Citrix 1Y0-440 Architecting a Citrix Networking Solution Exam Practice Test
Architecting a Citrix Networking Solution Questions and Answers
Scenario: A Citrix Architect and a team of Workspacelab members have met for a design discussion about the NetScaler Design Project. They captured the following requirements:
- Two pairs of NetScaler MPX appliances will be deployed in the DMZ network and the internal network.
- High availability will be accessible between the pair of NetScaler MPX appliances in the DMZ network.
- Multi-factor authentication must be configured for the NetScaler Gateway virtual server.
- The NetScaler Gateway virtual server is integrated with XenApp/XenDesktop environment.
- Load balancing must be deployed for the users from the workspacelab.com and vendorlab.com domains.
- The logon page must show the workspacelab logo.
- Certificate verification must be performed to identify and extract the username.
- The client certificate must have UserPrincipalName as a subject.
- All the managed workstations for the workspace users must have a client identifications certificate installed on it.
- The workspacelab users connecting from a managed workstation with a client certificate on it should be authenticated using LDAP.
- The workspacelab users connecting from a workstation without a client certificate should be authenticated using LDAP and RADIUS.
- The vendorlab users should be authenticated using Active Directory Federation Service.
- The user credentials must NOT be shared between workspacelab and vendorlab.
- Single Sign-on must be performed between StoreFront and NetScaler Gateway.
- A domain drop down list must be provided if the user connects to the NetScaler Gateway virtual server externally.
- The domain of the user connecting externally must be identified using the domain selected from the domain drop down list.
On performing the deployment, the architect observes that users are always prompted with two-factor authentication when trying to assess externally from an unmanaged workstation.
Click the exhibit button to view the configuration.
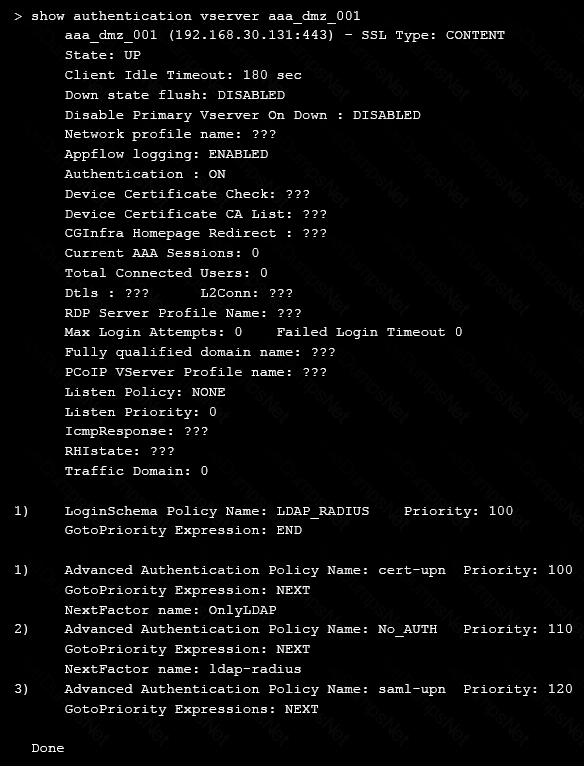
What should the architect do to correct this configuration?
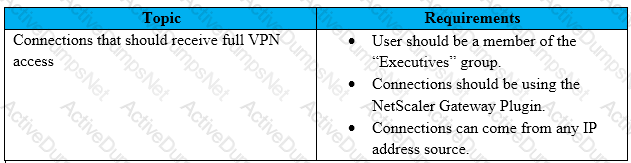
Scenario: A Citrix Architect needs to assess an existing NetScaler gateway deployment. During the assessment, the architect collects key requirements for different user groups, as well as the current session profile settings that are applied to those users.
Click the Exhibit button to view the information collected by the architect.
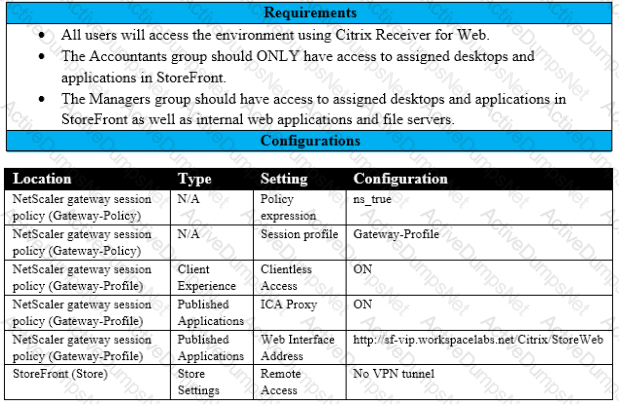
Which configuration should the architect make to meet these requirements?
Scenario: A Citrix Architect needs to plan for a customer environment in which more than 10,000 users will need access. The networking infrastructure needs to be able to handle the expected usage.
Which business driver should be prioritized based on the customer’s requirement?
Which three parameters must a Citrix Architect designate when creating a new session policy? (Choose three.)
Scenario: A Citrix Architect and a team of Workspacelab members met to discuss a Citrix ADC design project. They captured the following requirements from this design discussion:
• All three (3) Workspacelab sites (DC, NDR, and DR) will have similar Citrix ADC configurations and design.
• The external Citrix ADC MPX appliances will have Global Server Load Balancing (GSLB) configured and deployed in Active/Active mode.
• ADNS service should be configured on the Citrix ADC to make it authoritative for domain nsg.workspaceIab.com.
• In GSLB deployment, the DNS resolution should be performed to connect the user to the site with least network latency.
• On the internal Citrix ADC, load balancing for StoreFront services, Citrix XML services, and Citrix Director services must be configured.
• On the external Citrix ADC, the Gateway virtual server must be configured in ICA proxy mode.
Which GSLB method should the architect utilize to meet the design requirements?
Scenario: A Citrix Architect has deployed two MPX devices. 12.0.53.13 nc and MPX 11500 models, in a high availability (HA) pair for the Workspace labs team. The deployment method is two-arm and the devices are installed behind a CISCO ASA 5585 Firewall. The architect enabled the following features on the Citrix ADC devices. Content Switching. SSL Offloading, Load Balancing, Citrix Gateway. Application Firewall in hybrid security and Appflow. All are enabled to send monitoring information to Citrix Application Delivery Management 12.0.53.13 nc build. The architect is preparing to configure load balancing for Microsoft Exchange 2016 server.
The following requirements were discussed during the implementation:
- All traffic needs to be segregated based on applications, and the fewest number of IP addresses should be utilized during the configuration.
- All traffic should be secured and any traffic coming Into FITTP should be redirected to HTTPS.
- Single Sign-on should be created for Microsoft Outlook web access (OWA).
- Citrix ADC should recognize Uniform Resource Identifier (URI) and close the session to Citrix ADC when users hit the Logoff button In Microsoft Outlook web access.
- Users should be able to authenticate using either user principal name (UPN) or sAMAccountName.
- The Layer 7 monitor should be configured to monitor the Microsoft Outlook web access servers and the monitor probes must be sent on SSL.
Which monitor will meet these requirements?
Which StyleBook group should a Citrix Architect use to deploy the configuration for Microsoft SharePoint servers on Citrix ADC Management and Analytics (Citrix Application Delivery Management)?
Scenario: The Workspacelab team has configured their NetScaler Management and Analytics (NMAS) environment. A Citrix Architect needs to log on to the NMAS to check the settings.
Which two authentication methods are supported to meet this requirement? (Choose two.)
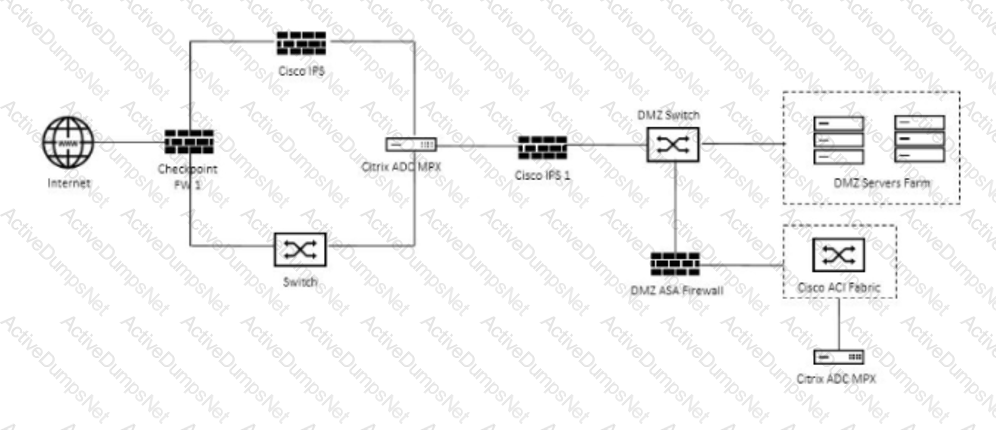
Scenario: A Citrix Architect and a team of Workspacelab members met to discuss a NetScaler design project. They captured the following requirements from this design discussion:
- A pair of NetScaler MPX appliances will be deployed in the DMZ network.
- High Availability will be accessible in the NetScaler MPX in the DMZ Network.
- Load balancing should be performed for the internal network services like Microsoft Exchange Client Access Services and Microsoft App-V.
- The load balancing should be performed for StoreFront.
- The NetScaler Gateway virtual server will be utilizing the StoreFront load-balancing virtual server.
- The NetScaler Gateway virtual server and StoreFront.
- The NetScaler Gateway virtual service and StoreFront and load-balancing services are publicly accessible.
- The traffic for internal and external services must be isolated.
Click the Exhibit button to review the logical network diagram.
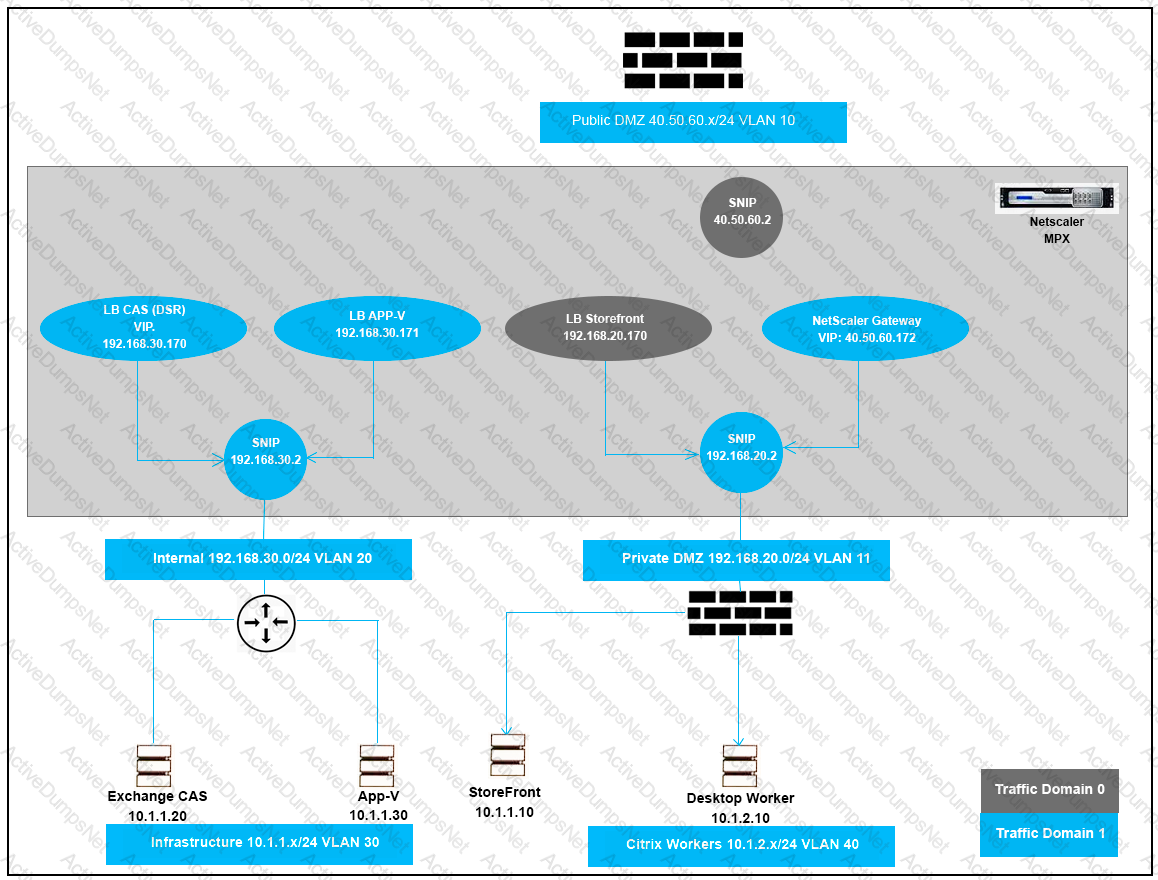
Which two design decisions are incorrect based on these requirements? (Choose two.)
Scenario: A Citrix Architect needs to design a new Citrix ADC Gateway deployment to provide secure RDP access to backend Windows machines.
Click the Exhibit button to view additional requirements collected by the architect during the design discussions.
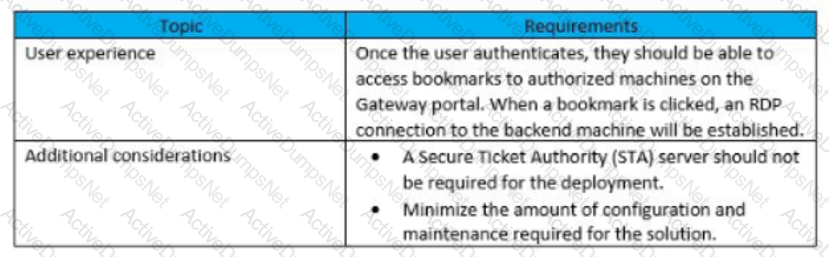
To meet the customer requirements, the architect should deploy the RDP proxy through _______, using a _________ solution. (Choose the correct option to complete the sentence.)
Scenario: A Citrix Architect needs to design a hybrid Citrix Virtual App and Citrix Virtual Desktop environment which will include as well as resource locations in an on-premises datacenter and Microsoft Azure.
Organizational details and requirements are as follows:
- Active Citrix Virtual App and Citrix Virtual Desktop Service subscription
- No existing Citrix deployment
- Minimization of additional costs
- All users should correct directly to the resource locations containing the servers which will host HDX sessions
Click the Exhibit button to view the conceptual environment architecture.
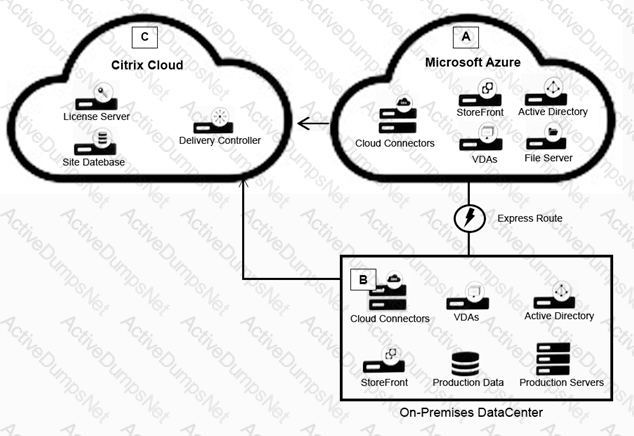
The architect should use___________ in Location A, and should use _______________ in Location B. (Choose the correct option to complete the sentence.)
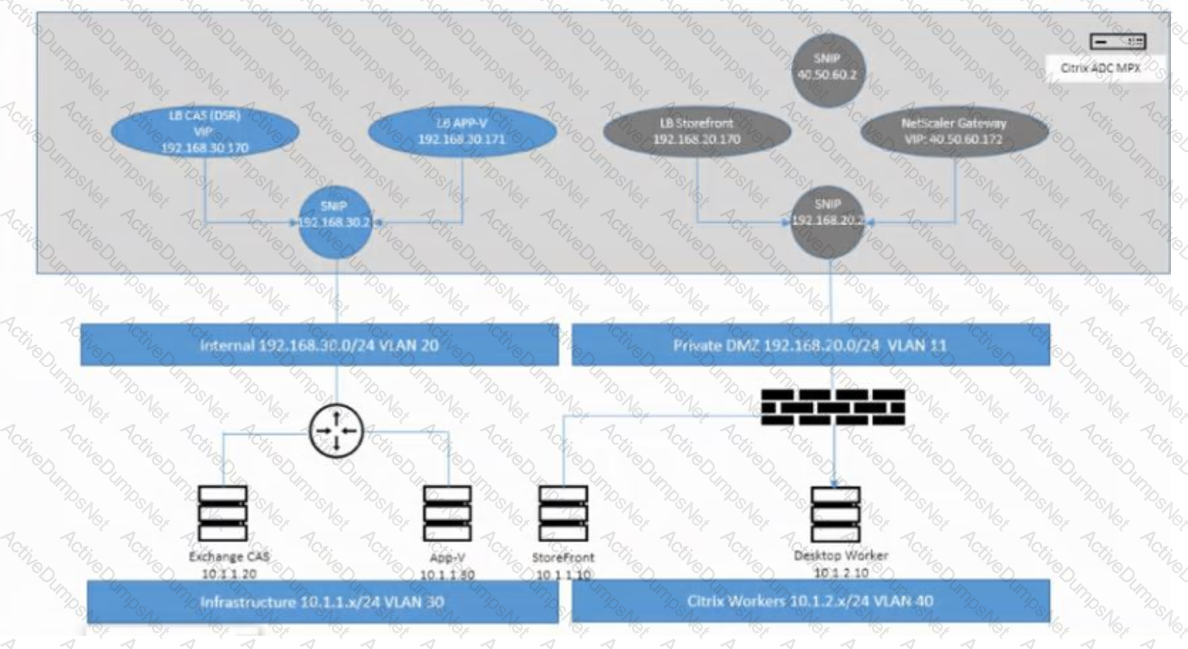
Which IP address should be bound to VLAN 11?
Scenario: A Citrix Architect needs to deploy a load balancing for an application server on the NetScaler. The authentication must be performed on the NetScaler. After the authentication, the Single Sign-on with the application servers must be performed using Kerberos impersonation.
Which three authentication methods can the Architect utilize to gather the credentials from the user in this scenario? (Choose three.)
Scenario: A Citrix Architect has deployed two MPX devices, 12.0.53.13 nc and MPX 11500 models, in high availability (HA) pair for the Workspace labs team. The deployment method is two-arm and the devices are installed behind a CISCO ASA 5585 Firewall. The architect enabled the following features on the NetScaler devices. Content Switching, SSL Offloading, Load Balancing, NetScaler Gateway, Application Firewall in hybrid security and Appflow. All are enabled to send monitoring information to NMAS 12.0.53.13 nc build. The architect is preparing to configure load balancing for Microsoft Exchange 2016 server.
The following requirements were discussed during the implementation:
- All traffic needs to be segregated based on applications, and the fewest number of IP addresses should be utilized during the configuration
- All traffic should be secured and any traffic coming into HTTP should be redirected to HTTPS.
- Single Sign-on should be created for Microsoft Outlook web access (OWA).
- NetScaler should recognize Uniform Resource Identifier (URl) and close the session to NetScaler when users hit the Logoff button in Microsoft Outlook web access.
- Users should be able to authenticate using either user principal name (UPN) or sAMAccountName.
- The Layer 7 monitor should be configured to monitor the Microsoft Outlook web access servers and the monitor probes must be sent on SSL
Which monitor will meet these requirements?
Scenario: A Citrix Architect needs to assess a Citrix Gateway deployment that was recently completed by a customer and is currently in pre-production testing. The Citrix Gateway needs to use ICA proxy to provide access to a Citrix Virtual Apps and Citrix Virtual Desktops environment. During the assessment, the customer informs the architect that users are NOT able to launch published resources using the Gateway virtual server.
Click the Exhibit button to view the troubleshooting details collected by the customer.
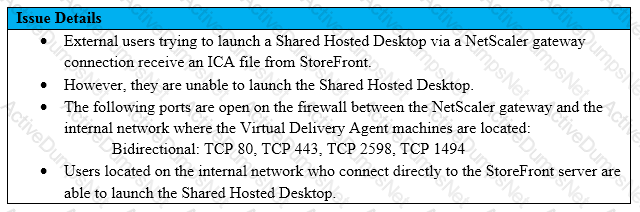
What is the cause of this issue?
Scenario: A Citrix Architect needs to design a hybrid Citrix Virtual App and Citrix Virtual Desktop environment which will include Citrix Cloud as well as resource locations in on-premises datacenter and Microsoft Azure.
Organizational details and requirements are as follows:
- Active Citrix Virtual App and Citrix Virtual Desktop Service subscription
- No existing NetScaler deployment
- About 3,000 remote users are expected to regularly access the environment
- Multi-factor authentication should be used for all external connections
- Solution must provide load balancing for backend application servers
- Load-balancing services must be in Location B
Click the Exhibit button to view the conceptual environment architecture.
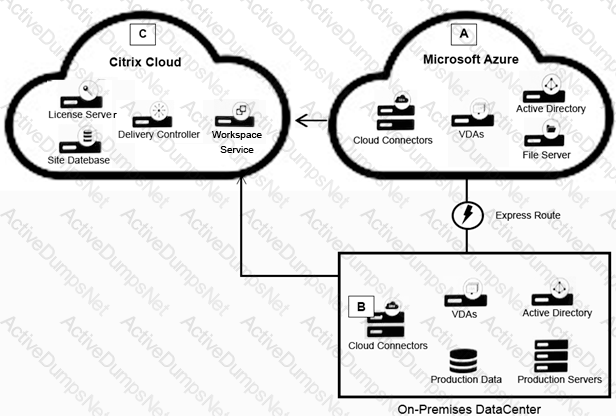
The architect should use ________ in Location A, and should use _________ in Location B. (Choose the correct option to complete the sentence.)
Scenario: A Citrix Architect needs to design a new Citrix ADC Gateway deployment to provide secure RDP access to backend Windows machines.
Click the Exhibit button to view additional requirements collected by the architect during the design discussions.
To meet the customer requirements, the architect should deploy the RDP proxy through _______, using a _________ solution. (Choose the correct option to complete the sentence.)
Scenario: The following NetScaler environment requirements were discussed during a design meeting between a Citrix Architect and the Workspacelab team:
- All traffic should be secured, and any traffic coming into HTTP should be redirected to HTTPS.
- Single Sign-on should be created for Microsoft Outlook web access (OWA).
- NetScaler should recognize Uniform Resource Identifier (URI) and close the session to NetScaler when users hit the Logoff button in Microsoft Outlook web access.
- Users should be able to authenticate using user principal name (UPN).
- The Layer 7 monitor should be configured to monitor the Microsoft Outlook web access servers and the monitor probes must be sent on SSL.
Which method can the architect use to redirect the user accessing https://mail.citrix.com to https://mail.citrix.com?
_________ content type supports sending NITRO commands to NetScaler. (Choose the correct option to complete sentence.)
Scenario: A Citrix Architect has configured two MPX devices in high availability mode with version 12.0.53.13 nc. After a discussion with the security team, the architect enabled the Application Firewall feature for additional protection.
In the initial deployment phase, the following security features were enabled:
- IP address reputation
- HTML SQL injection check
- Start URL
- HTML Cross-site scripting
- Form-field consistency
After deployment in pre-production, the team identifies the following additional security features and changes as further requirements:
- Application Firewall should retain the response of form field in its memory When a client submits the form in the next request. Application Firewall should check for inconsistency in the request before sending it to the web server
- All the requests dropped by Application Firewall should receive a pre-configured HTML error page with appropriate information.
- The Application Firewall profile should be able to handle the data from the RSS feed and an ATOM-based site.
Click the Exhibit button to view an excerpt of the existing configuration.
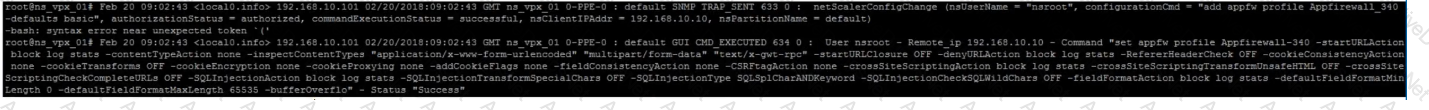
What should the architect do to meet these requirements?
A Citrix Architect needs to make sure that maximum concurrent AAA user sessions are limited to 4000 as a security restriction.
Which authentication setting can the architect utilize to view the current configuration?
Scenario: More than 10,000 users will access a customer’s environment. The current networking infrastructure is capable of supporting the entire workforce of users. However, the number of support staff is limited, and management needs to ensure that they are capable of supporting the full user base.
Which business driver is prioritized, based on the customer’s requirements?
Which three tasks can a Citrix Architect select and schedule using the Citrix ADC maintenance tasks? (Choose three.)
Scenario: A Citrix Architect needs to design a new multi-datacenter Citrix ADC deployment. The customer wants Citrix ADC to provide access the various backend resources by using Global Server Load Balancing (GSLB) in an Active-Active deployment.
Click the Exhibit button to view additional requirements identified by the architect.
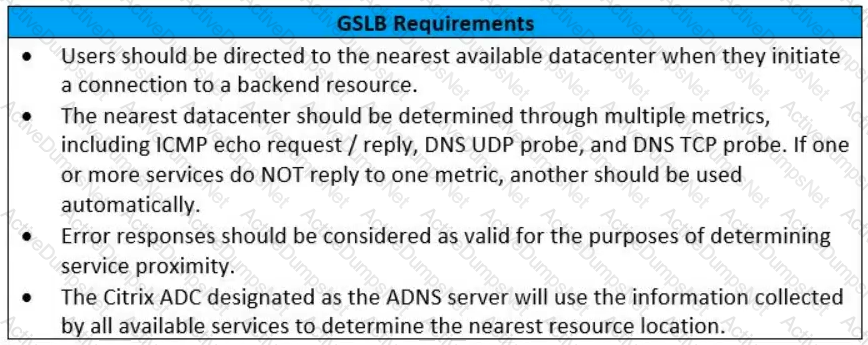
Which GSLB algorithm or method should the architect use for the deployment based on the stated requirements?
Scenario: Based on a discussion between a Citrix Architect and team of Workspacelab has been created across three (3) sites.
They captured the following requirements during the design discussion held for NetScaler design projects:
- All three (3) Workspacelab sites (DC, NDR, and DR) will have similar NetScaler configuration and design.
- Both external and internal NetScaler MPX appliances will have Global Server Load balancing (GSLB) configured and deployed in Active/Passive mode.
- GSLB should resolve both A and AAA DNS queries.
- In the GSLB deployment, the NDR site will act as backup for the DC site. whereas the DR site will act as backup for the NDR site.
- When the external NetScaler replies to DNS traffic coming in through Cisco Firepower IPS, the replies should be sent back through the same path.
- On the internal NetScaler, both front-end VIP and back-end SNIP will be part of the same subnet.
- USIP is configured on the DMZ NetScaler appliances.
- The external NetScaler will act default gateway for back-end servers.
- All three (3) sites (DC, NDR, and DR) will have two (2) links to the Internet from different service providers configured in Active/Standby mode.
Which design decision must the architect make to meet the design requirements above?
A Citrix Architect can execute a configuration job using a DeployMasterConfiguration template on a Citrix ADC____deployed________. (Choose the correct option to complete sentence:
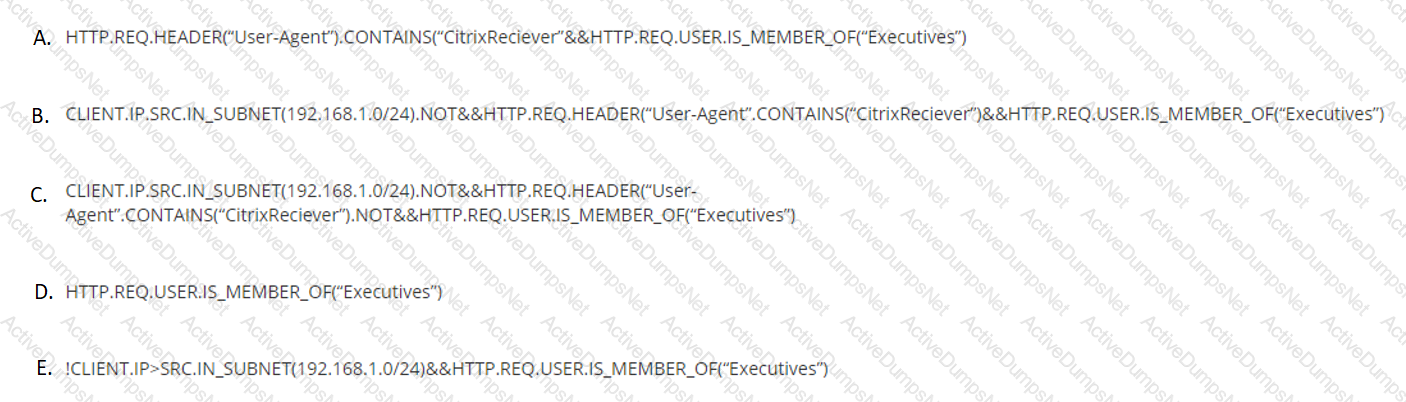
Scenario: A Citrix Architect needs to design a new Citrix Gateway deployment. During the design discussions, the architect documents the key requirements about when to provide VPN access for incoming connections to the Citrix Gateway virtual server. Click the Exhibit button to view the requirements.
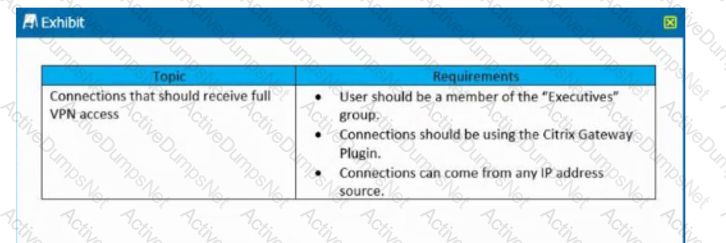
Which policy expression will meet these requirements?
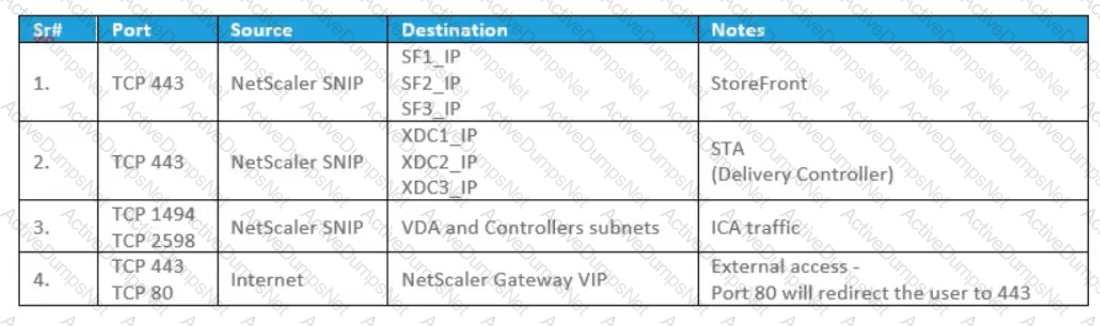
Scenario: A Citrix Architect and a team of Workspacelab members met to discuss a Citrix ADC design project. They captured the following requirements from this design discussion:
- All three (3) Workspacelab sites (DC. NDR. and DR) will have similar Citrix ADC configurations and design.
- The external Citrix ADC MPX appliances will have Global Server Load Balancing (GSLB) configured and deployed in Active/Active mode
- ADNS service should be configured on the Citrix ADC to make it authoritative for domain nsg Workspacelab.com.
- In GSLB deployment, the DNS resolution should be performed to connect the user to the site with least network latency.
- On the internal Citrix ADC, load balancing for StoreFront services, Citrix XML services, and Citrix Director services must be configured
- On the external Citrix ADC. the Gateway virtual server must be configured in ICA proxy mode
Click the Exhibit button to view the logical representation of the network and the firewall policy prerequisites provided by the architect. On which two firewalls should the architect configure the policies? (Choose two.)
Scenario: A Citrix Architect holds a design discussion with a team of Workspacelab members, and they capture the following requirements for the Citrix ADC design project:
- A pair of Citrlx ADC MPX appliances will be deployed in the DMZ network and another pair in the internal network.
- High availability will be accessible between the pair of Citrix ADC MPX appliances in the DMZ network.
- Multi-factor authentication must be configured for the Citrix Gateway virtual server.
- The Citrix Gateway virtual server is integrated with the StoreFront server.
- Load balancing must be configured for the StoreFront server. •Authentication must be deployed for users from the workspacelab.com domain.
- The Workspacelab users should be authenticated using Cert Policy and LDAP.
- All the client certificates must be SHA 256-signed, 2048 bits, and have UserPrincipalName as the subject.
- Single Sign-on must be performed between StoreFront and Citrix Gateway. After deployment the architect observes that LDAP authentication is failing.
Click the Exhibit button to review the output of aaad.debug and the configuration of the authentication policy.
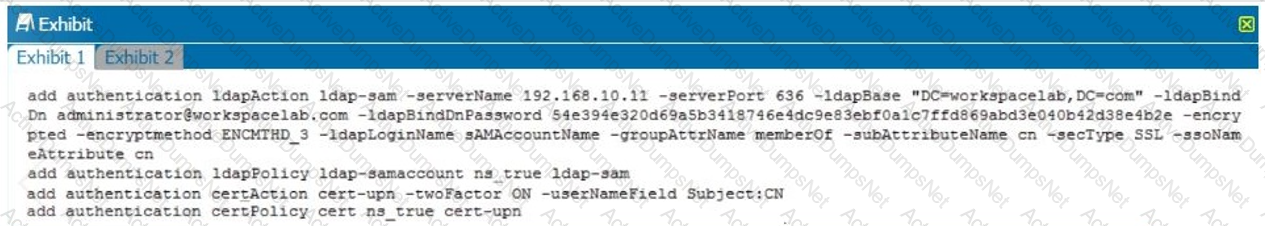
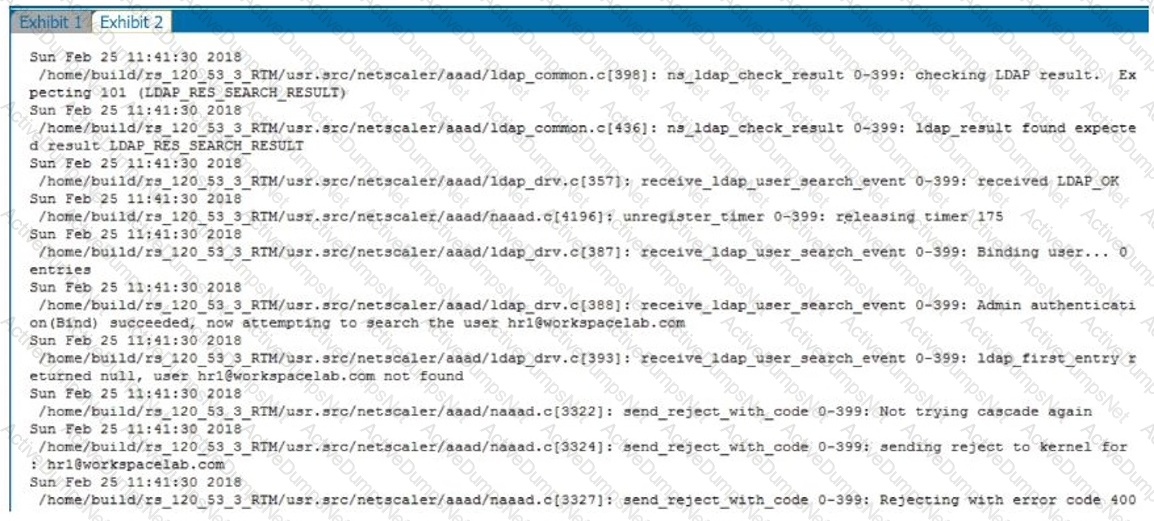
What is causing this issue?
Which encoding type can a Citrix Architect use to encode the StyleBook content, when importing the StyleBook configuration under source attribute?
Scenario: The Workspacelab team has implemented a Citrix ADC high availability pair and Citrix ADC Management and Analytics (Citrix Application Delivery Management). The Citrix Application Delivery Management was configured by a Citrix Architect to monitor and manage these devices. The Workspacelab team wants to load balance their Microsoft SharePoint servers on the Citrix ADC and needs the process to be streamlined and administered using Citrix Application Delivery Management. The following requirements were discussed during the meeting.
• The Microsoft SharePoint server should be optimized. Load balanced, and secured in the network and should be deployed using Citrix Application Delivery Management.
• All the configurations should be verified before getting pushed to the Citrix Application Delivery Management.
What is a prerequisite for installing Microsoft SharePoint using Citrix Application Delivery Management?
Scenario: A Citrix Architect needs to design a new solution within Microsoft Azure. The architect would like to create a highly available Citrix ADC VPX pair to provide load balancing for applications hosted in the Azure deployment which will receive traffic arriving from the Internet. In order to maximize its investment, the organization would like both Citrix ADC VPX instances to actively load-balance connection requests. Which two approaches are possible solutions for the architect to use to design the solution? (Choose two.)
Scenario: Based on a discussion between a Citrix Architect and a team of Workspacelab members, the MPX Logical layout for Workspacelab has been created across three (3) sites.
They captured the following requirements during the design discussion held for a Citrix ADC design project:
- All three (3) Workspacelab sites (DC, NDR, and DR) will have similar NetScaler configurations and design.
- Both external and internal NetScaler MPX appliances will have Global Server Load Balancing (GSLB) configured and deployed in Active/Passive mode.
- GSLB should resolve both A and AAA DNS queries.
- In the GSLB deployment, the NDR site will act as backup for the DC site, whereas the DR site will act as backup for the NDR site.
- When the external NetScaler replies to DNS traffic coming in through Cisco Firepower IPS, the replies should be sent back through the same path.
- On the internal NetScaler, both the front-end VIP and backend SNIP will be part of the same subnet.
- The external NetScaler will act as default gateway for the backend servers.
- All three (3) sites, DC, NDR, and DR, will have two (2) links to the Internet from different service providers configured in Active/Standby mode.
Which design decision must the architect make the design requirements above?
Which two options should a Citrix Architect evaluate during a capabilities assessment? (Choose two.)
Which two parameters are required to ensure that after authentication, the cookies can be transferred from browser to non-browser applications? (Choose two.)
Scenario: A Citrix Architect needs to assess a Citrix Gateway deployment that was recently completed by a customer and is currently in pre-production testing The Citrix Gateway needs to use ICA proxy to provide access to a Citrix Virtual Apps and Citrix Virtual Desktops environment. During the assessment, the customer informs the architect that users are NOT able to launch published resources using the Gateway virtual server.
Click the Exhibit button to view the troubleshooting details collected by the customer.
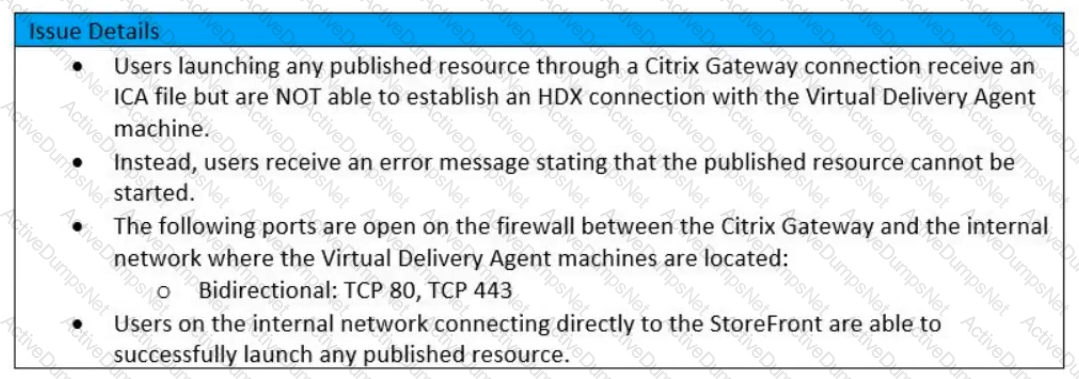
Which two reasons could cause this issue? (Choose two)
Which four parameters can a Citrix Architect change after the initial creation of a session profile? (Choose four.)
Which NetScaler Management and Analytics System (NMAS) utility can a Citrix Architect utilize to verify the configuration template created by the NMAS StyleBook, before actually executing it on the NetScaler?
Scenario: The Workspacelab team has configured their Citrix ADC Management and Analytics (Citrix Application Delivery Management) environment. A Citrix Architect needs to log on to the Citrix Application Delivery Management to check the settings.
Which two authentication methods are supported to meet this requirement? (Choose two.)
Scenario: A Citrix Architect observes the following configurations while performing an assessment of a Citrix ADC deployment:
- Citrix Gateway virtual server nsg-dmz-001 is configured in ICA Proxy mode.
- The authentication method used is Plaintext LDAP.
- The session policies bound are configured to integrate with StoreFront in ICA proxy mode to perform Single Sign-on.
- The connection to LDAP server is performed using SNIP by Citrix ADC.
- To meet the new design requirement the architect needs to change the SNIP used for communication with LDAP servers.
Which AAA parameter must the architect verify to update the source IP address for the communication from Citrix ADC to the LDAP server?
Scenario: Based on a discussion between a Citrix Architect and a team of Workspacelab members, the MPX Logical layout for Workspacelab has been created across three (3) sites.
The requirements captured during the design discussion held for a NetScaler design project are as follows:
- Two (2) pairs of NetScaler MPX appliances deployed in the DMZ and internal network.
- High Availability will be accessible for each NetScaler MPX
- The external NetScaler MPX appliance will be deployed in multi-arm mode.
- The internal NetScaler MPX will be deployed in single-arm mode wherein it will be connected to Cisco ACI Fabric.
- All three (3) Workspacelab sites: Dc, NDR and DR, will have similar NetScaler configurations and design.
How many NetScaler MPX appliances should the architect deploy at each site to meet the design requirements above?
Scenario: A Citrix Architect has deployed load balancing for SharePoint 2010 on a Citrix ADC instance. While editing the document, the architect observed the error displayed below:
Sorry, we couldn't open 'https://sharepointcs.emea.in/Shared Documents/Citrix Enhancement Request Form.doc'
After troubleshooting, the architect discovers the issue. When a user opens a document, it opens in the browser, but while editing the document, thd session is transferred from the browser to the Word application During this time, the cookies should be transferred from the browser to the Word application.
Which two configurations should the architect modify to ensure that the cookies are shared between the browser and non-browser applications? (Choose two.)
Which session parameter does the default authorization setting control when authentication, authorization, and auditing profiles are configured?
Scenario: A Citrix Architect has implemented two high availability pairs of MPX 5500 and MPX 11500 devices respectively with 12.0.53.13 nc version. The NetScaler devices are set up to handle NetScaler Gateway, Load Balancing, Application Firewall, and Content Switching. The Workspacelab infrastructure is set up to be monitored with NMAS version 12.0.53.13 nc by the Workspacelab administrators. The Workspacelab team wants to implement one more pair of NetScaler MPX 7500 devices with version 12.0.53.13 nc.
The Citrix consulting team has assigned the task to implement these NetScaler devices in the infrastructure and set them up to be monitored and managed by NMAS.
The following are the requirements that were discussed during the project initiation call:
- NMAS should be configured to get the infrastructure information under sections such as HDX Insight, WEB Insight, and Security Insight.
- Configuration on the new MPX devices should be identical to MPX 11500 devices.
- Configuration changes after the deployment and initial setup should be optimized using NMAS.
- NMAS should be utilized to configure templates that can be utilized by the Workspacelab team in future deployment.
- As per the requirement from the Workspacelab team, NMAS should be store the audited data for only 15 days.
Which process should the architect utilize to ensure that the deployment of MPX 11500 devices are optimized and that it is correct, before deploying the devices in production?
A Citrix Architect can execute a configuration job using a DeployMasterConfiguration template on a Citrix ADC _________deployed_________. (Choose the correct option to complete sentence.)
