Fortinet FCSS_EFW_AD-7.6 Fortinet NSE 7 - Enterprise Firewall 7.6 Administrator Exam Practice Test
Fortinet NSE 7 - Enterprise Firewall 7.6 Administrator Questions and Answers
Refer to the exhibit, which contains the partial output of an OSPF command.
An administrator is checking the OSPF status of a FortiGate device and receives the output shown in the exhibit.
Which statement on this FortiGate device is correct?
Which two parameters must you configure in neighbor-range for ADVPN iBGP deployment?
Refer to the exhibit.
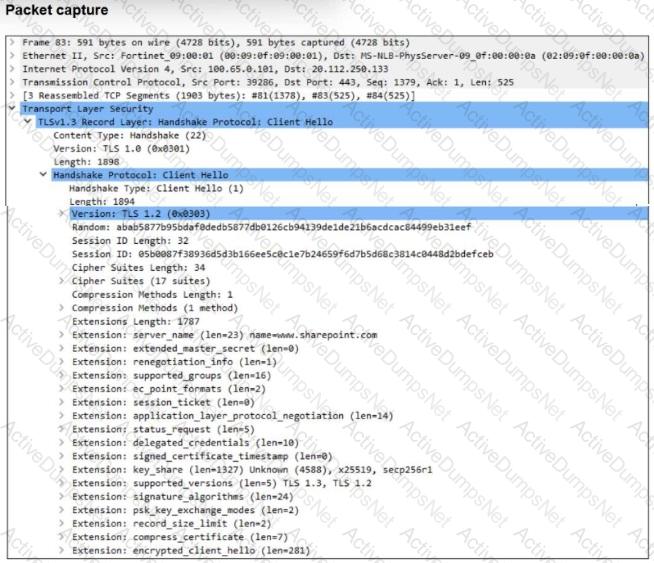
The packet capture output of a client hello message is shown.
You are updating a firewall policy that includes SSL certificate inspection. You are capturing packets from the traffic passing through this firewall policy.
Which two statements about the packet capture are correct? (Choose two.)
Refer to the exhibit, which shows the packet capture output of a three-way handshake between FortiGate and FortiManager Cloud.
What two conclusions can you draw from the exhibit? (Choose two.)
Refer to the exhibit, which shows a hub and spokes deployment.
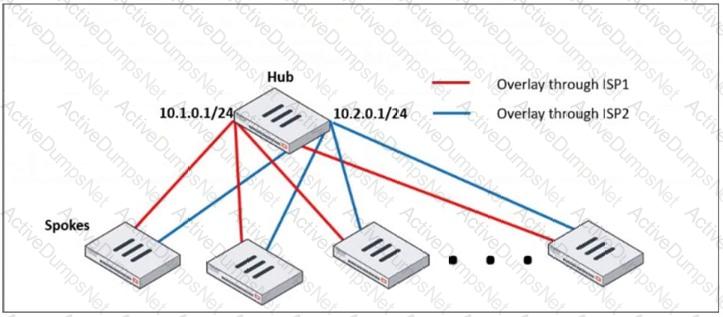
An administrator is deploying several spokes, including the BGP configuration for the spokes to connect to the hub.
Which two commands allow the administrator to minimize the configuration? (Choose two.)
Refer to the exhibit, which shows a partial enterprise network.
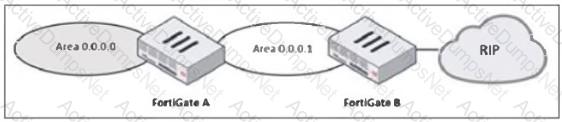
An administrator would like the area 0.0.0.0 to detect the external network.
What must the administrator configure?
Which two recommendations prevent invalid paths when using zero phase 2 selectors?
The IT department discovered during the last network migration that all zero phase selectors in phase 2 IPsec configurations impacted network operations.
What are two valid approaches to prevent this during future migrations? (Choose two.)
Refer to the exhibit, which shows an enterprise network connected to an internet service provider.
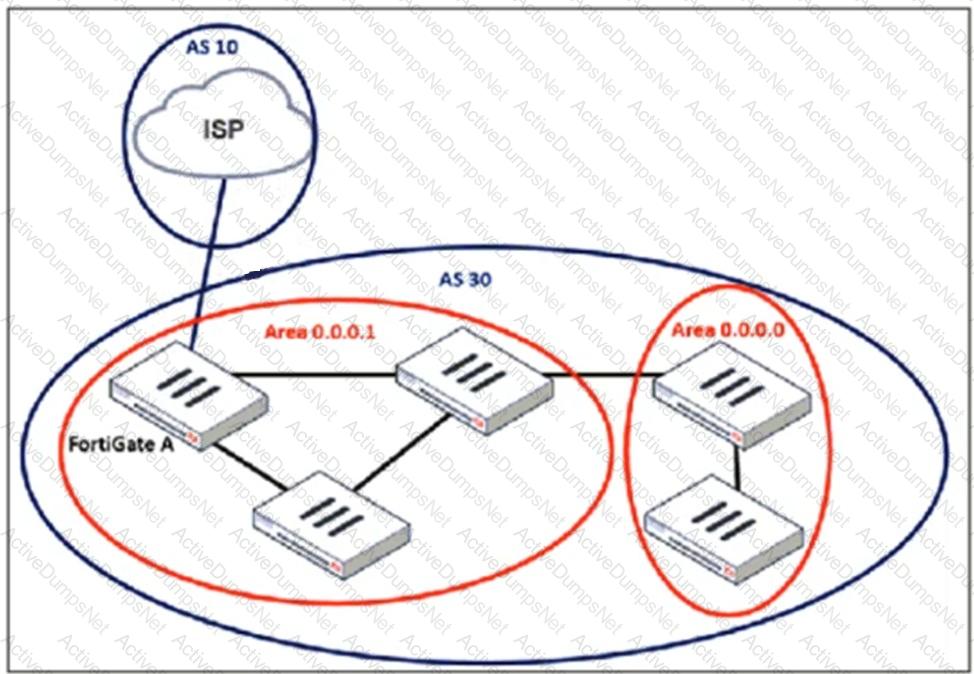
An administrator must configure a loopback as a BGP source to connect to the ISP.
Which two commands are required to establish the connection? (Choose two.)
Which action should you take after applying a block-all IPS profile that caused applications to stop working?
Which two statements about the LAN interface connection are correct?
How do you allow IPS inspection of inbound HTTPS traffic?
You are trying to efficiently deploy ADVPN within the enterprise network. Which two approaches can facilitate this deployment? (Choose two.)
What is the initial step performed by FortiGate when handling the first packets of a session?
Based on the TLS handshake shown, what can be inferred about the client?
Why do the firewall policy and reinstall preview show different address names during installation?
Which two features can you use to segment an enterprise network?
Refer to the exhibit, which contains a partial VPN configuration.
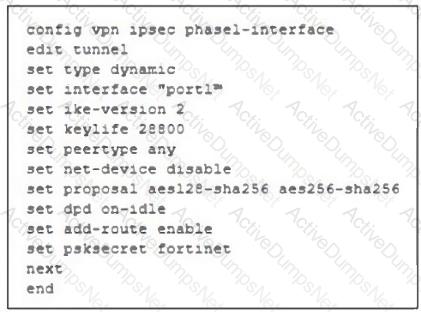
What can you conclude from this VPN IPsec phase 1 configuration?
Which parameter must be configured to modify the MED value?
A FortiGate device using unified threat management (UTM) profiles is reaching resource limits, and you expect traffic in your enterprise network to increase. You received an additional FortiGate of the same model.
Which two options should you consider using to integrate the additional FortiGate into your enterprise network? (Choose two.)
Refer to the exhibit.
The routing tables of FortiGate_A and FortiGate_B are shown. FortiGate_A and FortiGate_B are in the same autonomous system.
The administrator wants to dynamically add only route 172.16.1.248/30 on FortiGate_A.
What must the administrator configure?
Refer to the exhibit.
A physical topology along with a traffic log is shown. You are using FortiAnalyzer to monitor traffic from the device with IP address 10.0.2.51, which is located behind the FortiGate internal segmentation firewall (ISFW) device. Unified threat management (UTM) is not enabled in the firewall policy on the HQ-ISFW device, and you are surprised to see a log with the action Malware, as shown in the exhibit. What are two reasons why FortiAnalyzer would display this log? (Choose two answers)
Refer to the exhibit, which shows a network diagram showing the addition of site 2 with an overlapping network segment to the existing VPN IPsec connection between the hub and site 1.
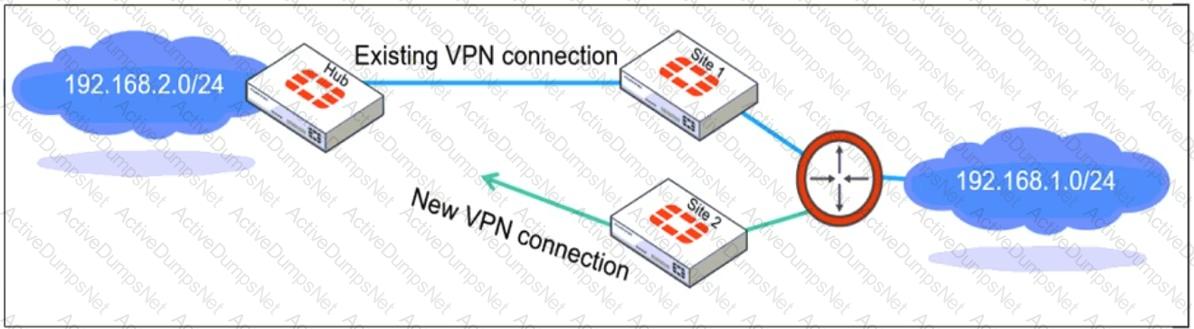
Which IPsec phase 2 configuration must an administrator make on the FortiGate hub to enable equal-cost multi-path (ECMP) routing when multiple remote sites connect with overlapping subnets?
How do you resolve object conflicts when importing a policy package?
An administrator is designing an ADVPN network for a large enterprise with spokes that have varying numbers of internet links. They want to avoid a high number of routes and peer connections at the hub.
Which method should be used to simplify routing and peer management?
Refer to the exhibit, which shows an ADVPN network
An administrator must configure an ADVPN using IBGP and EBGP to connect overlay network 1 with 2.
What two options must the administrator configure in BGP? (Choose two.)
Which hardware improves VXLAN performance?
Refer to the exhibits.
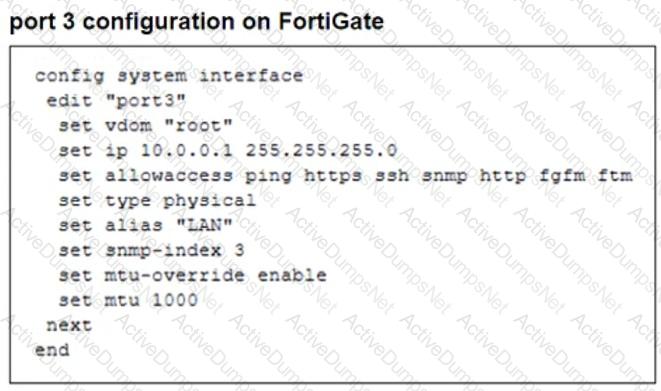
The configuration of a user ' s Windows PC, which has a default MTU of 1500 bytes, along with FortiGate interfaces set to an MTU of 1000 bytes, and the results of PC1 pinging server 172.16.0.254 are shown.
Why is the user in Windows PC1 unable to ping server 172.16.0.254 and is seeing the message: Packet needs to be fragmented but DF set?
Refer to the exhibit, which shows a revision history window in the FortiManager device layer.
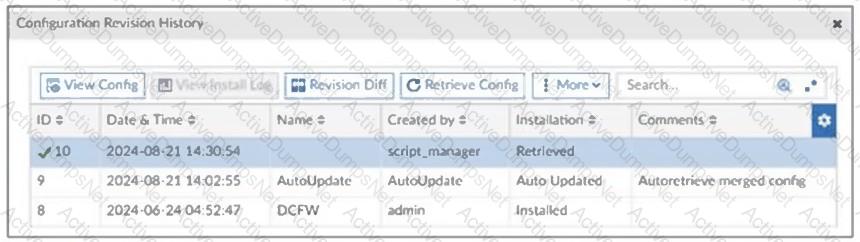
The IT team is trying to identify the administrator responsible for the most recent update in the FortiGate device database.
Which conclusion can you draw about this scenario?
What should be configured to provide hardware-accelerated inter-VDOM traffic?
Refer to the exhibit.
An HA configuration of an active-active (A-A) cluster with the same HA uptime is shown. You want HQ-NGFW-2 to handle the Core2 VDOM traffic. Which modification must you make to achieve this outcome? (Choose one answer)
Which two statements about IKEv2 are true if an administrator decides to implement IKEv2 in the VPN topology? (Choose two.)
Refer to the exhibit, which shows the ADVPN network topology and partial BGP configuration.
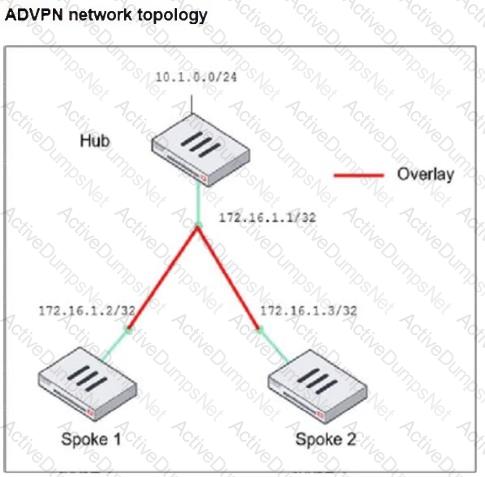
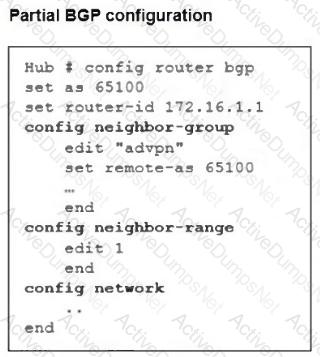
Which two parameters must an administrator configure in the config neighbor range for spokes shown in the exhibit? (Choose two.)
