Cisco 400-007 Cisco Certified Design Expert (CCDE v3.1) Exam Practice Test
Cisco Certified Design Expert (CCDE v3.1) Questions and Answers
Company XYZ wants to improve the security design of their network to include protection from reconnaissance and DoS attacks on their sub interfaces destined toward next hop routers. Which technology can be used to prevent these types of attacks?
Which service abstracts away the management of the operating system, middleware, and runtime?
While positive feedback loops generally don ' t last long enough to bring down a network completely, they can still last long enough to disrupt traffic flows or to cause the network to converge more slowly than it should.
What are two examples of cases where a positive feedback loop can be long-lived and devastating to the network ' s control plane? (Choose two)
A customer has a functional requirement that states HR systems within a data center must be segmented from other systems that reside in the same data center and same VLAN The systems run legacy applications by using hard-coded IP addresses with all HR systems dedicated to 129 to 254 of the 10 20.20 0/24 prefix Which segmentation method is optimal for the customer?
PaaS provides a cloud-based platform for developing, running, managing applications. Users access the PaaS through a GUI, where development or DevOps teams can collaborate on all their work across the entire application lifecycle including coding, integration, testing, delivery, deployment, and feedback. Which benefit does an organization get by using PaaS?
Which two compliance audit functions are useful to meet business requirements? (Choose two.)
The SD-WAN architecture is composed of separate orchestration management, control, and data planes Which activity happens at the orchestration plane?
A large defense organization is planning their cloud migration journey, but they have high data sovereignty concerns, major regulation or compliance requirements, and very restrictive SLAs. Which cloud architecture model can be adopted?
As a service provider is implementing Strong Access Control Measures, which two of the following PCI Data Security Standard requirements must be met? (Choose two . )
A customer migrates from a traditional Layer 2 data center network Into a new SDN- based, spine-and-leaf VXLAN EVPN data center within the same location. The networks are joined to enable host migration at Layer 2. Which activity should be completed each time a legacy network is migrated?
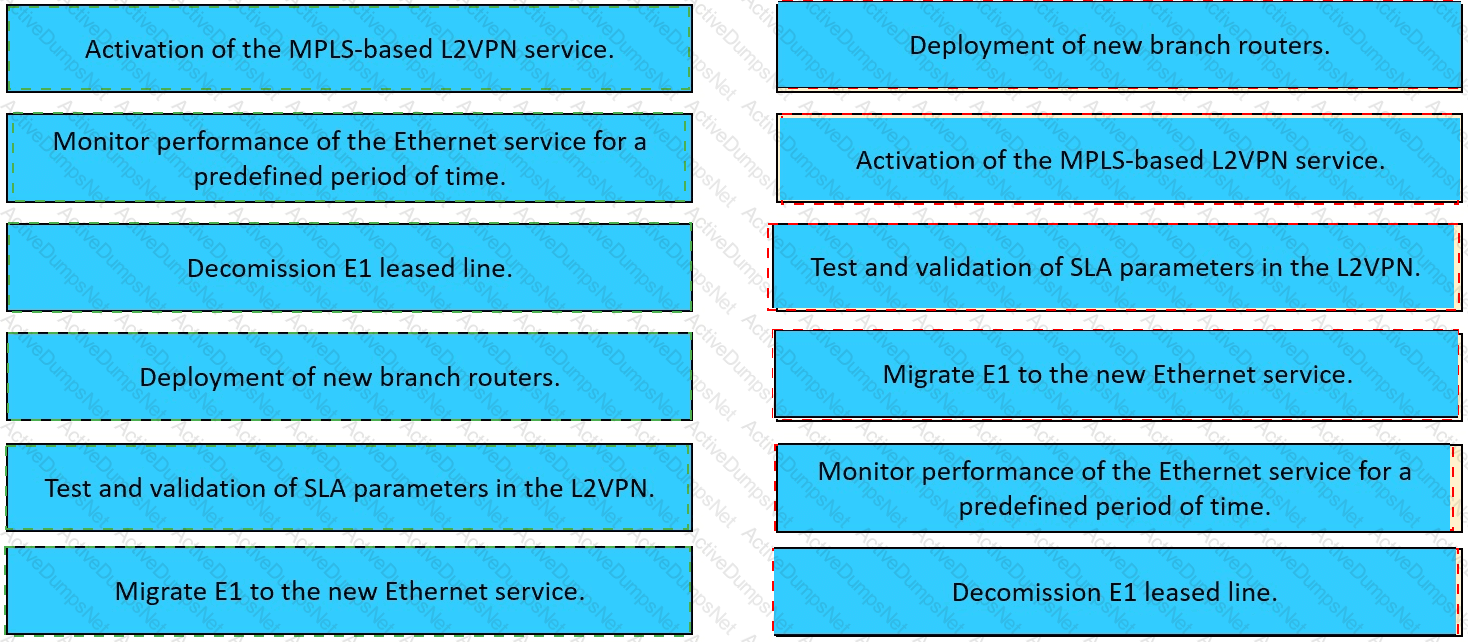
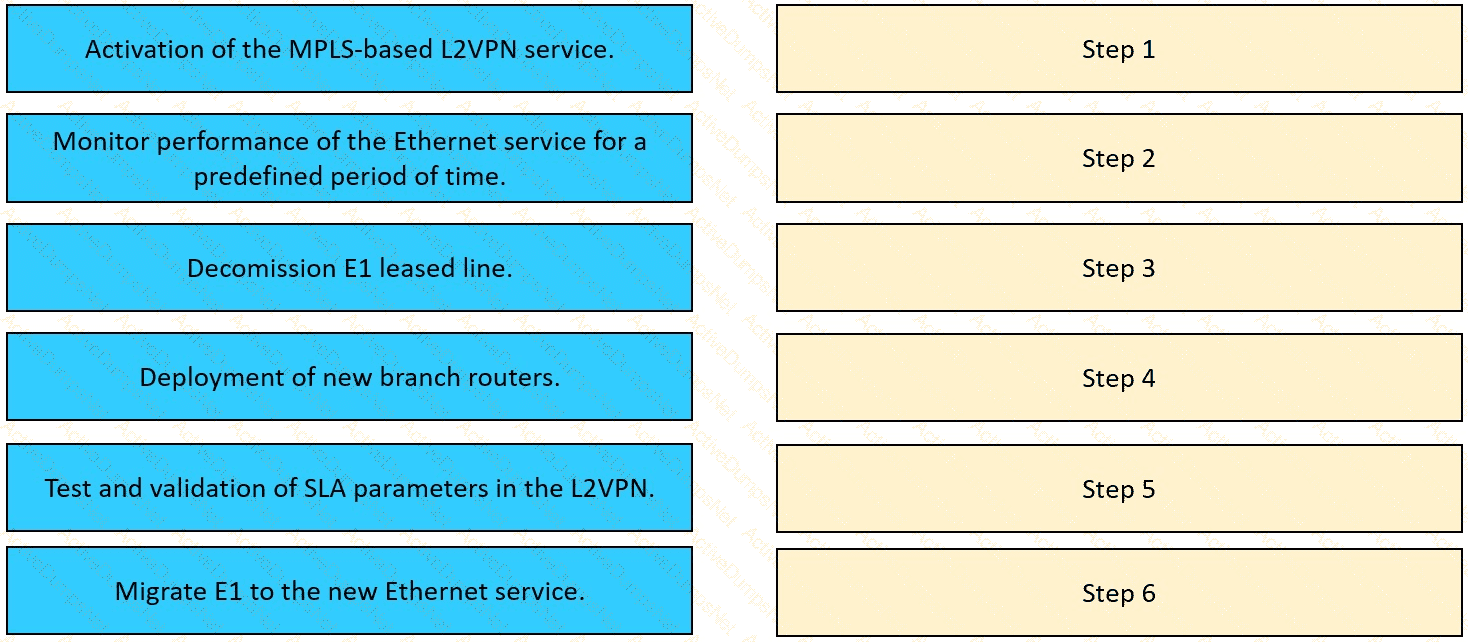
The network team in XYZ Corp wants to modernize their infrastructure and is evaluating an implementation and migration plan to allow integration MPLS-based, Layer 2 Ethernet services managed by a service provider to connect branches and remote offices. To decrease OpEx and improve
response times when network components fail, XYZ Corp decided to acquire and deploy new routers. The network currently is operated over E1 leased lines (2 Mbps) with a managed CE service provided by the telco.
Drag and drop the implementation steps from the left onto the corresponding targets on the right in the correct order.
As more links are added to the network, information and attributes related to the link is added to the control plane, meaning every link that gets added will slow down the convergence of the control plane by some measurable amount of time As a result when additional redundancy is built or added the MTTR will increase too Which risk increases along with the increased MTTR?
Company XYZ was not satisfied with the reconvergence time OSPF is taking BFD was implemented to try to reduce the reconvergence time, but the network is still experiencing delays when having to reconverge Which technology will improve the design?
monitoring solution, an organization wants to ensure they can collect feedback from network devices, particularly with a focus on being able to perform anomaly detection and automatically react to these events as they come m A key requirement is that the resources required to collect the data must be distributed Which data reporting approach is good fit for this use case?
Which development model is closely associated with Agile project management?
In a distributed cloud-native environment, calls to services and cloud resources can fail caused by unanticipated events that will require longer periods of time to resolve. These faults can range in severity from a partial loss of connectivity to the complete failure of a service. In these situations, it ' s pointless for an application to continually retry an operation that is unlikely to succeed. Which pattern can prevent an application from repeatedly trying to execute an operation that ' s likely to fail?
Following a series of security incidents, where hackers have been able to successfully gain access to the network with varying levels of access, the CTO of a large corporation has launched an initiative to ensure that there is end-to-end visibility inside the corporate network Which two technologies are relevant to include in the analysis that is started as part of the initiative? (Choose two.)
A bank recently had their security compromised during an initial key exchange between devices using a symmetric cryptography algorithm, and as a result the key was revealed/leaked. Going forward, they want to ensure that key exchanges are performed using asymmetric cryptography algorithms. Which algorithm offers the desired functionality?
Company XYZ network runs IPv4 and IPv6 and they want to Introduce a multidomain, multicast-based network. The new design should use a flavor of PIM that forwards traffic using SPT. Which technology meets this requirement?
A business wants to refresh its legacy Frame Relay WAN It currently has product specialists in each of its 200 branches but plans to reduce and consolidate resources. The goal is to have product specialists available via video link when customers visit the nationwide branch offices Which technology should be used to meet this objective?
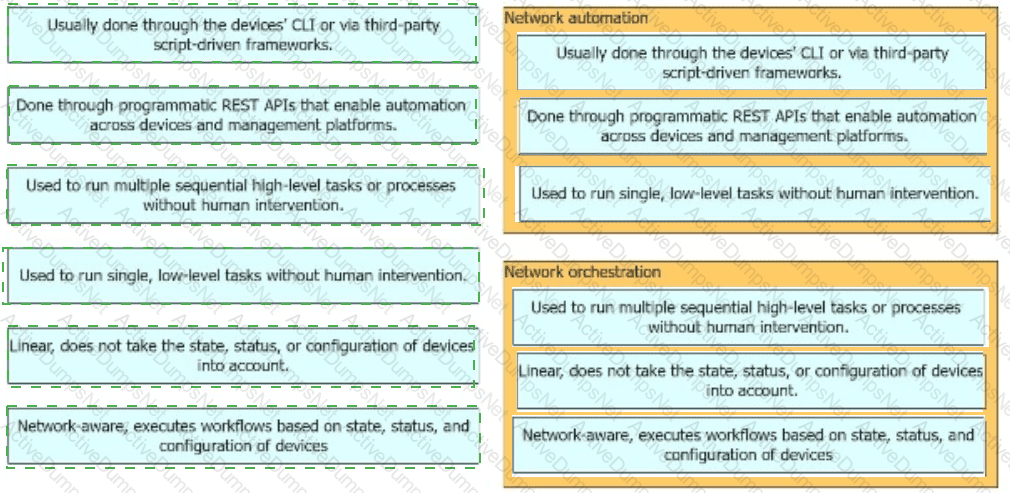
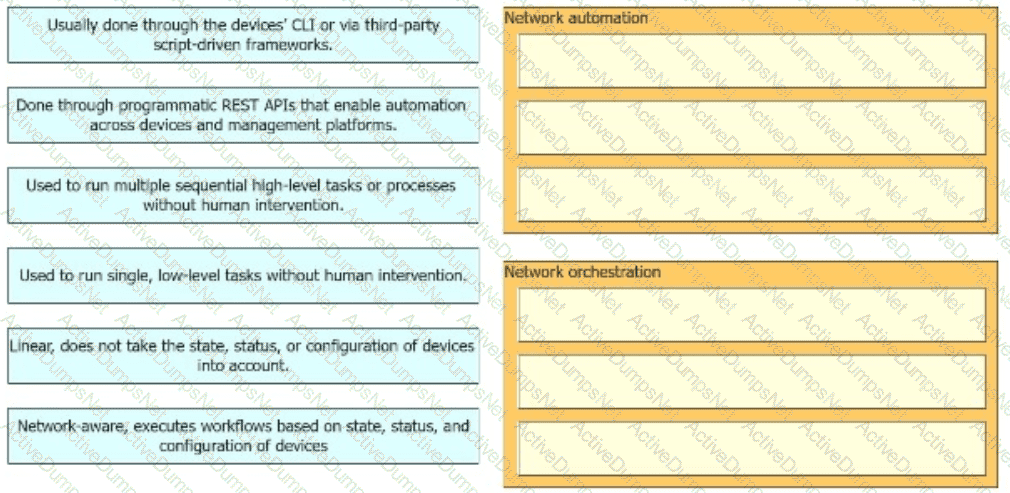
Drag and drop the high-level descriptions of network automation and network orchestration on the left to the corresponding category on the right in no particular order.
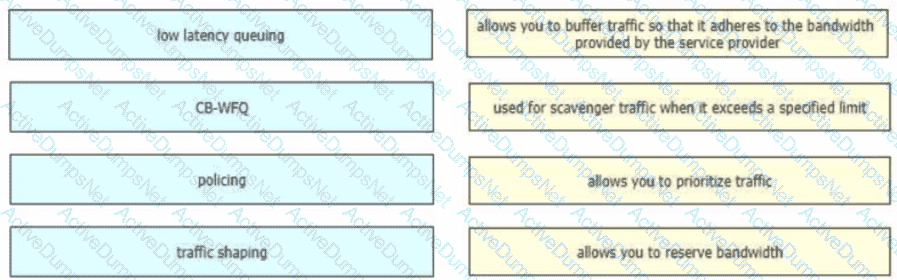
Drag and drop the QoS technologies from the left onto the correct capabilities on the right
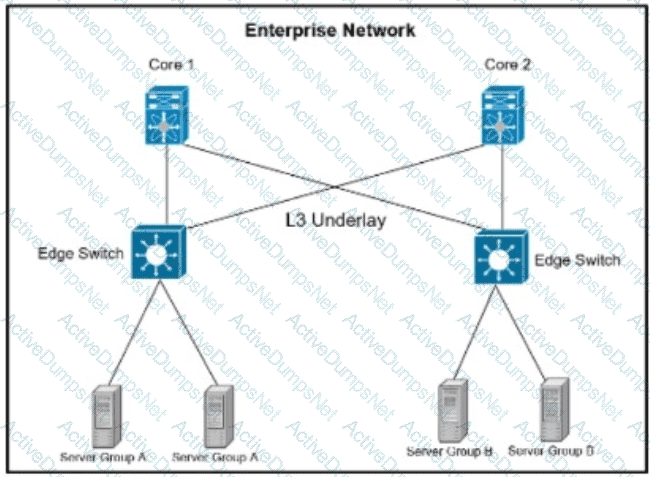
Refer to the exhibit. A company is running their data center based on VXLAN and BGP EVPN with stretched subnets for servers attaching to the edge devices being an important feature. The security team has defined a requirement where server group A must not be able to communicate with each other but is allowed to communicate with server group B. while servers in Group B must be able to communicate with all servers. Which scalable solution can be deployed to support these requirements?
Company XYZ wants to implement an IPS device to detect and block well-known attacks against their network They want a design solution where all packets that are forwarded to the network are checked against a signature database before being allowed through This check must be done with the minimum effect on performance Which design is recommended?
To provide network resilience organizations need to adopt a holistic approach that includes several key practices and technologies What are two effective ways to enhance network resilience by providing backup and alternative options to maintain network functionality?
In the wake of a security compromise incident where the internal networks were breached by an outside attacker at the perimeter of the infrastructure, an enterprise is now evaluating potential measures that can help protect against the same type of incident in the future. What are two design options that can be employed? (Choose two)
Compared to data plane traffic, control plane traffic is relatively small in volume, but these flows are critical to the overall functioning of the network infrastructure and to voice and video endpoint well. When designing a QoS policy for a network, which two actions for the network control service-class is recommended? (Choose two)
Which security architecture component offers streamlined security operations, ease of use, and visibility across all network security elements, independent of location or form factor?
What are two primary design constraints when a robust infrastructure solution is created? (Choose two.)
A company with an existing multivendor network is moving from 1 G dark fiber to an ISP virtual leased-line solution The company ' s internal security policy states that any traffic traversing a network that is not owned by the company must be encrypted What must be used to meet the requirements?
An enterprise SDWAN customer based in the US has several branches in Europe Currently branches use the HQ in the US to access both internal and external services over an MPLS arcuit The design team has been tasked to suggest a solution allowing branches to access their cloud-based office productivity tools and services directly Since all their applications and services are hosted in the cloud, the design team has also been asked to come up with a solution, so branches can connect to the cloud directly from the branch as well Which two cost-effective and optimized solutions can be suggested? (Choose two)
cloud onRamp (SaaS)
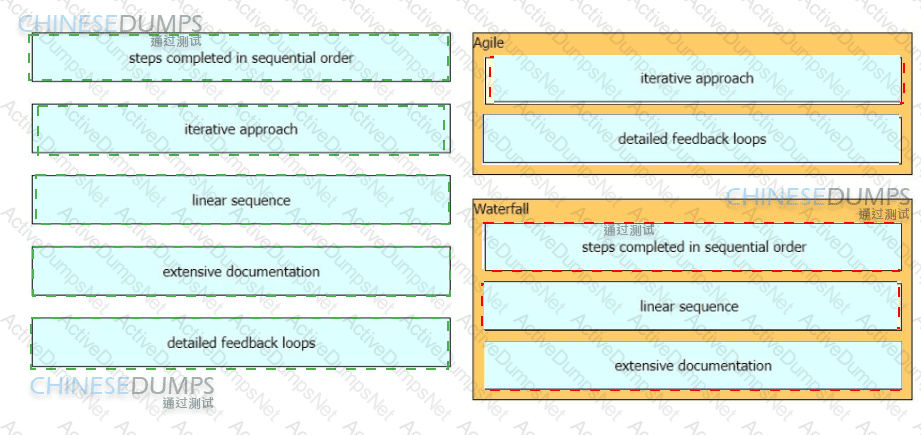
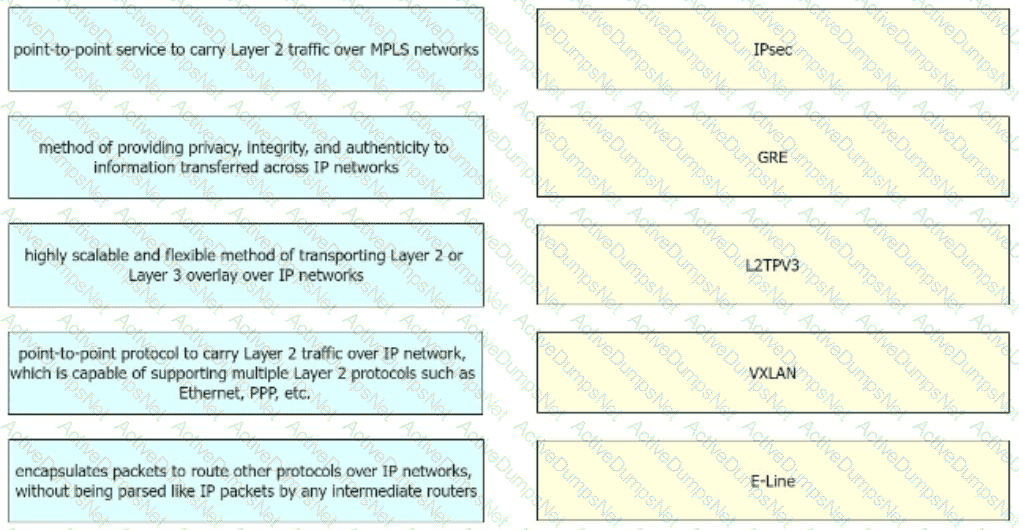
What are two advantages of the Agile project management methodology? (Choose two)
An architect receives a business requirement from a CTO that states the RTO and RPO for a new system should be as close as possible to zero. Which replication method and data center technology should be used?
risk is a major determining factor in whether a company chooses to go with a public cloud, a private, or a hybrid of both. what are two factors that impact the decision on which cloud service placement model to use? (choose two)
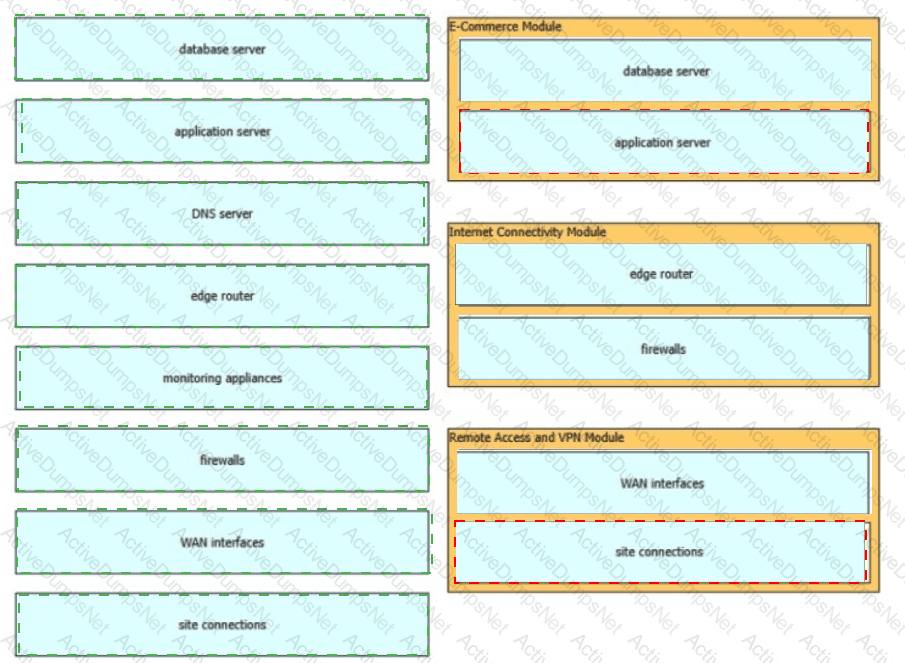
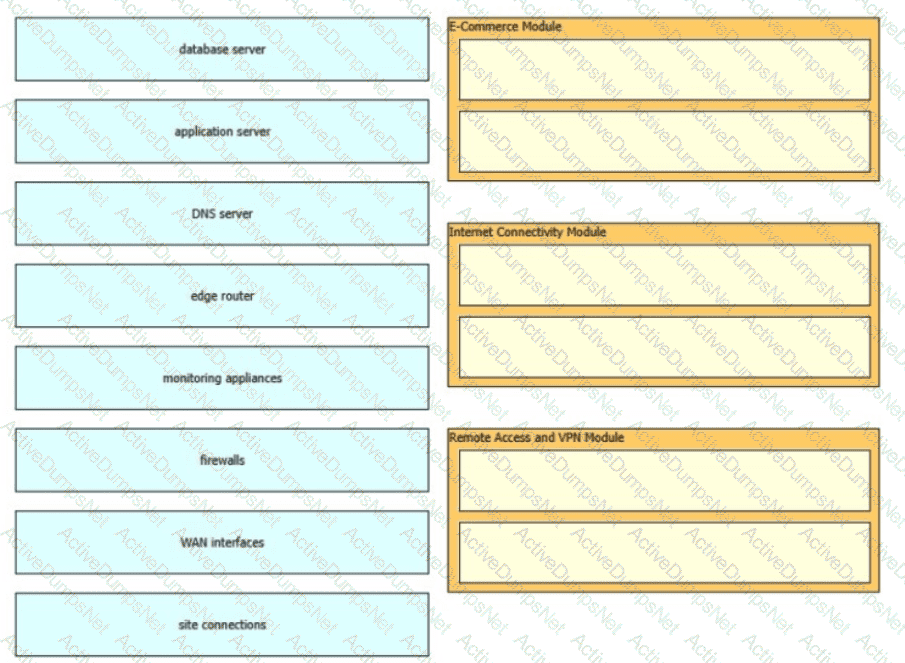
The Enterprise Edge infrastructure modules aggregate the connectivity from the various elements outside the campus—using various services and WAN technologies as needed typicaly provisioned from service providers and route the traffic into the Campus Core layer The Enterprise Edge modules perform security functions when enterprise resources connect across public networks and the internet Drag and drop the network device types from the left onto the corresponding modules on the right Not all options are used
A multinational enterprise integrates a cloud solution with these objectives
Achieve seamless connectivity across different countries and regions
Extend data center and private clouds into public clouds and provider-hosted clouds
What are two outcomes of deploying data centers and fabrics that interconnect different cloud networks? (Choose two)
Which two elements are key in strategic network design and planning?
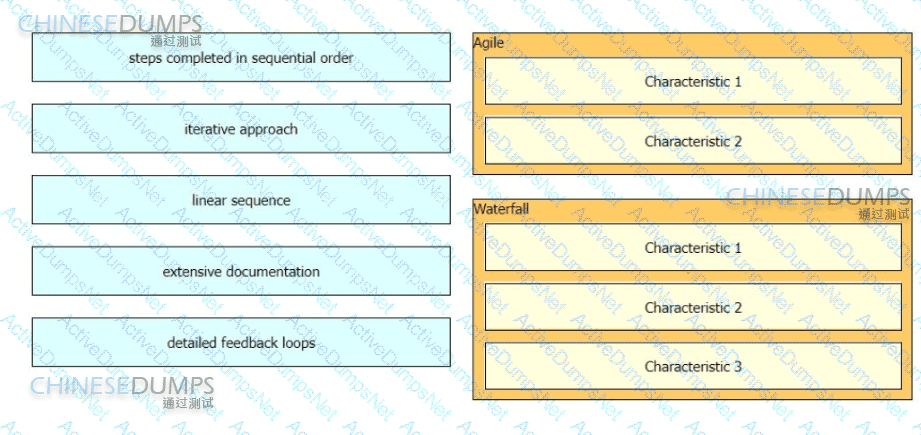
A consultant needs to explain different project management methodologies to a customer.
Drag and drop the characteristics from the left onto the corresponding methodologies on the right in no particular order.
Enterprise XYZ wants to implement fast convergence on their network and optimize timers for OSPF However they also want to prevent excess flooding of ISAs if there is a constantly flapping link on the network Which timers can help prevent excess flooding of LSAs for OSPF?
A multicast network is sing Bidirectional PIM. Which two combined actions achieve high availability so that two RPs within the same network can act in a redundant manner? (Choose two)
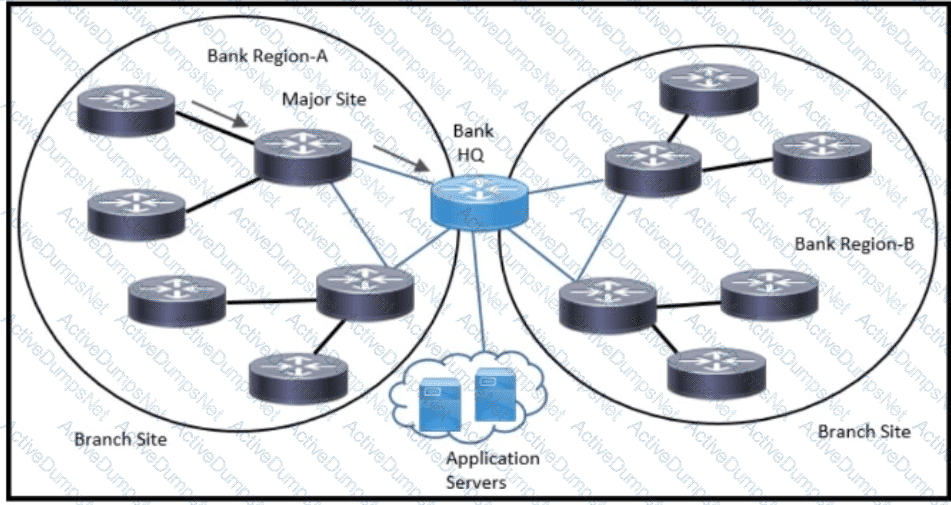
Refer to the exhibit. An architect has been tasked to design an ISIS solution for a medium-size financial customer. The resulting design must meet these requirements:
Which two ISIS design aspects must be included? (Choose two.)
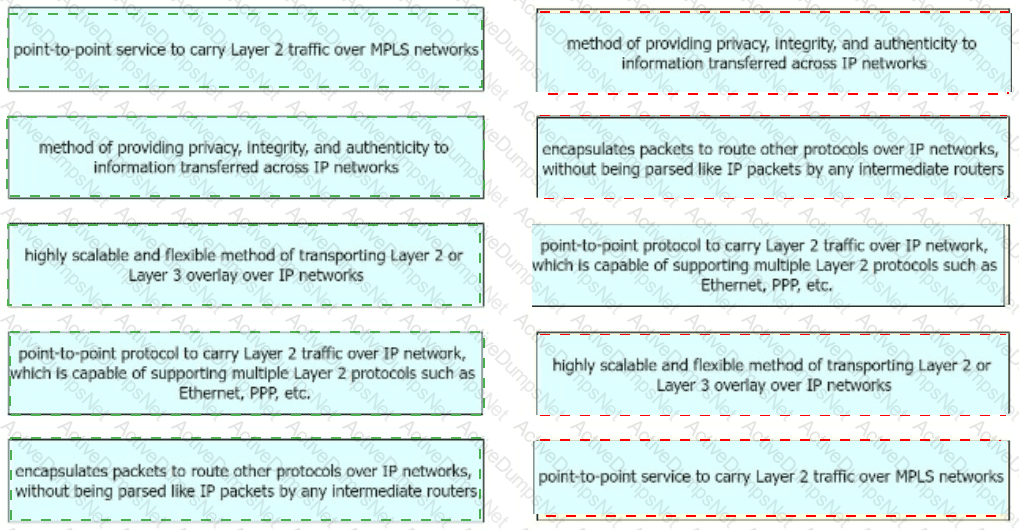
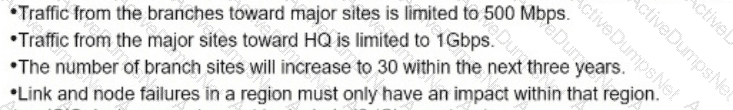
Drag and drop the right functional descriptions from the left onto the corresponding protocols on the right.
Refer to the table. A customer investigates connectivity options for a DCI between two production data centers. The solution must provide dual 10G connections between locations with no single points of failure for Day 1 operations. It must also include an option to scale for up to 20 resilient connections in the second year to accommodate isolated SAN over IP and isolated, dedicated replication IP circuits. All connectivity methods are duplex 10 Gbps. Which transport technology costs the least over two years, in the scenario?
Refer to the exhibit. This network is running legacy STP 802.1 d. Assuming " hello_timer " is fixed to 2 seconds, which parameters can be modified to speed up convergence times after single link/node failure?
Scalability is a desirable attribute of a network, system, or process Poor scalability can result in poor system performance, necessitating the reengineering or duplication of systems Load scalability is the ability of a system to perform gracefully as traffic increases Which two problems can occur due to poor load scalability design? (Choose two )
By monitoring the effects of the design variations, you can characterize the relative resilience of the design. Which method involves disturbing the network by removing an active interface and monitoring how the change is handled by the network?
Company XYZ has two routing domains in their network, EIGRP and OSPF. The company wants to provide full reachability between the two domains by implementing redistribution on a router running both protocols They need to design the redistribution in a way that the OSPF routers will see link costs added to external routes. How must the redistribution strategy be designed for this network?
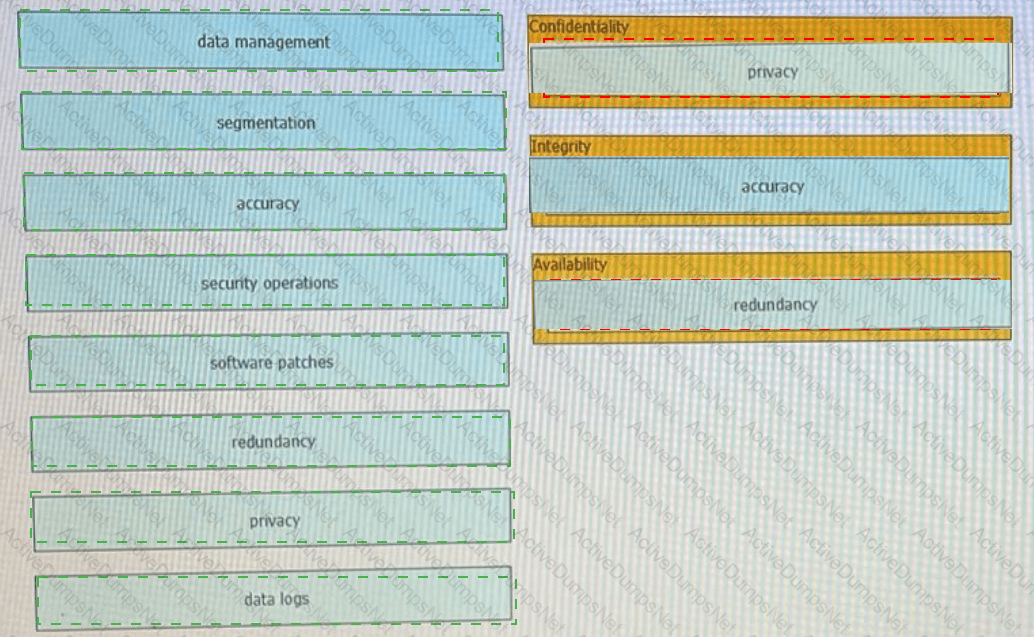
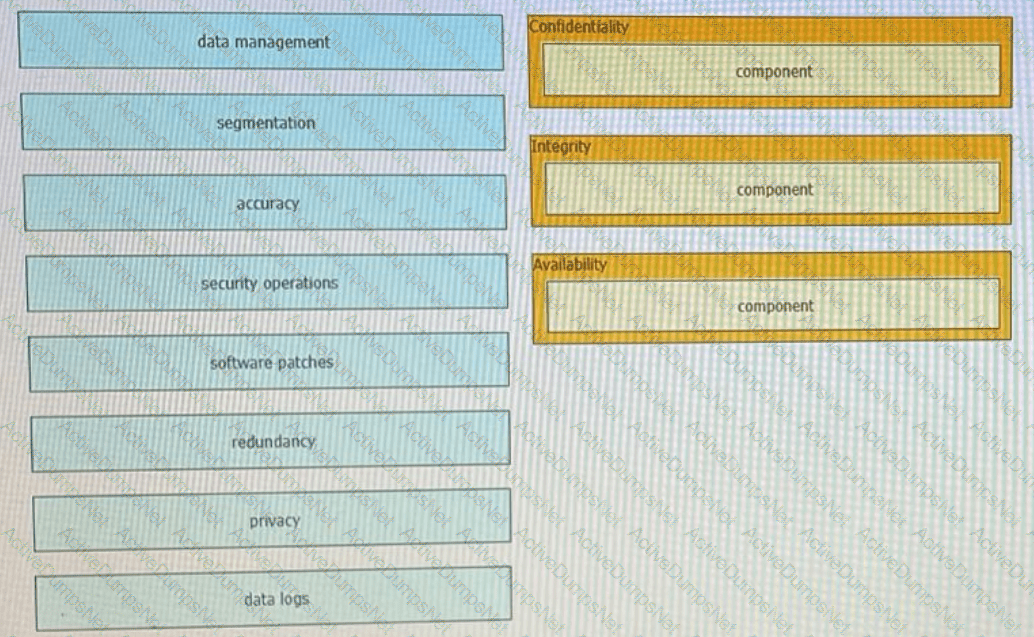
Drag t he components that are part of the CIA triad to the correct target on the right. Not all components are used.
Implementing a network automation architecture usually follows a phased approach that increases automation as the new technology and processes in the preceding phases are integrated and adopted. What provides a model that greatly simplifies the interaction with network devices?
A product manufacturing organization is integrating cloud services into their IT solution The IT team is working on the preparation phase of the implementation approach, which includes the Define Strategy step This step defines the scope of IT. the application, and the service. What is one topic that should be considered in the Define Strategy step?
Most security monitoring systems use a signature-based approach to detect threats. In which two instances are systems based on Network Behavior Anomaly Detection better than signature-based systems when it comes to detecting security threat vectors? (Choose two.)
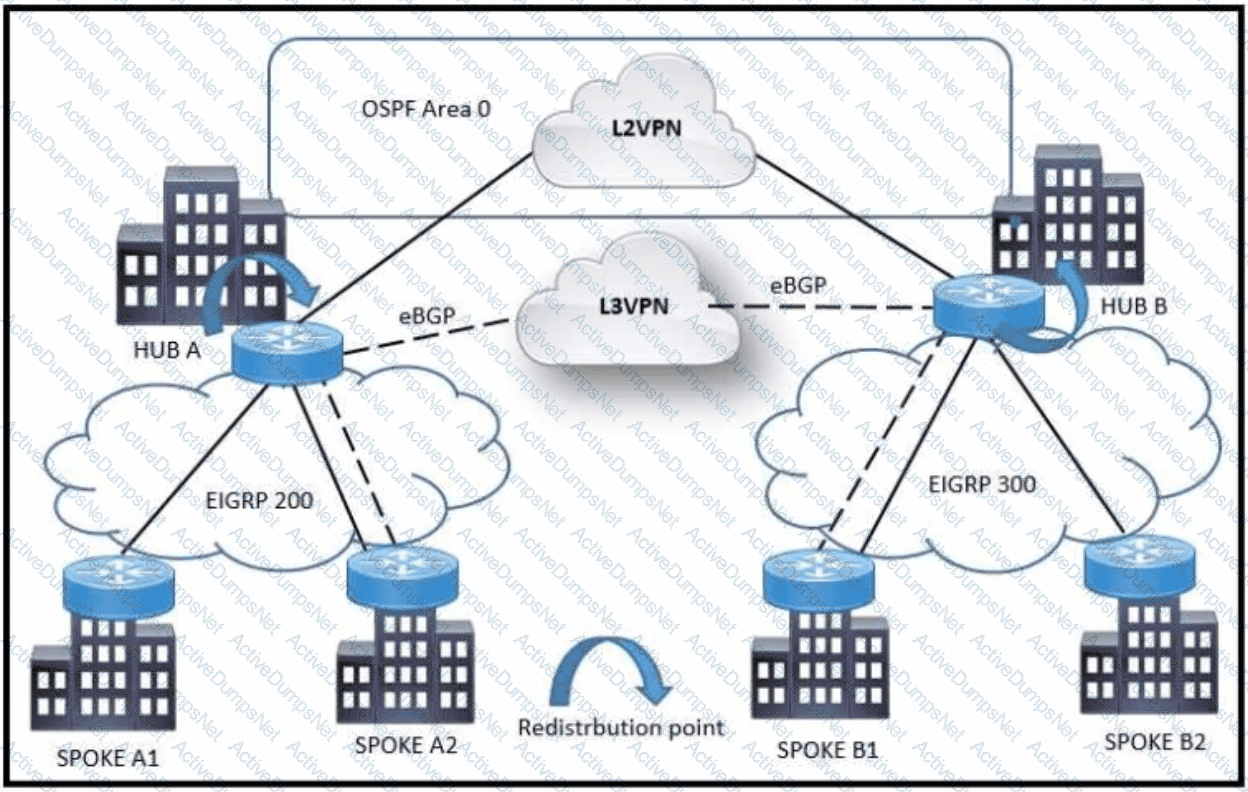
Refer to the exhibit A customer network design team is planning a migration from a legacy TDM-based L2VPN to an MPLS-based L3VPN Migration is planned in a phased approach:
•OSPF backbone Link between HUB A and HUB B sites to be migrated to eBGP
•Spoke A2 and Spoke B1 will be migrated to the L3VPN
Which solution design can be considered to avoid routing loops during backbone link migration
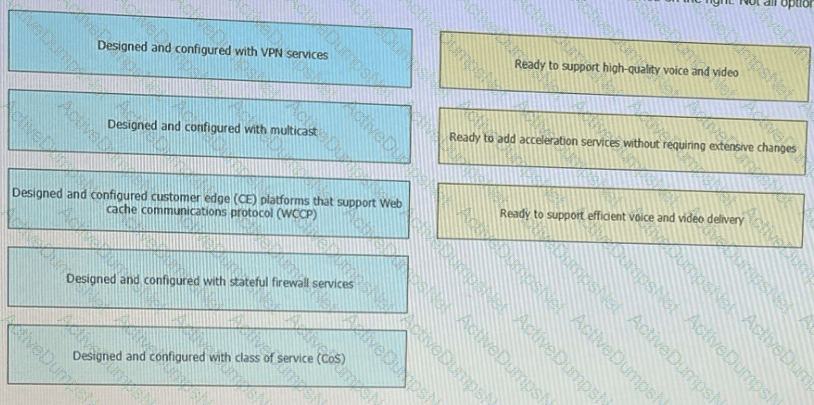
Flexibility, scalability, resiliency, and security are all chrematistics of a services-ready network An architecture featuring a modular design enables technologies and services to be added when the organization is ready to deploy. Drag and drop the design considerations on the left to the to type of service on the right Not all options are used
What is the most important operational driver when building a resilient and secure modular network design?
Software-defined networking architecture is used for cost-effective, adaptable, and easily manageable applications. In which two software-defined networks is SDN commonly used? (Choose two.)
A well-executed network design provides improved performance and efficiency, increased security, and reduced downtime and support costs Which feature helps to achieve resilience in the network?
Which purpose of a dynamically created tunnel interface on the design of IPv6 multicast services Is true?
Which two network design considerations improve the maximum link utilization? (Choose two)
Company XYZ Is running a redundant private WAN network using OSPF as the underlay protocol The current design accommodates for redundancy In the network, but it Is taking over 30 seconds for the network to reconverge upon failure Which technique can be Implemented In the design to detect such a failure in a subsecond?
As part of a design solution a consultant needs to describe the trade-offs between different SDN models Drag the characteristics on the left to the correct controller-based network designs on the right in no particular order.
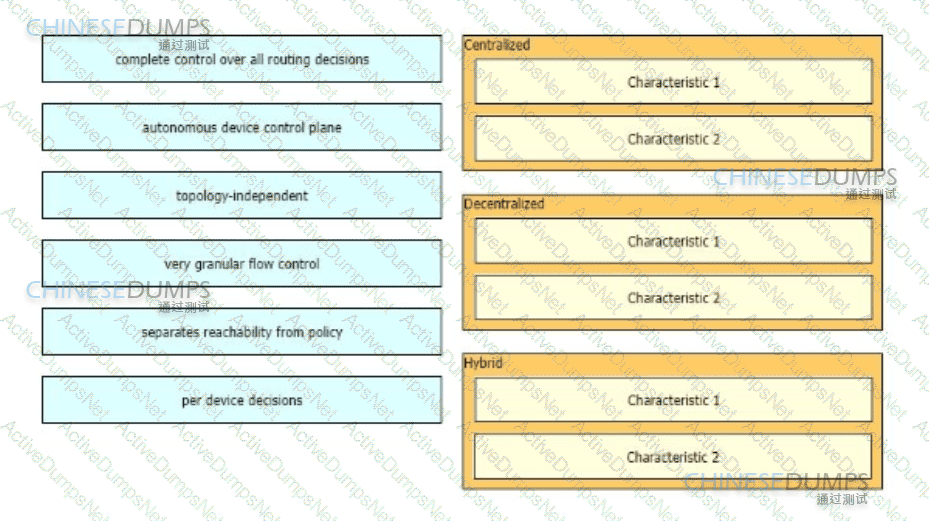
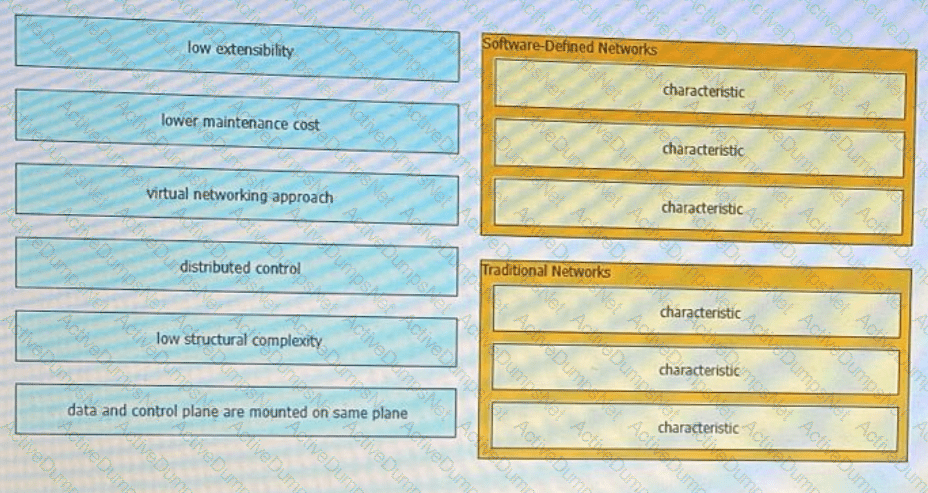
Software-defined network and traditional networks might appear the same to the end-user, but behind the scenes, each has unique sets of characteristics. Drag and drop these characteristic found on the left to the corresponding category on the right in no particular order?