Fortinet NSE6_SDW_AD-7.6 Fortinet NSE 6 - SD-WAN 7.6 Enterprise Administrator Exam Practice Test
Fortinet NSE 6 - SD-WAN 7.6 Enterprise Administrator Questions and Answers
Refer to the exhibits.
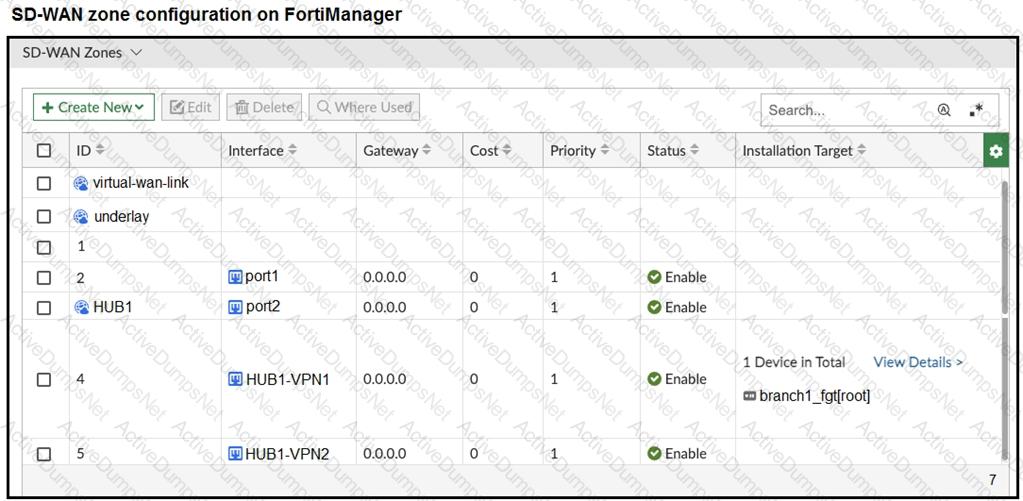
The exhibits show the SD-WAN zone configuration of an SD-WAN template prepared on FortiManager and the policy package configuration.
When the administrator tries to install the configuration changes, FortiManager fails to commit.
What should the administrator do to fix the issue?
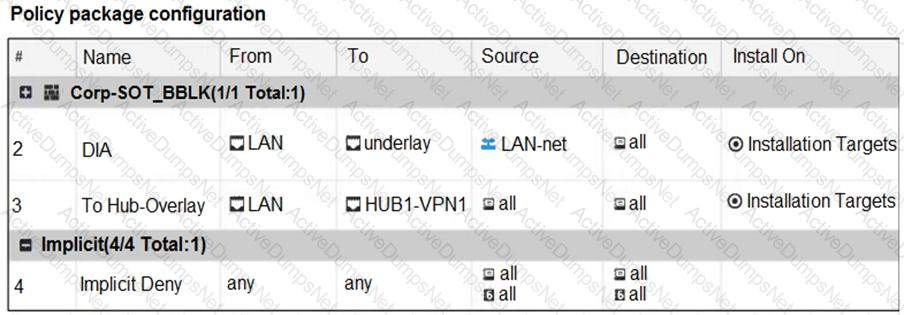
Refer to the exhibit.
The administrator analyzed the traffic between a branch FortiGate and the server located in the data center, and noticed the behavior shown in the diagram.
When the LAN clients located behind FGT1 establish a session to a server behind DC-1, the administrator observes that, on DC-1, the reply traffic is routed overT2. even though T1 is the preferred member in
the matching SD-WAN rule.
What can the administrator do to instruct DC-1 to route the reply traffic through the member with the best performance?
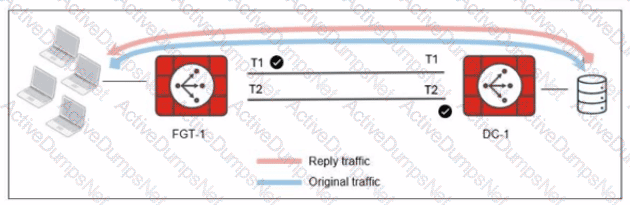
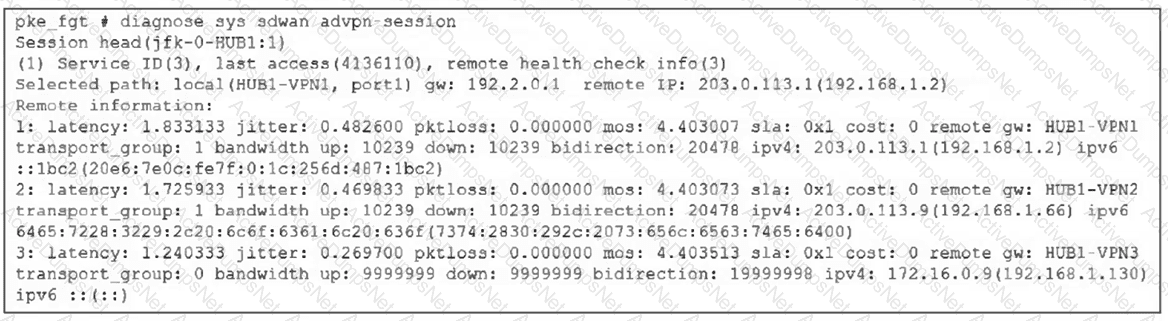
Refer to the exhibit.
Which two conclusions can you draw from the output shown? (Choose two.)
(When you deploy SD-WAN, you can choose from several common designs. Each design best applies to specific contexts.
Which two statements correctly associate a common SD-WAN design with its main indication or constraint? Choose two answers.)
Refer to the exhibit.
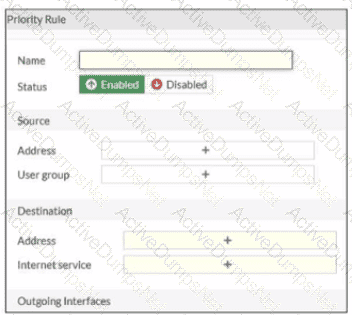
An administrator configures SD-WAN rules for a DIA setup using the FortiGate GUI. The page to configure the source and destination part of the rule looks as shown in the exhibit. The GUI page shows no option to configure an application as the destination of the SD-WAN rule Why?
You have configured the performance SLA with the probe mode as Prefer Passive.
What are two observable impacts of this configuration? (Choose two.)
Refer to the exhibit.
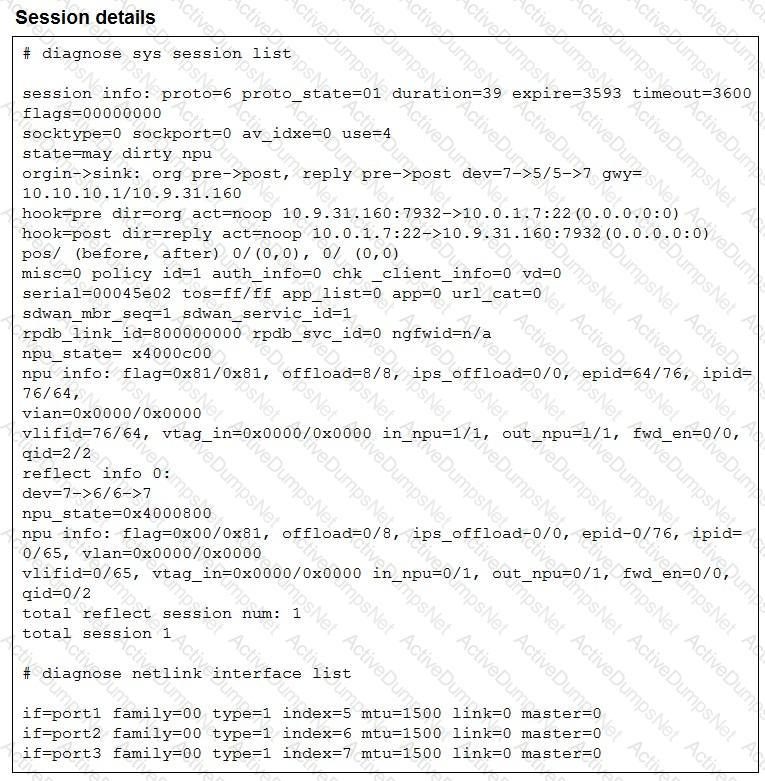
The exhibit shows the details of a session and the index numbers of some relevant interfaces on a FortiGate device that supports hardware offloading.
Based on the information shown in the exhibits, which two conclusions can you draw? (Choose two.)
As an MSSP administrator, you are asked to configure ADVPN on an existing SD-WAN topology. FortiManager manages the customer devices in a dedicated ADOM. The previous administrator used the SD-WAN overlay topology.
Which two statements apply to this scenario? (Choose two.)
Within the context of SD-WAN, what does SIA correspond to?
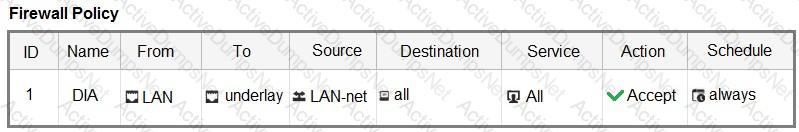
Refer to the exhibits.
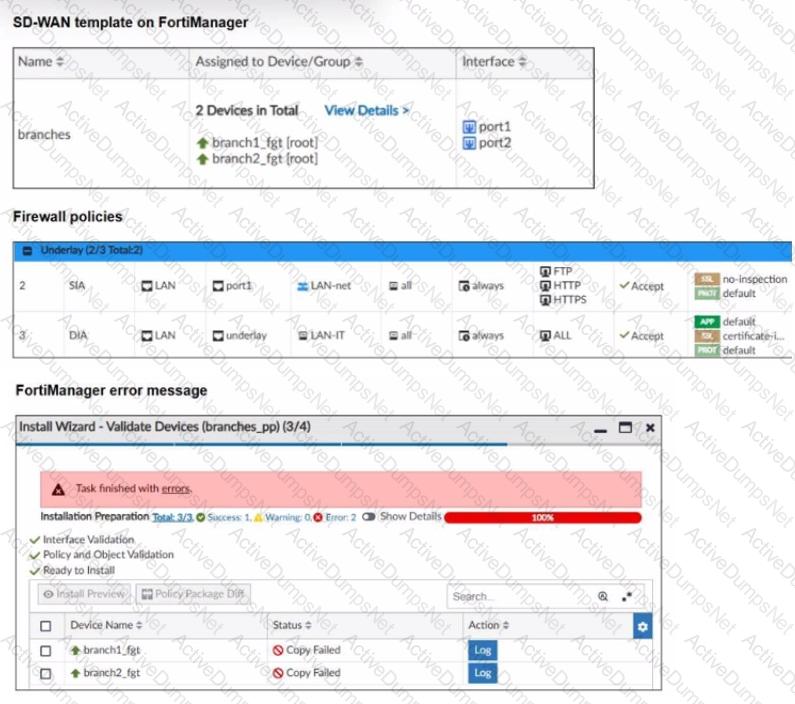
You use FortiManager to manage the branch devices and configure the SD-WAN template. You have configured direct internet access (DIA) for the IT department users. Now. you must configure secure internet access (SIA) for all local LAN users and have set the firewall policies as shown in the second exhibit.
Then, when you use the install wizard to install the configuration and the policy package on the branch devices, FortiManager reports an error as shown in the third exhibit.
Which statement describes why FortiManager could not install the configuration on the branches?
Which statement describes FortiGate behavior when you reference a zone in a static route?
Your FortiGate is in production. To optimize WAN link use and improve redundancy, you enable and configure SD-WAN.
What must you do as part of this configuration update process?
Refer to the exhibit that shows an SD-WAN zone configuration on the FortiManager GUI.
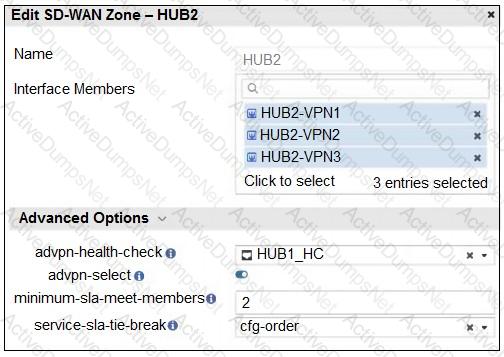
Based on the exhibit, how will the FortiGate device behave after it receives this configuration?
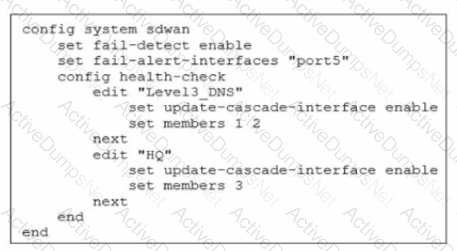
Refer to the exhibit.
The exhibit shows the health-check configuration on a FortiGate device used as a spoke. You notice that the hub FortiGate doesn’t prioritize the traffic as expected.
Which two configuration elements should you check on the hub? (Choose two.)
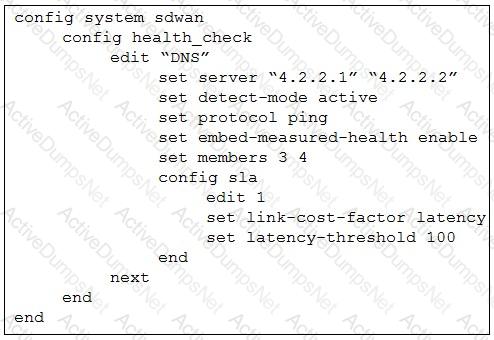
Refer to the exhibits, which show the configuration of an SD-WAN rule and the corresponding rule status and routing table.
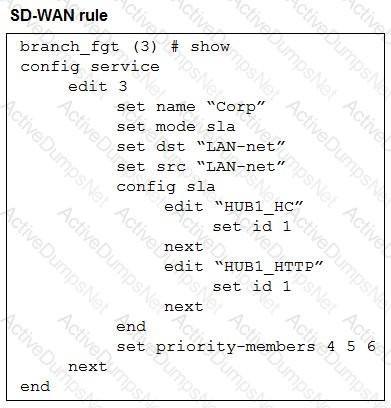
The administrator wants to understand the expected behavior for traffic matching the SD-WAN rule.
Based on the exhibits, what can the administrator expect for traffic matching the SD-WAN rule?
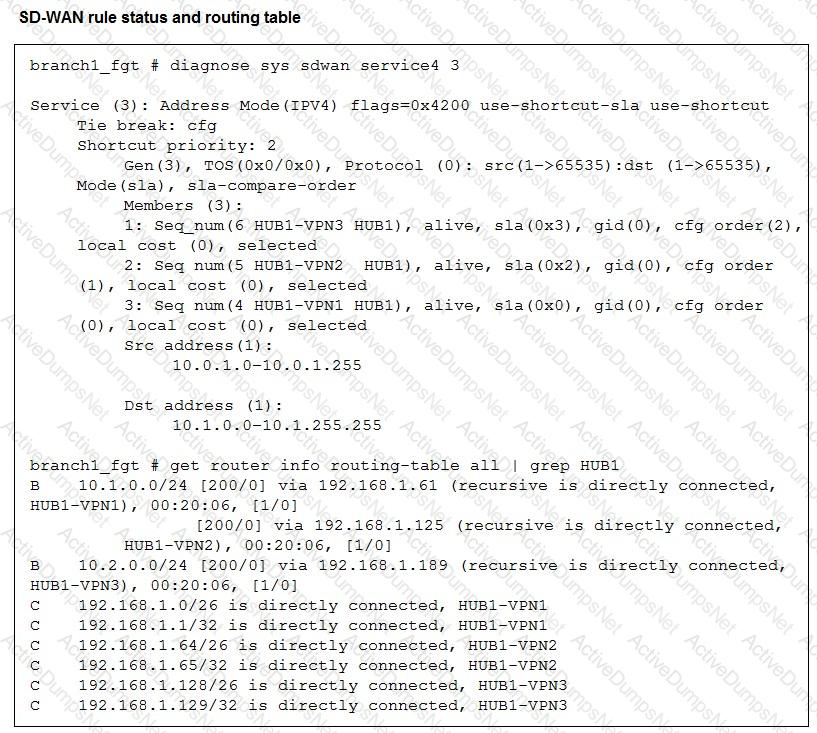
(Refer to the exhibits.
Two SD-WAN event logs, the member status, the SD-WAN rule configuration, and the health-check configuration for a FortiGate device are shown.
Immediately after the log messages are displayed, how will the FortiGate steer the traffic based on the information shown in the exhibits? Choose one answer.)
Exhibit.
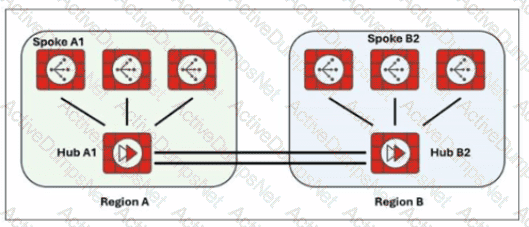
Two hub-and-spoke groups are connected through redundant site-to-site IPsec VPNs between Hub 1 and Hub 2
Which two configuration settings are required for the spoke A1 to establish an ADVPN shortcut with the spoke B2? (Choose two.)
(Refer to the exhibit.
Based on the output shown in the exhibit, what can you conclude about the device role and how it handles health checks? Choose one answer.)
Refer to the exhibit.
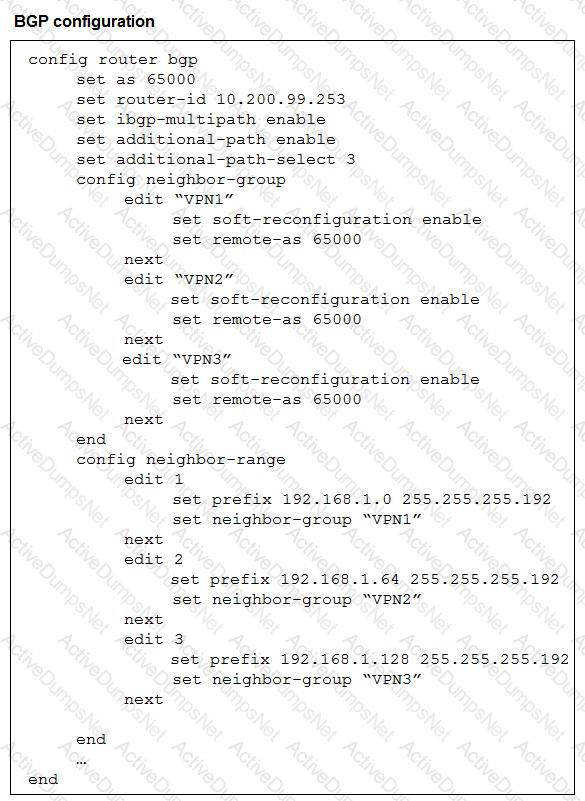
The exhibit shows the BGP configuration on the hub in a hub-and-spoke topology. The administrator wants BGP to advertise prefixes from spokes to other spokes over the IPsec overlays, including additional paths. However, when looking at the spoke routing table, the administrator does not see the prefixes from other spokes and the additional paths
Which three settings must the administrator configure inside each BGP neighbor group so spokes can learn the prefixes of other spokes and their additional paths? (Choose three.)
The FortiGate devices are managed by ForliManager, and are configured for direct internet access (DIA). You confirm that DIA is working as expected for each branch, and check the SD-WAN zone configuration and firewall policies shown in the exhibits.
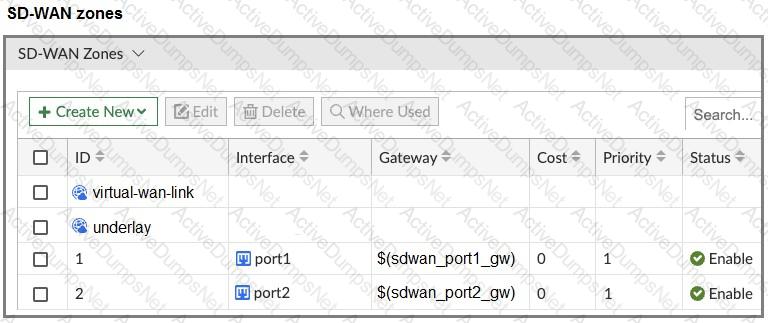
Then, you use the SD-WAN overlay template to configure the IPsec overlay tunnels. You create the associated SD-WAN rules to connect existing branches to the company hub device and apply the changes on the branches.
After those changes, users complain that they lost internet access. DIA is no longer working.
Based on the exhibit, which statement best describes the possible root cause of this issue?
You used the HUB IPsec_Recommended and the BRANCH IPsec_Recommended templates to define the overlay topology. Then, you used the SD-WAN template to define the SD- WAN members, rules, and performance SLAs.
You applied the changes to the devices and want to use the FortiManager monitors menu to get a graphical view that shows the status of each SD-WAN member.
Which statement best explains how to obtain this graphical view?
Refer to the exhibits.

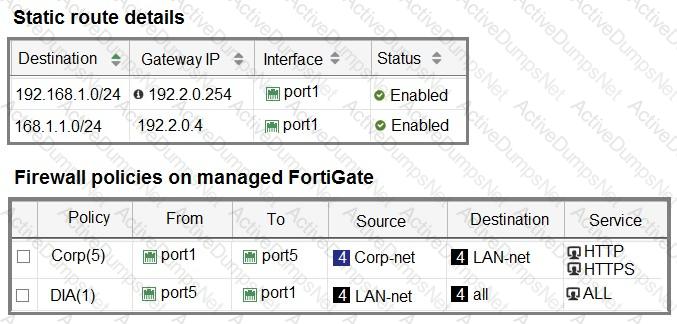
The interface details, static route configuration, and firewall policies on the managed FortiGate device are shown.
You want to configure a new SD-WAN zone, named Underlay, that contains the interfaces port1 and port2.
What must be your first action?
Exhibit.
Which action will FortiGate take if it detects SD-WAN members as dead?
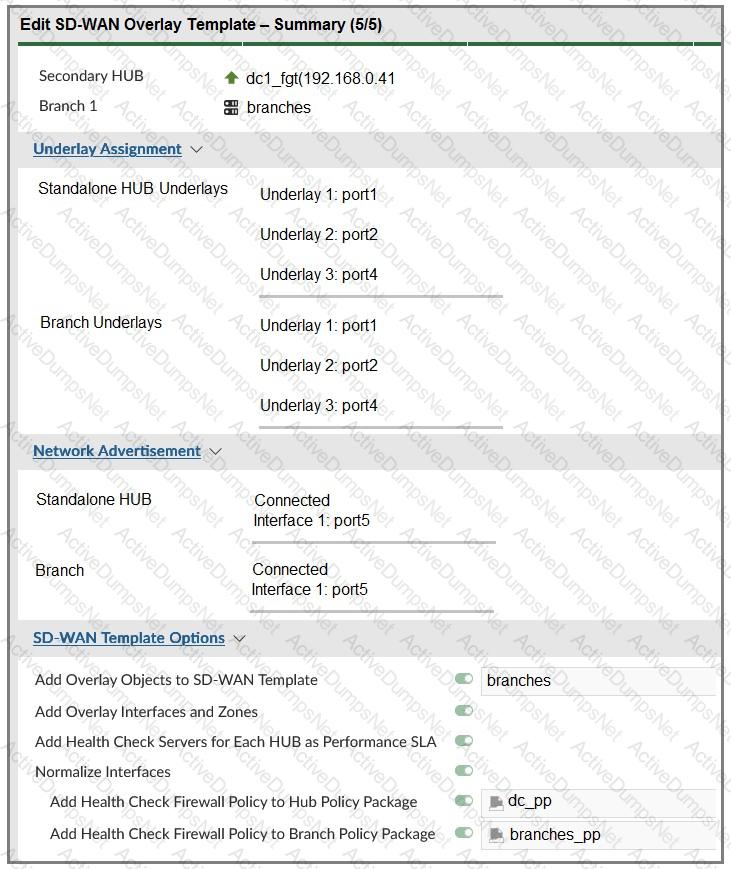
(Refer to the exhibits.
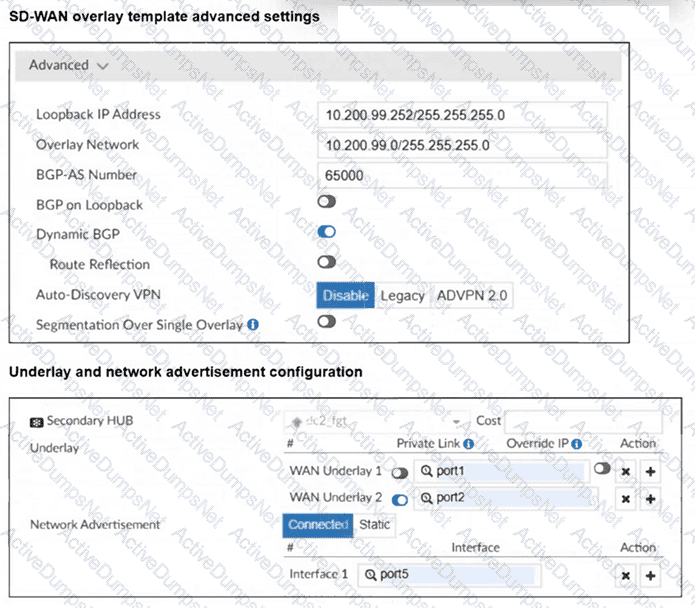
The SD-WAN overlay template advanced settings and the underlay and network advertisement settings are shown. These are the configurations for the secondary hub of a dual-hub SD-WAN topology created with the FortiManager SD-WAN overlay orchestrator.
Which two conclusions can you draw from the information shown in the exhibits? Choose two answers.)
Which three characteristics apply to provisioning templates available on FortiManager? (Choose three.)
When you use the command diagnose sys session list, how do you identify the sessions that correspond to traffic steered according to SD-WAN rules?
Refer to the exhibit.
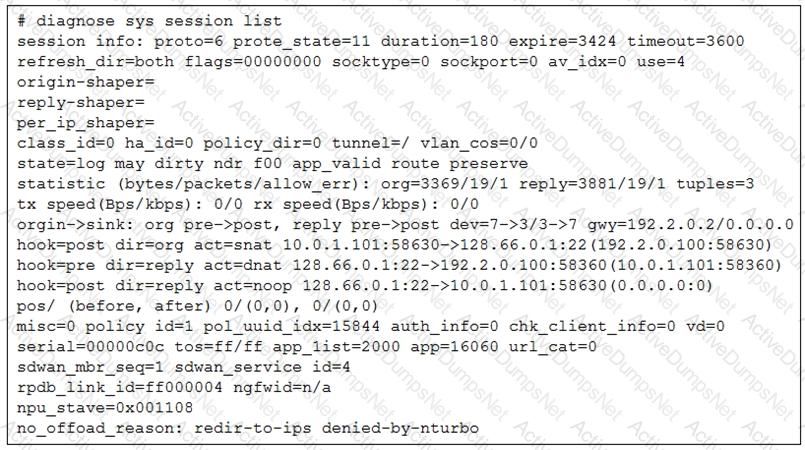
The administrator configured the SD-WAN rule ID 4 with two members (port1 and port2) and strategy lowest cost (SLA).
What are the two characteristics of the session shown in the exhibit? (Choose two.)
(Refer to the exhibit.
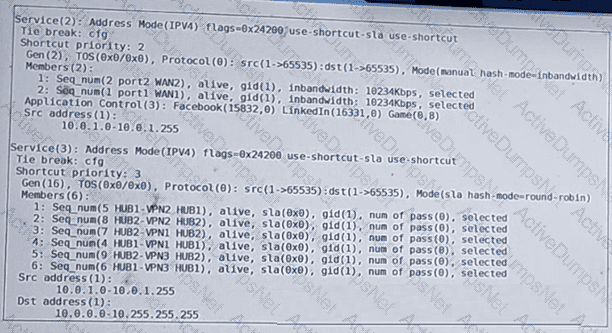
The administrator configured two SD-WAN rules to load balance traffic.
Which interfaces does FortiGate use to steer the traffic from 10.0.1.124 to 10.0.0.254 ? Choose one answer.)
