Fortinet FCP_FSA_AD-5.0 FCP - FortiSandbox 5.0 Administrator Exam Practice Test
FCP - FortiSandbox 5.0 Administrator Questions and Answers
A FortiGate root VDOM is authorized on FortiSandbox, and FortiGate is configured to send suspicious files to FortiSandbox for inspection. You create a new VDOM and then generates some traffic so that the new VDOM sends a file to FortiSandbox for the first time. In this scenario, which action will FortiSandbox take? (Choose one answer)
Refer to the exhibit.
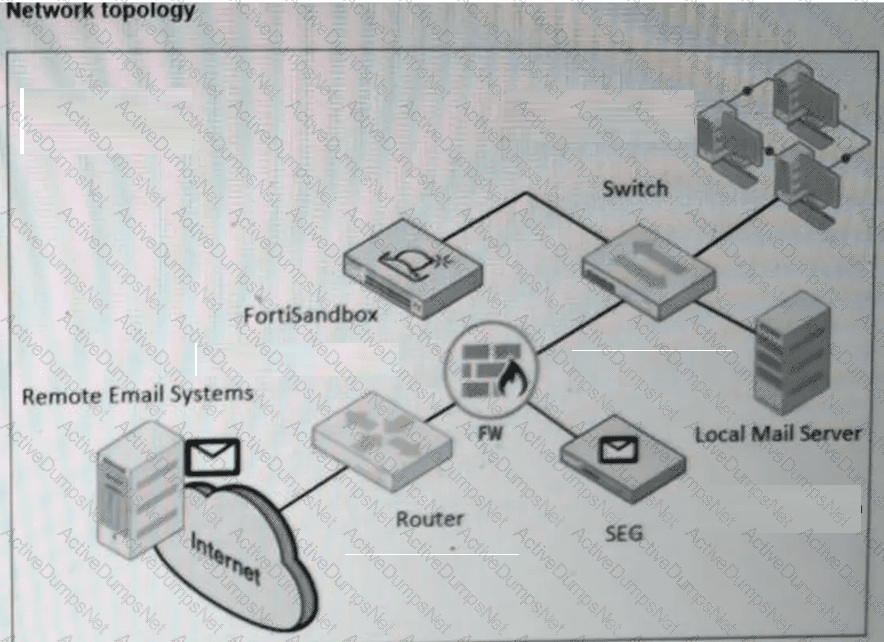
A network topology is shown. Which two important steps must you take before you enable a BCC adapter on FortiSandbox? (Choose two answers)
A security analyst is reviewing a scan job report that indicates a true positive match. The job report displays that the malware attempts to replace vital system executables. Which type of malware is the analyst observing? (Choose one answer)
To assign a file to a VM image, which two conditions must be true? (Choose two answers)
A FortiSandbox VM has been deployed and has been functioning correctly for several months. Suddenly, the system begins rejecting file submissions with an error message indicating a licensing problem. How can you determine, using the CLI, if the license is still valid? (Choose one answer)
Refer to the exhibit.
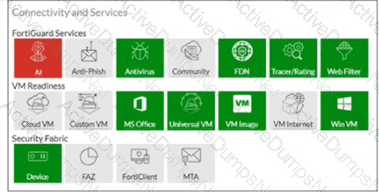
Which two inspections will FortiSandbox perform on samples submitted for sandboxing? (Choose two answers)
You determine that there are a large number of samples on FortiSandbox that are obsolete and no longer needed for future analysis. Which CLI tool must you use to remediate this issue? (Choose one answer)
Which three actions does FortiSandbox perform when it is integrated with FortiMail for advanced threat protection (ATP)? (Choose three answers)
You must increase the scanning capacity of a FortiSandbox device by increasing the number of clones, but the FortiSandbox local clone limit is already at maximum. Which two actions can you take to expand the scanning capacity of the unit? (Choose two answers)
Refer to the exhibit.
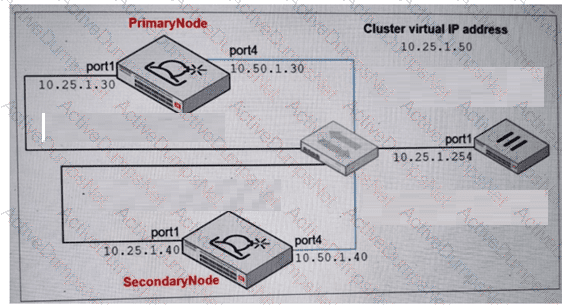
Which command must you use to configure the secondary node? (Choose one answer)
You are troubleshooting long delays between FortiMail file submissions to FortiSandbox and verdicts being returned form FortiSandbox. Which FortiMail debug tool must you use to troubleshoot this issue further? (Choose one answer)
You notice a recent file downloaded by some end stations is exhibiting malware behavior, however, on the sandbox the file is rated clean. After further investigation you determine that only end stations using the Opera browser are being affected. What must you do to prevent these infections? (Choose one answer)
