CyberArk CPC-CDE-RECERT CyberArk CDE-CPC Recertification Exam Practice Test
CyberArk CDE-CPC Recertification Questions and Answers
What is the purpose of the PSM Health Check hardening?
On the CPM, you want to verify if DEP is disabled for the required executables According to best practices, which executables should be listed? (Choose 2.)
What is the correct CyberArk user to use when installing the Privilege Cloud Connector software?
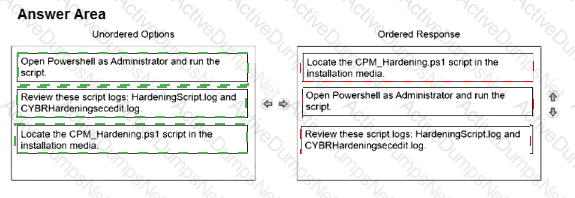
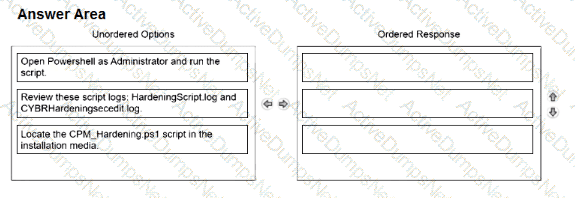
Arrange the steps to complete CPM Hardening for out-of-Domain deployment in the correct sequence.
What must be done before configuring directory mappings in the CyberArk Privilege Cloud Standard Portal for LDAP integration?
What creating a new safe, what is the default number of password versions stored if using 'Save latest account versions' within version management settings?
What must be specified when authenticating to Privilege Cloud during the Secure Tunnel install?
Which option correctly describes the authentication differences between CyberArk Privilege Cloud and CyberArk PAM Self-Hosted?
What is recommended when applying GPO (Group Policy Object) hardening for in-domain PSM servers?
Which actions must be performed when manually hardening a SUSE server with PSM for SSH? (Choose two.)
What are dependencies to update or change the CPM credential? (Choose 2.)
Which external-facing IP addresses need to be provided to CyberArk when configuring Privilege Cloud so that they can be allowlisted?
Which deployment criteria influences the CyberArk-provided hardening methods that need to be applied to CPM and PSM components?
According to best practice, when considering the location of PSM Connector servers in Privilege Cloud environments, where should the PSM be placed?
A CyberArk Privileged Cloud Shared Services customer asks you how to find recent failed login events for all users. Where can you do this without generating reports?
In addition to CyberArk, which additional licensing implication does the PSM have?
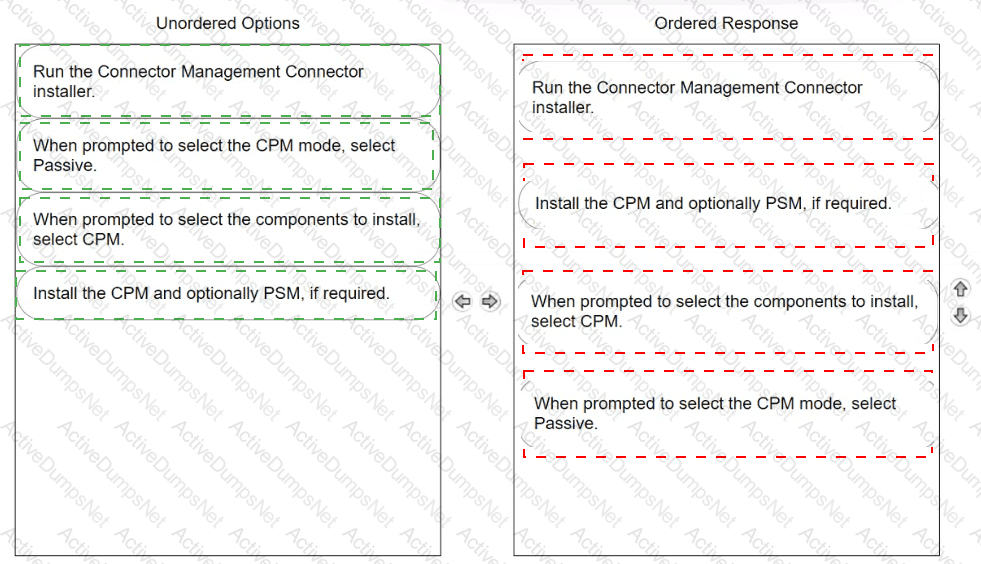
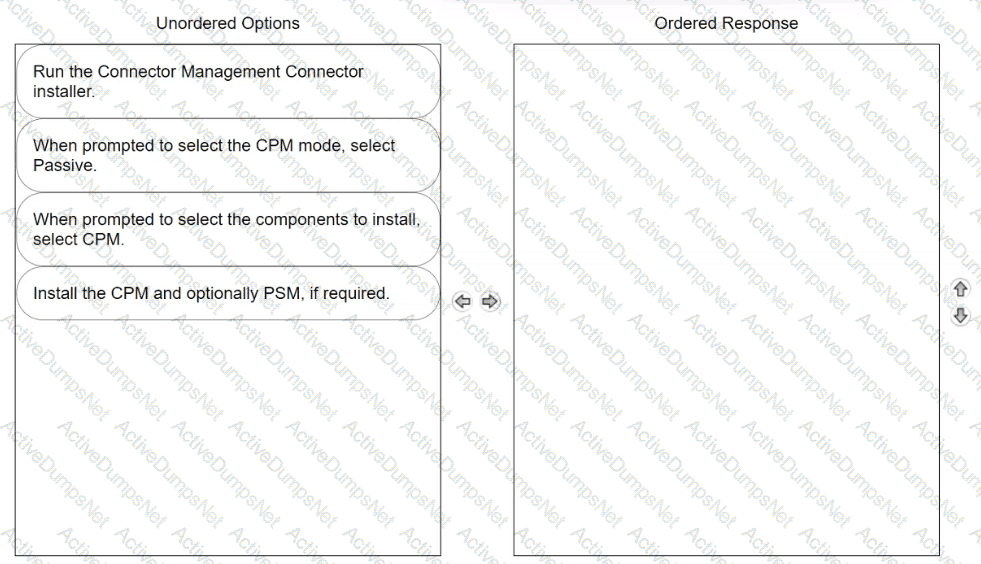
Arrange the steps to install passive CPM using Connector Management in the correct sequence
The System Health page shows the status of all components related to Privilege Cloud. Which components can administrators monitor on this page? (Choose two.)
Which file must you edit to ensure the PSM for SSH server is not hardened automatically after installation?
Which prerequisites are required for installing PSM for SSH (Unix Connector)? (Choose two.)
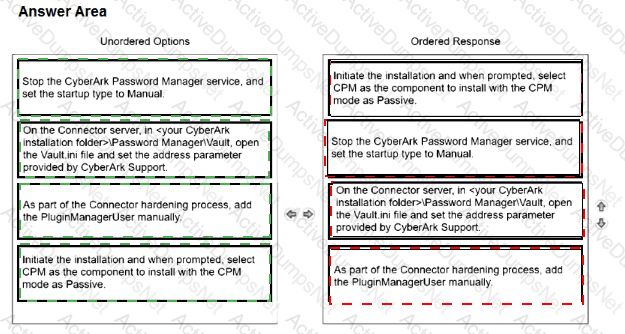
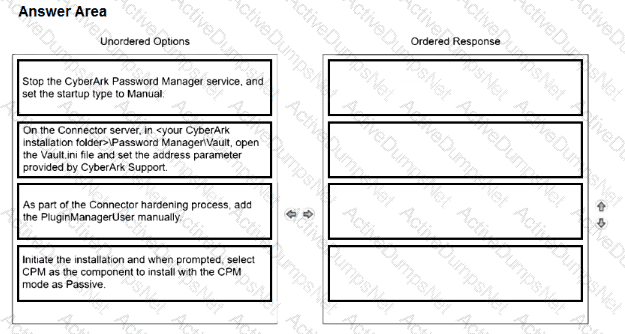
Arrange the steps to install a passive CPM using the Privilege Cloud installer in the correct sequence.
You want to improve performance on the CPM by restricting accounts for the CYBRWINDAD platform to only the WINDEMEA and WINDEMEA_ADMIN Safes. How do you set this in CyberArk?
To use SAML authentication in Privilege Cloud Standard Services, users must first be defined in Privilege Cloud. What are correct methods for defining users? (Choose two.)
Which statements are correct regarding enabling end users from multiple domains in the same forest to authenticate to CyberArk Privilege Cloud? (Choose two.)
Which group has only View Audit and View Safe permissions?
In which platform configuration section under Automatic Password Management is the AllowedSafes platform parameter found?
When performing “In Domain” hardening of a PSM server, which steps are recommended? (Choose two.)
You plan to install the Privilege Cloud Connector on Windows Server 2019 and must leverage your existing RDS Per-user licenses for PSM connections. What must you do?
Which component supports the required communication to send audit logs from Privilege Cloud through the Syslog protocol to a SIEM application?