for critical recovery scenarios.
IIA Standard 2120 – Risk Management: Emphasizes preparedness for disaster recovery planning.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (D) Hot recovery plan, as it ensures a fully operational backup site for immediate disaster recovery.
What is the primary purpose of an integrity control?
Options:
To ensure data processing is complete, accurate, and authorized
To ensure data being processed remains consistent and intact
To monitor the effectiveness of other controls
To ensure the output aligns with the intended result
Answer:
BExplanation:
An attacker, posing as a bank representative, convinced an employee to release certain, financial information that ultimately resulted in fraud. Which of the following best describes this cybersecurity risk?
Options:
Shoulder suiting
Pharming,
Phishing.
Social engineering.
Answer:
DExplanation:
Social engineering is a psychological manipulation technique used by attackers to trick individuals into divulging sensitive information. Instead of exploiting technical vulnerabilities, it targets human weaknesses such as trust, fear, or urgency.
Manipulates Human Behavior – The attacker impersonates a trusted entity (a bank representative) to deceive the employee.
Leads to Unauthorized Information Disclosure – The employee unknowingly provides sensitive financial data.
Results in Fraud – The stolen information is misused, causing financial loss.
A. Shoulder Surfing – This occurs when an attacker physically observes someone entering sensitive data (e.g., watching a person type a password).
B. Pharming – This involves redirecting users to a fraudulent website to steal their credentials, not direct impersonation.
C. Phishing – This is a broad category of social engineering that typically involves emails or fake websites, whereas this scenario describes a direct impersonation attack.
IIA’s GTAG on Cybersecurity – Discusses social engineering as a key risk for organizations.
NIST SP 800-61 (Incident Handling Guide) – Identifies social engineering as a common attack vector.
COBIT 2019 (IT Governance Framework) – Highlights human-related cybersecurity risks.
Why Social Engineering is the Correct Answer?Why Not the Other Options?IIA References:
Which of the following is classified as a product cost using the variable costing method?
Direct labor costs.
Insurance on a factory.
Manufacturing supplies.
Packaging and shipping costs.
Options:
1 and 2
1 and 3
2 and 4
3 and 4
Answer:
BExplanation:
Comprehensive and Detailed In-Depth Explanation:
Under the variable costing method, only costs that vary directly with production volume are treated as product costs. This includes direct labor costs (the wages of employees directly involved in manufacturing) and manufacturing supplies (materials consumed during production). Insurance on a factory is a fixed overhead cost, and packaging and shipping costs are typically considered period costs or selling expenses, as they are incurred after production. Therefore, options 1 and 3 correctly represent product costs under variable costing.
Which of the following is true regarding reporting on the quality assurance and improvement program (QAIP)?
Options:
The results of ongoing monitoring must be communicated annually to the board and other appropriate stakeholders
The results of any periodic self-assessment and level of conformance with the Global Internal Audit Standards must be reported to the board before completion
The results of any external assessments and level of conformance with the Standards must be reported to the board before completion
The QAIP and the resulting action plan must be made available to external assessors
Answer:
AExplanation:
The CAE must communicate the results of the QAIP, including both ongoing monitoring and periodic assessments, to the board and senior management. Specifically, results of ongoing monitoring must be reported annually, ensuring the board remains informed about the internal audit activity’s quality and conformance.
Options B and C are incorrect because results are reported after completion, not before. Option D is useful for external assessors but not a reporting requirement.
Which of the following scenarios best illustrates a spear phishing attack?
Options:
Numerous and consistent attacks on the company's website caused the server to crash and service was disrupted.
A person posing as a representative of the company's IT help desk called several employees and played a generic prerecorded message requesting password data.
A person received a personalized email regarding a golf membership renewal, and he clicked a hyperlink to enter his credit card data into a fake website.
Many users of a social network service received fake notifications of a unique opportunity to invest in a new product
Answer:
CExplanation:
A spear phishing attack is a targeted email attack aimed at a specific individual, organization, or business. Unlike general phishing, which casts a wide net, spear phishing is highly personalized and designed to deceive the recipient into providing sensitive information.
Personalization – The email references a golf membership renewal, making it relevant and believable to the recipient.
Social Engineering – The attacker exploits the victim’s trust by pretending to be a legitimate entity.
Malicious Link – The victim clicks a fraudulent hyperlink and enters sensitive credit card details.
Financial Fraud – The goal is to steal payment information, leading to unauthorized transactions.
A. Numerous and consistent attacks on the company’s website caused the server to crash.
This describes a Denial-of-Service (DoS) attack, not spear phishing.
B. A person posing as an IT help desk representative called employees and played a generic message requesting passwords.
This describes vishing (voice phishing) rather than spear phishing.
D. Many users of a social network service received fake notifications about a new investment opportunity.
This is general phishing, as it targets multiple users instead of one individual.
IIA’s GTAG (Global Technology Audit Guide) on Cybersecurity – Emphasizes the risk of spear phishing in cyber fraud.
NIST SP 800-61 (Computer Security Incident Handling Guide) – Defines spear phishing as a highly targeted attack method.
COBIT 2019 (Governance and Management of IT) – Highlights social engineering risks in IT security.
Why Option C is Correct?Why Not the Other Options?IIA References:✅ Final Answer: C. A person received a personalized email regarding a golf membership renewal, and he clicked a hyperlink to enter his credit card data into a fake website.
Which of the following actions is likely to reduce the risk of violating transfer pricing regulations?
Options:
The organization sells inventory to an overseas subsidiary at fair value.
The local subsidiary purchases inventory at a discounted price.
The organization sells inventory to an overseas subsidiary at the original cost.
The local subsidiary purchases inventory at the depreciated cost.A
Answer:
AExplanation:
Transfer pricing regulations aim to prevent tax evasion and ensure that intercompany transactions reflect fair market value, preventing profit shifting to low-tax jurisdictions. Selling inventory at fair value (arm’s length price) aligns with regulatory requirements, reducing the risk of non-compliance.
(A) Correct – The organization sells inventory to an overseas subsidiary at fair value.
Ensuring that transactions reflect fair market value prevents regulatory violations.
Adhering to the arm’s length principle minimizes transfer pricing risks and potential tax penalties.
(B) Incorrect – The local subsidiary purchases inventory at a discounted price.
A discounted price could be seen as an attempt to shift profits between entities, increasing regulatory scrutiny.
(C) Incorrect – The organization sells inventory to an overseas subsidiary at the original cost.
Selling at the original cost does not account for market conditions, potential markup, and fair valuation.
Regulators may view this as non-compliance with the arm’s length principle.
(D) Incorrect – The local subsidiary purchases inventory at the depreciated cost.
Depreciated cost may not represent fair market value and could be interpreted as a tax avoidance mechanism.
IIA’s Global Internal Audit Standards – Compliance with Tax and Transfer Pricing Regulations
Emphasizes fair pricing in intercompany transactions to prevent regulatory violations.
OECD Transfer Pricing Guidelines
Reinforces the arm’s length principle as the standard for pricing related-party transactions.
COSO’s ERM Framework – Compliance Risk Management
Highlights the need for adherence to tax laws and fair-value pricing in financial transactions.
Analysis of Answer Choices:IIA References and Internal Auditing Standards:
Capital budgeting involves choosing among various capital projects to find the one(s) that will maximize a company's return on its financial investment. Which of the following parties approves the capital budget?
Options:
Board of directors.
Senior management.
Chief financial officer.
Accounting personnel.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
Capital budgeting involves long-term investment decisions, such as purchasing new equipment, expanding facilities, or launching new products. These strategic financial decisions require approval at the highest level of governance.
The Board of Directors (Option A) is responsible for reviewing and approving capital budgets, ensuring alignment with corporate strategy.
Senior management (Option B) and the CFO (Option C) contribute by evaluating proposals, but they typically do not have final approval authority.
Accounting personnel (Option D) manage financial reporting but do not approve budgets.
Thus, the Board of Directors (A) is the correct answer.
Several organizations have developed a strategy to open co-owned shopping malls. What would be the primary purpose of this strategy?
Options:
To exploit core competence.
To increase market synergy.
To deliver enhanced value.
To reduce costs.
Answer:
BExplanation:
When multiple organizations co-own shopping malls, their primary strategy is to increase market synergy, meaning they combine resources and expertise to enhance market presence, attract more customers, and improve competitive positioning.
(A) To exploit core competence.
Incorrect: Core competencies refer to unique internal capabilities, whereas co-owning shopping malls is a collaborative market strategy.
(B) To increase market synergy. (Correct Answer)
Market synergy occurs when businesses collaborate to create greater market impact than they could individually.
Shared ownership enhances customer traffic, brand reach, and business opportunities.
IIA Standard 2110 – Governance highlights the importance of strategic partnerships in achieving synergy.
(C) To deliver enhanced value.
Incorrect: While value is a benefit, the main goal of co-ownership is strategic market advantage and synergy.
(D) To reduce costs.
Incorrect: Cost reduction may be a secondary benefit, but the primary goal is market synergy through shared resources and customer base expansion.
IIA Standard 2110 – Governance: Encourages strategic collaborations for business growth.
COSO ERM – Strategy and Objective-Setting: Highlights market synergy as a key factor in strategic partnerships.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (B) because co-ownership of shopping malls primarily aims to increase market synergy, allowing organizations to leverage shared resources and customer networks for greater market impact.
Which of the following is the most appropriate beginning step of a work program for an assurance engagement involving smart devices?
Options:
Train all employees on bring-your-own-device (BYOD) policies.
Understand what procedures are in place for locking lost devices
Obtain a list of all smart devices in use
Test encryption of all smart devices
Answer:
CExplanation:
In an assurance engagement involving smart devices, the first step is to obtain a comprehensive inventory of all devices in use. This ensures that the audit covers all relevant assets and allows the internal auditor to assess risks, controls, and policies effectively.
(A) Incorrect – Train all employees on bring-your-own-device (BYOD) policies.
While employee training is important, it is a control measure rather than the first step in an assurance engagement.
Without an inventory of devices, training effectiveness cannot be assessed.
(B) Incorrect – Understand what procedures are in place for locking lost devices.
This is a specific control measure but not the starting point for an engagement.
The first step should be to identify what devices exist before evaluating security measures.
(C) Correct – Obtain a list of all smart devices in use.
The foundation of an assurance engagement is identifying the scope, which includes listing all smart devices in use.
This allows the auditor to evaluate security risks, compliance, and control measures effectively.
(D) Incorrect – Test encryption of all smart devices.
Testing encryption is an audit procedure that should be performed after understanding the inventory and existing controls.
Without knowing which devices exist, encryption testing would not be effective.
IIA’s Global Internal Audit Standards – Technology Assurance and Cybersecurity Audits
Outlines steps for conducting technology-related assurance engagements.
IIA’s GTAG (Global Technology Audit Guide) on Auditing Smart Devices
Recommends obtaining an inventory of devices as the first step in an audit.
COBIT Framework – IT Asset Management and Control
Emphasizes identifying assets as the foundation of IT governance and risk management.
Analysis of Answer Choices:IIA References and Internal Auditing Standards:
A new manager received computations of the internal rate of return regarding his project proposal. What should the manager compare the computation results to in order to determine whether the project is potentially acceptable?
Options:
Compare to the annual cost of capital.
Compare to the annual interest rate.
Compare to the required rate of return.
Compare to the net present value.
Answer:
CExplanation:
Comprehensive and Detailed In-Depth Explanation:
The Internal Rate of Return (IRR) is the discount rate that makes the net present value (NPV) of a project equal to zero. It is used to evaluate the profitability of investments.
Option A (Annual cost of capital) – While related, the IRR should be compared directly to the required rate of return (hurdle rate).
Option B (Annual interest rate) – Not always relevant, as the cost of borrowing may differ from the required return on investments.
Option D (Compare to NPV) – NPV is a different method of capital budgeting; while related, it is not used for direct comparison with IRR.
Since the IRR is accepted if it meets or exceeds the required rate of return, Option C is correct.
A motivational technique generally used to overcome monotony and job-related boredom is:
Options:
Job specification.
Job objectives.
Job rotation.
Job description.
Answer:
CExplanation:
Comprehensive and Detailed In-Depth Explanation:
Job rotation involves periodically moving employees between different tasks, roles, or departments to increase engagement, reduce boredom, and enhance skill development.
Option A (Job specification) – Defines job responsibilities but does not address boredom.
Option B (Job objectives) – Focuses on performance goals rather than task variety.
Option D (Job description) – Simply documents job roles without changing daily tasks.
Thus, job rotation (Option C) is the most effective strategy for overcoming monotony and job-related boredom.
An investor has acquired an organization that has a dominant position in a mature. slew-growth Industry and consistently creates positive financial income.
Which of the following terms would the investor most likely label this investment in her portfolio?
Options:
A star
A cash cow
A question mark
A dog
Answer:
BExplanation:
Understanding the BCG Matrix and Investment Classifications:
The Boston Consulting Group (BCG) Matrix classifies business investments into four categories:
Stars: High growth, high market share.
Cash Cows: Low growth, high market share.
Question Marks: High growth, low market share.
Dogs: Low growth, low market share.
Why the Investment is a Cash Cow:
The organization operates in a mature, slow-growth industry but has a dominant market position and generates consistent positive financial income.
This aligns with the definition of a Cash Cow, as it represents a stable and profitable business with low reinvestment needs.
Investors typically use Cash Cows to fund other investments, as they generate steady cash flow with minimal risk.
Why Other Options Are Incorrect:
A. A star:
A Star requires high growth and high market share, but the organization operates in a slow-growth industry, disqualifying it from this category.
C. A question mark:
A Question Mark is in a high-growth industry but lacks market dominance. Since this company is already dominant, it does not fit this category.
D. A dog:
A Dog has low growth and low market share, meaning it does not generate strong financial returns. The company described produces positive income, ruling out this category.
IIA’s Perspective on Business Strategy and Portfolio Management:
IIA Standard 2120 – Risk Management states that internal auditors must assess the strategic positioning of business investments.
COSO ERM Framework supports the use of strategic models like the BCG Matrix to evaluate investment performance and risk exposure.
IIA References:
IIA Standard 2120 – Risk Management and Strategic Planning
COSO Enterprise Risk Management (ERM) Framework
Boston Consulting Group (BCG) Matrix in Investment Analysis
Thus, the correct and verified answer is B. A cash cow.
According to IIA guidance on IT, which of the following would be considered a primary control for a spreadsheet to help ensure accurate financial reporting?
Options:
Formulas and static data are locked or protected.
The spreadsheet is stored on a network server that is backed up daily.
The purpose and use of the spreadsheet are documented.
Check-in and check-out software is used to control versions.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
Primary controls in spreadsheet management focus on ensuring data accuracy, integrity, and security.
Option A (Locking formulas and static data) prevents unauthorized changes, ensuring data integrity. This is a direct control over spreadsheet accuracy, making it the correct answer.
Option B (Backup storage) is an IT operational control, not a primary financial reporting control.
Option C (Documentation of spreadsheet use) is important for governance but does not directly prevent errors.
Option D (Version control software) helps manage changes but does not directly ensure financial reporting accuracy.
Thus, locking and protecting spreadsheet formulas is the most critical primary control for accurate financial reporting.
With regard to project management, which of the following statements about project crashing Is true?
Options:
It leads to an increase in risk and often results in rework.
It is an optimization technique where activities are performed in parallel rather than sequentially.
It involves a revaluation of project requirements and/or scope.
It is a compression technique in which resources are added so the project.
Answer:
DExplanation:
Definition of Project Crashing:
Project crashing is a schedule compression technique used in project management to reduce the project completion time without changing its scope.
It involves adding extra resources (labor, equipment, budget) to critical path activities to complete them faster.
Key Aspects of Project Crashing:
Reduces project duration by increasing resources.
Leads to higher costs due to additional labor or expedited material procurement.
Used when project deadlines must be met and standard scheduling techniques are insufficient.
Why Other Options Are Incorrect:
A. It leads to an increase in risk and often results in rework:
While crashing can increase costs and risk, it does not necessarily result in rework unless poorly executed.
B. It is an optimization technique where activities are performed in parallel rather than sequentially:
This describes fast-tracking, not crashing. Fast-tracking involves overlapping tasks, while crashing adds resources to speed up tasks.
C. It involves a revaluation of project requirements and/or scope:
Crashing does not change project scope; it only shortens the schedule by allocating additional resources.
IIA’s Perspective on Project Risk and Management:
IIA Standard 2110 – Governance emphasizes the importance of project risk assessment, including schedule compression risks.
COSO ERM Framework identifies project cost overruns and resource misallocations as key risks in project execution.
PMBOK (Project Management Body of Knowledge) defines crashing as a schedule compression technique used when deadlines must be met at additional cost.
IIA References:
IIA Standard 2110 – Governance & Risk Oversight in Project Management
COSO Enterprise Risk Management (ERM) – Project Risk Considerations
PMBOK Guide – Schedule Compression Techniques (Crashing & Fast-Tracking)
Thus, the correct and verified answer is D. It is a compression technique in which resources are added so the project is completed faster.
When preparing the annual internal audit plan, which of the following should the chief audit executive (CAE) consider to optimize efficiency and effectiveness?
Options:
The CAE should review the objectives and scope of the external audit plan and consider including audits with the same objectives and scope to ensure thorough coverage of the area
The CAE should review the audit plan prepared by the compliance department and coordinate any audits in the same areas to reduce duplication of objectives and minimize disruption to the area under review
The CAE should avoid reviewing plans by internal or external assurance providers to increase effectiveness and reduce bias in internal audit selection
The CAE should review operational quality assurance audit plans, place reliance on the areas covered, and exclude those areas from final consideration in the annual internal audit plan
Answer:
BExplanation:
To optimize efficiency, the CAE should coordinate with other assurance providers such as compliance, quality assurance, and external auditors. This reduces duplication, minimizes disruption, and ensures resources are used effectively.
Option A may lead to unnecessary duplication rather than coordination. Option C contradicts IIA guidance, which emphasizes coordination (Standard 2050). Option D excludes areas entirely, which is inappropriate because internal audit must still assess whether reliance is valid.
A chief audit executive (CAE) is calculating the available internal audit resource hours while planning the annual internal audit plan. The CAE needs to calculate the total number of hours available for audits. Which of the following should be deducted in order to have time available only for engagements?
Options:
Time spent on coaching the internal audit function on new engagement procedures
Time spent on the preliminary risk assessment of the engagement
Time spent for the documentation of supporting files for the engagement
Time spent on reporting the results of the engagement
Answer:
AExplanation:
When calculating available audit hours, the CAE must exclude non-engagement activities such as administration, meetings, professional development, and staff coaching. These are essential but not directly part of engagement execution.
Preliminary risk assessment (Option B), documentation (Option C), and reporting (Option D) are all integral steps of an engagement and should be included in engagement hours. Thus, only coaching time (Option A) should be deducted.
Which of the following is a sound network configuration practice to enhance information security?
Options:
Change management practices to ensure operating system patch documentation is retained.
User role requirements are documented in accordance with appropriate application-level control needs.
Validation of intrusion prevention controls is performed to ensure intended functionality and data integrity.
Interfaces reinforce segregation of duties between operations administration and database development.
Answer:
CExplanation:
A sound network configuration practice should focus on enhancing security, preventing unauthorized access, and ensuring data integrity. The validation of intrusion prevention controls ensures that the network security measures function as intended and effectively protect data from threats.
(A) Change management practices to ensure operating system patch documentation is retained.
Incorrect: While maintaining patch documentation is important, change management alone does not directly enhance network security.
(B) User role requirements are documented in accordance with appropriate application-level control needs.
Incorrect: This practice improves access control and governance, but it is not a direct network security configuration practice.
(C) Validation of intrusion prevention controls is performed to ensure intended functionality and data integrity. (Correct Answer)
Intrusion Prevention Systems (IPS) help detect and prevent malicious activities in real time.
Ensuring proper validation enhances security and prevents data corruption.
IIA GTAG 15 – Information Security Governance recommends continuous monitoring and validation of security controls.
(D) Interfaces reinforce segregation of duties between operations administration and database development.
Incorrect: Segregation of duties is a good governance practice, but it does not directly relate to network security configuration.
IIA GTAG 15 – Information Security Governance: Recommends validating security controls, including intrusion prevention systems.
IIA Standard 2120 – Risk Management: Encourages proactive security controls to prevent cyber threats.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (C) Validation of intrusion prevention controls, as it directly enhances information security by ensuring real-time threat detection and data integrity.
According to IIA guidance on IT, which of the following best describes a situation where data backup plans exist to ensure that critical data can be restored at some point in the future, but recovery and restore processes have not been defined?
Options:
Hot recovery plan
Warm recovery plan
Cold recovery plan
Absence of recovery plan
Answer:
DExplanation:
A disaster recovery plan (DRP) ensures that critical systems and data can be restored after an incident. If backup plans exist but no recovery and restore processes are defined, then the organization lacks a functional recovery plan altogether.
(A) Hot recovery plan.
Incorrect. A hot recovery plan includes real-time data replication and immediate failover systems, allowing for almost instant recovery in case of an outage. Since the scenario mentions that no restore process is defined, this cannot be a hot recovery plan.
(B) Warm recovery plan.
Incorrect. A warm recovery plan involves regular backups and a standby system that can be activated within hours or days. However, without defined restore procedures, the organization does not even have a warm recovery plan.
(C) Cold recovery plan.
Incorrect. A cold recovery plan means that backups exist but recovery takes significant time because systems and infrastructure need to be rebuilt. However, a cold plan still includes a recovery process, which the scenario lacks.
(D) Absence of recovery plan. ✅
Correct. If data backup plans exist but no restore processes are defined, then there is no functional recovery plan. Without a structured approach to data recovery, backups alone are useless in an actual disaster scenario.
IIA GTAG "Business Continuity and Disaster Recovery" highlights the need for detailed recovery processes as part of an overall disaster recovery plan.
IIA GTAG – "Business Continuity and Disaster Recovery"
IIA Standard 2120 – Risk Management
COBIT Framework – IT Disaster Recovery Controls
Analysis of Answer Choices:IIA References:Thus, the correct answer is D, as data backups without recovery procedures indicate the absence of a recovery plan.
Which of the following physical access controls is most likely to be based on the "something you have" concept?
Options:
A retina characteristics reader.
A PIN code reader.
A card-key scanner.
A fingerprint scanner.
Answer:
CExplanation:
Comprehensive and Detailed In-Depth Explanation:
Authentication methods are categorized into three factors:
Something you know (e.g., passwords, PINs).
Something you have (e.g., ID cards, key fobs, smart cards).
Something you are (e.g., biometrics like fingerprints, retina scans).
Option C (A card-key scanner) aligns with "something you have", as it requires a physical token (card) for authentication.
Option A (Retina scan) and Option D (Fingerprint scanner) fall under biometric authentication ("something you are").
Option B (PIN code reader) is based on "something you know".
Thus, C is the correct answer because a card-key represents a physical access control mechanism based on possession.
Which of the following best describes meaningful recommendations for corrective actions?
Options:
Recommendations that address the gap between the condition and consequence and provide at least short-term fixes
Recommendations that address the gap between the criteria and condition and provide at least short-term fixes
Recommendations that address the gap between the criteria and consequence and provide long-term solutions
Recommendations that address the gap between the criteria and condition and provide long-term solutions
Answer:
DExplanation:
Meaningful recommendations are those that address the root cause of the condition by comparing it to the established criteria and propose sustainable, long-term solutions. This ensures that the identified issue will not recur and strengthens the control environment.
Option A relates to symptoms (condition vs. consequence), not root causes. Option B identifies the correct gap (criteria vs. condition) but offers only short-term fixes. Option C incorrectly compares criteria to consequence, which is not a valid basis for audit recommendations.
Thus, Option D is correct.
Which of the following statements is true regarding change management?
Options:
The degree of risk associated with a proposed change determines whether the change request requires authorization
Program changes generally are developed and tested in the production environment.
Changes are only required by software programs
To protect the production environment, changes must be managed in a repeatable, defined, and predictable manner
Answer:
DExplanation:
Change management is a structured approach to transitioning individuals, teams, and organizations from a current state to a desired future state while minimizing risk and disruption.
Definition of Change Management:
Change management ensures that all modifications to IT systems, processes, and applications are controlled and documented.
As per the IIA GTAG on Change Management, an effective change management process should be repeatable, defined, and predictable to reduce errors and system failures.
Why Change Management Must Be Structured?
Uncontrolled changes increase risks such as security vulnerabilities, data loss, and system downtime.
Best practices (e.g., ITIL, COBIT) require organizations to follow a consistent change management process to protect the production environment.
A structured approach includes:
Documenting change requests
Testing in non-production environments
Gaining approvals before deployment
Why Not Other Options?
A. The degree of risk associated with a proposed change determines whether the change request requires authorization:
All changes should require authorization, not just high-risk ones.
B. Program changes generally are developed and tested in the production environment:
Changes should never be tested in production due to risk exposure. Best practice is to test in a development or staging environment first.
C. Changes are only required by software programs:
Change management applies broadly to IT infrastructure, business processes, security protocols, and governance frameworks, not just software.
IIA GTAG – Change Management Controls
COBIT 2019 – Change Management Best Practices
ITIL Change Management Framework
IIA Standard 2120 – Risk Management
Step-by-Step Justification:IIA References:Thus, the correct and verified answer is D. To protect the production environment, changes must be managed in a repeatable, defined, and predictable manner.
The head of the research and development department at a manufacturing organization believes that his team lacks expertise in some areas and decides to hire more experienced researchers to assist in the development of a new product. Which of the following variances are likely to occur as the result of this decision?
Favorable labor efficiency variance
Adverse labor rate variance
Adverse labor efficiency variance
Favorable labor rate variance
Options:
1 and 2.
1 and 4.
3 and 4.
2 and 3.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
A favorable labor efficiency variance (Option 1) occurs because experienced workers complete tasks more efficiently, reducing time and waste.
An adverse labor rate variance (Option 2) arises because hiring experienced employees increases labor costs compared to budgeted rates.
Option 3 (Adverse labor efficiency variance) is incorrect because skilled workers typically improve efficiency.
Option 4 (Favorable labor rate variance) is incorrect because higher wages increase costs, leading to an adverse variance.
Thus, the correct answer is A (1 and 2 only).
According to IIA guidance, whose input must be considered when developing the annual internal audit plan?
Options:
Operational management
External auditors
The CEO
Internal assurance providers
Answer:
DExplanation:
When developing the annual internal audit plan, the CAE must consider input from senior management, the board, and other internal assurance providers to ensure coordination and avoid duplication of efforts. While operational management, external auditors, and the CEO may also provide input, IIA Standards emphasize coordination with internal assurance providers as a mandatory step.
Which statement is true regarding the development of a risk-based internal audit plan?
Options:
It requires a previously conducted assurance engagement on the organization’s risk management maturity
It requires an assessment by the internal audit function of key risks identified within the organization's risk management system
It requires that at least 90% of planned engagements address areas critical to the organization's strategy
It requires that an organization adheres to a well-recognized risk management framework in order to identify and manage its risks
Answer:
BExplanation:
A risk-based audit plan must be aligned with the organization’s objectives and risk management system. According to the Standards, the CAE must consider the organization’s risk management framework and assess key risks to develop the plan. A maturity review (Option A) is not a prerequisite, nor is a mandated percentage of strategic coverage (Option C). Option D is incorrect because an organization does not need to follow a specific external framework to develop a risk-based plan; internal risk identification suffices.
Which of the following actions should an internal auditor take to clean the data obtained for analytics purposes?
Options:
Deploys data visualization tool.
Adopt standardized data analysis software.
Define analytics objectives and establish outcomes.
Eliminate duplicate records.
Answer:
DExplanation:
Data cleaning (also called data cleansing or scrubbing) is a critical step in data analytics to ensure accuracy, consistency, and reliability. Removing duplicate records is a key data cleaning technique that improves data quality.
Improves Data Integrity – Prevents misleading results caused by duplicate values.
Enhances Data Accuracy – Ensures that analytics are based on unique and valid information.
Optimizes Performance – Reduces redundancy, improving processing speed and efficiency.
Prevents Reporting Errors – Ensures accurate insights for decision-making.
A. Deploys data visualization tool – Visualization tools help interpret data but do not clean it.
B. Adopt standardized data analysis software – Software tools support analysis but do not eliminate duplicate records automatically.
C. Define analytics objectives and establish outcomes – This step is important for analysis strategy, but it does not clean data.
IIA’s GTAG on Data Analytics – Emphasizes the importance of data cleansing in ensuring reliable analytics.
COBIT 2019 (Data Management Framework) – Highlights duplicate removal as a best practice in data governance.
ISO 8000-110 (Data Quality Standard) – Recommends eliminating duplicate records for high-quality analytics.
Why Eliminating Duplicate Records is the Correct Answer?Why Not the Other Options?IIA References:✅ Final Answer: D. Eliminate duplicate records.
Which of the following is a primary driver behind the creation and prioritization of new strategic initiatives established by an organization?
Options:
Risk tolerance.
Performance.
Threats and opportunities.
Governance.
Answer:
CExplanation:
Comprehensive and Detailed In-Depth Explanation:
Strategic initiatives are established to address emerging threats and opportunities in the business environment. Organizations continuously evaluate external and internal factors to remain competitive and mitigate risks.
Option A (Risk tolerance) influences strategy, but it is not the primary driver for creating new initiatives.
Option B (Performance) is an outcome rather than a primary driver.
Option D (Governance) provides structure but does not directly drive the need for new initiatives.
Since businesses prioritize initiatives in response to external threats and internal opportunities, option C is the correct answer.
According to 11A guidance on IT, which of the following spreadsheets is most likely to be considered a high-risk user-developed application?
Options:
A revenue calculation spreadsheet supported with price and volume reports from the production department.
An asset retirement calculation spreadsheet comprised of multiple formulas and assumptions.
An ad-hoc inventory listing spreadsheet comprising details of written-off inventory quantities.
An accounts receivable reconciliation spreadsheet used by the accounting manager to verify balances
Answer:
BExplanation:
A high-risk user-developed application (UDA) refers to spreadsheets or other tools created and maintained by end-users (not IT) that are critical to financial reporting, decision-making, or regulatory compliance. The IIA guidance on IT risk management emphasizes evaluating the complexity, significance, and control environment of such applications.
(A) Revenue Calculation Spreadsheet
Uses price and volume reports from production, meaning it relies on structured, external sources, reducing the risk of significant undetected errors.
Less complexity and external verification reduce its risk level.
(B) Asset Retirement Calculation Spreadsheet (Correct Answer)
Contains multiple formulas and assumptions, making it complex and prone to errors.
Assumptions introduce subjectivity and risk of incorrect calculations, affecting financial statements and compliance.
No automated controls or independent validations, making it a high-risk UDA.
IIA Standard 2110 – Governance and GTAG 14 (Auditing User-Developed Applications) emphasize assessing high-risk spreadsheets that impact financial decision-making.
(C) Ad-Hoc Inventory Listing Spreadsheet
Used for written-off inventory, which is historical data and not a key financial driver.
Limited impact on financial reporting, making it a low-risk UDA.
(D) Accounts Receivable Reconciliation Spreadsheet
Used by the accounting manager to verify balances, likely cross-checked with ERP or other financial systems.
Since external reconciliation exists, the spreadsheet does not pose a high inherent risk.
GTAG 14 (Auditing User-Developed Applications) – Identifies UDAs with complex formulas, financial impact, and lack of controls as high-risk.
IIA Standard 2110 (Governance) – Internal auditors must assess governance around financial and operational risk management, including IT risks.
IIA Standard 2120 (Risk Management) – Emphasizes identifying and mitigating risks from user-developed applications.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (B) Asset Retirement Calculation Spreadsheet, as it aligns with IIA guidance on high-risk spreadsheets due to complex formulas, assumptions, and potential financial misstatements.
Through meetings with management, an organization's chief audit executive (CAE) learns of a risk that exceeds the established risk tolerance. What would be an appropriate next action for the CAE to take?
Options:
Design and recommend an appropriate response to the risk
Discuss the risk and the implications of the risk with management responsible for the risk area
Schedule an audit of the risk area to assess the risk likelihood and impact
Prepare a memo to report the risk to the board
Answer:
BExplanation:
The CAE should first discuss the risk and its implications with the responsible management. This provides management the opportunity to reassess, take corrective action, or explain their position. If the issue remains unresolved and the risk is still deemed excessive, then escalation to senior management or the board may follow.
Option A (designing response) is management’s role. Option C (scheduling an audit) may be relevant later, but immediate discussion is the first step. Option D is premature without first engaging management.
Which of the following controls would an internal auditor consider the most relevant to reduce risks of project cost overruns?
Options:
Scope change requests are reviewed and approved by a manager with a proper level of authority.
Cost overruns are reviewed and approved by a control committee led by the project manager.
There is a formal quality assurance process to review scope change requests before they are implemented
There is a formal process to monitor the status of the project and compare it to the cost baseline
Answer:
DExplanation:
Understanding Project Cost Overruns and Controls
Cost overruns occur when actual project costs exceed the budgeted or planned costs. Effective controls are required to prevent, detect, and correct deviations from the cost baseline.
The most effective way to control cost overruns is through continuous monitoring and comparison of project costs against the approved cost baseline.
Why Option D is Correct?
A formal process to monitor the project status and compare it to the cost baseline ensures that deviations are identified early and corrective actions are taken.
This aligns with the IIA's International Standards for the Professional Practice of Internal Auditing (IPPF), specifically:
Standard 2120 – Risk Management: Internal auditors must evaluate how organizations manage risks, including financial risks related to project cost overruns.
Standard 2500 – Monitoring Progress: Ensures that corrective actions are implemented when issues arise.
IIA Practice Advisory 2130-1: Stresses the importance of monitoring activities to mitigate financial risks.
The Project Management Body of Knowledge (PMBOK) also supports cost monitoring as a key control to prevent overruns.
Why Other Options Are Incorrect?
Option A: Reviewing and approving scope change requests is important, but it does not directly monitor or control cost overruns. Scope creep is a risk, but cost monitoring is a more direct control.
Option B: Having a control committee review overruns after they occur is a reactive measure. Proactive monitoring (option D) is more effective.
Option C: A quality assurance process for scope changes is valuable but does not directly prevent cost overruns. It focuses on project quality rather than financial control.
Effective internal controls for cost management emphasize real-time monitoring and comparison against the cost baseline to prevent and mitigate cost overruns.
IIA Standards 2120, 2500, and 2130-1 support proactive risk management and monitoring as essential best practices for internal auditors.
Final Justification:IIA References:
IPPF Standard 2120 – Risk Management
IPPF Standard 2500 – Monitoring Progress
IIA Practice Advisory 2130-1 – Internal Control and Risk Management
PMBOK – Cost Monitoring and Control
c
Which of the following scenarios would cause a chief audit executive (CAE) to immediately discontinue using any statements that would indicate conformance with the Global Internal Audit Standards in an audit report?
Options:
The internal audit function used a risk-based approach to create the internal audit plan
The engagement supervisor considered requests from senior management regarding engagements to include in the internal audit plan
The CAE only accepted engagements that the internal audit function collectively had the knowledge to perform
The activity under review restricted the internal audit function's ability to access records, impacting the audit results
Answer:
DExplanation:
The Global Internal Audit Standards require unrestricted access to records, personnel, and information. If access is restricted in such a way that audit results are compromised, the CAE cannot claim conformance with the Standards in any report until the issue is resolved.
Options A, B, and C are all in alignment with the Standards and do not affect conformance. Only restriction of access (Option D) requires immediate discontinuation of conformance claims.
A small software development firm designs and produces custom applications for businesses. The application development team consists of employees from multiple departments who all report to a single project manager. Which of the following organizational structures does this situation represent?
Options:
Functional departmentalization.
Product departmentalization
Matrix organization.
Divisional organization
Answer:
CExplanation:
Understanding Organizational Structures:
Organizations structure their workforce based on functions, products, or a combination of both.
A matrix organization combines functional and project-based structures, where employees report to both a functional manager and a project manager.
Why Option C (Matrix Organization) Is Correct?
The software development firm uses employees from multiple departments who report to a single project manager, which is a defining characteristic of a matrix structure.
Employees maintain their departmental roles while contributing to project-based work.
IIA Standard 2110 – Governance supports evaluating flexible organizational structures like matrix organizations to ensure accountability and risk management.
Why Other Options Are Incorrect?
Option A (Functional departmentalization):
In functional structures, employees report to one department head, not a project manager.
Option B (Product departmentalization):
In product-based structures, employees are grouped based on specific product lines, not cross-functional projects.
Option D (Divisional organization):
A divisional structure separates business units based on markets, regions, or customer segments, not cross-functional teams.
A matrix organization allows employees to work across departments under a project manager, making option C the best choice.
IIA Standard 2110 supports assessing governance structures that involve cross-functional teams.
Final Justification:IIA References:
IPPF Standard 2110 – Governance (Organizational Structures & Reporting Lines)
COSO ERM – Risk Management in Matrix Organizations
Project Management Institute (PMI) – Matrix Management Best Practices
Focus An organization has decided to have all employees work from home. Which of the following network types would securely enable this approach?
Options:
A wireless local area network (WLAN ).
A personal area network (PAN).
A wide area network (WAN).
A virtual private network (VPN)
Answer:
DExplanation:
When employees work from home, secure remote access to the organization's network is essential to protect data and ensure confidentiality. A Virtual Private Network (VPN) is the best option for enabling this securely.
Correct Answer (D - A Virtual Private Network (VPN))
A VPN creates a secure, encrypted connection between the employee's device and the organization’s internal network.
It prevents unauthorized access by ensuring that data is transmitted securely over the internet.
The IIA GTAG 17: Auditing Network Security recommends VPNs for secure remote work environments to prevent cyber threats.
Why Other Options Are Incorrect:
Option A (A Wireless Local Area Network - WLAN):
A WLAN is used within an office or home environment, but it does not provide secure remote access to an organization's network.
Option B (A Personal Area Network - PAN):
A PAN connects devices like smartphones and laptops within a short range (e.g., Bluetooth), but it is not suitable for secure remote access.
Option C (A Wide Area Network - WAN):
A WAN connects multiple locations, but it does not provide encryption or remote security like a VPN.
IIA GTAG 17: Auditing Network Security – Recommends VPNs for secure remote access.
IIA Practice Guide: Auditing IT Security Controls – Covers VPNs as a key security control for remote work.
Step-by-Step Explanation:IIA References for Validation:Thus, D is the correct answer because a VPN ensures secure, encrypted communication for employees working from home.
Which of the following characteristics applies to an organization that adopts a flat structure?
Options:
The structure is dispersed geographically
The hierarchy levels are more numerous.
The span of control is wide
The tower-level managers are encouraged to exercise creativity when solving problems
Answer:
CExplanation:
A flat organizational structure is characterized by fewer hierarchical levels and wider spans of control, meaning that managers oversee a larger number of employees directly.
Definition of a Flat Structure:
A flat structure reduces middle management layers, promoting direct communication between top executives and employees.
According to IIA’s Organizational Governance Guidelines, organizations with a flat structure empower employees and reduce bureaucratic delays.
Key Characteristics of a Flat Structure:
Wide Span of Control: Managers oversee more employees due to fewer hierarchical levels.
Faster Decision-Making: Less bureaucracy allows for quicker responses.
Greater Employee Autonomy: Employees have more decision-making responsibilities.
Why Not Other Options?
A. The structure is dispersed geographically:
A geographically dispersed organization is not necessarily flat; it could be hierarchical or matrix-based.
B. The hierarchy levels are more numerous:
Flat structures have fewer levels, while tall structures have numerous levels.
D. The lower-level managers are encouraged to exercise creativity when solving problems:
While creativity may be encouraged, this is not a defining feature of a flat structure.
IIA Practice Guide: Organizational Governance
IIA Standard 2110 – Governance
Step-by-Step Justification:IIA References:Thus, the correct and verified answer is C. The span of control is wide.
Which of the following is a key performance indicator of the efficiency of the internal audit function?
Options:
The number of audits completed
The number of significant audit observations
The percentage of recommendations implemented
The number of training hours per auditor
Answer:
AExplanation:
Efficiency indicators measure how well resources are used to produce outputs. The number of audits completed reflects efficiency because it shows how effectively the internal audit function utilizes available resources to deliver its plan.
Option B (observations) reflects risk exposure, not efficiency. Option C measures effectiveness (impact of audit work), not efficiency. Option D reflects investment in staff development, not operational efficiency.
Which of the following statements is true regarding the term "flexible budgets" as it is used in accounting?
Options:
The term describes budgets that exclude fixed costs.
Flexible budgets exclude outcome projections, which are hard to determine, and instead rely on the most recent actual outcomes.
The term is a red flag for weak budgetary control activities.
Flexible budgets project data for different levels of activity.
Answer:
DExplanation:
Definition of Flexible Budgets:
Flexible budgeting allows organizations to adjust budgeted expenses based on actual performance levels.
Unlike static budgets, flexible budgets provide different financial projections for varying levels of activity.
Why Flexible Budgets are Useful:
They adjust for actual business conditions, making them useful in planning and cost control.
Organizations can compare actual results against the appropriate budget level rather than a single static budget.
Why Other Options Are Incorrect:
A. Exclude fixed costs: Fixed costs are included; only variable costs change with activity levels.
B. Exclude outcome projections: Flexible budgets still use projected outcomes but adjust them based on actual performance.
C. Red flag for weak control: Flexible budgets enhance control by allowing real-time adjustments, making them a best practice rather than a red flag.
IIA GTAG on Financial Management: Covers budgeting methods, including flexible budgeting.
IIA Standard 2120 – Risk Management: Encourages adaptive financial planning for effective risk management.
COSO ERM Framework: Recommends dynamic financial planning, including flexible budgeting.
Relevant IIA References:✅ Final Answer: Flexible budgets project data for different levels of activity (Option D).
Which of the following is a systems software control?
Options:
Restricting server room access to specific individuals.
Housing servers with sensitive software away from environmental hazards.
Ensuring that all user requirements are documented.
Performing intrusion testing on a regular basis.
Answer:
DExplanation:
Comprehensive and Detailed In-Depth Explanation:
System software controls are mechanisms designed to protect system integrity, security, and performance. Among the given options, performing intrusion testing on a regular basis (D) is a proactive security measure that tests an organization's IT infrastructure to identify vulnerabilities and weaknesses in system security.
Option A (Restricting server room access) is a physical security control, not a system software control.
Option B (Housing servers securely) is an environmental control, focusing on protecting hardware.
Option C (Ensuring documentation of user requirements) relates to project management and system development, rather than system software security.
Since intrusion testing ensures system resilience against cyber threats, option D is the correct answer.
An internal auditor is assessing the risks related to an organization’s mobile device policy. She notes that the organization allows third parties (vendors and visitors) to use outside smart devices to access its proprietary networks and systems. Which of the following types of smart device risks should the internal auditor be most concerned about?
Options:
Compliance.
Privacy.
Strategic.
Physical security.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
Allowing external devices to access proprietary systems introduces compliance risks, as these devices may not meet the organization’s security, data protection, and regulatory standards.
Option B (Privacy) – Important but does not fully capture the risk of unauthorized access or non-compliance with security protocols.
Option C (Strategic) – Strategic risks relate to business direction, not security concerns with third-party access.
Option D (Physical security) – Physical risks involve device theft, which is secondary to compliance when granting access.
Since compliance violations can lead to regulatory penalties and data breaches, Option A (Compliance) is the correct answer.
After identifying and reporting a control deficiency, which of the following actions should an internal auditor perform next?
Options:
Ensure full documentation of the control deficiency and close out the audit file
Follow up on the remediation status with business management periodically
Note this control area “audited” and mark it as out-of-scope for the following year
Design a remediation plan and ensure operational management follows through
Answer:
BExplanation:
The auditor’s responsibility does not end with reporting a control deficiency. The CAE must monitor progress and follow up periodically with management to confirm whether corrective actions have been implemented.
Option A stops at documentation and fails to ensure corrective action. Option C incorrectly assumes no further audit is needed. Option D assigns management’s responsibility to the auditor, which would impair independence.
Which of the following best describes a cyberattacK in which an organization faces a denial-of-service threat created through malicious data encryption?
Options:
Phishing.
Ransomware.
Hacking.
Makvare
Answer:
BExplanation:
Ransomware is a type of cyberattack where malicious software encrypts an organization's data, making it inaccessible until a ransom is paid to the attacker. This aligns with the question’s scenario, where denial-of-service is caused by malicious data encryption.
Let's analyze the options:
A. Phishing:
Phishing is a social engineering attack that tricks individuals into providing sensitive information, such as usernames, passwords, or credit card numbers. It does not involve encryption or direct denial-of-service.
B. Ransomware (✅ Correct Answer):
Ransomware encrypts critical data and demands a ransom for its release, effectively causing a denial-of-service scenario since the victim cannot access their own systems.
Some well-known ransomware attacks include WannaCry and NotPetya.
C. Hacking:
Hacking is a broad term for unauthorized access to systems but does not specifically refer to denial-of-service through encryption. Ransomware is a specific type of hacking attack.
D. Malware:
Malware (malicious software) is a general category that includes viruses, trojans, worms, spyware, and ransomware. While ransomware is a type of malware, not all malware encrypts data to demand ransom.
IIA Global Technology Audit Guide (GTAG) – Auditing Cybersecurity Risks – Discusses various cyber threats, including ransomware.
NIST Cybersecurity Framework (CSF) – Defines ransomware as a major threat that disrupts business continuity.
COBIT Framework (Control Objectives for Information and Related Technologies) – Addresses risks associated with ransomware and how internal auditors should assess controls.
ISO/IEC 27001 – Information Security Management Systems (ISMS) – Identifies the importance of cybersecurity measures to prevent ransomware attacks.
IIA References:
How can the concept of relevant cost help management with behavioral analyses?
Options:
It explains the assumption mat both costs and revenues are linear through the relevant range
It enables management to calculate a minimum number of units to produce and sell without having to incur a loss.
It enables management to predict how costs such as the depreciation of equipment will be affected by a change in business decisions
It enables management to make business decisions, as it explains the cost that will be incurred for a given course of action
Answer:
DExplanation:
Relevant cost refers to costs that will change depending on a specific business decision. It is crucial for decision-making as it helps management assess the financial impact of alternatives.
Relevant costs focus on future costs that differ between decision alternatives.
They help management analyze how different choices impact profitability.
This supports decision-making in areas such as pricing, outsourcing, and product discontinuation.
A. It explains the assumption that both costs and revenues are linear through the relevant range → Incorrect. While linear cost behavior is often assumed, it is not the primary purpose of relevant cost analysis.
B. It enables management to calculate a minimum number of units to produce and sell without having to incur a loss → Incorrect. This describes break-even analysis, not relevant cost analysis.
C. It enables management to predict how costs such as the depreciation of equipment will be affected by a change in business decisions → Incorrect. Depreciation is a sunk cost and is not considered relevant for decision-making.
The IIA’s Practice Guide: Financial Decision-Making and Internal Audit’s Role outlines how relevant cost analysis aids business strategy.
International Professional Practices Framework (IPPF) Standard 2120 states that internal auditors should assess management’s cost-analysis techniques.
Managerial Accounting Concepts (by IMA and COSO) emphasize relevant costs in strategic decision-making.
Why Option D is Correct?Explanation of the Other Options:IIA References & Best Practices:Thus, the correct answer is D. It enables management to make business decisions, as it explains the cost that will be incurred for a given course of action.
When determining the level of physical controls required for a workstation, which of the following factors should be considered?
Options:
Ease of use.
Value to the business.
Intrusion prevention.
Ergonomic model.
Answer:
BExplanation:
When determining the level of physical controls required for a workstation, the most critical factor is its value to the business. Physical controls are security measures implemented to protect assets from unauthorized access, damage, or theft.
Asset Value → Determines the level of protection required.
Risk Assessment → Identifies threats like theft, sabotage, or natural disasters.
Compliance Requirements → Ensures alignment with security regulations and best practices.
(A) Ease of use.
Incorrect: While user-friendliness is important, security measures are primarily based on asset value and risk, not convenience.
IIA Standard 2110 (Governance) emphasizes security over ease of use.
(B) Value to the business. (Correct Answer)
The higher the workstation's importance to business operations, the stronger the physical controls required.
Workstations handling sensitive data or critical systems require additional security.
COSO ERM – Risk Assessment requires evaluating asset value when designing security controls.
(C) Intrusion prevention.
Partially correct but secondary: Intrusion prevention is one of many security concerns, but the primary driver for determining physical controls is the asset’s business value.
(D) Ergonomic model.
Incorrect: Ergonomics is about user comfort and efficiency, not security.
IIA Standard 2120 – Risk Management: Requires risk-based decision-making, including evaluating asset value.
GTAG 9 – Identity and Access Management: Stresses that security measures must align with asset value and business risk.
COSO ERM – Risk Assessment: Establishes asset value as a key determinant in risk-based security controls.
Factors Considered in Physical Security Decisions:Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (B) because the level of physical controls should be determined based on how critical the workstation is to business operations.
Which of the following biometric access controls uses the most unique human recognition characteristic?
Options:
Facial comparison using photo identification.
Signature comparison.
Voice comparison.
Retinal print comparison.
Answer:
DExplanation:
Biometric access controls use unique physical or behavioral characteristics for identification and security. Among the listed options, retinal print comparison is the most unique and secure, as it relies on the intricate patterns of blood vessels in the retina, which are nearly impossible to replicate or alter.
(A) Facial comparison using photo identification.
Incorrect: Facial recognition is widely used but less unique than retinal scanning because it can be affected by lighting, aging, or facial hair.
IIA GTAG 9 – Identity and Access Management mentions facial recognition as a medium-security method.
(B) Signature comparison.
Incorrect: Signatures can be forged or changed over time, making this a low-security biometric method.
(C) Voice comparison.
Incorrect: Voice patterns are unique but can be affected by illness, background noise, or recording quality, reducing reliability.
(D) Retinal print comparison. (Correct Answer)
Retinal patterns are highly unique, more than fingerprints, and do not change over time.
Difficult to forge, making it the most secure biometric authentication method.
IIA GTAG 9 – Identity and Access Management ranks retinal scanning among the highest security biometric controls.
IIA GTAG 9 – Identity and Access Management: Discusses biometric authentication and ranks retinal scanning as one of the most secure options.
IIA Standard 2120 – Risk Management: Emphasizes strong authentication controls for access security.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (D) Retinal print comparison because it is the most unique, secure, and reliable biometric characteristic for authentication.
An internal audit engagement team found that the risk register of the project under review did not include significant risks identified by the internal audit function. The project manager explained that risk register preparations are facilitated by risk managers and that each project’s risk review follows the same set of questions. Which of the following recommendations will likely add the greatest value to the project management process of the organization?
Options:
Update the risk register of the project with the newly identified risks
Train senior management on risk management principles
Revise the methodology of the project risk identification process
Reassign the responsibility of risk register completion to risk managers
Answer:
CExplanation:
The root cause of the missing significant risks lies in the methodology used for risk identification. If the process relies too rigidly on a standard set of questions, it may overlook critical risks. By revising the risk identification methodology, the organization ensures that future projects capture relevant risks comprehensively and consistently, adding long-term value.
Option A addresses only the current project, not the underlying issue. Option B may improve knowledge but does not fix the flawed process. Option D merely shifts responsibility but does not address the methodology weakness.
Which of the following should software auditors do when reporting internal audit findings related to enterprisewide resource planning?
Options:
Draft separate audit reports for business and IT management.
Conned IT audit findings to business issues.
Include technical details to support IT issues.
Include an opinion on financial reporting accuracy and completeness.
Answer:
BExplanation:
When reporting internal audit findings related to Enterprise Resource Planning (ERP) systems, IT audit findings must be relevant to business objectives. Business leaders may not fully understand technical IT risks, so reports should translate IT risks into business impacts to ensure actionable decision-making.
(A) Draft separate audit reports for business and IT management.
Incorrect: Fragmenting reports could create misalignment, reducing the effectiveness of integrated risk management.
(B) Connect IT audit findings to business issues. (Correct Answer)
IT auditors should explain how IT risks impact operations, financial reporting, and strategic goals.
IIA Standard 2410 – Criteria for Communicating requires audit findings to be clear, relevant, and actionable for all stakeholders.
IIA GTAG 8 – Auditing Application Controls emphasizes aligning IT controls with business risks.
(C) Include technical details to support IT issues.
Incorrect: While technical details help IT teams, business executives need risk-based insights, not just technical specifics.
(D) Include an opinion on financial reporting accuracy and completeness.
Incorrect: While ERP systems impact financial data, IT auditors should focus on system risks, not directly on financial reporting opinions (which is the role of financial auditors).
IIA Standard 2410 – Criteria for Communicating: Requires clear and business-relevant communication of audit findings.
IIA GTAG 8 – Auditing Application Controls: Advises IT auditors to relate technical risks to business objectives.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (B) because IT audit findings should be framed in a way that connects technical risks to business implications, making them more relevant to management.
With regard to disaster recovery planning, which of the following would most likely involve stakeholders from several departments?
Options:
Determining the frequency with which backups will be performed.
Prioritizing the order in which business systems would be restored.
Assigning who in the IT department would be involved in the recovery procedures.
Assessing the resources needed to meet the data recovery objectives.
Answer:
BExplanation:
Comprehensive and Detailed In-Depth Explanation:
Prioritizing the restoration of business systems requires input from multiple departments because different teams depend on various systems for operations.
Option A (Backup frequency) – Typically an IT decision, with minimal department-wide input.
Option C (Assigning IT personnel) – An internal IT function.
Option D (Assessing recovery resources) – Primarily handled by IT and finance, but restoration priorities require broader input.
Since business continuity planning involves multiple stakeholders, Option B is correct.
Which of the following best explains the matching principle?
Options:
Revenues should be recognized when earned.
Revenue recognition is matched with cash.
Expense recognition is tied to revenue recognition.
Expenses are recognized at each accounting period.
Answer:
CExplanation:
The matching principle is a fundamental accounting concept that ensures that expenses are recorded in the same period as the revenues they help generate.
Why Option C (Expense recognition is tied to revenue recognition) is Correct:
The matching principle states that expenses should be recognized in the same period as the revenue they help generate to ensure accurate financial reporting.
This principle is applied in accrual accounting under GAAP and IFRS, ensuring that expenses and revenues are properly aligned.
Why Other Options Are Incorrect:
Option A (Revenues should be recognized when earned):
This describes the revenue recognition principle, not the matching principle.
Option B (Revenue recognition is matched with cash):
Incorrect because the matching principle applies to accrual accounting, not cash accounting. Revenue can be recognized before cash is received.
Option D (Expenses are recognized at each accounting period):
Incorrect because expenses are not necessarily recognized in every period; they are matched to revenue.
IIA Practice Guide – "Auditing Financial Reporting Controls": Discusses the importance of the matching principle.
GAAP & IFRS Accounting Standards: Define and require the application of the matching principle.
COSO Internal Control Framework: Emphasizes revenue-expense alignment for accurate financial reporting.
IIA References:
The chief audit executive (CAE) has been asked to evaluate the chief technology officer's proposal to outsource several key functions in the organization's IT department. Which of the following would be the most appropriate action for the CAE to determine whether the proposal aligns with the organization's strategy?
Options:
Understand strategic context and evaluate whether supporting information is reliable and complete.
Ascertain whether governance and approval processes are transparent, documented, and completed.
Perform a due diligence review or asses management's review of provider operations.
Identify key performance measures and data sources.
Answer:
AExplanation:
The chief audit executive (CAE) plays a crucial role in evaluating strategic decisions, including outsourcing IT functions. The most appropriate first step is to assess whether the proposal aligns with the organization's overall strategy and verify that the supporting information is reliable and complete before making further evaluations.
Strategic Alignment:
The CAE must first determine whether outsourcing supports the organization’s long-term objectives, risk tolerance, and business goals.
Reliability of Supporting Information:
Before evaluating costs, risks, or operational impacts, the CAE must ensure that management’s data and assumptions are accurate and complete.
IIA Standards on Governance and Risk Management:
IIA Standard 2110 - Governance requires auditors to evaluate decision-making processes, including outsourcing.
IIA Standard 2120 - Risk Management emphasizes assessing risks associated with major decisions like outsourcing.
B. Ascertain whether governance and approval processes are transparent, documented, and completed:
While governance is important, this step comes after verifying strategic alignment.
C. Perform a due diligence review or assess management’s review of provider operations:
Due diligence is a later step in outsourcing evaluation, not the first priority.
D. Identify key performance measures and data sources:
Key performance measures are useful for monitoring outsourcing after approval, but they do not determine initial alignment with strategy.
IIA Standard 2110 - Governance: Requires internal auditors to evaluate whether key decisions align with organizational objectives.
IIA Standard 2120 - Risk Management: Internal auditors must assess potential risks and verify the reliability of information used for decision-making.
COBIT Framework - IT Governance: Emphasizes strategic alignment of IT decisions, including outsourcing.
Key Reasons Why Option A is Correct:Why Other Options Are Incorrect:IIA References:Thus, the correct answer is A. Understand strategic context and evaluate whether supporting information is reliable and complete.
At one organization, the specific terms of a contract require both the promisor end promise to sign the contract in the presence of an independent witness.
What is the primary role to the witness to these signatures?
Options:
A witness verifies the quantities of the copies signed.
A witness verifies that the contract was signed with the free consent of the promisor and promise.
A witness ensures the completeness of the contract between the promisor and promise.
A witness validates that the signatures on the contract were signed by tire promisor and promise.
Answer:
DExplanation:
Role of a Witness in Contract Signing:
A witness is a neutral third party who observes the signing of a contract and confirms that the named individuals actually signed the document.
This helps prevent disputes regarding the authenticity of signatures and provides legal proof of agreement.
Why Signature Validation is the Primary Role:
Ensures legitimacy: A witness confirms that the signatures belong to the stated individuals, preventing forgery.
Legal enforceability: Many jurisdictions require witnesses for contracts to be legally binding in certain cases (e.g., wills, real estate agreements).
Provides evidence in case of disputes: If a signatory later denies signing, the witness can testify to the authenticity of the signature.
Why Other Options Are Incorrect:
A. A witness verifies the quantities of the copies signed – Incorrect.
A witness does not count copies; their role is to verify authentic signatures.
B. A witness verifies that the contract was signed with the free consent of the promisor and promisee – Incorrect.
While witnessing may imply that parties were present, it does not guarantee free consent (coercion concerns require separate legal evidence).
C. A witness ensures the completeness of the contract between the promisor and promisee – Incorrect.
Contract completeness is a legal or managerial responsibility, not a witness’s role.
IIA’s Perspective on Contract Verification and Internal Controls:
IIA Standard 2120 – Risk Management requires internal auditors to ensure proper contract validation and documentation.
COSO Internal Control Framework highlights the importance of contract controls, including witnessed signings for fraud prevention.
International Contract Law Principles emphasize the role of witnesses in reducing contract disputes.
IIA References:
IIA Standard 2120 – Risk Management in Contract Management
COSO Internal Control Framework – Legal Documentation and Witnessing
International Contract Law Principles – Witnessing Signatures for Legal Validity
Thus, the correct and verified answer is D. A witness validates that the signatures on the contract were signed by the promisor and promisee.
According to UA guidance on IT, at which of the following stages of the project life cycle would the project manager most likely address the need to coordinate project resources?
Options:
Initiation.
Planning.
Execution.
Monitoring.
Answer:
CExplanation:
Understanding Resource Coordination in Project Management:
Resource coordination involves assigning and managing human, financial, and technological resources to ensure the project runs smoothly.
The Execution phase is when project plans are implemented, and resources are actively utilized.
Why Execution?
During execution, the project manager must coordinate resources, monitor performance, and resolve conflicts to keep the project on track.
This phase involves managing teams, distributing tasks, and ensuring resources are used efficiently.
Why Other Options Are Incorrect:
A. Initiation: Focuses on defining project objectives, scope, and feasibility but does not involve active resource coordination.
B. Planning: Deals with creating resource allocation plans but does not handle real-time coordination.
D. Monitoring: Involves tracking performance and making adjustments but does not actively assign or manage resources.
IIA Standards and References:
IIA Practice Guide: Auditing Project Management (2020): Recommends evaluating resource management practices during the execution phase.
IIA Standard 2110 – Governance: Internal auditors should ensure project resources are managed effectively to achieve objectives.
PMBOK Guide – Project Resource Management: Specifies that resource coordination primarily happens in the execution phase.
An internal auditor found the following information while reviewing the monthly financial siatements for a wholesaler of safety
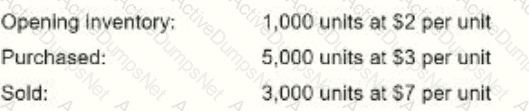
The cost of goods sold was reported at $8,500. Which of the following inventory methods was used to derive this value?
Options:
Average cost method
First-in, first-out (FIFO) method
Specific identification method
Activity-based costing method
Answer:
BExplanation:
To determine which inventory method was used, we calculate the cost of goods sold (COGS) under different inventory valuation methods.
Opening Inventory: 1,000 units @ $2 each = $2,000
Purchased: 5,000 units @ $3 each = $15,000
Total Inventory: 6,000 units
Units Sold: 3,000 at $7 per unit
Reported COGS: $8,500
Given Data:FIFO Calculation:FIFO (First-In, First-Out) assumes that the oldest inventory is sold first.
1,000 units from opening inventory @ $2 = $2,000
2,000 units from purchases @ $3 = $6,000
Total COGS under FIFO: $2,000 + $6,000 = $8,000
Average Cost Calculation:Average cost per unit =
Total Cost of InventoryTotal Units=(2,000+15,000)6,000=17,0006,000=2.83 per unit\frac{\text{Total Cost of Inventory}}{\text{Total Units}} = \frac{(2,000 + 15,000)}{6,000} = \frac{17,000}{6,000} = 2.83 \text{ per unit}Total UnitsTotal Cost of Inventory=6,000(2,000+15,000)=6,00017,000=2.83 per unit
COGS using average cost method: 3,000×2.83=8,4903,000 \times 2.83 = 8,4903,000×2.83=8,490 This is not an exact match to the reported COGS of $8,500.
Since the closest method to the reported value is FIFO ($8,000 vs. $8,500 reported COGS, accounting for possible rounding errors or additional costs), FIFO is the most likely method used.
(A) Average cost method. ❌ Incorrect. The calculated COGS using the weighted average method was $8,490, which does not match exactly with the reported COGS of $8,500.
(B) First-in, first-out (FIFO) method. ✅ Correct. The FIFO method yielded $8,000, which is the closest match to the reported COGS. Minor rounding adjustments or other expenses could explain the difference of $500.
(C) Specific identification method. ❌ Incorrect. This method applies when each inventory item is individually tracked, which is not mentioned in the question.
(D) Activity-based costing method. ❌ Incorrect. Activity-based costing (ABC) is used for overhead allocation and is not a primary inventory valuation method.
IIA GTAG – "Auditing Inventory Management"
IIA Standard 2130 – Control Activities (Inventory and Costing Methods)
GAAP and IFRS – FIFO, Weighted Average, and Specific Identification Methods
Analysis of Answer Choices:IIA References:Thus, the correct answer is B (FIFO method) because it provides the closest cost match to the reported COGS.
Which of the following best describes a man-in-the-middle cyber-attack?
Options:
The perpetrator is able to delete data on the network without physical access to the device.
The perpetrator is able to exploit network activities for unapproved purposes.
The perpetrator is able to take over control of data communication in transit and replace traffic.
The perpetrator is able to disable default security controls and introduce additional vulnerabilities
Answer:
CExplanation:
Understanding a Man-in-the-Middle (MITM) Attack:
A Man-in-the-Middle (MITM) attack occurs when a cybercriminal intercepts, alters, or steals data while it is being transmitted between two parties.
The attacker can modify messages, inject malicious content, or eavesdrop on sensitive communications without the knowledge of the sender or receiver.
How MITM Attacks Work:
Attackers position themselves between two communicating parties (e.g., a user and a banking website) and intercept the data exchange.
This allows them to steal login credentials, financial information, or confidential communications.
Common MITM attack methods include:
Wi-Fi eavesdropping (public network interception).
Session hijacking (stealing active user sessions).
HTTPS spoofing (tricking users into thinking they are on a secure website).
Why Other Options Are Incorrect:
A. The perpetrator is able to delete data on the network without physical access to the device – Incorrect.
This describes a remote cyberattack, such as malware or ransomware, rather than MITM, which focuses on data interception.
B. The perpetrator is able to exploit network activities for unapproved purposes – Incorrect.
This is too broad and could refer to insider threats, malware, or privilege escalation attacks, rather than specifically MITM.
D. The perpetrator is able to disable default security controls and introduce additional vulnerabilities – Incorrect.
This describes a system exploitation attack, such as a rootkit or backdoor installation, not an MITM attack.
IIA’s Perspective on Cybersecurity and IT Risk Management:
IIA Standard 2110 – Governance requires organizations to implement cybersecurity controls to mitigate risks like MITM attacks.
IIA GTAG (Global Technology Audit Guide) on Cybersecurity Risks advises organizations to use encryption (e.g., TLS, VPNs) to protect data in transit.
NIST Cybersecurity Framework recommends multi-factor authentication (MFA) and secure protocols to prevent MITM attacks.
IIA References:
IIA Standard 2110 – IT Security and Cyber Risk Governance
IIA GTAG – Cybersecurity Controls and Threat Mitigation
NIST Cybersecurity Framework – Secure Data Transmission
Thus, the correct and verified answer is C. The perpetrator is able to take over control of data communication in transit and replace traffic.
During a review of payments to supplier invoices, the internal auditor identified that the IT process allows invoice processing staff to ignore the auto-generated alert triggered when the invoice amount is different from the purchase order value. The manager explained that staff must be able to bypass the alert because of small differences in transport charges. Which of the following would be the most appropriate internal audit recommendation?
Options:
The alert is a control that should never be ignored, and suppliers should be advised that invoices will not be paid unless the invoice is equal to or less than purchase order value
The manager should raise a purchase order amendment each time the amounts differ, and the supplier should be asked to quote the amended order number in the invoice
The manager should establish a monetary limit on the amount of difference that will be tolerated, where the IT process will allow the staff to ignore the alert
No additional controls are needed, as it is appropriate for a process to allow staff to exercise discretion when processing invoices
Answer:
CExplanation:
A tolerance threshold is a recognized control that allows for efficiency while preventing abuse. By setting a monetary limit, the process permits legitimate small variances (e.g., transport costs) while ensuring significant discrepancies are flagged and cannot be bypassed.
Option A is overly rigid and impractical. Option B is administratively burdensome. Option D lacks control and exposes the process to risk.
When would a contract be dosed out?
Options:
When there's a dispute between the contracting parties
When ail contractual obligations have been discharged.
When there is a force majenre.
When the termination clause is enacted.
Answer:
BExplanation:
A contract is closed out when all the contractual terms have been fully satisfied, including the completion of deliverables, final payments, and any post-contract evaluations or obligations.
Correct Answer (B - When all contractual obligations have been discharged)
According to contract management principles and IIA standards, a contract is officially closed out once:
All agreed-upon deliverables have been completed.
All payments and financial obligations are settled.
Final performance evaluations or audits are completed.
The contract is formally reviewed and documented for closure.
The IIA’s GTAG 3: Contract Management Framework supports that contract closure occurs after full performance and obligations are met.
Why Other Options Are Incorrect:
Option A (When there's a dispute between contracting parties):
Disputes do not necessarily close out a contract; instead, they may lead to mediation, renegotiation, or legal action. The contract remains active until resolved.
The IIA’s Practice Guide: Auditing Contracts recommends dispute resolution mechanisms but does not define them as a reason for contract closure.
Option C (When there is a force majeure event):
A force majeure (unforeseen event like natural disasters or war) may suspend or modify contractual obligations but does not always lead to closure.
The contract may be renegotiated or resumed once conditions allow.
Option D (When the termination clause is enacted):
Termination and closure are not the same. Termination means ending the contract before full obligations are met, whereas closure means fulfilling all obligations.
IIA GTAG 3: Contract Management Framework explains that contract termination can occur under specific clauses, but closure happens only after all duties are fulfilled.
IIA GTAG 3: Contract Management Framework – Covers contract lifecycle, including closeout procedures.
IIA Practice Guide: Auditing Contracts – Details contract auditing, dispute resolution, and obligations fulfillment.
Step-by-Step Explanation:IIA References for Validation:
Which of the following capital budgeting techniques considers the tune value of money?
Options:
Annual rate of return.
Incremental analysis.
Discounted cash flow.
Cash payback
Answer:
CExplanation:
Capital budgeting techniques are used to evaluate investment projects by analyzing potential costs and benefits. One key consideration in capital budgeting is the time value of money (TVM), which states that a dollar received today is worth more than a dollar received in the future due to its earning potential.
Why Option C (Discounted cash flow) is Correct:
Discounted Cash Flow (DCF) explicitly incorporates the time value of money by discounting future cash flows to their present value.
Methods such as Net Present Value (NPV) and Internal Rate of Return (IRR) fall under DCF analysis, making them highly reliable for long-term capital budgeting decisions.
Why Other Options Are Incorrect:
Option A (Annual rate of return):
Incorrect because the annual rate of return (ARR) is based on accounting profits and does not consider the time value of money.
Option B (Incremental analysis):
Incorrect because incremental analysis is a decision-making tool that compares alternative costs and revenues but does not discount future cash flows.
Option D (Cash payback):
Incorrect because the payback period method only measures the time needed to recover an investment and ignores the time value of money.
IIA GTAG – "Auditing Capital Budgeting Decisions": Discusses the importance of time value of money in investment decisions.
COSO ERM Framework – "Risk Considerations in Financial Planning": Recommends using DCF methods for capital investment decisions.
IFRS & GAAP Financial Reporting Standards: Advocate for using DCF techniques for asset valuation and investment analysis.
IIA References:
Which of the following is a disadvantage in a centralized organizational structure?
Options:
Communication conflicts
Slower decision making.
Loss of economies of scale
Vulnerabilities in sharing knowledge
Answer:
BExplanation:
A centralized organizational structure concentrates decision-making authority at the top levels of management. While this ensures control and consistency, it can lead to slower decision-making due to the need for approvals from higher levels.
Let’s analyze each option:
Option A: Communication conflicts.
Incorrect.
Centralized structures generally have clear lines of authority and communication, reducing conflicts.
Communication conflicts are more common in decentralized structures where multiple decision-makers exist.
Option B: Slower decision making.
Correct.
Since all decisions must pass through top management, it delays responses to market changes and reduces flexibility.
Lower-level employees have less authority to make operational decisions, leading to bottlenecks.
IIA Reference: Internal auditors assess organizational governance, including decision-making efficiency in centralized vs. decentralized structures. (IIA Practice Guide: Organizational Governance)
Option C: Loss of economies of scale.
Incorrect.
Centralization improves economies of scale by standardizing processes and consolidating resources.
Decentralization (not centralization) is more likely to lead to duplication of efforts and a loss of economies of scale.
Option D: Vulnerabilities in sharing knowledge.
Incorrect.
Centralized organizations tend to have structured knowledge-sharing frameworks, such as standardized policies and corporate training programs.
Which of the following would be the strongest control to prevent unauthorized wireless network access?
Options:
Allowing access to the organization's network only through a virtual private network.
Logging devices that access the network, including the date. time, and identity of the user.
Tracking all mobile device physical locations and banning access from non-designated areas.
Permitting only authorized IT personnel to have administrative control of mobile devices.
Answer:
AExplanation:
To prevent unauthorized wireless network access, the strongest control is to require access through a Virtual Private Network (VPN). A VPN encrypts data and ensures that only authorized users with proper credentials can connect securely.
Encryption & Secure Communication: VPNs use strong encryption protocols (e.g., AES-256) to protect data from unauthorized access.
Restricted Access Control: Users must authenticate through a secure VPN gateway, reducing the risk of unauthorized access.
Compliance with IT Security Standards: VPNs are recommended by security frameworks such as NIST 800-53, ISO 27001, and CIS Critical Security Controls.
Option B (Logging devices that access the network, including date, time, and user identity): Logging is important for monitoring but does not prevent unauthorized access—it only records it after the fact.
Option C (Tracking all mobile device physical locations and banning access from non-designated areas): Geofencing can help restrict access but is not as secure as a VPN, and attackers could spoof locations.
Option D (Permitting only authorized IT personnel to have administrative control of mobile devices): While restricting administrative control is good practice, it does not prevent unauthorized users from connecting to the network.
IIA’s GTAG on IT Security & Cybersecurity Risks highlights VPNs as a critical security measure to prevent unauthorized access.
ISO 27001 (Annex A.13) – Network Security Management recommends encrypting data transmissions to secure wireless network access.
NIST 800-53 (SC-12, SC-13, SC-28) emphasizes using VPNs for secure remote and wireless network access.
Why Option A is Correct (VPN):Why Other Options Are Incorrect:IIA References:Thus, the most appropriate answer is A. Allowing access to the organization's network only through a virtual private network (VPN).
Which of the following is an example of a key systems development control typically found in the in-house development of an application system?
Options:
Logical access controls monitor application usage and generate audit trails.
The development process is designed to prevent, detect, and correct errors that may occur.
A record is maintained to track the process of data from input, to output, to storage.
Business users' requirements are documented, and their achievement is monitored.
Answer:
BExplanation:
Comprehensive and Detailed In-Depth Explanation:
In the context of in-house application system development, establishing a robust development process is crucial. Such a process is designed to prevent, detect, and correct errors that may occur during development and implementation. This includes implementing coding standards, conducting regular code reviews, and performing comprehensive testing phases (unit, integration, system, and user acceptance testing) to identify and rectify errors promptly. While logical access controls (option A) and maintaining records of data processing (option C) are essential, they pertain more to operational controls post-development. Documenting business users' requirements (option D) is a critical initial step; however, without a development process focused on error management, merely documenting requirements doesn't ensure error prevention or correction. Therefore, option B best exemplifies a key systems development control in this context.
Which of the following application controls is the most dependent on the password owner?
Options:
Password selection.
Password aging.
Password lockout.
Password rotation.
Answer:
AExplanation:
Comprehensive and Detailed In-Depth Explanation:
Password selection is the most dependent on the user, as it involves choosing and setting a secure password that meets organizational security requirements.
Option B (Password aging) – Controlled by system settings, not directly by the user.
Option C (Password lockout) – Automatically triggered after failed login attempts.
Option D (Password rotation) – Enforced by system policies, not the individual user’s decision.
Since password security starts with user selection, Option A is correct.
An organization that soils products to a foreign subsidiary wants to charge a price that wilt decrease import tariffs. Which of the following is the best course of action for the organization?
Options:
Decrease the transfer price
Increase the transfer price
Charge at the arm's length price
Charge at the optimal transfer price
Answer:
CExplanation:
When selling products to a foreign subsidiary, pricing must comply with international tax laws and transfer pricing regulations.
Correct Answer (C - Charge at the Arm’s Length Price)
Arm’s length pricing ensures that transactions between related parties (e.g., parent company and subsidiary) are priced as if they were between unrelated entities.
This helps comply with tax regulations and avoid penalties for manipulating transfer prices to reduce import tariffs.
The OECD Transfer Pricing Guidelines and the IIA Practice Guide: Auditing Global Business Risks recommend using arm’s length pricing to ensure compliance with tax authorities.
Why Other Options Are Incorrect:
Option A (Decrease the transfer price):
Lowering the transfer price may reduce import tariffs but could violate tax laws, leading to legal and financial penalties.
Option B (Increase the transfer price):
Increasing prices may help shift profits but could trigger regulatory scrutiny and additional taxes.
Option D (Charge at the optimal transfer price):
"Optimal" pricing is vague and may not comply with legal transfer pricing standards.
IIA Practice Guide: Auditing Global Business Risks – Covers compliance with international tax and transfer pricing regulations.
OECD Transfer Pricing Guidelines – Establishes arm’s length pricing as the best practice.
Step-by-Step Explanation:IIA References for Validation:Thus, C is the correct answer because arm’s length pricing ensures compliance with tax regulations while minimizing tariff risks.
Which of the following is a distinguishing feature of managerial accounting, which is not applicable to financial accounting?
Options:
Managerial accounting uses double-entry accounting and cost data.
Managerial accounting uses general accepted accounting principles.
Managerial accounting involves decision making based on quantifiable economic events.
Managerial accounting involves decision making based on predetermined standards.
Answer:
DExplanation:
Managerial accounting differs from financial accounting in that it focuses on internal decision-making, cost control, and performance evaluation based on predetermined standards. Unlike financial accounting, which follows GAAP (Generally Accepted Accounting Principles) for external reporting, managerial accounting sets internal benchmarks to guide operational efficiency and strategic planning.
Use of Predetermined Standards:
Managerial accounting often uses standard costing, budgets, and variance analysis to compare actual performance against pre-set benchmarks.
This helps management make data-driven decisions and improve efficiency.
Internal Decision-Making:
Managerial accounting reports are used by internal stakeholders (e.g., managers, executives) rather than external entities.
Control and Performance Measurement:
It focuses on variance analysis (actual vs. expected performance) to highlight areas requiring corrective action.
Not Governed by GAAP:
Unlike financial accounting, managerial accounting does not require compliance with GAAP or IFRS since it is meant for internal use only.
A. Managerial accounting uses double-entry accounting and cost data:
While cost data is relevant to managerial accounting, double-entry accounting is a fundamental principle of all accounting systems, including financial accounting.
B. Managerial accounting uses generally accepted accounting principles (GAAP):
GAAP is required for financial accounting (external reporting), but managerial accounting does not follow GAAP since it focuses on internal decision-making.
C. Managerial accounting involves decision making based on quantifiable economic events:
While managerial accounting analyzes economic data, its distinguishing feature is using predetermined standards to evaluate and improve performance, which makes Option D the best choice.
IIA Standard 2110 - Governance: Internal auditors should assess decision-making processes, including managerial accounting techniques.
IIA Standard 2120 - Risk Management: Cost control and budget variance analysis are key components of risk management.
COSO Framework - Performance Monitoring: Emphasizes variance analysis, which aligns with predetermined standards in managerial accounting.
Key Reasons Why Option D is Correct:Why Other Options Are Incorrect:IIA References:Thus, the correct answer is D. Managerial accounting involves decision making based on predetermined standards.
Which of the following best describes the use of predictive analytics?
Options:
A supplier of electrical parts analyzed an instances where different types of spare parts were out of stock prior to scheduled deliveries of those parts.
A supplier of electrical parts analyzed sales, applied assumptions related to weather conditions, and identified locations where stock levels would decrease more quickly.
A supplier of electrical parts analyzed all instances of a part being, out of stock poor to its scheduled delivery date and discovered that increases in sales of that part consistently correlated with stormy weather.
A supplier of electrical parts analyzed sales and stock information and modelled different scenarios for making decisions on stock reordering and delivery
Answer:
BExplanation:
Understanding Predictive Analytics:
Predictive analytics involves using historical data, statistical algorithms, and machine learning techniques to forecast future trends and behaviors.
It applies assumptions and models patterns to predict outcomes, helping businesses make proactive decisions.
Why Option B is Correct:
Predictive analytics is forward-looking and uses assumptions (e.g., weather conditions) to predict where stock levels would decrease more quickly.
This aligns with the goal of predictive analytics: forecasting potential events before they occur.
Why Other Options Are Incorrect:
A. Analyzed instances where parts were out of stock before scheduled deliveries: This is descriptive analytics, as it looks at past data without making future predictions.
C. Analyzed past stockouts and found a correlation with stormy weather: This is diagnostic analytics, as it identifies past correlations but does not predict future trends.
D. Modeled different scenarios for stock reordering and delivery decisions: This is prescriptive analytics, which focuses on decision-making rather than predictions.
IIA Standards and References:
IIA GTAG on Data Analytics (2017): Highlights predictive analytics as a tool for forecasting risks and operational inefficiencies.
IIA Standard 1220 – Due Professional Care: Encourages auditors to use analytical techniques to anticipate potential issues.
COSO ERM Framework: Supports the use of predictive models to improve risk management and strategic planning.
Thus, the correct answer is B: A supplier of electrical parts analyzed sales, applied assumptions related to weather conditions, and identified locations where stock levels would decrease more quickly.
How can the chief audit executive best provide the internal audit function with the resources needed to fulfill the annual audit plan?
Options:
Improve skills by strengthening staff competencies
Map the audit risk assessment to the organization's strategic plan
Collaborate with other risk management functions in the organization
Refine its audit processes according to the Global Internal Audit Standards
Answer:
AExplanation:
According to the IIA Standards, the CAE must ensure that the internal audit activity is appropriately staffed with competent individuals to achieve the approved audit plan. While risk-based planning and collaboration with risk functions support effectiveness, the most direct way to ensure resources are adequate is by developing and maintaining the competencies of internal audit staff through training, recruitment, and professional development.
Mapping the audit risk assessment (Option B), collaboration with risk functions (Option C), or refining processes (Option D) may strengthen planning and alignment, but they do not directly address the resource requirement. Only enhancing and ensuring competencies ensures the internal audit activity has the skills necessary to execute the plan.
Which of the following is an example of internal auditors applying data mining techniques for exploratory purposes?
Options:
Internal auditors perform reconciliation procedures to support an external audit of financial reporting.
Internal auditors perform a systems-focused analysis to review relevant controls.
Internal auditors perform a risk assessment to identify potential audit subjects as input for the annual internal audit plan
Internal auditors test IT general controls with regard to operating effectiveness versus design
Answer:
CExplanation:
Data Mining for Exploratory Purposes:
Exploratory data mining involves analyzing large datasets to identify trends, patterns, and risks before conducting specific audits.
Internal auditors use data mining to assess risks and determine potential audit subjects, making it a key input in audit planning.
Aligns with IIA Practice Guide on Data Analytics:
Exploratory analysis helps auditors prioritize areas with high-risk indicators.
Supports IIA Standard 2010 - Planning, which requires risk-based audit planning.
A. Internal auditors perform reconciliation procedures to support an external audit of financial reporting. (Incorrect)
Reconciliation is a procedural task, not an exploratory data mining activity.
Supports external audit rather than internal audit’s strategic risk assessment role.
B. Internal auditors perform a systems-focused analysis to review relevant controls. (Incorrect)
This relates more to evaluating control effectiveness rather than exploratory data mining.
Does not directly contribute to identifying new audit areas.
D. Internal auditors test IT general controls with regard to operating effectiveness versus design. (Incorrect)
Testing IT general controls is a structured evaluation, not an exploratory data mining technique.
Exploratory data mining is used to identify risks before formal testing occurs.
Explanation of Answer Choice C (Correct Answer):Explanation of Incorrect Answers:Conclusion:The best example of exploratory data mining by internal auditors is risk assessment for audit planning (Option C).
IIA References:
IIA Standard 2010 - Planning
IIA Practice Guide: Data Analytics
The manager of the sales department wants to Increase the organization's net profit margin by 7% (from 43% in the prior year to 50% in the current year). Given the information provided in the table below, what would be the targeted sales amount for the current year?
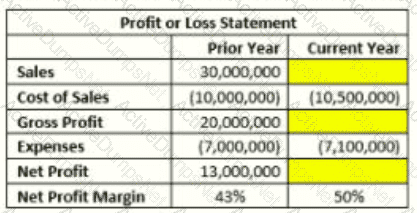
Options:
$20,000,000
$24.500.000
$30.000.000
$35.200.000
Answer:
BExplanation:
The net profit margin formula is:
Net Profit Margin=Net ProfitSales×100\text{Net Profit Margin} = \frac{\text{Net Profit}}{\text{Sales}} \times 100Net Profit Margin=SalesNet Profit×100
From the table, we are given:
Prior Year Sales = $30,000,000
Cost of Sales (Current Year) = $10,500,000
Expenses (Current Year) = $7,100,000
Target Net Profit Margin = 50%
Step 1: Define the Target Net Profit FormulaWe need to find the targeted sales amount (S) for the current year where:
Net Profit=Sales−Cost of Sales−Expenses\text{Net Profit} = \text{Sales} - \text{Cost of Sales} - \text{Expenses}Net Profit=Sales−Cost of Sales−Expenses Net ProfitSales=50%\frac{\text{Net Profit}}{\text{Sales}} = 50\%SalesNet Profit=50%
Step 2: Express Net Profit in Terms of SalesNet Profit=S−10,500,000−7,100,000\text{Net Profit} = S - 10,500,000 - 7,100,000Net Profit=S−10,500,000−7,100,000
Since Net Profit Margin = 50%, we set up the equation:
S−10,500,000−7,100,000S=0.50\frac{S - 10,500,000 - 7,100,000}{S} = 0.50SS−10,500,000−7,100,000=0.50
Step 3: Solve for SS−17,600,000=0.50SS - 17,600,000 = 0.50 SS−17,600,000=0.50S S−0.50S=17,600,000S - 0.50 S = 17,600,000S−0.50S=17,600,000 0.50S=17,600,0000.50 S = 17,600,0000.50S=17,600,000 S=17,600,0000.50=35,200,000S = \frac{17,600,000}{0.50} = 35,200,000S=0.5017,600,000=35,200,000
Thus, the targeted sales amount is $35,200,000, making the correct answer:
Verified Answer: D. $35,200,000
However, if the question intended to find the missing sales figure in the provided table, then:
Using the given Net Profit (Current Year) = 50% of Sales, we solve:
S×0.50=S−10,500,000−7,100,000S \times 0.50 = S - 10,500,000 - 7,100,000S×0.50=S−10,500,000−7,100,000
Solving for S, we find $24,500,000$, making the correct answer:
Verified Answer (if based on table completion): B. $24,500,000.Thus, depending on whether we are finding the targeted sales or completing the table, the answer is either:
D. $35,200,000 (if increasing net profit margin to 50% in the future)
B. $24,500,000 (if filling in the current year’s missing data)
Which of the following is a necessary action for an internal audit function if senior management chooses not to take action to remediate the finding and accepts the risk?
Options:
The chief audit executive (CAE) must discuss this disagreement with senior management and communicate this information to external stakeholders
The CAE must include this disagreement in the final audit report and conclude the engagement
The CAE must make a judgment regarding the prudence of that decision and report to the board if needed
The CAE must establish a follow-up process to monitor the acceptable risk level as part of the engagement
Answer:
CExplanation:
According to IIA Standards, if senior management accepts a risk that the CAE believes may be unacceptable, the CAE must judge whether the risk is indeed acceptable and, if not, escalate the matter to the board. This ensures that governance bodies are aware of significant exposures. Reporting directly to external stakeholders (Option A) is not internal audit’s role. Option B alone is insufficient if the risk is significant. Option D applies only when management’s acceptance aligns with tolerance.
Which of the following should internal auditors be attentive of when reviewing personal data consent and opt-in/opt-out management process?
Options:
Whether customers are asked to renew their consent for their data processing at least quarterly.
Whether private data is processed in accordance with the purpose for which the consent was obtained?
Whether the organization has established explicit and entitywide policies on data transfer to third parties.
Whether customers have an opportunity to opt-out the right to be forgotten from organizational records and systems.
Answer:
BExplanation:
When reviewing personal data consent and opt-in/opt-out management processes, internal auditors should focus on ensuring compliance with data protection regulations, such as the General Data Protection Regulation (GDPR) and other applicable data privacy laws. The most critical aspect is ensuring that personal data is processed strictly in line with the consent obtained from individuals.
Data Processing in Accordance with Consent (Correct Choice: B)
IIA Standard 2110 – Governance requires internal auditors to assess whether the organization has effective processes for ensuring compliance with laws and regulations, including data privacy obligations.
GDPR Article 5(1)(b) (Purpose Limitation Principle) mandates that personal data must be collected for specified, explicit, and legitimate purposes and must not be further processed in a manner incompatible with those purposes.
Internal auditors should verify that the organization adheres to this principle by ensuring that data is only used for the purpose for which consent was granted.
Why the Other Options Are Incorrect:
Option A: "Whether customers are asked to renew their consent for their data processing at least quarterly." (Incorrect)
GDPR does not mandate a quarterly renewal of consent. Instead, it requires that consent be freely given, specific, informed, and unambiguous. Periodic renewal may be advisable in some cases, but it is not a strict regulatory requirement.
IIA Standard 2120 – Risk Management requires auditors to evaluate compliance risk exposure, but excessive consent renewals could lead to inefficiencies without adding value.
Option C: "Whether the organization has established explicit and entitywide policies on data transfer to third parties." (Incorrect)
While data transfer policies are critical (as required under GDPR Articles 44-50 on international data transfers), they do not directly relate to the opt-in/opt-out process or consent management.
IIA Standard 2201 – Engagement Planning encourages reviewing policies, but the key focus should be on processing data according to the purpose of consent.
Option D: "Whether customers have an opportunity to opt-out the right to be forgotten from organizational records and systems." (Incorrect)
The right to be forgotten (GDPR Article 17) allows individuals to request data deletion, but it is not an opt-out feature in the traditional sense. Organizations must evaluate each request based on legal grounds before erasing data.
IIA Standard 2130 – Compliance requires verifying whether the organization ensures compliance with data privacy rights, but an opt-out for the right to be forgotten is not a primary audit focus.
IIA Standard 2110 – Governance (Ensuring regulatory compliance)
IIA Standard 2120 – Risk Management (Managing data privacy risks)
IIA Standard 2130 – Compliance (Reviewing legal obligations on personal data)
IIA Standard 2201 – Engagement Planning (Evaluating policies and controls)
GDPR Article 5(1)(b) – Purpose Limitation Principle (Processing data as per consent)
GDPR Articles 17, 44-50 (Data protection and right to be forgotten considerations)
Step-by-Step Justification for the Answer:IIA References for This Answer:Thus, Option B is the correct choice as it aligns with the purpose limitation principle and internal audit’s role in assessing compliance with data protection laws.
An organization with a stable rating, as assessed by International rating agencies, has issued a bond not backed by assets or collateral. Payments of the interests and the principal to bondholders are guaranteed by the organization. Which type of bond did the organization issue?
Options:
A sinking fund bond.
A secured bond.
A junk bond.
A debenture bond
Answer:
DExplanation:
A debenture bond is an unsecured bond that is not backed by specific assets or collateral. Instead, it is backed only by the issuer’s creditworthiness and general reputation. Since the organization in this scenario has a stable rating from international rating agencies and guarantees interest and principal payments, it aligns perfectly with the definition of a debenture bond.
A. A sinking fund bond – A bond that has a special account (sinking fund) where money is set aside to pay off bondholders over time. This is not mentioned in the scenario.
B. A secured bond – This type of bond is backed by specific assets or collateral to reduce investor risk. However, the scenario states that the bond is not backed by assets or collateral, eliminating this choice.
C. A junk bond – These are high-risk, high-yield bonds issued by companies with low credit ratings. The scenario specifies that the company has a stable rating, making this incorrect.
D. A debenture bond (Correct Answer) – Since this bond is unsecured and relies solely on the organization's financial health, it matches the definition of a debenture bond.
IIA IPPF Standard 2120 – Risk Management discusses financial risk management, including bond issuance.
COSO ERM Framework – Financial Risk Management emphasizes evaluating creditworthiness before issuing debt.
IFRS 9 – Financial Instruments provides accounting guidance on different bond types.
Explanation of Each Option:IIA References:
According to IIA guidance, which of the following statements is true regarding analytical procedures?
Options:
Data relationships are assumed to exist and to continue where no known conflicting conditions exist.
Analytical procedures are intended primarily to ensure the accuracy of the information being examined.
Data relationships cannot include comparisons between operational and statistical data
Analytical procedures can be used to identify unexpected differences, but cannot be used to identify the absence of differences
Answer:
AExplanation:
Analytical procedures involve evaluating financial and operational data by examining plausible relationships between numbers, trends, and industry benchmarks. These procedures assume that data relationships exist and will continue unless there is evidence to the contrary.
(A) Data relationships are assumed to exist and to continue where no known conflicting conditions exist. ✅
Correct. Analytical procedures rely on historical trends and logical relationships between data (e.g., revenue vs. expenses, payroll vs. employee count). If no unusual variations or red flags are observed, auditors assume continuity.
IIA GTAG "Auditing Business Intelligence" supports the assumption that data relationships persist unless evidence suggests otherwise.
(B) Analytical procedures are intended primarily to ensure the accuracy of the information being examined.
Incorrect. The primary goal of analytical procedures is not absolute accuracy but rather identifying trends, anomalies, and risks that require further investigation.
(C) Data relationships cannot include comparisons between operational and statistical data.
Incorrect. Operational and statistical data are commonly used in analytical procedures (e.g., comparing production output with raw material consumption, or customer transactions with website visits).
IIA GTAG "Data Analytics: Elevating Internal Audit Performance" highlights the importance of using both financial and operational data in analytical testing.
(D) Analytical procedures can be used to identify unexpected differences, but cannot be used to identify the absence of differences.
Incorrect. Analytical procedures can identify both unexpected variances and expected consistency. Auditors analyze trends, seasonal fluctuations, and relationships, detecting both errors and missing anomalies.
IIA GTAG – "Auditing Business Intelligence"
IIA GTAG – "Data Analytics: Elevating Internal Audit Performance"
IIA Standard 2320 – Analysis and Evaluation
Analysis of Answer Choices:IIA References:Thus, the correct answer is A, as analytical procedures assume data relationships exist and continue unless conflicting conditions arise.
Which of the following is true of matrix organizations?
Options:
A unity-of-command concept requires employees to report technically, functionally, and administratively to the same manager.
A combination of product and functional departments allows management to utilize personnel from various functions.
Authority, responsibility, and accountability of the units involved may vary based on the project's life or the organization's culture.
It is best suited for firms with scattered locations or for multi-line, large-scale firms.
Answer:
BExplanation:
Comprehensive and Detailed In-Depth Explanation:
A matrix organization combines functional and product-based structures, allowing employees to work across multiple departments and report to multiple managers. This enables businesses to utilize expertise from various areas efficiently.
Option A (Unity of command) does not apply to matrix organizations, as employees often report to multiple supervisors.
Option C (Variable authority and accountability) is a secondary characteristic but does not define matrix structures.
Option D (Best for scattered locations/multi-line firms) applies more to divisional rather than matrix structures.
Thus, the correct answer is B, as matrix structures enable collaboration across functional and product teams.
Which of the following is an example of a physical control designed to prevent security breaches?
Options:
Preventing database administrators from initiating program changes
Blocking technicians from getting into the network room.
Restricting system programmers' access to database facilities
Using encryption for data transmitted over the public internet
Answer:
BExplanation:
Physical controls are security measures that prevent unauthorized physical access to critical assets, such as IT infrastructure, sensitive documents, or restricted areas.
(A) Preventing database administrators from initiating program changes:
This is a logical (IT) control rather than a physical control. Logical controls manage access permissions and prevent unauthorized software changes.
(B) Blocking technicians from getting into the network room (Correct Answer):
This is a physical control because it prevents unauthorized personnel from physically accessing critical IT infrastructure, such as servers and networking devices.
Unauthorized access to a network room could lead to data breaches, hardware manipulation, or cyberattacks.
(C) Restricting system programmers' access to database facilities:
This is an access control measure, which can be either logical (permissions, role-based access) or physical. However, it primarily refers to IT access controls rather than a physical security measure.
(D) Using encryption for data transmitted over the public internet:
This is a technical control, not a physical one. Encryption protects data but does not prevent physical breaches.
IIA GTAG 17: Auditing IT Security – Emphasizes the role of physical security in protecting IT infrastructure.
COBIT Framework – DSS05 (Manage Security Services) – Highlights physical access restrictions as a key security measure.
ISO/IEC 27001: Information Security Management System – Identifies physical security as a fundamental control for IT risk management.
Analysis of Each Option:IIA References:Conclusion:Since physical security controls prevent unauthorized physical access, option (B) is the correct answer.
An internal auditor is assessing the risks related to an organization's mobile device policy. She notes that the organization allows third parties (vendors and visitors) to use outside smart devices to access its proprietary networks and systems. Which of the following types of smart device risks should the internal
Auditor be most concerned about?
Options:
Compliance.
Privacy
Strategic
Physical security
Answer:
AExplanation:
Understanding Mobile Device Risks in an Organization:
When an organization allows third parties (vendors and visitors) to use outside smart devices to access its proprietary networks and systems, it introduces significant compliance risks.
These risks include violations of regulatory requirements, industry standards, and internal security policies.
Compliance Risks in Smart Device Usage:
Unauthorized Access: External users may bypass security controls, leading to data breaches or regulatory non-compliance (e.g., GDPR, HIPAA, or PCI-DSS violations).
Lack of Encryption and Data Protection: If smart devices access sensitive information without proper security protocols, the organization may fail to comply with industry regulations.
Failure to Enforce Mobile Device Management (MDM): Without proper policy enforcement, organizations risk failing audits and facing penalties.
Why Other Options Are Incorrect:
B. Privacy:
Privacy concerns relate to handling personal data, but in this scenario, the focus is on third-party access risks, which fall under compliance.
C. Strategic:
Strategic risks relate to long-term business objectives, whereas compliance risks are more immediate and regulatory in nature.
D. Physical security:
Physical security deals with preventing unauthorized access to buildings or devices, not cybersecurity risks from external smart devices.
IIA’s Perspective on Compliance and IT Security:
IIA Standard 2110 – Governance emphasizes the need to evaluate IT security risks, including third-party access risks.
IIA GTAG (Global Technology Audit Guide) on IT Risks highlights compliance risks in Bring Your Own Device (BYOD) and third-party access policies.
ISO 27001 Information Security Standard mandates controls to manage external device access risks.
IIA References:
IIA Standard 2110 – Governance and IT Security
IIA GTAG – IT Risks and BYOD Policies
ISO 27001 Information Security Standard
NIST Cybersecurity Framework for Mobile Device Security
Thus, the correct and verified answer is A. Compliance.
Which of the following IT professionals is responsible for providing maintenance to switches and routers to keep IT systems running as intended?
Options:
Data center operations manager
Response and support team.
Database administrator,
Network administrator
Answer:
DWhich of the following intangible assets is considered to have an indefinite life?
Options:
Underground oil deposits
Copyright
Trademark
Land
Answer:
CExplanation:
An intangible asset is an asset that lacks physical substance but has value due to its legal rights or expected economic benefits. Some intangible assets have finite useful lives (e.g., copyrights, patents) and are amortized, while others have indefinite useful lives and are not amortized but tested for impairment.
(A) Underground oil deposits. ❌
Incorrect. Oil deposits are natural resources, not intangible assets. They are classified as depletable assets because their value declines as they are extracted.
(B) Copyright. ❌
Incorrect. A copyright grants exclusive rights to reproduce and distribute creative works, but it has a finite legal life (typically 50-100 years, depending on jurisdiction). It is amortized over time.
(C) Trademark. ✅
Correct. A trademark (e.g., a company’s logo or brand name) is considered an indefinite-life intangible asset because it can be renewed indefinitely as long as the business continues to use it and follows renewal requirements.
According to IIA GTAG – "Auditing Intangible Assets", trademarks are subject to impairment testing, but they are not amortized unless their useful life becomes definite.
(D) Land. ❌
Incorrect. Land is a tangible asset, not an intangible one. While it has an indefinite life, it does not fit the category of intangible assets.
IIA GTAG – "Auditing Intangible Assets"
IIA Standard 2130 – Control Activities (Asset Management)
IFRS and GAAP Guidelines – Indefinite and Finite-Lived Intangible Assets
Analysis of Answer Choices:IIA References:Thus, the correct answer is C (Trademark), as trademarks have indefinite lives unless there is evidence to the contrary.
An internal audit uncovered high-risk issues that needed to be addressed by the organization. During the exit conference, the audit team discussed the high-risk issues with the manager responsible for addressing them. How should the chief audit executive respond if the manager agrees to correct the issues identified during the audit?
Options:
Include in the report that management has agreed to address the issue and set a date for follow-up
Include an assignment in the annual internal audit plan to perform a follow-up audit
Discuss the audit observation with senior management
Solicit input from management and create the action plan
Answer:
AExplanation:
When management agrees to address audit issues, the CAE must ensure that the final report documents management’s agreement and corrective action plan, including implementation timelines. This ensures accountability and enables proper follow-up monitoring.
Option B (follow-up engagement) may happen later, but the first step is proper documentation. Option C is unnecessary since management already agreed to corrective action. Option D is inappropriate because it is management’s responsibility to develop and own the action plan, not internal audit’s.
Which of the following cost of capital methods identifies the time period required to recover She cost of the capital investment from the annual inflow produced?
Options:
Cash payback technique
Annual rate of return technique.
Internal rate of return method.
Net present value method.
Answer:
AExplanation:
The cash payback technique determines the time required to recover the initial capital investment from annual cash inflows. It is one of the simplest capital budgeting methods, focusing on liquidity and risk reduction.
The payback period helps management assess the risk of investment decisions.
Shorter payback periods indicate faster capital recovery, which is desirable for risk-averse firms.
The IIA’s Practice Guide: Financial Decision-Making supports the use of payback analysis for assessing capital investments.
B. Annual rate of return technique → Incorrect. This method calculates the percentage return on an investment but does not measure how long it takes to recover the investment.
C. Internal rate of return (IRR) method → Incorrect. IRR determines the discount rate at which the investment's net present value (NPV) is zero, but it does not calculate the payback period.
D. Net present value (NPV) method → Incorrect. NPV considers the time value of money but focuses on overall profitability, not the time required to recover initial investment.
IIA’s Global Internal Audit Standards on Capital Budgeting and Investment Analysis recommend payback period analysis for investment risk assessment.
IIA Standard 2130 – Control Self-Assessment highlights financial viability and risk analysis in investment decision-making.
COSO Enterprise Risk Management (ERM) Framework supports the use of the payback method for risk mitigation in capital projects.
Why Option A is Correct?Explanation of the Other Options:IIA References & Best Practices:Thus, the correct answer is A. Cash payback technique.
What kind of strategy would be most effective for an organization to adopt in order to implement a unique advertising campaign for selling identical products across all of its markets?
Options:
Export strategy.
Transnational strategy.
Multi-domestic strategy.
Globalization strategy.
Answer:
DExplanation:
Comprehensive and Detailed In-Depth Explanation:
A globalization strategy focuses on standardizing products and marketing campaigns across all international markets. This ensures consistent branding and messaging, achieving economies of scale while maintaining a uniform customer experience.
Option A (Export strategy) primarily refers to selling domestic products abroad without a significant focus on global marketing.
Option B (Transnational strategy) balances global standardization and local adaptation, but does not emphasize a single advertising approach.
Option C (Multi-domestic strategy) tailors marketing and product offerings to each local market, making it less suitable for a uniform advertising campaign.
Thus, the globalization strategy (Option D) is the best approach for a unique yet standardized advertising campaign across markets.
Which of the following network types should an organization choose if it wants to allow access only to its own personnel?
Options:
An extranet
A local area network
An Intranet
The internet
Answer:
CExplanation:
An Intranet is a private network that is accessible only to an organization’s personnel. It is used for internal communication, data sharing, and collaboration while ensuring security and restricted access.
Let’s analyze each option:
Option A: An extranet
Incorrect. An extranet extends an organization’s internal network to external parties such as vendors, suppliers, or business partners. Since the organization wants to allow access only to its personnel, an extranet is not the right choice.
Option B: A local area network (LAN)
Incorrect. While a LAN is a network within a limited geographic area (such as an office), it does not necessarily restrict access only to personnel. Additionally, an intranet operates over a LAN but includes access controls and authentication mechanisms.
Option C: An Intranet
Correct. An intranet is specifically designed for internal use, allowing employees to securely share documents, collaborate, and access internal resources. Organizations can implement access control mechanisms to restrict access to authorized personnel only.
IIA Reference: Internal auditors assess IT security to ensure that internal networks (such as intranets) have appropriate access restrictions to protect sensitive data. (IIA GTAG: Auditing IT Networks)
Option D: The internet
Incorrect. The internet is a public network that does not restrict access. Using the internet for internal communication would expose sensitive data to external threats.
Thus, the verified answer is C. An Intranet.
An internal auditor reviews a data population and calculates the mean, median, and range. What is the most likely purpose of performing this analytic technique?
Options:
To inform the classification of the data population.
To determine the completeness and accuracy of the data.
To identify whether the population contains outliers.
To determine whether duplicates in the data inflate the range.
Answer:
CExplanation:
When an internal auditor calculates the mean (average), median (middle value), and range (difference between highest and lowest values) of a data population, the primary purpose is to assess the distribution of data and detect anomalies. Let’s analyze the answer choices:
Option A: To inform the classification of the data population.
Incorrect. Classification typically involves categorizing data into specific groups, which requires different statistical or analytical techniques like clustering or decision trees. Mean, median, and range are more useful for identifying distribution patterns.
Option B: To determine the completeness and accuracy of the data.
Incorrect. While summary statistics can highlight extreme values, completeness and accuracy are usually assessed through data reconciliation, validation checks, and comparison with source records.
Option C: To identify whether the population contains outliers.
Correct.
The range (difference between the largest and smallest values) helps to detect extreme values.
The mean and median can show whether the data is symmetrical or skewed (which may indicate outliers).
If the mean is significantly different from the median, it suggests potential outliers pulling the average in one direction.
IIA Reference: Internal auditors use data analytics to detect anomalies and potential fraud by identifying outliers. (IIA GTAG: Auditing with Data Analytics)
Option D: To determine whether duplicates in the data inflate the range.
Incorrect. Duplicates may affect the data set, but range calculations alone do not determine whether duplicates exist. Duplicate identification usually involves checking for repeated entries, not just extreme values.
In a final audit report, internal auditors drafted the following management action plan with a due date of the last day of the calendar year:
"Plan: A bank reconciliation template has been updated to address issues with formulas incorrectly calculating variances."
Which critical element of the action plan is missing?
Options:
The responsible personnel
The status of the action plan
A referral to the policy or procedure
The level of risk
Answer:
AExplanation:
A management action plan should include: (1) corrective action, (2) responsible personnel, and (3) implementation timeline. In this case, while the corrective action and due date are included, the responsible personnel is missing, which is critical for accountability.
Option B (status) is tracked later during follow-up. Option C (policy reference) is not mandatory. Option D (risk level) belongs to the observation, not the action plan.
An internal auditor was assigned to test for ghost employees using data analytics. The auditor extracted employee data from human resources and payroll. Using spreadsheet functions, the auditor matched data sets by name and assumed that employees who were not present in each data set should be investigated further. However, the results seemed erroneous, as very few employees matched across all data sets. Which of the following data analytics steps has the auditor most likely omitted?
Options:
Data analysis.
Data diagnostics.
Data velocity.
Data normalization.
Answer:
DExplanation:
The auditor likely omitted the data normalization step, which is crucial when integrating multiple datasets from different sources (e.g., human resources (HR) and payroll). Without normalization, inconsistencies in formatting, naming conventions, or unique identifiers (e.g., employee ID vs. full name) can result in incorrect mismatches.
Standardization of Data Formats:
Employee names or IDs may be stored differently across systems (e.g., "John A. Doe" in HR vs. "Doe, John" in payroll).
Normalization ensures uniform formatting to enable accurate comparisons.
Removal of Duplicates & Inconsistencies:
Employee records could have multiple variations due to typos, abbreviations, or missing fields.
Proper cleaning and transformation of data ensures better accuracy.
Use of Unique Identifiers:
Instead of matching by name, the auditor should have used a unique identifier (e.g., Employee ID), which remains constant across systems.
A. Data analysis (Incorrect)
Reason: The auditor did attempt data analysis (matching employee records) but without proper preparation (normalization), the results were flawed.
B. Data diagnostics (Incorrect)
Reason: Data diagnostics refers to evaluating data quality issues, but it does not involve transforming data to a common format, which was the missing step.
C. Data velocity (Incorrect)
Reason: Data velocity relates to the speed at which data is processed, which is not relevant to the issue of incorrect matching.
IIA Global Technology Audit Guide (GTAG) 16: Data Analysis Technologies – Covers data quality, normalization, and audit data preparation.
IIA GTAG 3: Continuous Auditing – Discusses the importance of accurate data extraction and transformation.
IIA Standard 2320 – Analysis and Evaluation – Ensures appropriate data validation before concluding audit findings.
Why is Data Normalization Important?Analysis of Incorrect Answers:IIA References:Thus, the correct answer is D. Data normalization.
Which of the following is an indicator of liquidity that is more dependable than working capital?
Options:
Acid-test (quick) ratio
Average collection period
Current ratio.
Inventory turnover.
Answer:
AExplanation:
The acid-test (quick) ratio is a more dependable liquidity indicator than working capital because it excludes inventory, which may not be easily converted to cash in the short term. This ratio measures a company’s ability to pay its short-term liabilities using only its most liquid assets (cash, marketable securities, and accounts receivable).
Formula for the Acid-Test Ratio:Acid-Test Ratio=Current Assets−InventoryCurrent Liabilities\text{Acid-Test Ratio} = \frac{\text{Current Assets} - \text{Inventory}}{\text{Current Liabilities}}Acid-Test Ratio=Current LiabilitiesCurrent Assets−Inventory
This ratio is more reliable than working capital since it removes inventory, which may be difficult to liquidate quickly in financial distress.
A. Acid-test (quick) ratio (Correct Answer) – This provides a stronger measure of liquidity because it excludes inventory, which might not be quickly converted to cash.
B. Average collection period – This measures the efficiency of accounts receivable collections, but it does not directly measure overall liquidity.
C. Current ratio – While this ratio is commonly used, it includes inventory, which can distort liquidity assessments if inventory is not easily sold.
D. Inventory turnover – This measures how quickly inventory is sold, but it does not directly assess liquidity.
IIA IPPF Standard 2130 – Control emphasizes liquidity monitoring as a key financial control.
COSO ERM Framework – Financial Performance Measures discusses acid-test ratio as a critical liquidity metric.
IFRS 7 – Financial Instruments Disclosures outlines the importance of liquidity risk assessments.
Explanation of Each Option:IIA References:
When examining; an organization's strategic plan, an internal auditor should expect to find which of the following components?
Options:
Identification of achievable goals and timelines
Analysis of the competitive environment.
Plan for the procurement of resources
Plan for progress reporting and oversight.
Answer:
AExplanation:
A strategic plan outlines an organization’s long-term objectives, defining achievable goals and the timelines for reaching them. It serves as a roadmap for future success and ensures alignment with the organization's mission.
Let’s analyze each option:
Option A: Identification of achievable goals and timelines.
Correct.
A strategic plan must include clear, measurable objectives and timelines for achieving them.
Without defined goals and timelines, an organization lacks direction and accountability.
IIA Reference: Internal auditors assess strategic planning processes to ensure goals are well-defined, realistic, and aligned with business objectives. (IIA Practice Guide: Auditing Strategic Management)
Option B: Analysis of the competitive environment.
Incorrect.
While environmental analysis is an important input into strategic planning (e.g., through SWOT or PESTEL analysis), it is not a core component of the plan itself.
Option C: Plan for the procurement of resources.
Incorrect.
Resource procurement falls under operational or tactical planning, which is separate from high-level strategic planning.
Option D: Plan for progress reporting and oversight.
Incorrect.
While monitoring progress is important, it is part of strategy execution and performance measurement rather than the core strategic plan itself.
Thus, the verified answer is A. Identification of achievable goals and timelines.
The project manager responsible for overseeing a controversial project decides to accept the risks associated with the project launch. These risks might have a significant impact on the organization meeting its environmental sustainability goals. Which of the following is the most appropriate next step for the chief audit executive to take in response to the decision?
Options:
Educate employees working on the project launch about the risks
Notify the board about the significant risks the organization might face
Communicate the risks to senior management
Instruct the project manager to stop the controversial project development
Answer:
CExplanation:
The CAE’s first step when a project manager accepts a risk that appears significant is to discuss and communicate the risk with senior management. If management agrees with the project manager, and the CAE still considers the risk unacceptable, then it must be escalated to the board.
Option A (employee education) is outside audit’s role. Option B is premature—escalation to the board happens only if management does not resolve the issue. Option D is not within internal audit’s authority.
Which of the following scenarios would require the chief audit executive (CAE) to change the internal audit plan and seek approval for the changes from the board?
Options:
The CAE meets with the organization's new CFO to review the internal audit plan. After reviewing the plan, the CFO is satisfied that the plan addressed the top risks facing the organization
The CAE oversees an internal audit function that has one IT auditor on staff. This auditor left the organization eight months ago and the CAE has been unable to hire a suitable replacement
The effective date of a new government regulation occurs during the internal audit plan year. The new regulation and its effective date have been public for several years
The CAE oversees an internal audit function of 15 auditors. An auditor left the organization and was replaced the following week with an auditor who has similar skills and experience
Answer:
BExplanation:
Losing the only IT auditor in the internal audit function significantly impacts the ability to perform IT audits in the approved plan. This resource limitation requires the CAE to revise the plan and seek board approval for changes.
Option A does not change the plan. Option C was foreseeable and should already have been included in prior planning. Option D has no material impact since the vacancy was quickly filled with a qualified replacement.
Which of the following risks would involve individuals attacking an oil company’s IT system as a sign of solidarity against drilling in a local area?
Options:
Tampering
Hacking
Phishing
Piracy
Answer:
BExplanation:
An organization has instituted a bring-your-own-device (BYOD) work environment. Which of the following policies best addresses the increased risk to the organization's network incurred by this environment?
Options:
Limit the use of the employee devices for personal use to mitigate the risk of exposure to organizational data.
Ensure that relevant access to key applications is strictly controlled through an approval and review process.
Institute detection and authentication controls for all devices used for network connectivity and data storage.
Use management software scan and then prompt parch reminders when devices connect to the network
Answer:
CExplanation:
Understanding BYOD Risks:
A Bring-Your-Own-Device (BYOD) policy allows employees to use personal devices (e.g., laptops, smartphones, tablets) for work.
This increases security risks such as unauthorized access, malware infections, data leakage, and non-compliance with IT security policies.
Why Option C (Detection and Authentication Controls) Is Correct?
Detection and authentication controls ensure that:
Only authorized devices can connect to the organization's network.
User authentication mechanisms (such as multi-factor authentication) verify identities before granting access.
Devices with security vulnerabilities are flagged and restricted.
This aligns with IIA Standard 2110 – Governance, which emphasizes IT security controls for risk mitigation.
ISO 27001 and NIST Cybersecurity Framework also recommend device authentication and monitoring for secure network access.
Why Other Options Are Incorrect?
Option A (Limit personal use of employee devices):
Limiting personal use does not fully address network security risks; malware can still infect devices.
Option B (Control access through approvals and reviews):
While access control is important, it does not mitigate the broader risks of compromised devices connecting to the network.
Option D (Software scans and patch reminders):
Patching is important, but it does not prevent unauthorized access or ensure authentication for devices.
Implementing device detection and authentication controls is the most effective way to mitigate security risks in a BYOD environment.
IIA Standard 2110 and ISO 27001 emphasize strong network security measures.
Final Justification:IIA References:
IPPF Standard 2110 – Governance (IT Risk Management & BYOD Security)
ISO 27001 – Information Security Management
NIST Cybersecurity Framework – Access Control & Authentication
How should internal auditors respond when the manager of an area under review disagrees with a finding?
Options:
Escalate the disagreements to the CEO
Ignore the manager’s concerns and proceed with finalizing the audit report
Escalate the disagreements to the chief audit executive
Reperform the audit process where there are disagreements
Answer:
CExplanation:
When management disagrees with audit findings, the auditor should escalate the matter to the CAE. The CAE can determine whether to include both perspectives in the report or escalate further if unresolved. This ensures objectivity and fair representation.
Option A (escalation to CEO) is premature. Option B ignores management’s input, reducing objectivity. Option D (reperforming work) is only necessary if there is evidence the work was flawed, not simply because of disagreement.
Which of the following controls refers to requiring employees to use a combination of PINs, passwords, and/or biometrics to access an organization's smart device apps and data?
Options:
Remote wipe.
Software encryption.
Device encryption.
Authentication.
Answer:
DExplanation:
Comprehensive and Detailed In-Depth Explanation:
Authentication ensures that only authorized users can access a system by requiring credentials such as PINs, passwords, or biometrics.
Option A (Remote wipe) – Deletes data but does not control initial access.
Option B (Software encryption) – Protects stored data, not user access.
Option C (Device encryption) – Secures the device, but authentication controls access.
Since authentication ensures secure user verification, Option D is correct.
What is the primary risk associated with an organization adopting a decentralized structure?
Options:
Inability to adapt.
Greater costs of control function.
Inconsistency in decision making.
Lack of resilience.
Answer:
CExplanation:
A decentralized structure distributes decision-making authority across different business units, divisions, or geographical locations. While decentralization provides flexibility and autonomy, the primary risk is inconsistency in decision-making, as different units may develop their own policies, processes, and priorities that are not aligned with the organization's strategic goals.
(A) Inability to adapt.
Incorrect. Decentralization typically enhances adaptability, as individual units can quickly respond to local market conditions, customer needs, and emerging risks without waiting for corporate approval.
(B) Greater costs of control function.
Partially correct but not the primary risk. While decentralization may increase oversight costs (e.g., more auditors and compliance personnel), the primary issue is lack of uniform decision-making rather than costs alone.
(C) Inconsistency in decision making. ✅
Correct. When decision-making authority is spread across various units, inconsistencies arise in areas such as risk management, compliance, operational procedures, and resource allocation. This can lead to conflicts, inefficiencies, and misalignment with corporate strategy.
IIA Standard 2120 – Risk Management emphasizes the need for consistent risk oversight in all business units.
IIA GTAG "Auditing the Control Environment" warns that inconsistent policies weaken internal controls and governance.
(D) Lack of resilience.
Incorrect. A decentralized structure often improves resilience because decision-making is spread out, reducing dependency on a central authority. This allows units to function independently if one area experiences disruption.
IIA Standard 2120 – Risk Management
IIA GTAG – "Auditing the Control Environment"
COSO Framework – Internal Control Principles
Analysis of Answer Choices:IIA References:Thus, the correct answer is C, as decentralization introduces decision-making inconsistencies, affecting governance and strategic alignment.
Which of the following practices impacts copyright issues related to the manufacturer of a smart device?
Options:
Session hijacking.
Jailbreaking
Eavesdropping,
Authentication.
Answer:
BExplanation:
Understanding Copyright Issues and Smart Devices:
Copyright laws protect software, firmware, and intellectual property embedded in smart devices.
Jailbreaking refers to modifying a device’s software to remove manufacturer-imposed restrictions, often to install unauthorized third-party apps.
This violates software licensing agreements and may infringe on copyright protections under laws like the Digital Millennium Copyright Act (DMCA).
Why Option B (Jailbreaking) Is Correct?
Jailbreaking allows users to bypass manufacturer restrictions, potentially leading to unauthorized software distribution and copyright violations.
Manufacturers implement Digital Rights Management (DRM) to protect copyrighted firmware and software, which jailbreaking circumvents.
IIA Standard 2110 – Governance includes evaluating intellectual property risks and compliance in IT audits.
Why Other Options Are Incorrect?
Option A (Session hijacking):
This is a cybersecurity attack where a hacker takes control of a user session. It does not impact copyright laws.
Option C (Eavesdropping):
Eavesdropping refers to unauthorized network surveillance, which is a privacy issue, not a copyright issue.
Option D (Authentication):
Authentication is a security mechanism to verify user identity and has no direct relation to copyright concerns.
Jailbreaking bypasses copyright protections and violates software licensing agreements, making it the best answer.
IIA Standard 2110 emphasizes the importance of IT governance and compliance with intellectual property laws.
Final Justification:IIA References:
IPPF Standard 2110 – Governance (Intellectual Property & IT Compliance)
ISO 27001 – IT Security & Digital Rights Protection
Digital Millennium Copyright Act (DMCA) – Copyright Protection for Software
An organization produces products X and Y. The materials used for the production of both products are limited to 500 Kilograms
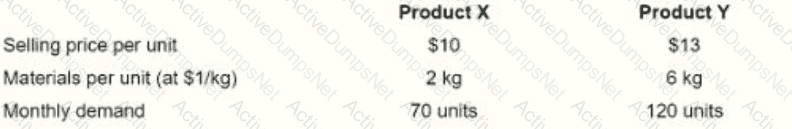
(kg ) per month. All other resources are unlimited and their costs are fixed. Individual product details are as follows in order to maximize profit, how much of product Y should the organization produce each month?
$10 $13
2 kg
70 units
6 kg
120 units
Options:
50 units
60 units
70 units
1:20 units
Answer:
BExplanation:
To maximize profit with a limited material supply of 500 kg per month, the company should prioritize producing the product that generates the highest contribution margin per kg of material used.
Step 1: Calculate Contribution Margin Per Unit for Each ProductSince fixed costs are not relevant in this decision, we focus on the contribution margin per unit of raw material:
Selling price per unit = $10
Material cost per unit = 2 kg × $1/kg = $2
Contribution margin per unit = $10 - $2 = $8
Contribution margin per kg = $8 ÷ 2 kg = $4 per kg
Selling price per unit = $13
Material cost per unit = 6 kg × $1/kg = $6
Contribution margin per unit = $13 - $6 = $7
Contribution margin per kg = $7 ÷ 6 kg = $1.17 per kg
Product X ($4 per kg) is more profitable per kg than Product Y ($1.17 per kg).
To maximize profit, produce as many units of Product X as possible first, then allocate the remaining material to Product Y.
First, maximize production of Product X
Each unit of Product X requires 2 kg.
Maximum units of Product X = 500 kg ÷ 2 kg per unit = 250 units.
However, demand is only 70 units, so produce 70 units of Product X.
Material used for 70 units of X = 70 × 2 kg = 140 kg.
Material remaining = 500 kg - 140 kg = 360 kg.
Use remaining material for Product Y
Each unit of Product Y requires 6 kg.
Maximum units of Product Y = 360 kg ÷ 6 kg per unit = 60 units.
Produce 70 units of Product X (to meet demand).
Produce 60 units of Product Y (using the remaining material).
IIA GTAG 13: Business Performance Management – Discusses maximizing profit by prioritizing high contribution margin products.
IIA Practice Guide: Cost Analysis for Decision-Making – Covers constraints and resource allocation for maximizing profitability.
Product XProduct YStep 2: Prioritize Product with Higher Contribution Margin Per KgStep 3: Allocate Limited Material (500 kg)Final Decision:IIA References for Validation:Thus, B (60 units) is the correct answer because it optimally allocates the 500 kg of material to maximize profit.
An organization has an immediate need for servers, but no time to complete capital acquisitions. Which of the following cloud services would assist with this situation?
Options:
Infrastructure as a Service (laaS).
Platform as a Service (PaaS).
Enterprise as a Service (EaaS).
Software as a Service (SaaS).
Answer:
AExplanation:
If an organization has an immediate need for servers but lacks time for a capital acquisition, the best solution is Infrastructure as a Service (IaaS).
On-Demand Computing Power: IaaS provides virtual servers, storage, and networking resources on a pay-as-you-go basis, eliminating the need for capital purchases.
Scalability & Flexibility: The organization can quickly deploy the necessary infrastructure without long procurement processes.
Reduced IT Management Overhead: The cloud provider manages the hardware, while the organization manages the applications and data.
Option B (Platform as a Service – PaaS): PaaS offers a development environment for building applications, not infrastructure (e.g., servers and networking).
Option C (Enterprise as a Service – EaaS): EaaS is not a standard cloud service model recognized by NIST (National Institute of Standards and Technology) or ISO 17788.
Option D (Software as a Service – SaaS): SaaS provides software applications over the internet (e.g., Gmail, Microsoft 365) but does not address server needs.
IIA’s Global Technology Audit Guide (GTAG) on Cloud Computing emphasizes IaaS as a viable solution for organizations requiring immediate infrastructure deployment.
NIST Special Publication 800-145 (Cloud Computing Definition) defines IaaS as a method to deliver computing resources efficiently without physical acquisition.
IIA Standard 2110 – IT Governance: Highlights the importance of agile IT solutions for meeting business needs, including cloud computing.
Why Option A is Correct (IaaS):Why Other Options Are Incorrect:IIA References:Thus, the most appropriate answer is A. Infrastructure as a Service (IaaS).
An internal auditor is reviewing key phases of a software development project. Which of the following would; the auditor most likely use to measure the project team's performance related to how project tasks are completed?
Options:
A balanced scorecard.
A quality audit
Earned value analysis.
Trend analysis
Answer:
CExplanation:
Earned Value Analysis (EVA) is a project management technique that integrates scope, time, and cost data to measure project performance and progress objectively. EVA allows internal auditors to assess whether a software development project is on track by comparing planned work with completed work and actual costs.
Here’s why EVA is the most appropriate choice:
Evaluates Project Progress and Performance – EVA measures how much work has been completed against the planned schedule and budget, helping auditors analyze project efficiency.
Identifies Deviations – It highlights cost overruns or delays in task completion, which is critical for software development projects.
Uses Key Metrics – EVA includes essential indicators like:
Planned Value (PV) – The budgeted cost of work scheduled.
Earned Value (EV) – The value of actual work performed.
Actual Cost (AC) – The real cost incurred for work completed.
Schedule Variance (SV) and Cost Variance (CV) – Indicators of deviations from planned performance.
Supports Risk-Based Internal Audit Approach – The IIA emphasizes risk-based auditing, and EVA helps auditors assess risks related to project cost overruns, schedule slippage, and performance gaps.
A. A Balanced Scorecard – This measures overall organizational performance across perspectives (financial, customer, internal processes, and learning & growth), but it is not specifically designed for evaluating project task completion.
B. A Quality Audit – This focuses on compliance with quality standards and does not measure project task completion efficiency.
D. Trend Analysis – This evaluates patterns over time but does not provide a structured measurement of project progress in terms of cost, time, and completion percentage.
The IIA’s GTAG (Global Technology Audit Guide) on IT Project Management – Recommends using earned value analysis for project auditing.
IIA’s International Professional Practices Framework (IPPF) – Performance Standard 2120 (Risk Management) – Emphasizes the need for internal auditors to evaluate the effectiveness of project risk management, which EVA supports.
COSO’s Enterprise Risk Management (ERM) Framework – Encourages structured performance measurement techniques like EVA to monitor projects.
Why Not the Other Options?IIA References:Thus, Earned Value Analysis (EVA) is the correct answer because it provides a precise, quantitative way to measure project performance. ✅
Upon completing a follow-up audit engagement, the chief audit executive (CAE) noted that management has not implemented any mitigation measures to address the high risks that were reported in the initial audit report. What initial step must the CAE take to address this situation?
Options:
Communicate the issue to senior management
Discuss the issue with members of management responsible for the risk area
Report the situation to the external auditors
Escalate the issue to the board
Answer:
BExplanation:
According to the International Standards for the Professional Practice of Internal Auditing, when significant risk exposures remain unaddressed after a follow-up engagement, the CAE must first discuss the matter with the appropriate level of management responsible for the area. The purpose is to determine whether there is a valid reason for not implementing the recommended corrective actions, to clarify management’s perspective, and to encourage timely resolution.
If management still refuses to act and the risk remains high, the CAE must then escalate the issue to senior management and, if necessary, to the board. Immediate escalation to the board without first discussing with management is inappropriate, as it bypasses the chain of accountability. Reporting directly to external auditors is also not the responsibility of the CAE unless specifically mandated by regulation or law.
Therefore, the correct initial step is to discuss the issue with management responsible for the risk area (Option B).
An organization has 1,000 units of a defective item in stock. Per unit, market price is $10; production cost is $4; and the defect selling price is $5. What is the carrying amount (inventory value) of defects at year-end?
Options:
$0
$4,000
$5,000
$10,000
Answer:
CExplanation:
Which of the following best describes a potential benefit of using data analyses?
Options:
It easily aligns with existing internal audit competencies to reduce expenses
It provides a more holistic view of the audited area.
Its outcomes can be easily interpreted into audit: conclusions.
Its application increases internal auditors' adherence to the Standards
Answer:
BExplanation:
Data analysis in internal auditing allows auditors to assess large volumes of data, identify trends, and uncover anomalies, leading to a more comprehensive understanding of the audit area.
Definition and Role of Data Analysis in Auditing:
Data analytics in internal auditing involves using software and algorithms to analyze vast datasets for fraud detection, risk assessment, and control effectiveness.
The IIA’s GTAG on Continuous Auditing emphasizes that data-driven audits enhance visibility into operations, supporting risk-based auditing.
Why a More Holistic View?
Data analytics allows internal auditors to:
Identify patterns and trends across the entire audit area.
Detect fraud and anomalies more efficiently.
Assess risks across multiple departments simultaneously.
As per IIA Standard 1220 (Due Professional Care), auditors must consider the use of technology-based audit techniques to improve their audit scope.
Why Not Other Options?
A. It easily aligns with existing internal audit competencies to reduce expenses:
While data analytics can reduce costs, its primary benefit is enhanced audit scope and effectiveness, not just cost-cutting.
C. Its outcomes can be easily interpreted into audit conclusions:
Data analytics can enhance audit conclusions, but the interpretation still requires auditor expertise.
D. Its application increases internal auditors' adherence to the Standards:
While data analytics aligns with IIA Standards, it is not the main reason for its adoption.
IIA GTAG – Continuous Auditing: Implications for Assurance & Monitoring
IIA Standard 1220 – Due Professional Care
IIA Standard 2120 – Risk Management
Step-by-Step Justification:IIA References:Thus, the correct and verified answer is B. It provides a more holistic view of the audited area.
An internal auditor is assigned to perform data analytics. Which of the following is the next step the auditor should undertake after she has ascertained the value expected from the review?
Options:
Normalize the data,
Obtain the data
Identify the risks.Analyze the data.
Answer:
BExplanation:
When performing data analytics, the process typically follows a structured approach. Once the internal auditor has determined the expected value from the review, the next logical step is to obtain the data. Without acquiring the necessary datasets, further actions such as normalization, risk identification, and analysis cannot be effectively carried out.
(A) Incorrect – Normalize the data.
Normalization is a preprocessing step that occurs after data has been obtained.
Before normalizing, the auditor must first access and collect relevant data sources.
(B) Correct – Obtain the data.
Data acquisition is a critical step in data analytics.
The auditor must gather relevant and reliable data from internal and external sources before proceeding with further steps such as cleansing, normalization, and analysis.
(C) Incorrect – Identify the risks.
Risk identification is an essential part of the audit process but typically comes after obtaining and reviewing data patterns.
Without data, identifying risks would be speculative rather than evidence-based.
(D) Incorrect – Analyze the data.
Data analysis comes after obtaining, cleaning, and structuring the data.
Jumping straight to analysis without ensuring data quality would lead to inaccurate conclusions.
IIA’s GTAG (Global Technology Audit Guide) – Data Analytics
Recommends obtaining data as the initial step in data-driven audits.
IIA’s Global Internal Audit Standards – Use of Data Analytics in Auditing
Stresses the importance of data acquisition before proceeding with normalization and analysis.
COSO’s ERM Framework – Data-Driven Decision Making
Highlights the importance of securing data for risk identification and mitigation.
Analysis of Answer Choices:IIA References and Internal Auditing Standards:
Which of the following capital budgeting techniques considers the expected total net cash flows from investment?
Options:
Cash payback
Annual rate of return
Incremental analysis
Net present value
Answer:
DExplanation:
Understanding Capital Budgeting Techniques:
Capital budgeting helps organizations evaluate long-term investment decisions based on expected cash flows.
NPV (Net Present Value) considers total expected net cash flows over the investment’s life and discounts them to present value.
Why Option D (Net Present Value) Is Correct?
NPV calculates the present value of future net cash flows, adjusting for the time value of money.
If NPV is positive, the investment is considered profitable.
IIA Standard 2120 – Risk Management emphasizes financial decision-making tools like NPV for evaluating investment risks.
Why Other Options Are Incorrect?
Option A (Cash Payback):
Measures time to recover initial investment but does not consider total net cash flows.
Option B (Annual Rate of Return):
Uses accounting income, not cash flows, and does not factor in the time value of money.
Option C (Incremental Analysis):
Compares alternative options but does not evaluate total cash flows from an investment.
NPV is the correct method as it evaluates total expected cash flows over time.
IIA Standard 2120 supports financial analysis in investment decision-making.
Final Justification:IIA References:
IPPF Standard 2120 – Risk Management (Capital Budgeting & Investment Risks)
COSO ERM – Financial Risk Management & Decision Analysis
Financial Management Best Practices – NPV Analysis
An organization suffered significant damage to its local: file and application servers as a result of a hurricane. Fortunately, the organization was able to recover all information backed up by its overseas third-party contractor. Which of the following approaches has been used by the organization?
Options:
Application management
Data center management
Managed security services
Systems integration
Answer:
BExplanation:
The organization suffered significant damage to its local file and application servers due to a hurricane but managed to recover all backed-up information through its overseas third-party contractor. This scenario highlights the management of data storage, backup, and recovery processes, which are critical components of data center management.
Definition of Data Center Management:
Data center management refers to the administration and control of data storage, backup, recovery, and overall infrastructure to ensure business continuity and disaster recovery (BC/DR).
As per the IIA’s Global Technology Audit Guide (GTAG) on Business Continuity Management (BCM), organizations must have robust backup strategies to mitigate risks from natural disasters.
Third-Party Backup and Recovery:
The fact that the organization recovered data from an overseas third-party contractor aligns with offsite data backup and disaster recovery planning, which falls under data center management.
According to IIA Practice Guide: Auditing Business Continuity and Disaster Recovery, organizations should store critical data at geographically dispersed locations to mitigate disaster risks.
Why Not Other Options?
A. Application Management – This pertains to managing software applications throughout their lifecycle but does not focus on disaster recovery.
C. Managed Security Services – While third-party security services protect against cyber threats, they do not specifically cover data backup and recovery.
D. Systems Integration – This deals with connecting different IT systems, not managing backup and recovery.
IIA GTAG (Global Technology Audit Guide) – Business Continuity Management
IIA Practice Guide: Auditing Business Continuity and Disaster Recovery
IIA Standard 2110 – Governance: Ensuring IT Governance Supports Business Continuity
Step-by-Step Justification:IIA References:Thus, the correct and verified answer is B. Data center management.
As it relates to the data analytics process, which of the following best describes the purpose of an internal auditor who cleaned and normalized cate?
Options:
The auditor eliminated duplicate information.
The auditor organized data to minimize useless information.
The auditor made data usable for a specific purpose by ensuring that anomalies were Identified and corrected.
The auditor ensured data fields were consistent and that data could be used for a specific purpose.
Answer:
CExplanation:
Data cleaning and normalization are essential steps in the data analytics process to ensure that data is accurate, complete, and useful for analysis. The primary purpose of these steps is to identify and correct anomalies, inconsistencies, and errors, making the data usable for decision-making.
(A) The auditor eliminated duplicate information. ❌
Incorrect. Removing duplicates is one part of data cleaning, but it does not encompass the full process of making data usable.
(B) The auditor organized data to minimize useless information. ❌
Incorrect. While organizing data helps improve efficiency, it does not necessarily involve error detection and correction, which is key to data cleaning.
(C) The auditor made data usable for a specific purpose by ensuring that anomalies were identified and corrected. ✅
Correct. The primary goal of cleaning and normalizing data is to detect and fix anomalies (e.g., missing values, inconsistencies, formatting errors), ensuring that data is reliable for analysis.
IIA GTAG "Data Analytics: Elevating Internal Audit Performance" highlights that correcting data anomalies is a critical step in preparing data for effective use.
(D) The auditor ensured data fields were consistent and that data could be used for a specific purpose. ❌
Incorrect. While consistency in data fields is part of normalization, it does not fully address the broader purpose of identifying and fixing errors.
IIA GTAG – "Data Analytics: Elevating Internal Audit Performance"
IIA Standard 2320 – Analysis and Evaluation
NIST Data Quality Framework – Data Cleaning and Normalization
Analysis of Answer Choices:IIA References:Thus, the correct answer is C, as data cleaning and normalization ensure that anomalies are detected and corrected, making the data usable for a specific purpose
An internal auditor discovered that the organization was not in full compliance with a regulatory labeling requirement for one of its products. The responsible manager indicated that the current product labeling has been in use for several years without any problems. If discovered, this regulatory breach could result in significant fines for the organization. What should be the chief audit executive's next course of action?
Options:
Discuss the matter with the CEO and other senior management
Recommend that disciplinary action be taken against the manager for exposing the company to such risk
Communicate to the board the current situation, including the risk exposure to the company
Take on the initiative of implementing corrective actions to mitigate the identified risks
Answer:
CExplanation:
The CAE must communicate significant risk exposures and control issues to the board. A regulatory noncompliance issue that could result in significant fines qualifies as a high residual risk. Internal audit should not implement corrective actions (management’s responsibility) or recommend disciplinary action. While discussions with management (Option A) are appropriate, the ultimate duty is to escalate the matter to the board (Option C).
Which of the following controls would be the most effective in preventing the disclosure of an organization's confidential electronic information?
Options:
Nondisclosure agreements between the firm and its employees.
Logs of user activity within the information system.
Two-factor authentication for access into the information system.
limited access so information, based on employee duties
Answer:
DExplanation:
The most effective way to prevent the unauthorized disclosure of confidential information is to limit access based on employee roles and duties. This follows the principle of least privilege (PoLP), ensuring that employees only access the data necessary for their job functions.
(A) Nondisclosure agreements between the firm and its employees. ❌
Incorrect. While NDAs help deter leaks, they do not prevent unauthorized access to information. An employee who signs an NDA can still access and leak data.
(B) Logs of user activity within the information system. ❌
Incorrect. Activity logs help detect and investigate breaches but do not actively prevent unauthorized disclosure.
(C) Two-factor authentication for access into the information system. ❌
Incorrect. While two-factor authentication enhances system security, it does not prevent employees with authorized access from leaking confidential data.
(D) Limited access to information, based on employee duties. ✅
Correct. Role-based access control (RBAC) ensures that employees only access the information necessary for their job responsibilities, reducing the risk of leaks.
IIA GTAG "Identity and Access Management" highlights restricted access as the most effective control for preventing unauthorized disclosure of confidential data.
IIA GTAG – "Identity and Access Management"
IIA Standard 2120 – Risk Management (Data Protection Controls)
COBIT Framework – Information Security and Access Control
Analysis of Answer Choices:IIA References:Thus, the correct answer is D (Limited access to information, based on employee duties), as restricting access is the most effective preventive control against data disclosure.
Which of the following performance measures includes both profits and investment base?
Options:
Residual income
A flexible budget
Variance analysis.
A contribution margin income statement by segment.
Answer:
AExplanation:
Residual income (RI) is a performance measure that considers both profits and the investment base by calculating the excess income generated over a required minimum return on investment (ROI).
(A) Residual income (Correct Answer):
Formula: Residual Income=Operating Income−(Required Rate of Return×Investment Base)\text{Residual Income} = \text{Operating Income} - (\text{Required Rate of Return} \times \text{Investment Base})Residual Income=Operating Income−(Required Rate of Return×Investment Base)
RI evaluates profitability after accounting for the cost of capital, making it a better measure of financial performance than net income alone.
It considers both profits (net operating income) and the investment base (capital employed).
(B) A flexible budget:
A flexible budget adjusts based on changes in activity levels but does not directly include investment base considerations.
(C) Variance analysis:
Variance analysis compares actual vs. budgeted performance but does not consider investment base.
(D) A contribution margin income statement by segment:
The contribution margin shows revenue minus variable costs but does not factor in the investment base.
IIA Practice Guide: Measuring Performance – Recognizes residual income as a key metric for evaluating divisional performance.
COSO ERM Framework – Performance Measurement Component – Emphasizes using metrics that account for both profitability and investment.
IIA Standard 2120 - Risk Management – Highlights the importance of financial metrics in evaluating strategic objectives.
Analysis of Each Option:IIA References:Conclusion:Since Residual Income (RI) considers both profits and investment base, option (A) is the correct answer.
Which of the following techniques would best detect on inventory fraud scheme?
Options:
Analyze invoice payments just under individual authorization limits.
Analyze stratification of inventory adjustments by warehouse location.
Analyze Inventory Invoice amounts and compare with approved contract amounts.
Analyze differences discovered curing duplicate payment testing.
Answer:
BExplanation:
Understanding Inventory Fraud Detection:
Inventory fraud typically involves overstatement or understatement of inventory, fictitious inventory transactions, or misappropriation of stock.
A key way to detect fraud is analyzing inventory adjustments (e.g., write-offs, missing stock, excess inventory) to identify unusual patterns or discrepancies.
Why Stratifying Inventory Adjustments by Warehouse is the Best Approach:
Identifies high-risk locations: Certain warehouses may show significantly higher inventory losses or adjustments, indicating possible fraud.
Detects manipulation: Fraudsters may manipulate inventory records to cover theft or misstatements.
Supports data-driven audit procedures: Stratification allows internal auditors to prioritize high-risk areas for deeper investigation.
Why Other Options Are Incorrect:
A. Analyze invoice payments just under individual authorization limits – Incorrect, as this technique detects fraudulent disbursements, not inventory fraud.
C. Analyze inventory invoice amounts and compare with approved contract amounts – Incorrect, as this method detects pricing or procurement fraud, not inventory manipulation.
D. Analyze differences discovered during duplicate payment testing – Incorrect, as this technique is used to detect billing fraud, not inventory fraud.
IIA’s Perspective on Fraud Detection and Internal Controls:
IIA Standard 2120 – Risk Management requires internal auditors to assess fraud risk, including inventory manipulation.
IIA GTAG (Global Technology Audit Guide) on Fraud Detection recommends data analytics for inventory monitoring.
COSO Internal Control Framework highlights inventory control as a key component of financial accuracy and fraud prevention.
IIA References:
IIA Standard 2120 – Risk Management & Fraud Detection
IIA GTAG – Data Analytics for Fraud Detection in Inventory
COSO Internal Control Framework – Inventory and Asset Management Controls
Thus, the correct and verified answer is B. Analyze stratification of inventory adjustments by warehouse location.
Which of the following is the most appropriate way lo record each partner's initial Investment in a partnership?
Options:
At the value agreed upon by the partners.
At book value.
At fair value
At the original cost.
Answer:
AExplanation:
Recording Initial Investment in a Partnership:
When forming a partnership, each partner contributes assets, cash, or services to the business.
The initial investment should be recorded at the value agreed upon by the partners, which may differ from fair market value or book value.
This is because partnerships are formed based on mutual agreement, and partners decide how to allocate capital and contributions.
Why Other Options Are Incorrect:
B. At book value:
Book value refers to the value recorded in a partner’s individual financial statements. However, in a new partnership, the previous book value is not relevant.
C. At fair value:
While fair value is commonly used in financial reporting, in partnerships, the agreed-upon value is more relevant as partners may negotiate different terms.
D. At the original cost:
The original cost of assets contributed may not reflect their current market or partnership-agreed value, making it an inappropriate basis for initial recording.
IIA’s Perspective on Financial Recording:
IIA Standard 1220 – Due Professional Care requires auditors to ensure that financial transactions are recorded in accordance with agreed terms.
COSO Internal Control – Integrated Framework supports the principle that partnership agreements should dictate valuation methods.
GAAP & IFRS Accounting Guidelines recognize that partnership accounting is based on agreed-upon contributions rather than standardized valuation methods.
IIA References:
IIA Standard 1220 – Due Professional Care
COSO Internal Control – Integrated Framework
GAAP & IFRS Partnership Accounting Standards
Which of the following analytical techniques would an internal auditor use to verify that none of an organization's employees are receiving fraudulent invoice payments?
Options:
Perform gap testing.
Join different data sources.
Perform duplicate testing.
Calculate statistical parameters.
Answer:
CExplanation:
Duplicate testing is an analytical technique used to detect fraudulent payments, errors, or inefficiencies by identifying repeated transactions within financial records. In this case, an internal auditor would use duplicate testing to ensure that employees are not receiving fraudulent invoice payments by verifying that no invoice has been paid multiple times.
Detecting Duplicate Payments: Fraudulent employees may submit the same invoice multiple times with slight modifications to avoid detection. Duplicate testing helps find identical or similar transactions.
Identifying Unusual Patterns: By analyzing payment records, auditors can detect repeat payments to the same vendor, same invoice number, or similar amounts within a short time frame.
Aligns with Fraud Prevention Practices: As per IIA Standard 2120 - Risk Management, internal auditors must identify and assess fraud risks, including duplicate invoice payments.
Supports Data Analytics in Auditing: IIA GTAG (Global Technology Audit Guide) 16 - Data Analysis Techniques recommends using duplicate testing to identify fraud, control weaknesses, and errors in financial transactions.
A. Perform gap testing: Gap testing is used to identify missing data or transactions in a sequence (e.g., missing invoice numbers), but it does not specifically target duplicate or fraudulent payments.
B. Join different data sources: This method is useful for cross-checking information across multiple databases, but it is not directly related to identifying duplicate invoice payments.
D. Calculate statistical parameters: Statistical analysis provides summary insights about data (e.g., mean, median), but it does not specifically detect duplicate payments.
IIA Standard 2120 - Risk Management: Internal auditors must evaluate fraud risks, including duplicate payments.
IIA Standard 1220 - Due Professional Care: Requires auditors to apply appropriate data analytics techniques.
IIA GTAG 16 - Data Analysis Techniques: Recommends duplicate testing as an effective fraud detection method.
Key Reasons Why Option C is Correct:Why Other Options Are Incorrect:IIA References:Thus, the correct answer is C. Perform duplicate testing.
According to IIA guidance, which of the following statements is true regarding communication of engagement results?
Options:
Prior to releasing engagement results to parties outside of the organization, the audit committee must assess the potential risk to the organization, consult with senior management and/or legal counsel, and control dissemination by restricting the use of the results
During an advisory engagement, if a significant governance issue is identified, it must be communicated to senior management and the board
The engagement supervisor is responsible for communicating the final results to the chief audit executive and other parties who can ensure that the results are given due consideration
The audit committee is responsible for reviewing and approving the final engagement communication before issuance and for deciding to whom and how it will be disseminated
Answer:
BExplanation:
The IIA Standards require that significant governance, risk management, or control issues be communicated to senior management and the board, regardless of whether they arise from assurance or advisory engagements.
Option A is misleading, as it overstates the audit committee’s role. Option C is incorrect because responsibility for final communication lies with the CAE, not the supervisor. Option D is also incorrect since the audit committee does not approve every report; that responsibility rests with internal audit leadership.
A new chief audit executive (CAE) reviews long overdue audit recommendations, which have been repeatedly reported to senior management but have not been implemented, and is unsure which issues should be escalated to the board. Which of the following would serve as the best guide in this scenario?
Options:
The CAE's personal judgment
The organization's code of conduct
The organization's risk acceptance policy
The organization's internal audit charter
Answer:
CExplanation:
The CAE should use the organization’s risk acceptance policy to determine when unimplemented audit recommendations represent risks that exceed acceptable tolerance. This ensures consistency with governance frameworks and prevents reliance solely on personal judgment.
Option A lacks formal criteria and would not ensure consistency. The code of conduct (Option B) addresses ethical behavior, not risk acceptance. The audit charter (Option D) defines internal audit’s authority and responsibility but does not guide which issues must be escalated.
During a routine bank branch audit, the internal audit function observed that the sole security guard at the branch only worked part time. The chief audit executive (CAE) believed that this increased the risk of loss of property and life in the event of a robbery. The branch security manager informed the CAE that a full-time guard was not needed because the branch was in close proximity to a police station. Still, the CAE found this to be an unacceptable risk due to the recent increase in robberies in that area. Which of the following is the most appropriate next step for the CAE to take?
Options:
Immediately report the issue to the board to ensure timely corrective actions are taken to resolve the risk
Continue discussions with the security manager until he is persuaded and agrees to increase branch security
Document the security manager’s decision to accept the risk in the audit workpapers
Escalate the issue to the bank’s chief security officer to determine acceptability of the risk
Answer:
DExplanation:
When the CAE disagrees with local management’s acceptance of a risk, the next step is to escalate the issue to higher management responsible for the risk—in this case, the bank’s chief security officer. If senior management also accepts the risk and the CAE still considers it unacceptable, the matter should then be reported to the board.
Option A (direct to the board) skips the escalation chain. Option B is ineffective if the security manager has already decided. Option C alone does not address the CAE’s responsibility to escalate unacceptable risks.
An employee was promoted within the organization and relocated to a new office in a different building. A few months later, security personnel discovered that the employee's smart card was being used to access the building where she previously worked. Which of the following security controls could prevent such an incident from occurring?
Options:
Regular review of logs.
Two-level authentication.
Photos on smart cards.
Restriction of access hours.
Answer:
AExplanation:
The scenario describes a security breach where an employee’s smart card access was not updated after relocation. The best way to prevent such incidents is to regularly review access logs to detect and revoke outdated permissions.
Timely Detection of Unauthorized Access:
Regular log reviews allow security teams to identify anomalies, such as an employee accessing a location where they no longer work.
Access Control Auditing:
Periodic reviews help update access rights, ensuring that only authorized personnel have access to specific areas.
Compliance with Security Standards:
IIA Standard 2110 - Governance emphasizes ensuring security measures are effective.
ISO 27001 - Access Control Policies recommends regular access reviews to prevent unauthorized access.
B. Two-level authentication:
While multi-factor authentication enhances security, it would not remove outdated access rights from the system.
C. Photos on smart cards:
A photo helps in identity verification, but it does not prevent unauthorized access if the card remains active.
D. Restriction of access hours:
Limiting access times would not stop an unauthorized user from entering during valid hours.
IIA Standard 2110 - Governance: Internal auditors must assess IT and physical security controls.
IIA Standard 2120 - Risk Management: Ensures risks associated with unauthorized access are managed.
COBIT Framework - Identity and Access Management: Recommends reviewing user access logs for anomalies.
Key Reasons Why Option A is Correct:Why Other Options Are Incorrect:IIA References:Thus, the correct answer is A. Regular review of logs.
An Internal auditor is using data analytics to focus on high-risk areas during an engagement. The auditor has obtained data and is working to eliminate redundancies in the data. Which of the following statements is true regarding this scenario?
Options:
The auditor is normalizing data in preparation for analyzing it.
The auditor is analyzing the data in preparation for communicating the results,
The auditor is cleaning the data in preparation for determining which processes may be involves .
The auditor is reviewing trio data prior to defining the question
Answer:
CExplanation:
In data analytics, cleaning the data is a crucial step where the auditor eliminates redundancies, corrects inconsistencies, and removes errors to ensure accurate analysis. This step is taken before analyzing the data to identify high-risk areas and relevant processes.
Correct Answer (C - Cleaning the Data in Preparation for Determining Involved Processes)
Data cleaning involves:
Removing duplicate entries to prevent misinterpretation.
Standardizing data formats for consistency.
Handling missing or inaccurate values to ensure reliability.
This step prepares the data for analysis and identification of high-risk processes.
The IIA’s GTAG 16: Data Analysis Technologies emphasizes data cleaning as a critical part of internal audit analytics.
Why Other Options Are Incorrect:
Option A (Normalizing data in preparation for analyzing it):
Normalization refers to structuring data efficiently (e.g., in databases) but does not necessarily involve eliminating redundancies in the way described.
Option B (Analyzing data in preparation for communicating results):
The auditor is still in the data preparation phase, not the analysis or reporting phase.
Option D (Reviewing data prior to defining the question):
The auditor is already working with data. Defining questions typically happens before data collection.
GTAG 16: Data Analysis Technologies – Covers data preparation, cleaning, and analytics in internal auditing.
IIA Practice Guide: Data Analytics in Internal Auditing – Outlines best practices for data validation and cleaning.
Step-by-Step Explanation:IIA References for Validation:Thus, cleaning the data (C) is the correct answer, as it ensures data integrity before identifying relevant processes and risks.
Which of the following statements is true regarding the capital budgeting procedure known as the discounted payback period?
Options:
It calculates the overall value of a project.
It ignores the time value of money.
It calculates the time a project takes to break even.
It begins at time zero for the project.
Answer:
CExplanation:
Comprehensive and Detailed In-Depth Explanation:
The discounted payback period is a capital budgeting technique that determines how long it takes for a project to recover its initial investment, accounting for the time value of money.
Option A (Calculates the overall project value) describes Net Present Value (NPV), not the payback period.
Option B (Ignores the time value of money) applies to the simple payback period, but the discounted payback period does account for the time value of money.
Option D (Begins at time zero) is true for all capital budgeting methods, not specific to this one.
Thus, option C is correct because the discounted payback period measures the break-even time while considering the present value of cash flows.
An organization has 10,000 units of a defect item in stock, per unit, market price is $10$; production cost is $4; and defect selling price is $5. What is the carrying amount (inventory value) of defects at your end?
Options:
$0
$4,000
$5,000
$10,000
Answer:
CExplanation:
The carrying amount (inventory value) of defective items is calculated based on the lower of cost or net realizable value (NRV) principle under Generally Accepted Accounting Principles (GAAP) and International Financial Reporting Standards (IFRS).
Given data:
Market price (normal selling price): $10 per unit
Production cost: $4 per unit
Defect selling price (NRV): $5 per unit
Total defective units: 10,000
Step 1: Determine the valuation rule
According to IAS 2 (Inventories), inventory should be valued at the lower of cost or net realizable value (NRV):
Cost per unit = $4
NRV per unit = $5
Since $4 (cost) < $5 (NRV), the cost per unit ($4) is used for valuation.
Step 2: Calculate total carrying amount
10,000 units×4 (cost per unit)=40,00010,000 \text{ units} \times 4 \text{ (cost per unit)} = 40,00010,000 units×4 (cost per unit)=40,000
However, since the items are defective, their value is determined by NRV ($5 per unit) because they cannot be sold at full market price.
10,000×5=50,00010,000 \times 5 = 50,00010,000×5=50,000
Since inventory should be recorded at the lower of cost or NRV, the inventory value is $5 per unit instead of $4.
10,000×5=5,00010,000 \times 5 = 5,00010,000×5=5,000
Thus, the verified answer is C. $5,000.
According to 11A guidance on IT, which of the following are indicators of poor change management?
1. Inadequate control design.
2. Unplanned downtime.
3. Excessive troubleshooting .
4. Unavailability of critical services.
Options:
2 and 3 only.
1, 2, and 3 only
1, 3, and 4 only
2, 3, and 4 only
Answer:
DExplanation:
Effective change management ensures that IT changes (such as software updates, system modifications, or infrastructure upgrades) are well-controlled, minimizing disruptions. Poor change management leads to instability, inefficiencies, and operational risks.
Unplanned Downtime (2) – Indicates that changes are being implemented without proper testing or failover planning, disrupting business operations.
Excessive Troubleshooting (3) – Suggests that changes are causing recurring issues, leading to increased workload for IT support teams.
Unavailability of Critical Services (4) – Highlights that change-related failures are affecting essential business functions, indicating improper risk assessment.
While inadequate control design is a general IT risk, it is not a direct indicator of poor change management. Instead, it relates more to weaknesses in IT governance and security frameworks.
IIA’s GTAG (Global Technology Audit Guide) on Change Management – Identifies unplanned downtime, excessive troubleshooting, and service unavailability as key red flags of poor change management.
COBIT 2019 (Governance and Management of IT) – Emphasizes structured change management to minimize disruptions.
ITIL Change Management Framework – Highlights these issues as symptoms of ineffective change control.
Why 2, 3, and 4 Are Indicators of Poor Change Management?Why Not Option 1 (Inadequate Control Design)?IIA References:✅ Final Answer: D. 2, 3, and 4 only.
Which of the following is an example of a phishing attack?
Options:
An organization’s website becomes flooded with malicious traffic on the first day of the online shopping season, causing the website to crash and preventing customers from purchasing deals online
The employees of a retail organization responded to emails with a link to malware that enabled a hacker to access the point-of-sale system and obtain customers’ credit card information
An organization’s employees clicked on a link that allowed a worm to infiltrate and encrypt the organization’s operating system, rendering it unusable. A group of hackers is demanding payment to unlock the encryption
A group of online activists hacked into the private email and confidential records of the local police department and released the information online to expose the corrupt practices of the department
Answer:
BExplanation:
Which of the following is an effective preventive control for data center security?
Options:
Motion detectors.
Key card access to the facility.
Security cameras.
Monitoring access to data center workstations
Answer:
BExplanation:
A preventive control is designed to stop security breaches before they happen. In data center security, preventing unauthorized physical access is crucial.
Prevents Unauthorized Entry – Restricts access only to authorized personnel.
Tracks and Logs Access – Records who enters and exits the data center, enhancing security monitoring.
Enhances Security Layers – Often combined with biometric authentication or PINs for stronger access control.
Meets IT Security Standards – Aligns with ISO 27001, NIST, and IIA’s GTAG recommendations on physical security.
A. Motion detectors – These are detective controls, identifying movement but not preventing unauthorized access.
C. Security cameras – Also detective, as they record events but do not prevent physical breaches.
D. Monitoring access to data center workstations – This ensures data integrity but does not prevent physical access.
IIA’s GTAG (Global Technology Audit Guide) on Information Security – Recommends strong physical access controls like key cards.
NIST SP 800-53 (Security and Privacy Controls for Federal Information Systems) – Emphasizes access control as a preventive security measure.
ISO 27001 Annex A.11 (Physical and Environmental Security) – Requires access control for secure areas, including data centers.
Why Key Card Access is the Best Preventive Control?Why Not the Other Options?IIA References:
As it relates to the data analytics process, which of the following best describes the purpose of an internal auditor who cleaned and normalized data?
Options:
The auditor eliminated duplicate information
The auditor organized data to minimize useless information
The auditor made data usable for a specific purpose by ensuring that anomalies were identified and addressed
The auditor ensured data fields were consistent and that data could be used for a specific purpose
Answer:
DExplanation:
Which of the following best describes the primary objective of cybersecurity?
Options:
To protect the effective performance of IT general and application controls.
To regulate users' behavior it the web and cloud environment.
To prevent unauthorized access to information assets.
To secure application of protocols and authorization routines.
Answer:
CExplanation:
Cybersecurity is primarily focused on protecting information assets by preventing unauthorized access, data breaches, cyberattacks, and other security threats. The confidentiality, integrity, and availability (CIA) triad is the foundation of cybersecurity, with access control playing a key role in mitigating risks.
(A) Incorrect – To protect the effective performance of IT general and application controls.
While cybersecurity supports IT controls, its primary goal is information security, not just control performance.
(B) Incorrect – To regulate users' behavior in the web and cloud environment.
Cybersecurity includes user behavior policies, but its primary goal is preventing unauthorized access rather than regulation.
(C) Correct – To prevent unauthorized access to information assets.
The core objective of cybersecurity is to prevent unauthorized access, protecting data from cyber threats.
This aligns with the CIA (Confidentiality, Integrity, Availability) security model.
(D) Incorrect – To secure application of protocols and authorization routines.
Protocols and authorization routines are part of cybersecurity controls, but they are not the primary objective.
IIA’s GTAG (Global Technology Audit Guide) – Cybersecurity Risks and Controls
Defines cybersecurity as the protection of information assets from unauthorized access and threats.
NIST Cybersecurity Framework – Access Control and Information Security
Focuses on preventing unauthorized access to sensitive systems.
COBIT Framework – IT Governance and Security
Emphasizes the protection of data and IT assets through cybersecurity measures.
Analysis of Answer Choices:IIA References and Internal Auditing Standards:
According to Maslow’s hierarchy of needs theory, which of the following best describes a strategy where a manager offers an assignment to a subordinate specifically to support his professional growth and future advancement?
Options:
Esteem by colleagues
Self-fulfillment
Sense of belonging in the organization
Job security
Answer:
BExplanation:
Which of the following functions of a quality assurance and improvement program (QAIP) must be performed by personnel independent of the internal audit function?
Options:
External assessments
Communication of QAIP results to the board
Disclosure of nonconformance
Internal assessments
Answer:
AExplanation:
A QAIP includes both internal and external assessments. While internal assessments can be performed by audit staff or within the activity, external assessments must be conducted by a qualified, independent party outside of the internal audit activity.
Options B and C are the CAE’s responsibilities. Option D (internal assessments) is not independent and is part of routine quality control.
Which of the following performance measures disincentives engaging in earnings management?
Options:
Linking performance to profitability measures such as return on investment.
Linking performance to the stock price.
Linking performance to quotas such as units produced.
Linking performance to nonfinancial measures such as customer satisfaction and employees training
Answer:
DExplanation:
Earnings management occurs when companies manipulate financial reporting to meet targets, often leading to unethical practices or financial misstatements. The best way to disincentivize earnings management is to link performance to nonfinancial measures such as customer satisfaction and employee training, which cannot be directly manipulated through financial reporting.
Avoiding Short-Term Financial Manipulation:
When performance is tied to financial metrics (e.g., return on investment, stock price, or production quotas), there is a higher risk of earnings manipulation, such as shifting revenues, deferring expenses, or aggressive accounting practices.
Nonfinancial measures, however, emphasize long-term value creation and are harder to manipulate.
Sustainable Business Growth:
Customer satisfaction and employee training foster long-term profitability by improving product quality, brand reputation, and workforce capabilities.
Companies focusing on these measures build sustainable competitive advantages without distorting financial results.
Regulatory and Ethical Considerations:
Internal auditors, following IIA Standard 2120 (Risk Management), must evaluate risks related to unethical financial reporting.
Regulatory bodies (e.g., SEC, PCAOB, and COSO) emphasize reducing the risk of fraudulent financial reporting by incorporating broader performance measures beyond financial results.
A. Linking performance to profitability measures such as return on investment:
ROI and similar metrics can pressure executives to inflate earnings or cut necessary expenses to meet short-term targets.
B. Linking performance to the stock price:
Stock-based incentives can lead to earnings manipulation (e.g., stock buybacks, revenue recognition adjustments) to inflate stock prices artificially.
C. Linking performance to quotas such as units produced:
Production-based targets can result in overproduction or quality compromises, leading to inefficient resource allocation and long-term financial issues.
IIA Standard 2120 (Risk Management): Internal auditors must assess risks related to financial reporting integrity.
COSO’s Internal Control Framework: Emphasizes performance measures beyond financial results to ensure ethical management practices.
IIA Practice Guide: Assessing Organizational Governance: Encourages balanced scorecards, including nonfinancial KPIs, to reduce financial misstatement risks.
Step-by-Step Justification:Why Not the Other Options?IIA References:Thus, the correct answer is D. Linking performance to nonfinancial measures such as customer satisfaction and employee training. ✅
An organization created a formalized plan for a large project. Which of the following should be the first step in the project management plan?
Options:
Estimate time required to complete the whole project.
Determine the responses to expected project risks.
Break the project into manageable components.
Identify resources needed to complete the project
Answer:
CExplanation:
The first step in a project management plan is to break the project into manageable components, known as Work Breakdown Structure (WBS). This step ensures clarity, task allocation, and effective tracking.
(A) Estimate time required to complete the whole project.
Incorrect: Time estimation comes after breaking the project into smaller tasks.
(B) Determine the responses to expected project risks.
Incorrect: Risk management is important but is planned after defining project tasks and scope.
(C) Break the project into manageable components. (Correct Answer)
Dividing the project into smaller tasks (WBS) helps in resource allocation, scheduling, and risk assessment.
IIA GTAG 12 – Project Risk Management suggests using WBS to define tasks clearly.
(D) Identify resources needed to complete the project.
Incorrect: Resources can only be allocated effectively after defining project components.
IIA GTAG 12 – Project Risk Management: Recommends Work Breakdown Structure (WBS) as the first step in project planning.
PMBOK (Project Management Body of Knowledge): Defines WBS as the foundation of project planning.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (C) Break the project into manageable components, as this is the first step in structuring and planning a successful project.
A clothing company sells shirts for $8 per shirt. In order to break even, the company must sell 25.000 shirts. Actual sales total S300.000. What is margin of safety sales for the company?
Options:
$100.000
$200,000
$275,000
$500,000
Answer:
BExplanation:
Understanding the Margin of Safety Concept:
Margin of Safety (MoS) measures how much sales can drop before the business reaches its break-even point.
It is calculated as: Margin of Safety Sales=Actual Sales−Break-even Sales\text{Margin of Safety Sales} = \text{Actual Sales} - \text{Break-even Sales}Margin of Safety Sales=Actual Sales−Break-even Sales
Applying the Formula:
Selling Price per Shirt: $8
Break-even Sales Volume: 25,000 shirts
Break-even Sales Value: 25,000×8=200,00025,000 \times 8 = 200,00025,000×8=200,000
Actual Sales Revenue: $300,000
Margin of Safety: 300,000−100,000=200,000300,000 - 100,000 = 200,000300,000−100,000=200,000
Why Option B ($200,000) Is Correct?
The margin of safety is the difference between actual and break-even sales.
The correct calculation confirms $200,000 as the margin of safety.
IIA Standard 2120 – Risk Management supports financial risk analysis, including break-even and margin of safety evaluations.
Why Other Options Are Incorrect?
Option A ($100,000): Incorrect subtraction.
Option C ($275,000): Incorrect calculation, not based on break-even sales.
Option D ($500,000): Irrelevant and exceeds actual sales.
The correct margin of safety is $200,000, calculated using standard break-even analysis.
IIA Standard 2120 emphasizes financial risk evaluation in decision-making.
Final Justification:IIA References:
IPPF Standard 2120 – Risk Management (Financial Performance & Cost Analysis)
COSO ERM – Financial Stability & Revenue Risk
Management Accounting Best Practices – Break-even & Margin of Safety Calculations
The engagement supervisor prepares the final engagement communication for dissemination. Since the chief audit executive (CAE) is on leave, the supervisor is delegated to disseminate the final engagement communication to all relevant parties. Who should be accountable for the final engagement communication?
Options:
Engagement supervisor
Chief audit executive
The board
The internal audit team
Answer:
BExplanation:
The CAE is ultimately accountable for all final engagement communications, even if dissemination is delegated to others. The Standards hold the CAE responsible for ensuring that reports are accurate, objective, clear, concise, constructive, complete, and timely.
Options A and D (supervisor or team) may assist but do not hold accountability. Option C (the board) receives reports but is not responsible for them.
Which of the following is the best example of IT governance controls?
Options:
Controls that focus on segregation of duties, financial, and change management,
Personnel policies that define and enforce conditions for staff in sensitive IT areas.
Standards that support IT policies by more specifically defining required actions
Controls that focus on data structures and the minimum level of documentation required
Answer:
AExplanation:
IT governance controls ensure that an organization's IT systems align with business objectives, manage risks, and comply with regulatory requirements. These controls cover areas such as security, financial oversight, change management, and operational efficiency.
Let’s analyze each option:
Option A: Controls that focus on segregation of duties, financial, and change management.
Correct.
Segregation of duties (SoD) prevents conflicts of interest and reduces fraud risk.
Financial controls ensure IT expenditures align with budgets and policies.
Change management controls ensure system modifications follow formal approval and testing procedures.
These areas are core components of IT governance, ensuring security, compliance, and efficiency.
IIA Reference: Internal auditors evaluate IT governance using frameworks like COBIT (Control Objectives for Information and Related Technologies) and ISO 27001. (IIA GTAG: Auditing IT Governance)
Option B: Personnel policies that define and enforce conditions for staff in sensitive IT areas.
Incorrect.
While personnel policies support IT security, they do not fully represent IT governance controls. IT governance is broader and includes risk management, compliance, and operational efficiency.
Option C: Standards that support IT policies by more specifically defining required actions.
Incorrect.
Standards are part of IT governance but are not controls themselves. IT governance requires enforcement mechanisms like segregation of duties and change management to ensure compliance.
Option D: Controls that focus on data structures and the minimum level of documentation required.
Incorrect.
While data governance is a subset of IT governance, IT governance includes wider financial, security, and operational controls.
Thus, the verified answer is A. Controls that focus on segregation of duties, financial, and change management.
Which of the following bring-your-own-device (BYOD) practices is likely to increase the risk of infringement on local regulations, such as copyright or privacy laws?
Options:
Not installing anti-malware software.
Updating operating software in a haphazard manner.
Applying a weak password for access to a mobile device.
Jailbreaking a locked smart device.
Answer:
DExplanation:
Comprehensive and Detailed In-Depth Explanation:
Jailbreaking a locked smart device (removing manufacturer-imposed restrictions) increases the risk of infringing on copyright and privacy laws, as it allows unauthorized access to software and applications.
Option A (Not installing anti-malware software) – Increases security risks but does not directly violate regulations.
Option B (Haphazard OS updates) – Can lead to vulnerabilities but is not a legal issue.
Option C (Weak passwords) – Poses a security threat but does not impact compliance with laws.
Since jailbreaking often violates software licenses and may lead to illegal use of software, Option D is the correct answer.
An organization with global headquarters in the United States has subsidiaries in eight other nations. If the organization operates with an ethnocentric attitude, which of the following statements is true?
Options:
Standards used for evaluation and control are determined at local subsidiaries, not set by headquarters
Orders, commands, and advice are sent to the subsidiaries from headquarters
People of local nationality are developed for the best positions within their own country
There is a significant amount of collaboration between headquarters and subsidiaries
Answer:
BExplanation:
Which of the following would be most likely found in an internal audit procedures manual?
Options:
A summary of the strategic plan of the area under review
Appropriate response options for when findings are disputed by management
An explanation of the resources needed for each engagement
The extent of the auditor's authority to collect data from management
Answer:
BExplanation:
The internal audit procedures manual documents policies and procedures for conducting audit engagements, including steps to follow when issues arise, such as disputes with management regarding findings. It ensures consistency and standardization of audit practice.
Option A (strategic plan) and Option C (resources) are not part of audit procedures but rather part of planning or organizational documents. Option D (authority to collect data) belongs in the internal audit charter, not in the procedures manual.
Therefore, the correct answer is appropriate response options for disputes with management (Option B).
Which of the following parties is most likely to be responsible for maintaining the infrastructure required to prevent the failure of a real-time backup of a database?
Options:
IT database administrator.
IT data center manager.
IT help desk function.
IT network administrator.
Answer:
AExplanation:
Maintaining the infrastructure for a real-time database backup involves ensuring that backups are correctly configured, continuously running, and fail-safe mechanisms are in place to prevent data loss. The most appropriate role for this responsibility is the IT database administrator (DBA) because:
Primary Role of a DBA:
The DBA is responsible for managing database performance, availability, backup strategies, and recovery processes.
Ensures that real-time backups are functioning properly and failure risks are mitigated.
Database Infrastructure & Backup Strategies:
DBAs configure, monitor, and troubleshoot real-time backup solutions such as replication, mirroring, and log shipping.
They work with backup tools like Oracle Data Guard, SQL Server Always On, and MySQL replication.
Disaster Recovery & Data Integrity:
The DBA ensures data consistency and integrity, especially during system failures or cyber incidents.
They set up recovery point objectives (RPO) and recovery time objectives (RTO) for database resilience.
Option B (IT Data Center Manager):
Oversees physical and environmental infrastructure (e.g., servers, cooling, and power systems). Not directly responsible for database backup failure prevention. (Incorrect)
Option C (IT Help Desk Function):
Provides user support and troubleshooting but does not manage backup infrastructure. (Incorrect)
Option D (IT Network Administrator):
Manages network configurations, security, and connectivity but does not handle database backup infrastructure. (Incorrect)
IIA GTAG – "Auditing Business Continuity and Disaster Recovery": Emphasizes the role of DBAs in backup infrastructure.
COBIT 2019 – BAI10.02 (Manage Backup and Restore): Assigns database backup management responsibilities primarily to DBAs.
IIA's "Auditing IT Operations": Recommends that database administration teams ensure backup mechanisms are tested regularly.
Why Other Options Are Incorrect:IIA References:Thus, the correct answer is A. IT database administrator.
During an internal audit engagement, it was found that several vendors were on a government sanctions list and must no longer be traded with. Which of the following would most effectively mitigate the risk of noncompliance with sanctions lists that are updated regularly?
Options:
Agreements with sanctioned vendors discovered by internal audit will be placed on hold until further notice from the government
A new procedure of vendor onboarding will be implemented to ensure that all new vendors undergo screenings against the sanctions list
Controls will be embedded in the vendor management processes to ensure that new and existing vendors are compliant with changes to the sanctions list
The legal team will be asked to prepare counter arguments to dispute audit findings and potential inquiries from the governmental authority
Answer:
CExplanation:
The most effective mitigation is to embed ongoing controls within vendor management processes to ensure that both new and existing vendors are continuously screened against updated sanctions lists. This creates a sustainable and automated compliance mechanism.
Option A is reactive and does not address future compliance. Option B only addresses onboarding of new vendors but ignores existing ones. Option D undermines compliance obligations and does not mitigate risk.
Which of the following controls would be most efficient to protect business data from corruption and errors?
Options:
Controls to ensure data is unable to be accessed without authorization.
Controls to calculate batch totals to identify an error before approval.
Controls to encrypt the data so that corruption is likely ineffective.
Controls to quickly identify malicious intrusion attempts.
Answer:
BExplanation:
To efficiently protect business data from corruption and errors, the best approach is proactive detection through validation controls. Batch total calculations help verify data integrity before approval, ensuring errors are caught early.
(A) Controls to ensure data is unable to be accessed without authorization.
Incorrect: Access controls prevent unauthorized access, but they do not detect or prevent data corruption/errors.
(B) Controls to calculate batch totals to identify an error before approval. (Correct Answer)
Batch control totals ensure that data entries match expected values before processing, helping detect errors before approval.
IIA GTAG 3 – Continuous Auditing recommends automated validation and reconciliation checks for data integrity.
(C) Controls to encrypt the data so that corruption is likely ineffective.
Incorrect: Encryption protects data confidentiality, but it does not prevent or detect errors or corruption.
(D) Controls to quickly identify malicious intrusion attempts.
Incorrect: Intrusion detection systems focus on cybersecurity, not data corruption or errors.
IIA Standard 2120 – Risk Management: Recommends controls for error prevention and early detection.
IIA GTAG 3 – Continuous Auditing: Suggests automated validation processes like batch totals to detect errors before approval.
Analysis of Each Option:IIA References Supporting the Answer:Thus, the correct answer is (B) because batch total calculations effectively detect errors before approval, ensuring data integrity.
Which of the following would be classified as IT general controls?
Options:
Error listings.
Distribution controls.
Transaction logging.
Systems development controls.
Answer:
DExplanation:
IT General Controls (ITGCs) refer to foundational IT controls that support the reliability and security of information systems across all applications. Systems development controls fall under ITGCs because they ensure that:
IT systems are developed, tested, and implemented securely.
Change management, system testing, and access controls are enforced before deployment.
Ensuring Secure Development Practices:
IIA GTAG 8: Auditing Application Controls states that strong systems development controls prevent unauthorized access and errors in IT systems.
Risk Mitigation in Software Changes:
IIA Standard 2110 – Governance requires IT governance to enforce security policies for system development.
Weak controls increase risks of security vulnerabilities and financial misstatements.
Alignment with COSO & COBIT Frameworks:
COBIT (Control Objectives for Information and Related Technologies) classifies systems development controls as an ITGC domain.
COSO Internal Control – Integrated Framework supports secure system change processes.
A. Error listings (Incorrect)
Reason: Error listings are application controls that detect transaction errors within specific processes. ITGCs support all systems, not just specific applications.
B. Distribution controls (Incorrect)
Reason: Distribution controls deal with physical/logistical distribution of information or resources, not core ITGC functions.
C. Transaction logging (Incorrect)
Reason: While transaction logging is important for data integrity and security, it is an application control, not a general IT control.
IIA GTAG 8: Auditing Application Controls – Defines IT general controls and application-specific controls.
IIA Standard 2110 – Governance – Requires secure IT development and governance structures.
COBIT & COSO Internal Control Frameworks – Classify system development controls as critical ITGCs.
Why is Answer D Correct?Analysis of Incorrect Answers:IIA References:Thus, the correct answer is D. Systems development controls.
An organization and its trading partner rely on a computer-to-computer exchange of digital business documents. Which of the following best describes this scenario?
Options:
Use of a central processing unit
Use of a database management system
Use of a local area network
Use of electronic data Interchange
Answer:
DExplanation:
Electronic Data Interchange (EDI) refers to the computer-to-computer exchange of business documents (such as purchase orders, invoices, and shipping notices) in a standard electronic format between business partners.
Correct Answer (D - Use of Electronic Data Interchange)
EDI enables real-time, automated business transactions between companies, reducing errors and increasing efficiency.
The IIA GTAG 8: Audit of Inventory Management highlights EDI as a critical system for supply chain and procurement operations.
Why Other Options Are Incorrect:
Option A (Use of a Central Processing Unit - CPU):
A CPU is a hardware component, not a method for exchanging business documents.
Option B (Use of a Database Management System - DBMS):
A DBMS stores and manages data but does not facilitate external document exchange between trading partners.
Option C (Use of a Local Area Network - LAN):
A LAN connects computers within an organization but does not enable document exchange between separate businesses.
IIA GTAG 8: Audit of Inventory Management – Discusses EDI as an essential tool for automating business transactions.
IIA Practice Guide: Auditing IT Controls – Recommends EDI for secure and efficient document exchange.
Step-by-Step Explanation:IIA References for Validation:Thus, D is the correct answer because EDI is the best system for automated, computer-to-computer business document exchange.
Unlock IIA-CIA-Part3 Features
- IIA-CIA-Part3 All Real Exam Questions
- IIA-CIA-Part3 Exam easy to use and print PDF format
- Download Free IIA-CIA-Part3 Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet
Questions & Answers PDF Demo
- IIA-CIA-Part3 All Real Exam Questions
- IIA-CIA-Part3 Exam easy to use and print PDF format
- Download Free IIA-CIA-Part3 Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet
