CrowdStrike CCSE-204 CrowdStrike Engineer Exam Practice Test
CrowdStrike Engineer Questions and Answers
Review the log sample below:
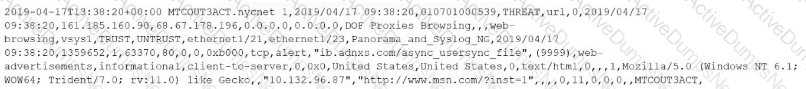
What type of parser should be used to extract fields and values from this log?
You suspect that an API key you recently generated has been compromised.
What should you do?
You are reviewing logs and find that the content appears as one large block of text within the @rawstring field for incoming firewall logs. The other expected structured fields are empty.
What is the cause of this issue?
Which default parser would you use to parse the log event below?
Jan 15 14:22:07 host1 sshd[1234]: Failed login
Which command helps visualize in real time whether sources and sinks are working properly in the Log Collector?
Which CPS-compliant practice should be followed when a third-party field has no matching ECS field?
The parseJson() function would be used to parse which log message format from the list below?
Which Falcon LogScale Collector mode keeps the log source configuration stored locally on the collector host instead of centrally in Fleet Management?
How can you enable internal logging for a specific Falcon Log Collector instance from the Fleet view?
You need to import a pre-built workflow into Fusion SOAR to automate a part of your incident response process.
Which file format would you use?
What should you do with a field that is not CPS-compliant when adding it to a parser?
In the Next-Gen SIEM Connector Dashboard, what is the maximum retention period for which you can query third-party data ingestion metrics?
An event has the following fields:
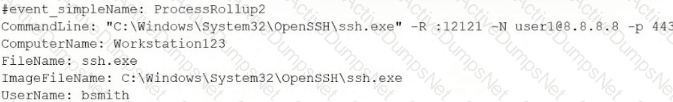
Which CQL query will output the frequency of a unique set of ComputerName, UserName, CommandLine?
What dashboard presents a view of third-party data ingestion over the past 30 days?
Which three System alerts are enabled by default in Next-Gen SIEM for third-party connectors?
Which field should be used in a correlation rule when detections must be based on the original event occurrence time?
You notice that the format of incoming logs suddenly changes from JSON format to key-value pairs during log collection.
What action would you take to parse the data correctly?
You are onboarding a log source that includes a timestamp with a different timezone.
How should you address any time parsing errors that occur?
