Fortinet NSE4_FGT_AD-7.6 Fortinet NSE 4 - FortiOS 7.6 Administrator Exam Practice Test
Fortinet NSE 4 - FortiOS 7.6 Administrator Questions and Answers
An administrator creates a new address object on the root FortiGate (HQ-NGFW-1) in the Security Fabric. After synchronization, this object is not available on the downstream FortiGate (HQ-ISFW).
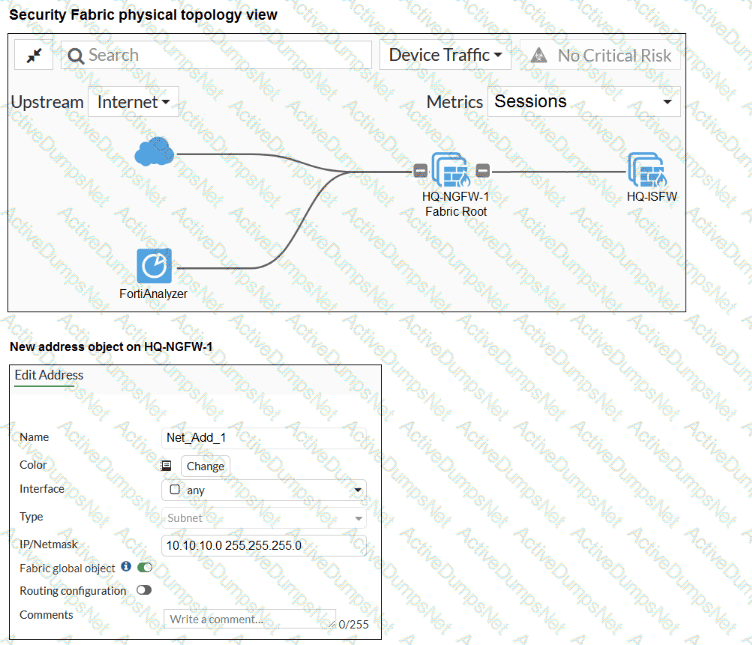
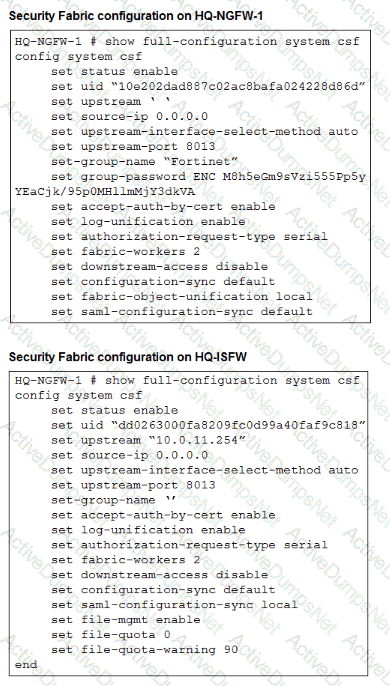
What must the administrator do to synchronize the address object?
Refer to the exhibits.
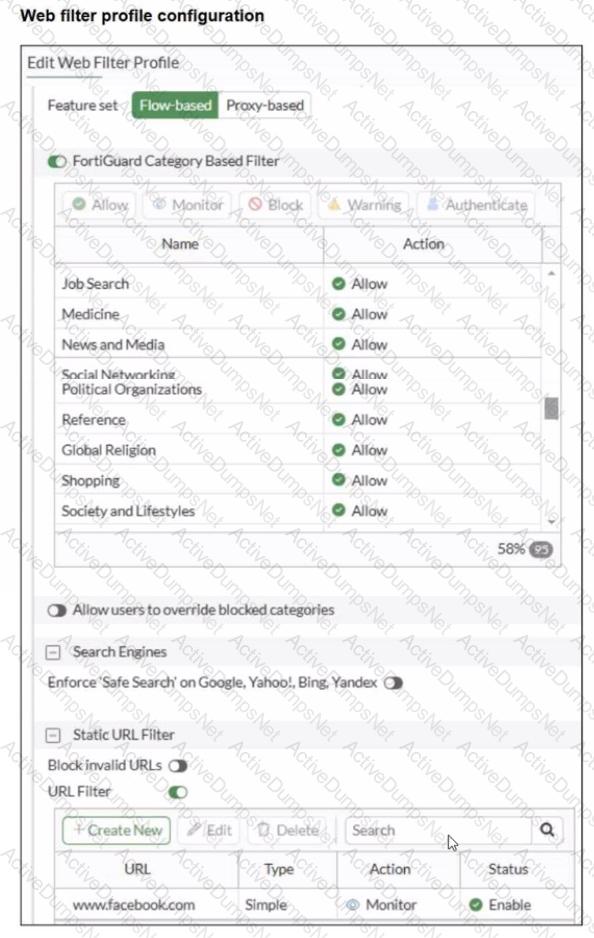
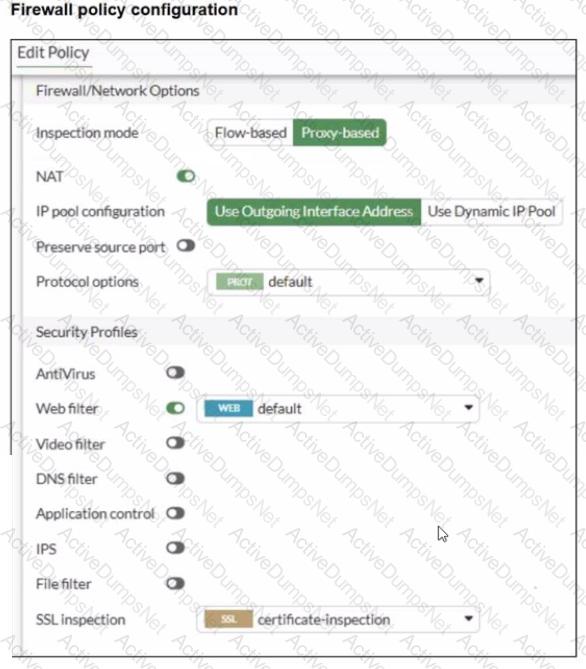
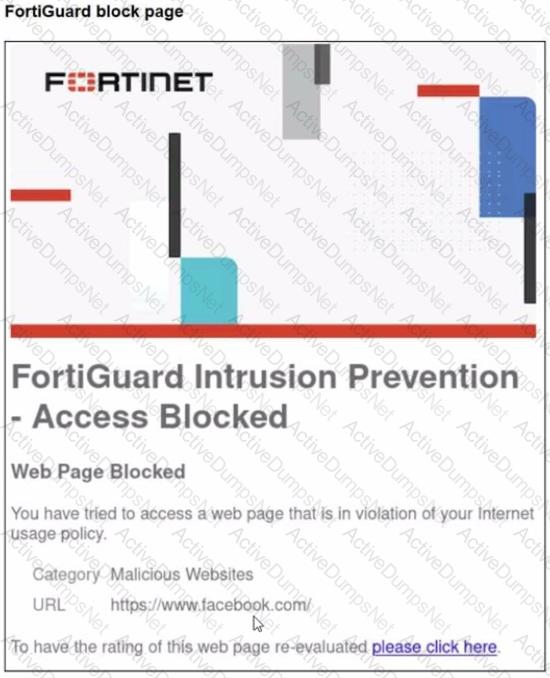
A web filter profile configuration and firewall policy configuration are shown.
You are trying to access www. facebook.com, but you are redirected to a FortiGuard web filtering block page.
Based on the exhibits, what is the possible cause of the issue?
When configuring firewall policies which of the following is true regarding the policy ID? (Choose two.)
How does FortiExtender connect to FortiSASE in a site-based, remote internet access method?
An administrator wanted to configure an IPS sensor to block traffic that triggers the signature set number of times during a specific time period. How can the administrator achieve the objective?
Refer to the exhibit
A firewall policy to enable active authentication is shown.
When attempting to access an external website using an active authentication method, the user is not presented with a login prompt. What is the most likely reason for this situation?
You have configured an application control profile, set peer-to-peer traffic to Block under the Categories tab. and applied it to the firewall policy. However, your peer-to-peer traffic on known ports is passing through the FortiGate without being blocked.
What FortiGate settings should you check to resolve this issue?
Which two statements about the Security Fabric rating are true? (Choose two answers)
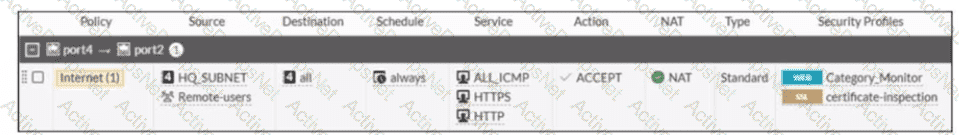
Refer to the exhibits.
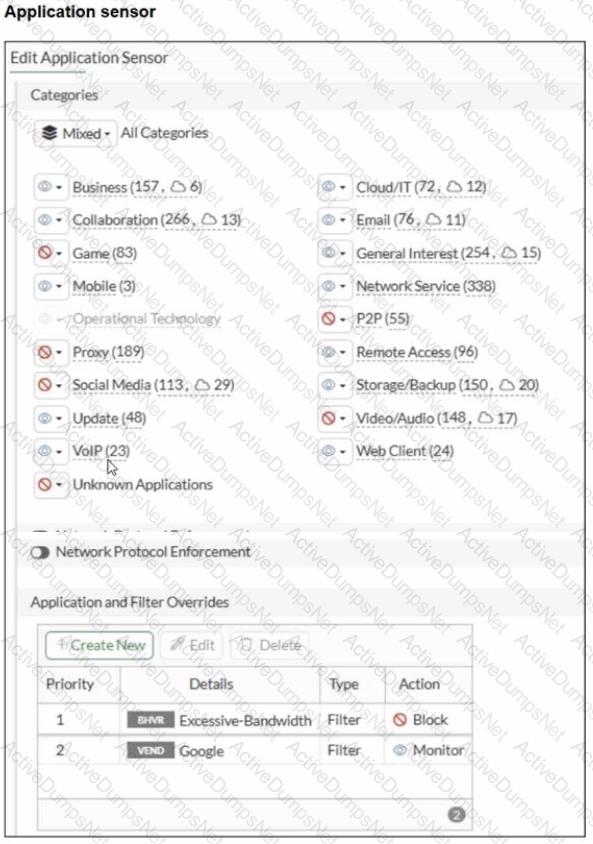
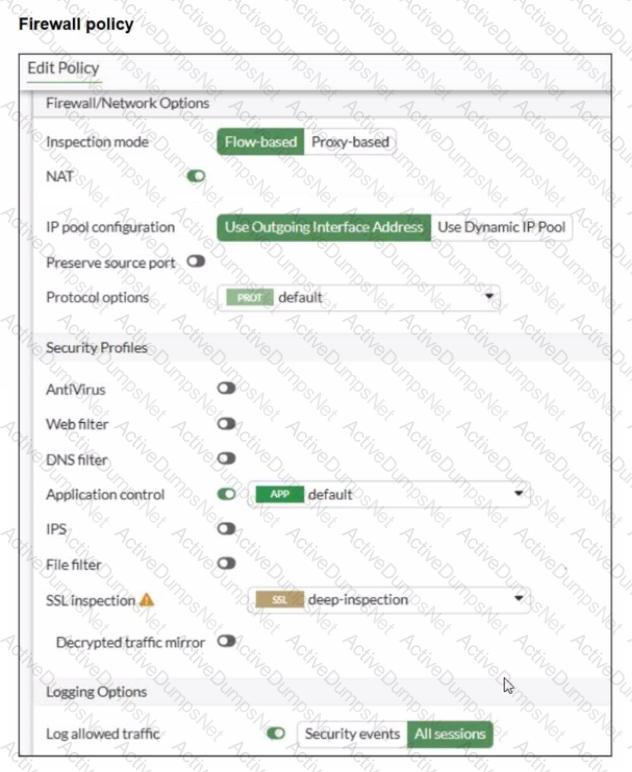
You have implemented the application sensor and the corresponding firewall policy as shown in the exhibits.
Which two factors can you observe from these configurations? (Choose two.)
Refer to the exhibit showing a debug flow output.
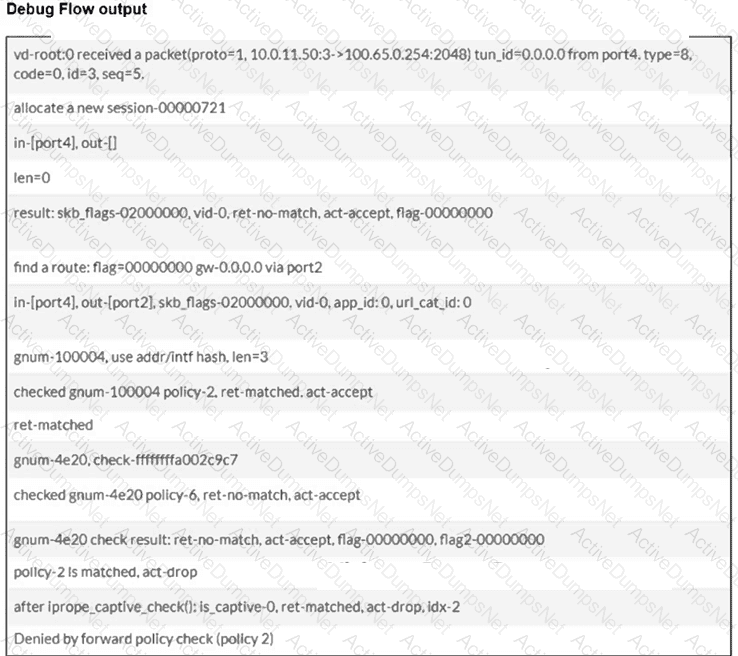
Which two conclusions can you make from the debug flow output? (Choose two answers)
A new administrator is configuring FSSO authentication on FortiGate using DC Agent Mode. Which step is not part of the expected process?
Which three statements about SD-WAN performance SLAs are true? (Choose three.)
What is the primary FortiGate election process when the HA override setting is enabled? (Choose one answer)
What are two features of collector agent advanced mode? (Choose two.)
Refer to the exhibit.
A partial cloud topology is shown.
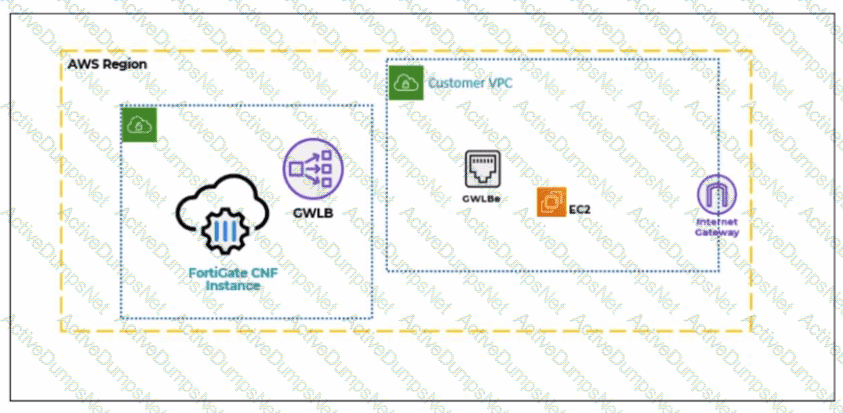
You deployed a FortiGate Cloud-Native Firewall (CNF) in AWS.
During the deployment, which components must the FortiGate CNF create to handle traffic from the EC2 instance?
What are two characteristics of HA cluster heartbeat IP addresses in a FortiGate device? (Choose two.)
Refer to the exhibits.
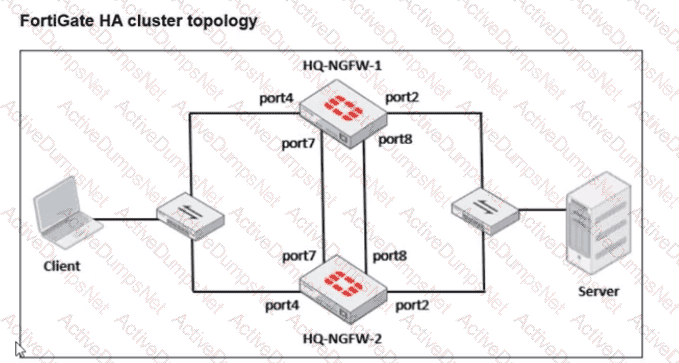
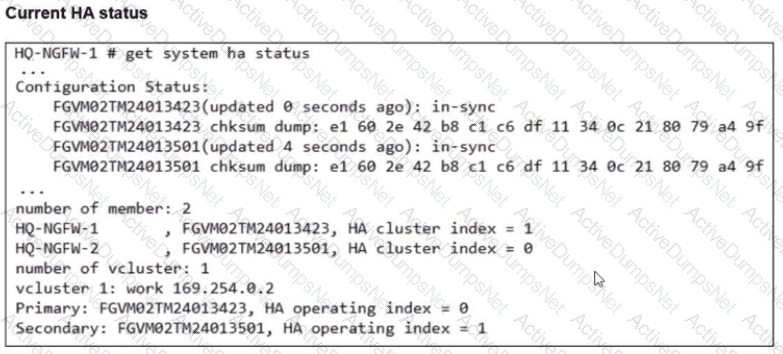
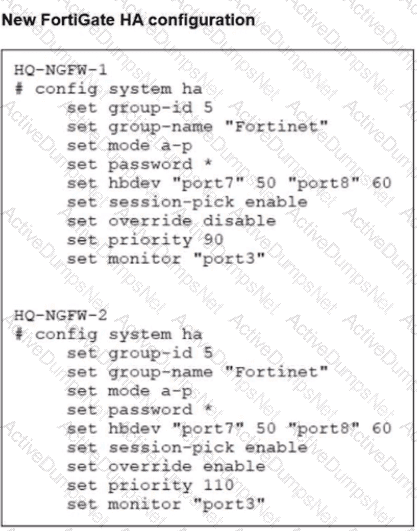
Based on the current HA status, an administrator updates the override and priority parameters on HQ-NGFW-1 and HQ-NGFW-2 as shown in the exhibits.
What would be the expected outcome in the HA cluster?
What are two features of FortiGate FSSO agentless polling mode? (Choose two.)
Refer to the exhibits.
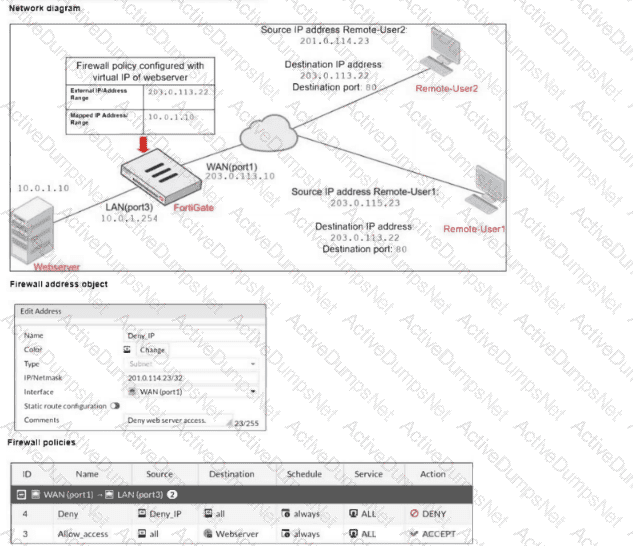
The exhibits show a diagram of a FortiGate device connected to the network, and the firewall configuration. An administrator created a Deny policy with default settings to deny Webserver access for Remote-User2. The policy should work such that Remote-User1 must be able to access the Webserver while preventing Remote-User2 from accessing the Webserver. Which additional configuration can the administrator add to a deny firewall policy, beyond the default behavior, to block Remote-User2 from accessing the Webserver? (Choose one answer)
You have created a web filter profile named restrictmedia-profile with a daily category usage quota.
When you are adding the profile to the firewall policy, the restrict_media-profile is not listed in the available web profile drop down.
What could be the reason?
An administrator wants to configure dead peer detection (DPD) on IPsec VPN for detecting dead tunnels. The requirement is that FortiGate sends DPD probes only when there is no inbound traffic.
Which DPD mode on FortiGate meets this requirement?
Refer to the exhibit.
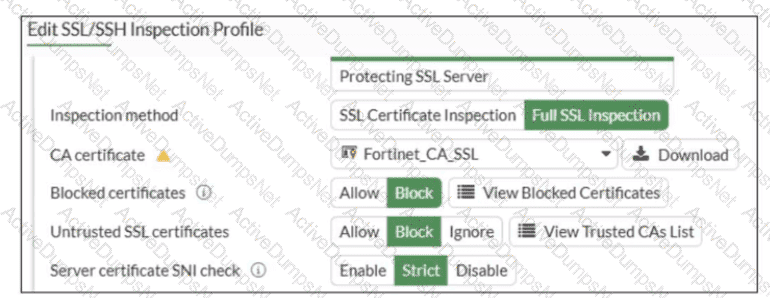
What would be the impact of these settings on the Server certificate SNI check configuration on FortiGate?
Which two statements describe characteristics of automation stitches? (Choose two answers)
Which three methods are used by the collector agent for AD polling? (Choose three answers)
There are multiple dialup IPsec VPNs configured in aggressive mode on the HQ FortiGate. The requirement is to connect dial-up users to their respective department VPN tunnels.
Which phase 1 setting you can configure to match the user to the tunnel?
Refer to the exhibits.
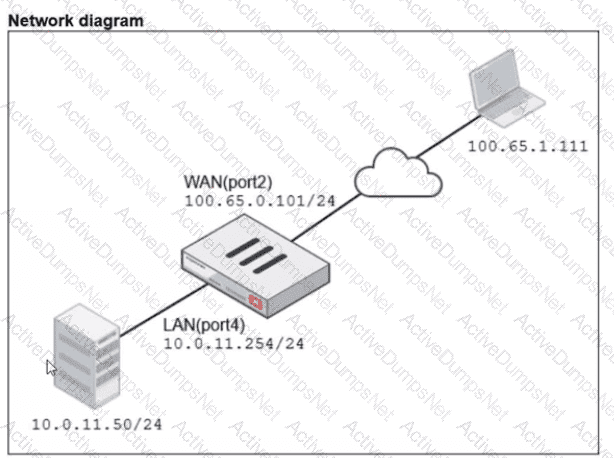
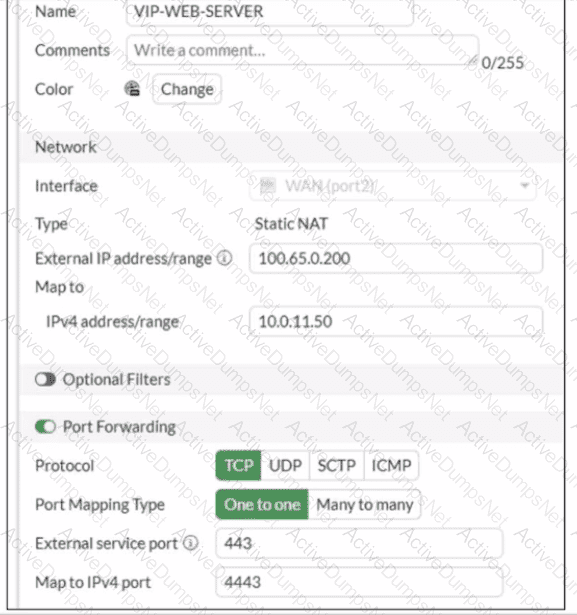

A diagram of a FortiGate device connected to the network VIP object and firewall policy configurations are shown.
The WAN (port2) interface has the IP address
100.65.0.101/24.
The LAN (port4) interface has the IP address
10.0.11.254/24.
If the host 100.65.1.111 sends a TCP SYN packet on port 443 to 100.65.0.200. what will the source address, destination address, and destination port of the packet be at the time FortiGate forwards the packet to the destination?
You have configured an application control profile, set peer-o-peer traffic to Block under the Categories tab, and applied it to the firewall policy. However, you peer-to-peer traffic on known ports is passing through the FortiGate without being blocked. What FortiGate settings should you check to resolve this issue?
