- Home
- Fortinet
- Fortinet Network Security Expert
- NSE5_SSE_AD-7.6
- NSE5_SSE_AD-7.6 - Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator
Fortinet NSE5_SSE_AD-7.6 Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator Exam Practice Test
Fortinet NSE 5 - FortiSASE and SD-WAN 7.6 Core Administrator Questions and Answers
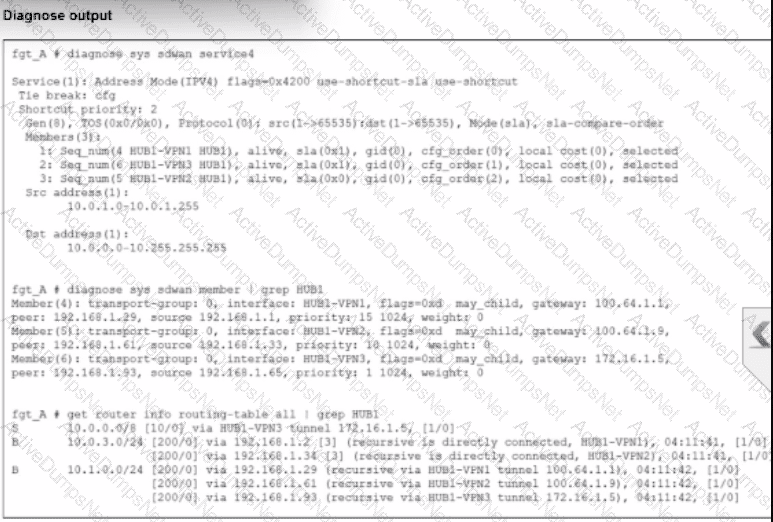
An administrator is troubleshooting SD-WAN on FortiGate. A device behind branch1_fgt generates traffic to the 10.0.0.0/8 network. The administrator expects the traffic to match SD-WAN rule ID 1 and be routed over HUB1-VPN1. However, the traffic is routed over HUB1-VPN3.
Based on the output shown in the exhibit, which two reasons, individually or together, could explain the observed behavior? (Choose two.)
Options:
HUB1-VPN1 does not have a valid route to the destination.
HUB1-VPN3 has a higher member configuration priority than HUB1-VPN1.
HUB1-VPN3 has a lower route priority value (higher priority) than HUB1-VPN1.
The traffic matches a regular policy route configured with HUB1-VPN3 as the outgoing device.
Answer:
A, CExplanation:
According to theSD-WAN 7.6 Core Administratorcurriculum and the diagnostic outputs shown in the exhibit, the reason traffic is steered toHUB1-VPN3instead of the expectedHUB1-VPN1(defined in SD-WAN rule ID 1) can be explained by two core routing principles in FortiOS:
Valid Route Requirement (Option A): In thediagnose sys sdwan service 4output (which corresponds to Rule ID 1), it shows the rule has membersHUB1-VPN1,HUB1-VPN2, andHUB1-VPN3. A key principle of SD-WAN steering is that for a member to be "selectable" by a rule, itmust have a valid route to the destinationin the routing table (RIB/FIB). If the routing table output (the third section of the exhibit) shows a route to 10.0.0.0/8 viaHUB1-VPN3butnotthroughHUB1-VPN1, the SD-WAN engine will skip HUB1-VPN1 entirely because it is considered a "non-reachable" path for that specific destination.
Policy Route Precedence (Option D): In the FortiOS route lookup hierarchy,Regular Policy Routes (PBR)are evaluatedbeforeSD-WAN rules. If an administrator has configured a traditional Policy Route (found underNetwork > Policy Routes) that matches traffic destined for 10.0.0.0/8 and specifiesHUB1-VPN3as the outgoing interface, the FortiGate will forward the packet based on that policy route and willnever evaluate the SD-WAN rulesfor that session. This "bypass" occurs regardless of whether the SD-WAN rule would have chosen a "better" link.
Why other options are incorrect:
Option B: While member configuration priority (cfg_order) is a tie-breaker in some strategies, the SD-WAN rule logic is only applied if the routing table allows it or if a higher-priority policy route doesn't intercept the traffic first.
Option C: Lower route priority (which means higher preference in the RIB) affects theImplicit Rule(standard routing). However, SD-WAN rules are designed tooverrideRIB priority for matching traffic. If HUB1-VPN1 was a valid candidate and no Policy Route existed, the SD-WAN rule would typically ignore RIB priority to enforce its own steering strategy.
Which configuration is a valid use case for FortiSASE features in supporting remote users?
Options:
Enabling secure SaaS access through SD-WAN integration, protecting against web-based threats with data loss prevention, and monitoring user connectivity with shadow IT visibility.
Monitoring SaaS application performance, isolating browser sessions for all websites, and integrating with SD-WAN for data loss prevention.
Enabling secure web browsing to protect against threats, providing explicit application access with zero-trust or SD-WAN integration, and addressing shadow IT visibility with data loss prevention.
Providing secure web browsing through remote browser isolation, addressing shadow IT with zero-trust access, and protecting data at rest only.
Answer:
CExplanation:
According to theFortiSASE 7.6 Architecture GuideandFCP - FortiSASE 24/25 Administratormaterials, the solution is built around three primary use cases that support a hybrid workforce:
Secure Internet Access (SIA):This enables secure web browsing by applying security profiles such asWeb Filter,Anti-Malware, andSSL Inspectionin the SASE cloud. It protects remote users from internet-based threats regardless of their location.
Secure Private Access (SPA):This provides granular, explicit access to private applications hosted in data centers or the cloud. It is achieved throughZTNA (Zero Trust Network Access)for session-based security or throughSD-WAN integrationwhere FortiSASE acts as a spoke to an existing corporate SD-WAN hub.
SaaS Security:FortiSASE utilizesInline-CASBandShadow IT visibilityto monitor and control the use of cloud applications.Data Loss Prevention (DLP)is integrated into these workflows to prevent sensitive corporate data from being uploaded to unauthorized SaaS platforms.
Why other options are incorrect:
Option A:While it mentions SD-WAN and Shadow IT, it misses the core definition of SIA (secure web browsing) which is the primary driver for SASE deployments.
Option B:Remote Browser Isolation (RBI)is typically applied to risky or uncategorized websites, not "all websites," due to the high performance and resource overhead.
Option D:FortiSASE is designed to protect data in motion (via security profiles) as well as data stored in sanctioned cloud apps, not "at rest only".
Which statement is true about FortiSASE supported deployment?
Options:
FortiSASE supports VPN mode and Agentless mode, based on user requirements.
FortiSASE supports both Endpoint mode and SWG mode, depending on deployment.
FortiSASE operates only in SWG mode, where all traffic is forced through FortiSASE POPs.
FortiSASE relies on ZTNA-only mode, which replaces SWG and endpoint functions.
Answer:
BExplanation:
According to theFortiSASE 7.6 Administration Guideand theFCP - FortiSASE 24/25 Administratorcurriculum, FortiSASE is designed with a hybrid deployment architecture to support various user and device requirements. It primarily operates in two modes:
Endpoint Mode (Agent-based): This mode requires the installation ofFortiClienton the user's laptop or device. The agent establishes an "always-up" secure VPN tunnel to the nearest FortiSASE Point of Presence (PoP), providing full Secure Internet Access (SIA), Secure Private Access (SPA), and endpoint posture checks (ZTNA).
Secure Web Gateway (SWG) Mode (Agentless): This mode is used for users or devices where installing an agent is not feasible (e.g., unmanaged devices or Chromebooks). It relies on explicit web proxy settings or a PAC (Proxy Auto-Configuration) file to redirect web traffic (HTTP/HTTPS) to the SASE PoP for inspection.
Why other options are incorrect:
Option A: While it supports VPN, "VPN mode" is not the formal name of the deployment type; it is "Endpoint mode".
Option C: FortiSASE is not limited to SWG; it is a full SSE (Security Service Edge) solution including FWaaS and ZTNA.
Option D: ZTNA is a capability within the platform, not a replacement for the overall endpoint or SWG functions.
Refer to the exhibit.
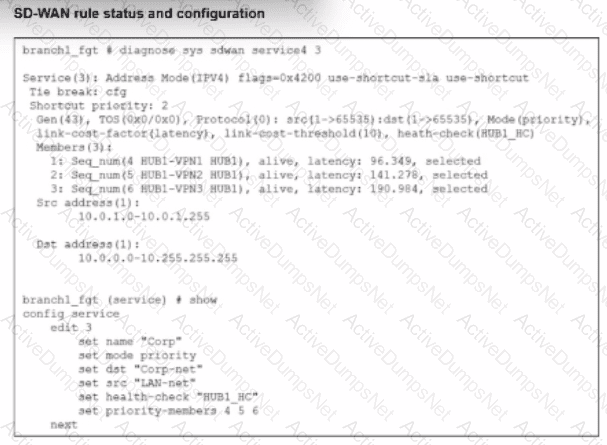
The SD-WAN rule status and configuration is shown. Based on the exhibit, which change in the measured latency will first make HUB1-VPN3 the new preferred member?
Options:
When HUB1-VPN3 has a latency of 80 ms
When HUB1-VPN3 has a lower latency than HUB1-VPN1 and HUB1-VPN2
When HUB1-VPN1 has a latency of 200 ms
When HUB1-VPN3 has a latency of 90 ms
Answer:
AExplanation:
According to theSD-WAN 7.6 Core Administratorstudy guide and theFortiOS 7.6 Administration Guide, the selection of a preferred member in aBest Quality (priority)rule is determined by the measured quality metric (latency, in this case) and thelink-cost-threshold.
Rule Logic (Best Quality): In the exhibit, the SD-WAN rule is configured with set mode priority, which corresponds to theBest Qualitystrategy. This strategy ranks members based on the link-cost-factor, which is set tolatency.
The Link-Cost-Threshold: The exhibit shows link-cost-threshold(10), which is the default 10% value. This threshold is designed to prevent "link flapping". To replace the current preferred member, a new member must not only have a better latency but must be better bymore than 10%.
The Calculation:
The current preferred member isHUB1-VPN1with a real latency of96.349 ms.
To calculate the "target" latency a lower-priority member must achieve to take over, we use the formula: $Target = \frac{Current\_Latency}{(1 + \frac{Threshold}{100})}$.
$\frac{96.349}{1.1} = \mathbf{87.59\text{ ms}}$.
Evaluating Options:
Option A (80 ms): Since 80 ms is lower than the required 87.59 ms target, HUB1-VPN3 successfully overcomes the 10% advantage of HUB1-VPN1 and becomes the new preferred member.
Option D (90 ms): While 90 ms is lower than 96.349 ms, it isnotlower than 87.59 ms. Therefore, the 10% threshold prevents a member switch, and HUB1-VPN1 remains preferred.
Option B: Incorrect because having a "lower" latency is not enough due to the 10% threshold.
Option C: If HUB1-VPN1 moved to 200 ms, HUB1-VPN2 (at 141.278 ms) would likely become the new preferred member before HUB1-VPN3 (at 190.984 ms).
You have a FortiGate configuration with three user-defined SD-WAN zones and one or two members in each of these zones. One SD-WAN member is no longer used in health-check and SD-WAN rules. This member is the only member of its zone. You want to delete it.
What happens if you delete the SD-WAN member from the FortiGate GUI?
Options:
FortiGate displays an error message. SD-WAN zones must contain at least one member.
FortiGate accepts the deletion and removes static routes as required.
FortiGate accepts the deletion with no further action.
FortiGate accepts the deletion and places the member in the default SD-WAN zone.
Answer:
BExplanation:
Questions no:9Verified Answer: B
Comprehensive and Detailed Explanation with all FortiSASE and SD-WAN 7.6 Core Administrator curriculum documents: According to theSD-WAN 7.6 Core Administratorstudy guide andFortiOS 7.6 Administration Guide, the behavior for deleting an SD-WAN member from the GUI when it is the only member in its zone is governed by the following operational logic:
Reference Checks: Before allowing the deletion of any SD-WAN member, FortiOS performs a "check for dependencies." If an interface is being used in an activePerformance SLAor anSD-WAN Rule, the GUI will typically prevent the deletion or gray out the option until those references are removed. However, the question specifies that this member isno longer usedin health-checks or rules.
Zone Integrity: Unlike some other network objects, an SD-WAN zone is permitted to exist without any members. When you delete the final member of a user-defined zone through the GUI, the zone itself remains in the configuration as an empty container.
Route Management: When an SD-WAN member is deleted, any static routes that were specifically tied to that interface's membership in the SD-WAN bundle are automatically updated or removed by the FortiGate to prevent routing loops or "black-holing" traffic. This is part of the automated cleanup process handled by the FortiOS management plane.
GUI vs. CLI: In the GUI, the process is streamlined to allow the removal of the member interface. Once the member is deleted, the interface returns to being a "regular" system interface and can be used for standard firewall policies or other functions.
Why other options are incorrect:
Option A: There is no requirement that a zone must contain at least one member; "empty" zones are valid configuration objects in FortiOS 7.6.
Option C: While the deletion is accepted, it is not with "no further action"—the system must still reconcile the routing table and interface status.
Option D: FortiGate does not automatically move deleted members into the default zone (virtual-wan-link). Once deleted, the interface is simply no longer an SD-WAN member.
For a small site, an administrator plans to implement SD-WAN and ensure high network availability for business-critical applications while limiting the overall cost and the cost of pay-per-use backup connections.
Which action must the administrator take to accomplish this plan?
Options:
Use a mid-range FortiGate device to implement standalone SD-WAN.
Implement dynamic routing.
Set up a high availability (HA) cluster to implement standalone SD-WAN.
Configure at least two WAN links.
Answer:
DExplanation:
According to theSD-WAN 7.6 Core Administratorcurriculum, to implement an SD-WAN solution that ensures high network availability for business-critical applications while managing costs, the administrator mustconfigure at least two WAN links.
SD-WAN Fundamentals: SD-WAN operates by creating a virtual overlay across multiple physical or logical transport links (e.g., broadband, LTE, MPLS). Without at least two links, the SD-WAN engine has no alternative path to steer traffic toward if the primary link fails or degrades.
Cost Management: By using multiple links, administrators can implement theLowest Cost (SLA)orMaximize Bandwidthstrategies. This allows the site to use a low-cost broadband connection for primary traffic and only failover to a "pay-per-use" backup (like LTE) when the primary link's quality falls below the defined SLA target.
High Availability (Link Level): While a "High Availability (HA) cluster" (Option C) provides device redundancy (protecting against a hardware failure of the FortiGate itself), it does not address link redundancy or steering, which are the core functions of SD-WAN for application uptime.
Why other options are incorrect:
Option A: Using a mid-range device refers to hardware capacity but does not solve the requirement for link-level redundancy and cost-steering logic.
Option B: Dynamic routing (like BGP or OSPF) is often usedwithSD-WAN in large topologies, but for a small site, the primary mechanism for meeting availability and cost goals is the configuration of the SD-WAN member links and rules themselves.
Option C: HA clusters protect against hardware failure, but the question specifically asks about ensuring availability forapplicationswhile limitingbackup link costs, which is a traffic-steering (SD-WAN) requirement rather than a hardware-redundancy requirement.
Refer to the exhibit.
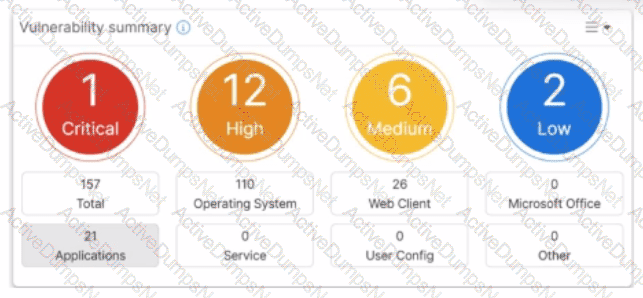
Which two statements about the Vulnerability summary dashboard in FortiSASE are correct? (Choose two.)
Options:
The dashboard shows the vulnerability score for unknown applications.
Vulnerability scan is disabled in the endpoint profile.
The dashboard allows the administrator to drill down and view CVE data and severity classifications.
Automatic vulnerability patching can be enabled for supported applications.
Answer:
C, DExplanation:
Based on theFortiSASE 7.6 (and later 2025 versions)curriculum and administration guides, the Vulnerability summary dashboard is a key component of the endpoint security posture management.
Drill Down Capability (Option C): According to theFortiSASE Administration Guide, the Vulnerability summary widget on the Security dashboard is interactive. An administrator can click on specific risk categories (e.g., Critical, High) or application types (e.g., Operating System, Web Client) todrill down. This action opens a detailed pane showing the specific affected endpoints, associatedCVE identifiers, and severity classifications based on the CVSS standard.
Automatic Vulnerability Patching (Option D): In theFortiSASE 7.6/2025feature sets, the endpoint profile configuration (underEndpoint > Configuration > Profiles) includes an "Automatic Patching" section. This feature allows the system to automatically install security updates for supported third-party applications and the underlying operating system (Windows/macOS) when vulnerabilities are detected. Furthermore, administrators can schedule these patches directly from theVulnerability Summarywidget by selecting specific vulnerabilities.
Why other options are incorrect:
Option A: The dashboard categories (Operating System, Web Client, Microsoft Office, etc.) are based on known software signatures. While there is an "Other" category, the dashboard primarily provides scores for recognized applications where CVE data is available.
Option B: The exhibit shows active data (157 total vulnerabilities), which indicates that thevulnerability scan is enabledand currently reporting data from the endpoints. If it were disabled, the widget would be empty or show zeros.
How is the Geofencing feature used in FortiSASE? (Choose one answer)
Options:
To allow or block remote user connections to FortiSASE POPs from specific countries.
To restrict access to applications based on the time of day in specific countries.
To encrypt data at rest on mobile devices in specific countries.
To monitor user behavior on websites and block non-work-related content from specific countries
Answer:
AExplanation:
According to theFortiSASE 7.6 Administration Guideand theFCP - FortiSASE 24/25 Administratorstudy materials, theGeofencingfeature is a security measure implemented at the edge of the FortiSASE cloud to control ingress connectivity based on the physical location of the user.
Access Control by Location (Option A): Geofencing allows administrators toallow or block remote user connectionsto the FortiSASE Points of Presence (PoPs) based on the source country, region, or specific network infrastructure (e.g., AWS, Azure, GCP).
Scope of Application: This feature is universal across all SASE connectivity methods. It applies toAgent-based users(FortiClient),Agentless users(SWG/PAC file), andEdge devices(FortiExtender/FortiAP). If a user attempts to connect from a blacklisted country, the connection is dropped at the PoP level before the user can even attempt to authenticate.
Use Case Example: An organization operating exclusively in North America might configure geofencing toblock all connections originating from outside the US and Canada. This significantly reduces the attack surface by preventing brute-force or unauthorized access attempts from high-risk regions or countries where the organization has no legitimate employees.
Configuration Path: In the FortiSASE portal, this is managed underConfiguration > Geofencing. From there, administrators can create an "Allow" or "Deny" list and select the relevant countries from a standardized global database.
Why other options are incorrect:
Option B: While FortiSASE supportsTime-based schedulesfor firewall policies, geofencing is specifically an IP-to-Geography mapping tool for connection admission, not a time-of-day restriction tool.
Option C: Encryption of data at rest on mobile devices is a function of anMDM (Mobile Device Management)solution or local OS features (like FileVault or BitLocker), not a SASE network geofencing feature.
Option D: Monitoring web behavior and blocking non-work content is the role of theWeb FilterandApplication Controlprofiles, which operate on the trafficafterthe connection is allowed by geofencing.
Which two statements correctly describe what happens when traffic matches the implicit SD-WAN rule? (Choose two answers)
Options:
Traffic is load balanced using the algorithm set for the v4-ecmp-mode setting.
Traffic does not match any of the entries in the policy route table.
FortiGate flags the session with may_dirty and vwl_default.
The traffic is distributed, regardless of weight, through all available static routes.
The session information output displays no SD-WAN service id.
Answer:
B, EExplanation:
According to theSD-WAN 7.6 Core Administratorstudy guide andFortiOS 7.6 Administration Guide, the "implicit rule" is the default rule at the bottom of the SD-WAN rule list (ID 0). It is only evaluated if traffic does not match any manually configured SD-WAN rules.
Policy Route Table Context (Option B): SD-WAN rules are technically a specialized form of policy-based routing. For a packet to match theimplicit rule, it must first pass through the routing hierarchy. If traffic matches the implicit rule, it indicates that it did not match any higher-priority user-defined SD-WAN rules or any specific entries in the manualpolicy route tablethat would have intercepted the traffic earlier.
Session Information (Option E): When you use the CLI to inspect an active session (e.g., diagnose sys session list), the output contains a field for theSD-WAN Service ID. If traffic is steered by a user-defined rule, it displays the ID of that rule (e.g., service_id=1). However, when traffic falls through to theimplicit rule, the session information displaysno SD-WAN service ID(it often shows as 0 or is omitted), because the implicit rule does not function as a "service" in the same way user-defined rules do.
Routing Behavior: The implicit rule follows the standard routing table (RIB/FIB) logic. It uses thepriorityanddistanceof the static routes to determine the path. If multiple paths have the same distance and priority, it uses the algorithm set by v4-ecmp-mode, but this is a function of the routing engine, not the SD-WAN engine itself.
Why other options are incorrect:
Option A: While v4-ecmp-mode (e.g., source-ip-based) is used for ECMP routing, this is part of the general FortiOS routing behavior for equal-cost paths in the FIB, whereas the implicit rule simply "hands over" the decision to that routing table.
Option C: When traffic matches the implicit rule, the session is actually flagged with vwl_id=0 and potentially dirty if a route change occurs, but vwl_default is not the standard flag name used in this specific context in the curriculum.
Option D: This is incorrect because the implicit ruledoes respect weight, distance, and priorityas defined in the static routes within the routing table; it does not distribute traffic "regardless" of these values.
Which two delivery methods are used for installing FortiClient on a user's laptop? (Choose two.)
Options:
Use zero-touch installation through a third-party application store.
Download the installer directly from the FortiSASE portal.
Send an invitation email to selected users containing links to FortiClient installers.
Configure automatic installation through an API to the user's laptop.
Answer:
B, CExplanation:
TheFortiSASE 7.6 Administration Guideoutlines the standard onboarding procedures for deploying theFortiClientagent to remote endpoints. There are two primary user-facing delivery methods:
Download from the FortiSASE portal (Option B):Administrators can provide users with access to the FortiSASE portal where they can directly download apre-configured installer. This installer is uniquely tied to the organization’s SASE instance, ensuring the client automatically registers to the correct cloud EMS upon installation.
Invitation Email (Option C):This is the most common administrative method. The FortiSASE portal (via its integrated EMS) allows administrators to send an invitation email to specific users or groups. This email contains direct download links for various operating systems (Windows, macOS, Linux) and the necessary invitation code for zero-touch registration.
Why other options are incorrect:
Option A:While third-party stores (like the App Store or Google Play) are used for mobile devices, "zero-touch installation through a third-party store" is not the standard curriculum-defined method forlaptops(Windows/macOS) in a SASE environment.
Option D:FortiSASE does not use a direct "API to the user's laptop" for automatic installation. While MDM/GPO (centralized deployment) is supported, it is not described as an API-based auto-installation in the core curriculum.
Unlock NSE5_SSE_AD-7.6 Features
- NSE5_SSE_AD-7.6 All Real Exam Questions
- NSE5_SSE_AD-7.6 Exam easy to use and print PDF format
- Download Free NSE5_SSE_AD-7.6 Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet
Questions & Answers PDF Demo
- NSE5_SSE_AD-7.6 All Real Exam Questions
- NSE5_SSE_AD-7.6 Exam easy to use and print PDF format
- Download Free NSE5_SSE_AD-7.6 Demo (Try before Buy)
- Free Frequent Updates
- 100% Passing Guarantee by Activedumpsnet
