Which of the following cloud deployment strategies is best for an organization that wants to run open-source workloads with other organizations that are sharing the cost?
A company wants to implement a work environment that will have low operational overhead and highly accessible enterprise resource planning, email, and data resources. Which of
the following cloud service models should the company implement?
Which of the following do developers use to keep track of changes made during software development projects?
Which of the following integration systems would best reduce unnecessary network traffic by allowing data to travel bidirectionally and facilitating real-time results for developers who need to display critical information within applications?
Which of the following is used to deliver code quickly and efficiently across the development, test, and production environments?
A cloud engineer is reviewing a disaster recovery plan that includes the following requirements:
• System state, files, and configurations must be backed up on a weekly basis.
• The system state, file, and configuration backups must be tested annually.
Which of the following backup methods should the engineer implement for the first week the plan is executed?
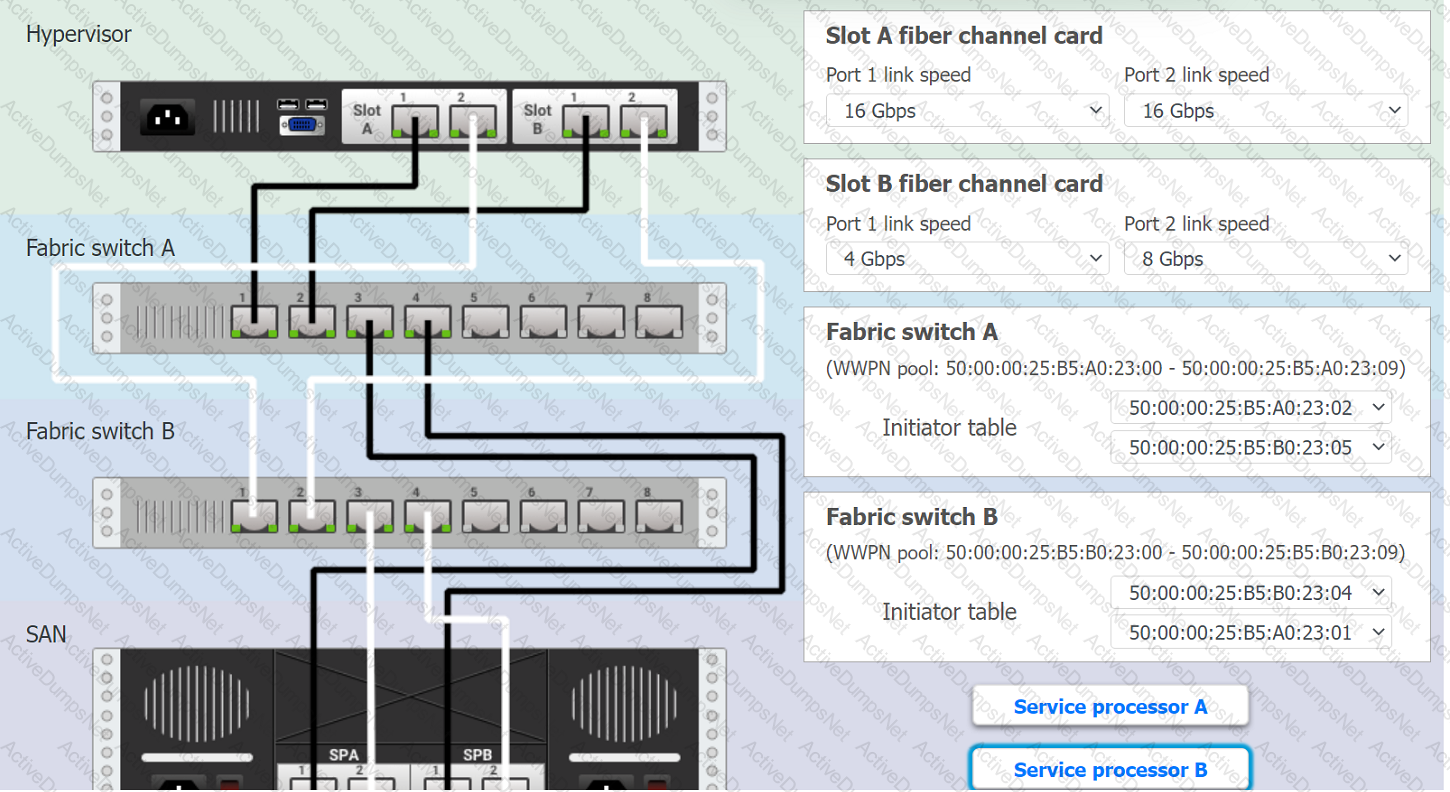
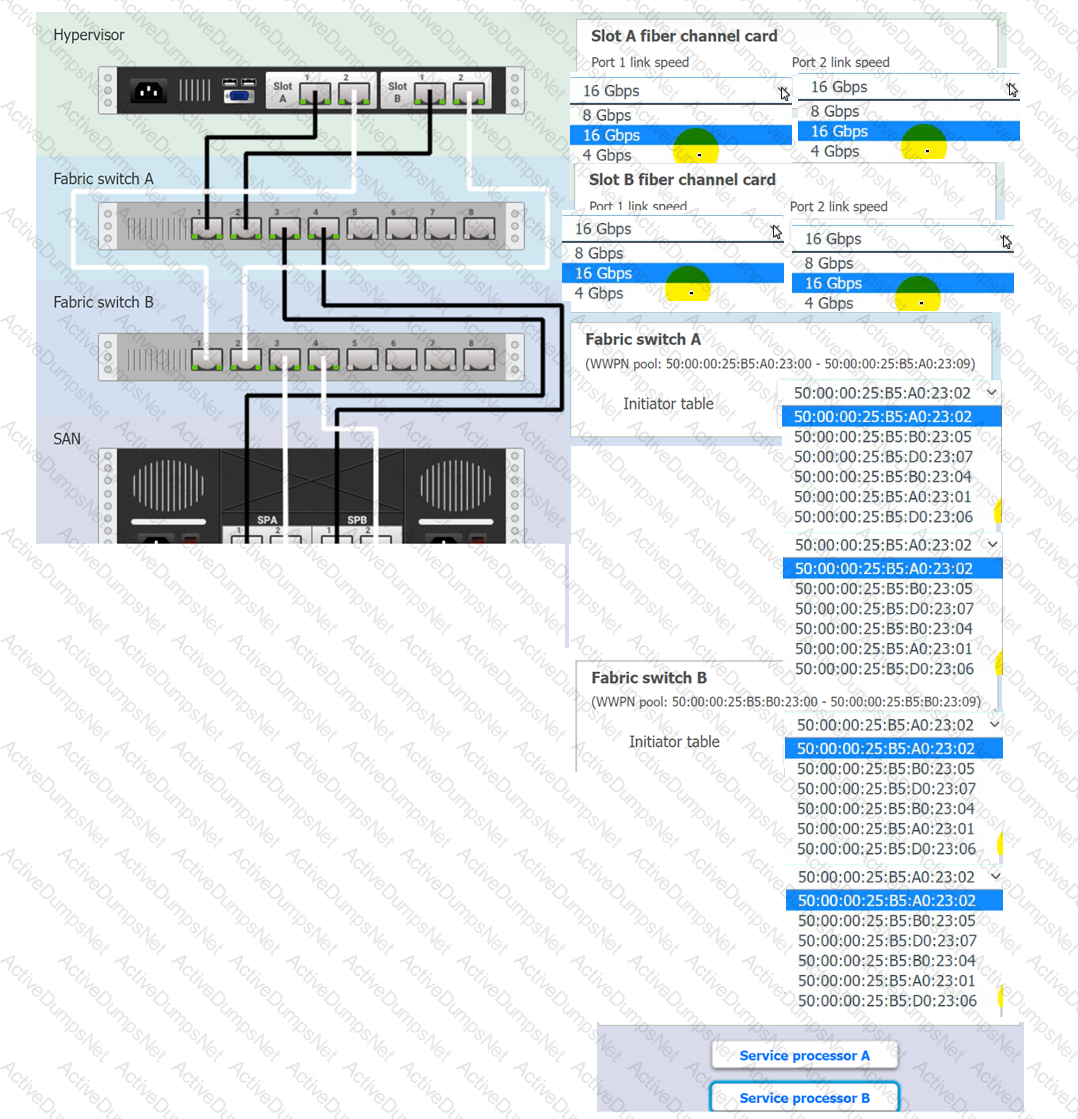
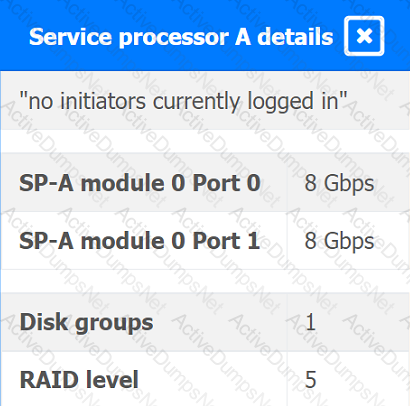
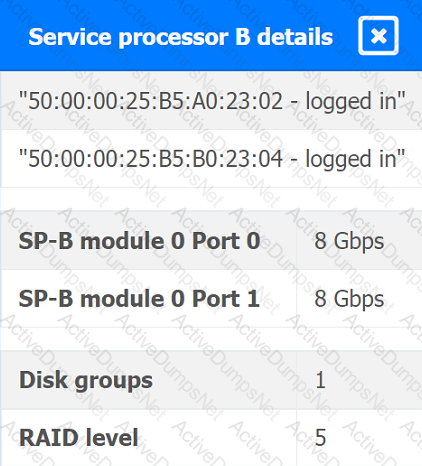
You are a cloud engineer working for a cloud service provider that is responsible for an
IaaS offering.
Your customer, who creates VMs and manages virtual storage, has noticed I/O bandwidth issues and low IOPS (under 9000).
Your manager wants you to verify the proper storage configuration as dictated by your service level agreement (SLA).
The SLA specifies:
. Each SFP on the hypervisor host must be set to the maximum link speed
allowed by the SAN array. . All SAN array disk groups must be configured in a RAID 5.
. The SAN array must be fully configured for redundant fabric paths. . IOPS should not fall below 14000
INSTRUCTIONS
Click on each service processor to review the displayed information. Then click on the drop-down menus to change the settings of each device as necessary to conform to the SLA requirements.
A cloud engineer wants to implement a disaster recovery strategy that:
. Is cost-effective.
. Reduces the amount of data loss in case of a disaster.
. Enables recovery with the least amount of downtime.
Which of the following disaster recovery strategies best describes what the cloud engineer wants to achieve?
A customer is migrating applications to the cloud and wants to grant authorization based on the classification levels of each system. Which of the following should the customer implement to ensure authorisation to systems is granted when the user and system classification properties match? (Select two).
A company's man web application is no longer accessible via the internet. The cloud administrator investigates and discovers the application is accessible locally and only via an IP access. Which of the following was misconfigured?
Which of the following cloud deployment models is the best way to replicate a workload non-disruptively between on-premises servers and a public cloud?
A cloud solutions architect is designing a VM-based solution that requires reducing the cost as much as possible. Which of the following solutions will best satisfy this requirement?
Which of the following is the most cost-effective way to store data that is infrequently accessed?
A company wants to optimize cloud resources and lower the overhead caused by managing multiple operating systems. Which of the following compute resources would be best to help to achieve this goal?
Which of the following container storage types loses data after a restart?
An IT manager is migrating the production environment to the cloud but needs to keep control of the operating systems, patches, and settings of all resources. Which of the following deployment models will best meet the requirements?
A video surveillance system records road incidents and stores the videos locally before uploading them to the cloud and deleting them from local storage. Which of the following
best describes the nature of the local storage?
Which of the following describes what CRUD is typically used for?
Which of the following compute resources is the most optimal for running a single scripted task on a schedule?
An organization has been using an old version of an Apache Log4j software component in its critical software application. Which of the following should the organization use to calculate the severity of the risk from using this component?
A cloud engineer is troubleshooting an application that consumes multiple third-party REST APIs. The application is randomly experiencing high latency. Which of the following would best help determine the source of the latency?
For compliance purposes, a cloud developer at an insurance company needs to save all customer policies for more than ten years. Which of the following options is the most cost-
efficient tier to save the data in the cloud?
Which of the following network protocols is generally used in a NAS environment?
Which of the following will best reduce the cost of running workloads while maintaining the same performance? (Select two).
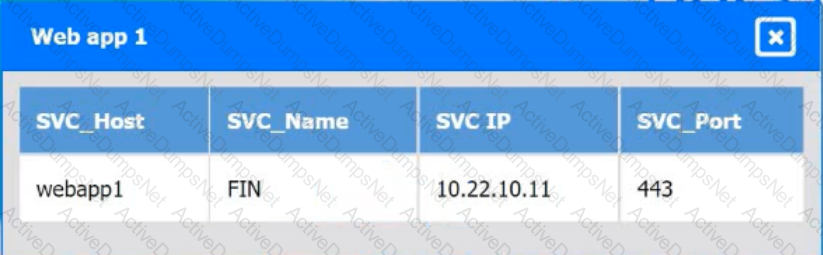
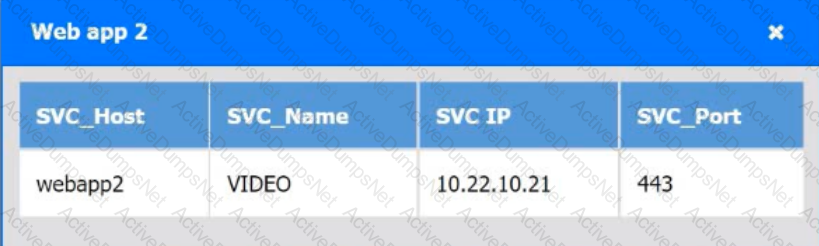
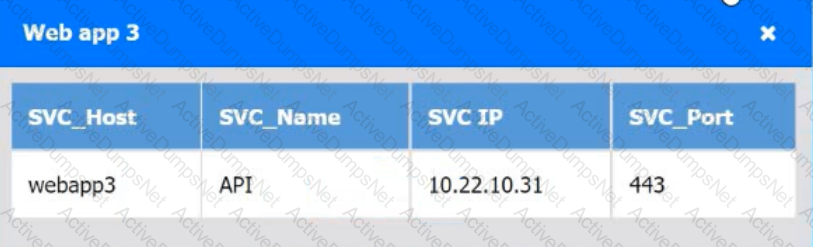
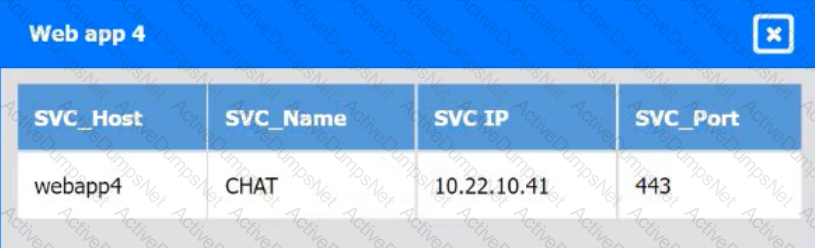
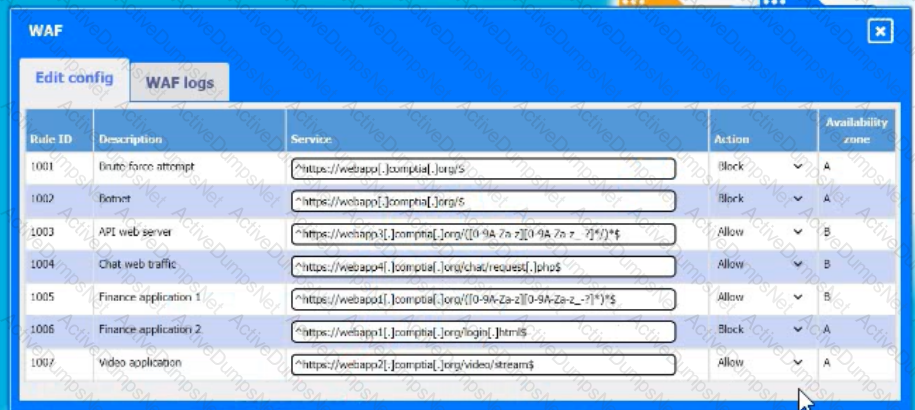
A company hosts various containerized applications for business uses. A client reports that one of its routine business applications fails to load the web-based login prompt hosted in the company cloud.
Click on each device and resource. Review the configurations, logs, and characteristics of each node in the architecture to diagnose the issue. Then, make the necessary changes to the WAF configuration to remediate the issue.
The company's IDS has reported an anomaly. The cloud engineer remotely accesses the cloud instance, runs a command, and receives the following information:
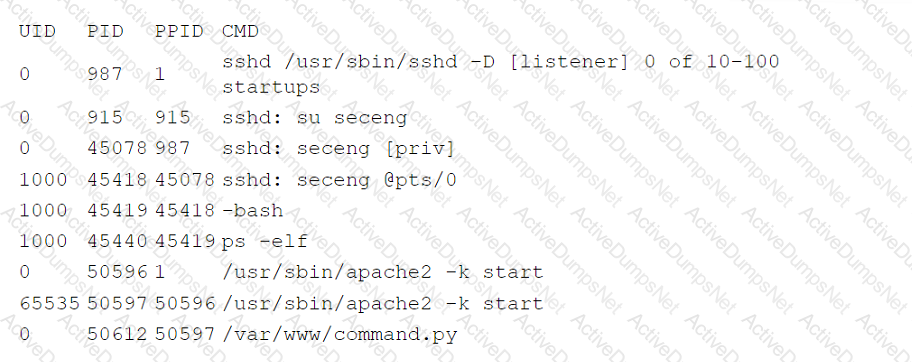
Which of the following is the most likely root cause of this anomaly?
A cloud engineer is deploying a cloud solution that will be used on premises with need-to-know access. Which of the following cloud deployment models best meets this
requirement?
The performance of an e-commerce website decreases dramatically during random periods. The IT team is evaluating available resources to mitigate the situation. Which of the following is the best approach to effectively manage this scenario'?
A company migrated its CRM system to a SaaS solution. The security team is updating the RAG matrix for the newly migrated CRM. Given the following table:
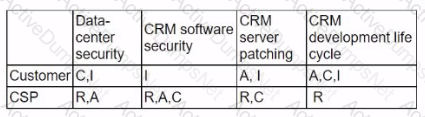
Which of the following responsibility assignments best aligns with the shared responsibility model for the new CRM?
A cloud engineer needs to deploy a new version of a web application to 100 servers. In the past, new version deployments have caused outages. Which of the following deployment types should the cloud engineer implement to prevent the outages from happening this time?
A company runs a discussion forum that caters to global users. The company's monitoring system reports that the home page suddenly is seeing elevated response times, even
though internal monitoring has reported no issues or changes. Which of the following is the most likely cause of this issue?
A developer is sending requests to a SaaS application. The developer becomes unable to send more requests after sending a number of them, but other developers can still send requests. Which of the following is most likely causing the issue?
A developer is deploying a new version of a containerized application. The DevOps team wants:
• No disruption
• No performance degradation
* Cost-effective deployment
• Minimal deployment time
Which of the following is the best deployment strategy given the requirements?
An organization's critical data was exfiltrated from a computer system in a cyberattack. A cloud analyst wants to identify the root cause and is reviewing the following security logs of
a software web application:
"2021/12/18 09:33:12" "10. 34. 32.18" "104. 224. 123. 119" "POST / login.php?u=administrator&p=or%201%20=1"
"2021/12/18 09:33:13" "10.34. 32.18" "104. 224. 123.119" "POST /login. php?u=administrator&p=%27%0A"
"2021/12/18 09:33:14" "10. 34. 32.18" "104. 224. 123. 119" "POST /login. php?u=administrator&p=%26"
"2021/12/18 09:33:17" "10.34. 32.18" "104. 224. 123.119" "POST / login.php?u=administrator&p=%3B"
"2021/12/18 09:33:12" "10.34. 32. 18" "104. 224. 123. 119" "POST / login. php?u=admin&p=or%201%20=1"
"2021/12/18 09:33:19" "10.34.32.18" "104. 224. 123.119" "POST / login. php?u=admin&p=%27%0A"
"2021/12/18 09:33:21" "10. 34. 32.18" "104.224. 123.119" "POST / login. php?u=admin&p=%26"
"2021/12/18 09:33:23" "10. 34. 32.18" "104. 224. 123.119" "POST / login. php?u=admin&p=%3B"
Which of the following types of attacks occurred?
A cross-site request forgery vulnerability exploited a web application that was hosted in a public laaS network. A security engineer determined that deploying a WAF in blocking mode at a CDN would prevent the application from being exploited again. However, a week after implementing the WAF, the application was exploited again. Which of the following should the security engineer do to make the WAF control effective?
A security engineer recently discovered a vulnerability in the operating system of the company VMs. The operations team reviews the issue and decides all VMs need to be updated
from version 3.4.0 to 3.4.1. Which of the following best describes the type of update that will be applied?
A company implements a web farm with 100 servers behind an application load balancer. Dunng scaling events, new web servers that are placed in service have not loaded all their modules, which causes some requests to the web farm to fail. Which of the following should the cloud engineer implement to address the scaling issue?
A cloud security analyst is investigating the impact of a recent cyberattack. The analyst is reviewing the following information:
Web server access log:
104.210.233.225 - - [21/10/2022:11:17: 40] "POST /uploadfile.html?f=myfile.php" 200 1638674
45.32.10.66 - - [21/10/2022:11:19:12] "GET /welcome.html" 200 5812
104.210.233.225 - - [21/10/2022:11:21:19] "GET / .. / .. / .. / .. /conf/server.xml HTTP/1.1" 200 74458
45.32.10.66 - - [21/10/22:11:22:32] "GET /admin.html HTTP/1.1" 200 9518
Web application firewall log:
"2022/10/21 11:17:33" "10.25.2.35" "104. 210.233.225" "userl" "File transfer completed successfully."
"2022/10/21 11:21:05" "10. 25.2. 35" "104. 210.233.225" "userl" "Accessed application page."
"2022/10/21 11:22:13" "10.25.2.35" "45. 32. 10. 66" "user2" "Accessing admin page. "
Which of the following has occurred?
A group of cloud administrators frequently uses the same deployment template to recreate a cloud-based development environment. The administrators are unable to go back and
review the history of changes they have made to the template. Which of the following cloud resource deployment concepts should the administrator start using?
A company uses containers stored in Docker Hub to deploy workloads (or its laaS infrastructure. The development team releases changes to the containers several times per hour. Which of the following should a cloud engineer do to prevent the proprietary code from being exposed to third parties?
A security analyst confirms a zero-day vulnerability was exploited by hackers who gained access to confidential customer data and installed ransomware on the server Which of the following steps should the security analyst take? (Select two).
A cloud solutions architect needs to have consistency between production, staging, and development environments. Which of the following options will best achieve this goal?
A cloud engineer is developing an operating expense report that will be used to purchase various cloud billing models for virtual machine instances. The cloud billing model must meet the following requirements:
• The instance cannot be ephemeral.
• The minimum life cycle of the instance is expected to be five years.
• The software license is charged per physical CPU count.
Which of the following models would best meet these requirements?
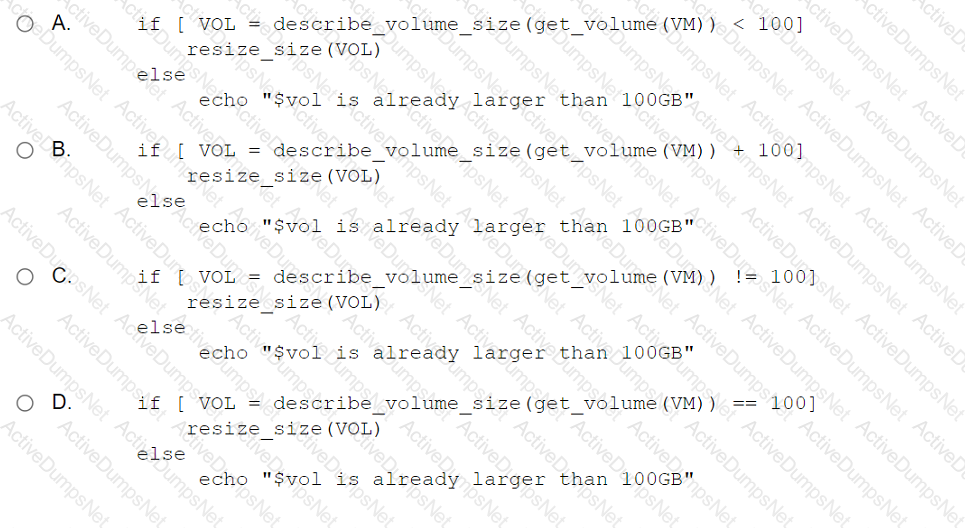
A cloud engineer wants to run a script that increases the volume storage size if it is below 100GB. Which of the following should the engineer run?
Which of the following is a difference between a SAN and a NAS?
An organization's security policy states that software applications should not exchange sensitive data in cleartext. The security analyst is concerned about a software application that uses Base64 to encode credit card data. Which of the following would be the best algorithm to replace Base64?
A junior cloud administrator was recently promoted to cloud administrator and has been added to the cloud administrator group. The cloud administrator group is the only one that can access the engineering VM. The new administrator unsuccessfully attempts to access the engineering VM. However, the other administrators can access it without issue. Which of the following is the best way to identify the root cause?
Which of the following communication methods between on-premises and cloud environments would ensure minimal-to-low latency and overhead?
A cloud engineer is designing a cloud-native, three-tier application. The engineer must adhere to the following security best practices:
• Minimal services should run on all layers of the stack.
• The solution should be vendor agnostic.
• Virealization could be used over physical hardware.
Which of the following concepts should the engineer use to design the system to best meet these requirements?
A cloud engineer is concerned about command-and-control (C2) communication out of a cloud network over HTTPS. Which of the following should the cloud engineer implement to most efficiently identify the type of communication?
Which of the following service options would provide the best availability for critical applications in the event of a disaster?
A company has been using a CRM application that was developed in-house and is hosted on local servers. Due to internal changes, the company wants to migrate the application to the cloud without having to manage the infrastructure. Which of the following services should the company consider?
A company's VMs that are created using the noncritical application tag are automatically shut down at 5:00 p.m. using a cronjob. Which of the following actions would allow a cloud engineer to stop all unresponsive instances with the least effort in case the automation fails?
A banking firm's cloud server will be decommissioned after a successful proof of concept using mirrored data. Which of the following is the best action to take regarding the storage used on the decommissioned server?
A company operates a website that allows customers to upload, share, and retain full ownership of their photographs. Which of the following could affect image ownership as the website usage expands globally?
A cloud consultant needs to modernize a legacy application that can no longer address user demand and is expensive to maintain. Which of the following is the best migration
strategy?
A cloud security analyst is looking for existing security vulnerabilities on software applications. Which of the following describes this vulnerability management phase?
A cloud service provider requires users to migrate to a new type of VM within three months. Which of the following is the best justification for this requirement?
A company's engineering department is conducting a month-long test on the scalability of an in-house-developed software that requires a cluster of 100 or more servers. Which of
the following models is the best to use?
A company has ten cloud engineers working on different manual following is the best method to address this issue?
A CI/CD pipeline is used to deploy VMs to an laaS environment. Which of the following can be used to harden the operating system once the VM is running?
A high-usage cloud resource needs to be monitored in real time on specific events to guarantee its availability. Which of the following actions should be used to meet this requirement?
A company requests that its cloud administrator provision virtual desktops for every user. Given the following information:
• One hundred users are at the company.
• A maximum of 30 users work at the same time.
• Users cannot be interrupted while working on the desktop.
Which of the following strategies will reduce costs the most?
Which of the following is a direct effect of cloud migration on an enterprise?
An engineer wants lo scale several cloud workloads on demand. Which of the following approaches is the most suitable?
An organization is hosting a seminar with eight individuals who need to connect to their own dedicated VM. The technician used the following VM configurations:
IP address: DHCP
NIC: 1Gbps
Network: 10.1.10.0/29
Several users are unable to access their VMs. Which of the following best describes the reason?
A critical security patch is required on a network load balancer in a public cloud. The organization has a major sales conference next week, and the Chief Executive Officer does not want any interruptions during the demonstration of an application behind the load balancer. Which of the following approaches should the cloud security engineer take?
A company that has several branches worldwide needs to facilitate full access to a specific cloud resource to a branch in Spain. Other branches will have only read access. Which of
the following is the best way to grant access to the branch in Spain?