Fortinet NSE6_OTS_AR-7.6 Fortinet NSE 6 - OT Security 7.6 Architect Exam Practice Test
Fortinet NSE 6 - OT Security 7.6 Architect Questions and Answers
Refer to the exhibit.

The OT devices behind the ruggedized FortiGate have vulnerabilities and you want to apply a virtual patching profile in the firewall policy. Why is Virtual Patching not available in the Security Profiles section? (Choose one answer)
In the Purdue model, at which level are physical assets like the Industrial Internet of Things (IIoT) placed? (Choose one answer)
Refer to the exhibits.
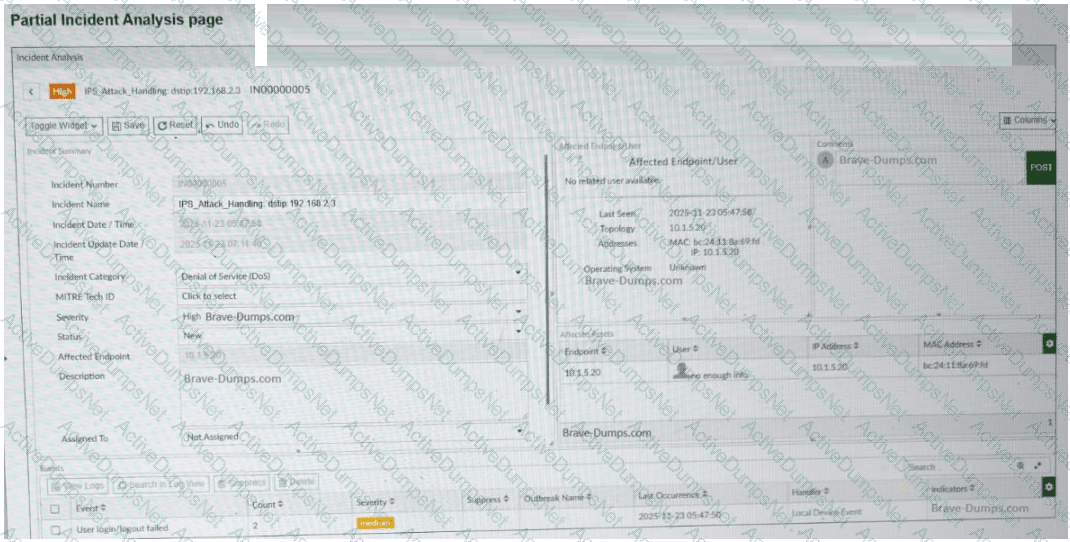
A partial Incident Analysis page and the log details related to the event are shown. An attack is reported on your OT network. You analyze the corresponding incident. Based on the information provided on the Incident Analysis page and the log details, which two statements are correct? (Choose two answers)
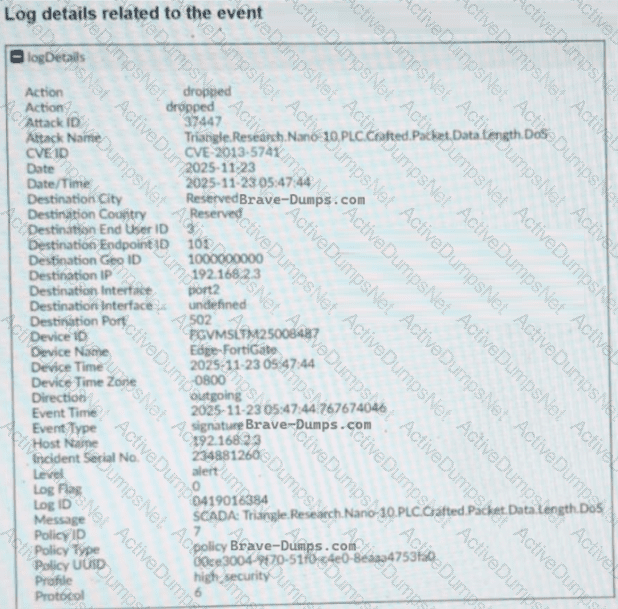
Refer to the exhibit.
A firewall policy page is shown. To improve the security of your OT network, you have configured a Supervisor profile in the firewall policies, as shown in the exhibit. However, a supervisor is reporting that he cannot ping PLC-1. What are the two reasons? (Choose two answers)
What is the main OT component for monitoring and controlling industrial processes? (Choose one answer)
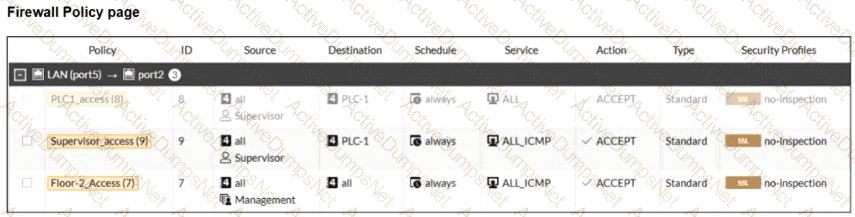
Refer to the exhibit.
A simplified OT network is shown. You want to optimize the protection of this OT network. Which two controls must you implement? (Choose two answers)
Refer to the exhibit.
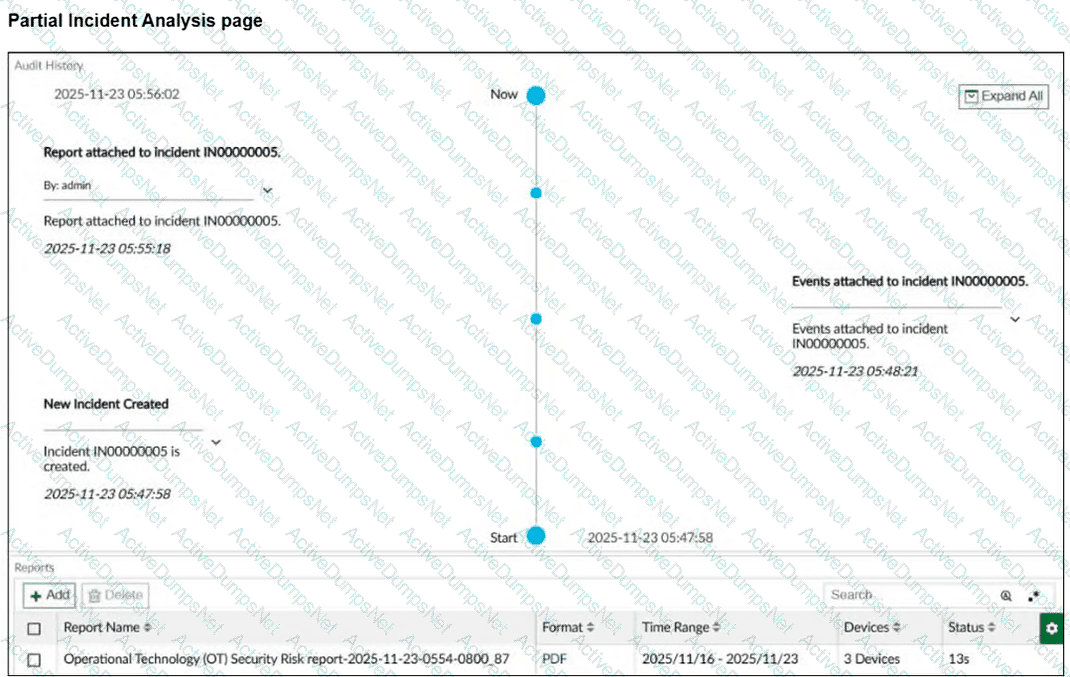
A partial Incident Analysis page is shown. How was the 360-Degree Security Review OT report attached to the incident? (Choose one answer)
Refer to the exhibit.
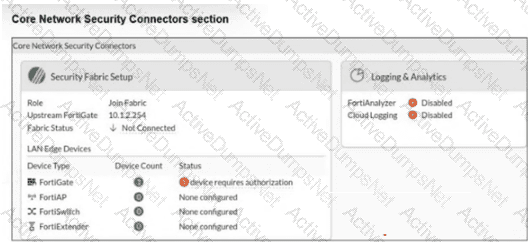
The Core Network Security Connectors page of the FortiGate-2 device is shown. Which statement is correct? (Choose one answer)
You want to automate some tasks in your OT network. Which three configurations are directly available in a new basic event handler on FortiAnalyzer? (Choose three answers)
Refer to the exhibit.
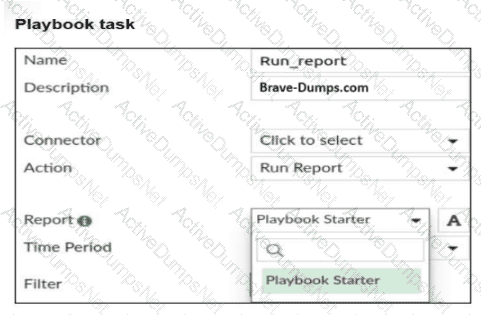
A Run_report task is shown. You want to automate the generation of a newly created report on FortiAnalyzer . When you configure the Run_report task in Playbook, why is the report not shown in the Report field? (Choose two answers)
Refer to the exhibit.
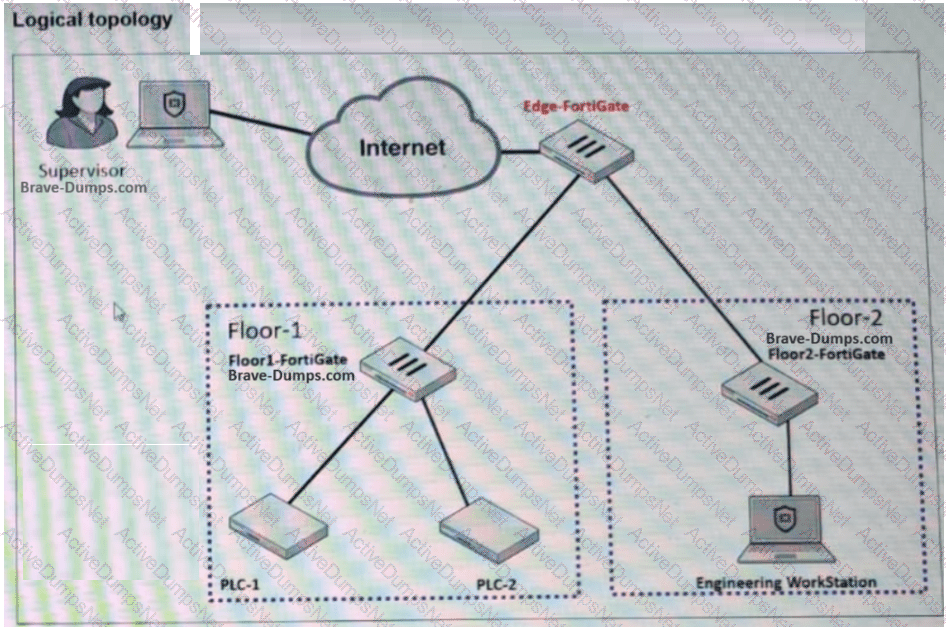
A partial OT network is shown. You want to provide the supervisor with secure remote access. Which two features can you implement on Edge-FortiGate ? (Choose two answers)
You want FortiAnalyzer to trigger an automation stitch on a FortiGate device automatically. What must you configure on FortiAnalyzer to enable direct communication with FortiGate? (Choose one answer)
Refer to the exhibit.
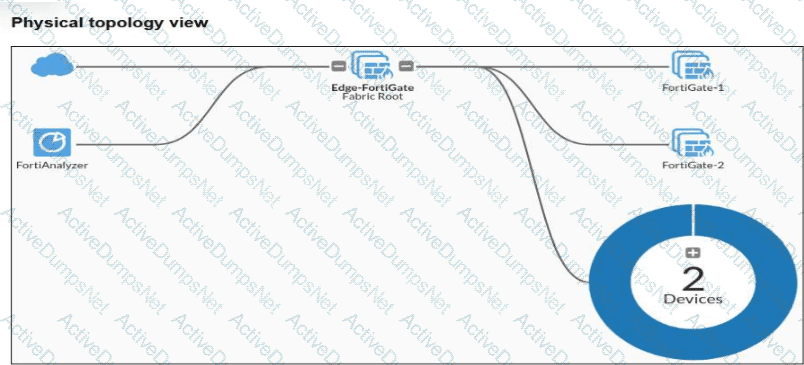
Why is the OT View tab not available in the Asset Identity Center section of the FortiGate-1 device? (Choose one answer)
