Cisco 350-701 Implementing and Operating Cisco Security Core Technologies (SCOR 350-701) Exam Practice Test
Implementing and Operating Cisco Security Core Technologies (SCOR 350-701) Questions and Answers
Why is it important to implement MFA inside of an organization?
Which DevSecOps implementation process gives a weekly or daily update instead of monthly or quarterly in the applications?
Which metric is used by the monitoring agent to collect and output packet loss and jitter information?
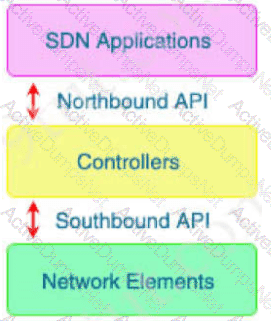
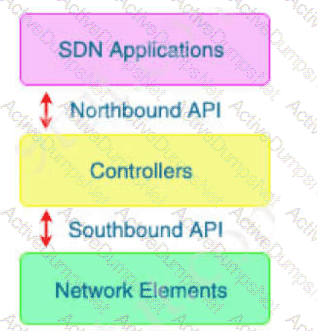
Which type of API is being used when a controller within a software-defined network architecture dynamically
makes configuration changes on switches within the network?
An engineer must modify a policy to block specific addresses using Cisco Umbrella. The policy is created already and is actively u: of the default policy elements. What else must be done to accomplish this task?
An engineer configures new features within the Cisco Umbrella dashboard and wants to identify and proxy traffic that is categorized as risky domains and may contain safe and malicious content. Which action accomplishes these objectives?
Which type of data does the Cisco Stealthwatch system collect and analyze from routers, switches, and firewalls?
What are two DDoS attack categories? (Choose two)
Why should organizations migrate to an MFA strategy for authentication?
Which Cisco DNA Center RESTful PNP API adds and claims a device into a workflow?
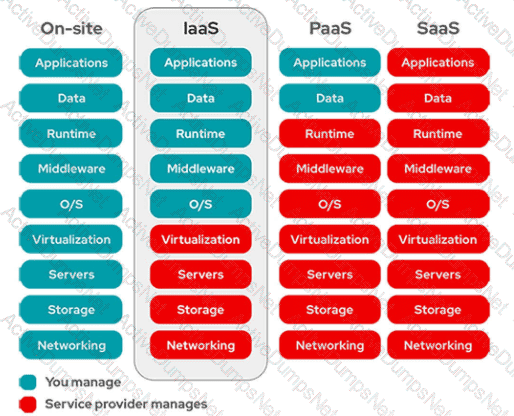
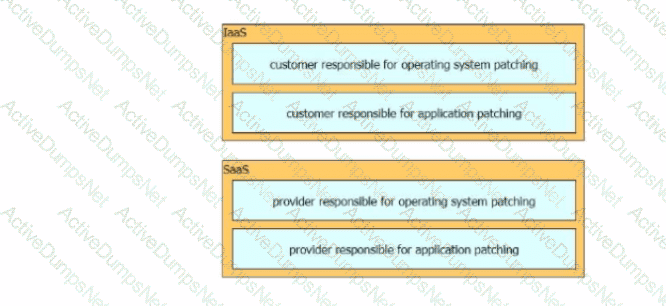
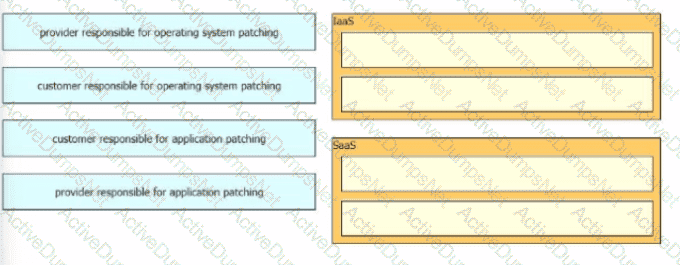
In which cloud services model is the customer responsible for scanning for and mitigation of application vulnerabilities?
In which two ways does a system administrator send web traffic transparently to the Web Security Appliance?
(Choose two)
Which two request methods of REST API are valid on the Cisco ASA Platform? (Choose two.)
Which two prevention techniques are used to mitigate SQL injection attacks? (Choose two)
Which two Cisco Umbrella security categories are used to prevent command-and-control callbacks on port 53 and protect users from being tricked into providing confidential information? (Choose two.)
Which two criteria must a certificate meet before the WSA uses it to decrypt application traffic? (Choose two.)
How is a cross-site scripting attack executed?
What is a characteristic of an EDR solution and not of an EPP solution?
Which system performs compliance checks and remote wiping?
A network administrator configures Dynamic ARP Inspection on a switch. After Dynamic ARP Inspection is applied, all users on that switch are unable to communicate with any destination. The network administrator checks the interface status of all interfaces, and there is no err-disabled interface. What is causing this problem?
Which two preventive measures are used to control cross-site scripting? (Choose two)
What are two ways that Cisco Container Platform provides value to customers who utilize cloud service providers? (Choose two.)
Why is it important to have logical security controls on endpoints even though the users are trained to spot security threats and the network devices already help prevent them?
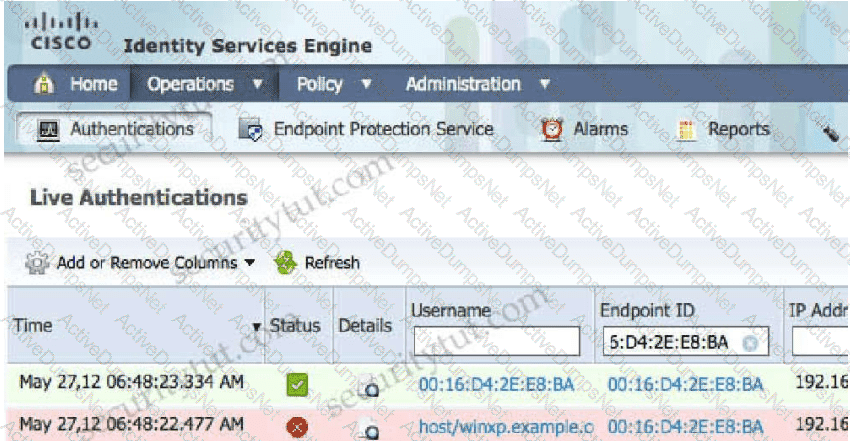
Refer to the exhibit.
What will happen when this Python script is run?
Which statement describes a serverless application?
An email administrator is setting up a new Cisco ESA. The administrator wants to enable the blocking of greymail for the end user. Which feature must the administrator enable first?
Which deployment model is the most secure when considering risks to cloud adoption?
What features does Cisco FTDv provide over ASAv?
Which two functions does the Cisco Advanced Phishing Protection solution perform in trying to protect from phishing attacks? (Choose two.)
What is the most commonly used protocol for network telemetry?
When a next-generation endpoint security solution is selected for a company, what are two key
deliverables that help justify the implementation? (Choose two.)
What are two recommended approaches to stop DNS tunneling for data exfiltration and command and control call backs? (Choose two.)
Which API method and required attribute are used to add a device into Cisco DNA Center with the native API?
An organization is receiving SPAM emails from a known malicious domain. What must be configured in order to
prevent the session during the initial TCP communication?
Which technology provides the benefit of Layer 3 through Layer 7 innovative deep packet inspection,
enabling the platform to identify and output various applications within the network traffic flows?
Which two are valid suppression types on a Cisco Next Generation Intrusion Prevention System? (Choose two)
What is the purpose of a denial-of-service attack?
Which two activities can be done using Cisco DNA Center? (Choose two)
What Cisco command shows you the status of an 802.1X connection on interface gi0/1?
How many interfaces per bridge group does an ASA bridge group deployment support?
Which attack gives unauthorized access to files on the web server?
Which attack is preventable by Cisco ESA but not by the Cisco WSA?
What are two advantages of using Cisco Any connect over DMVPN? (Choose two)
Refer to the exhibit.
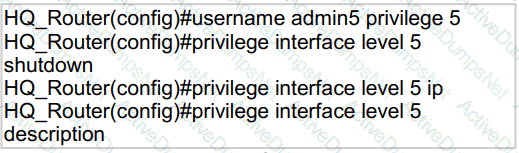
A network administrator configures command authorization for the admin5 user. What is the admin5 user able to do on HQ_Router after this configuration?
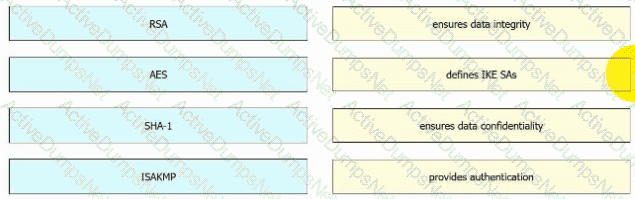
Drag and drop the VPN functions from the left onto the descriptions on the right.
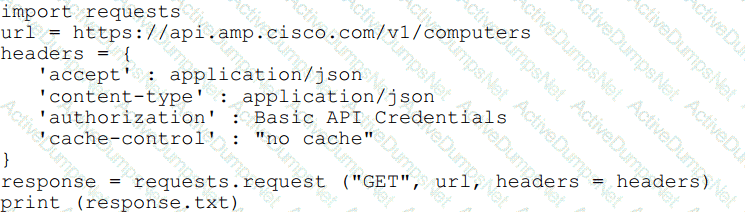
Refer to the exhibit.
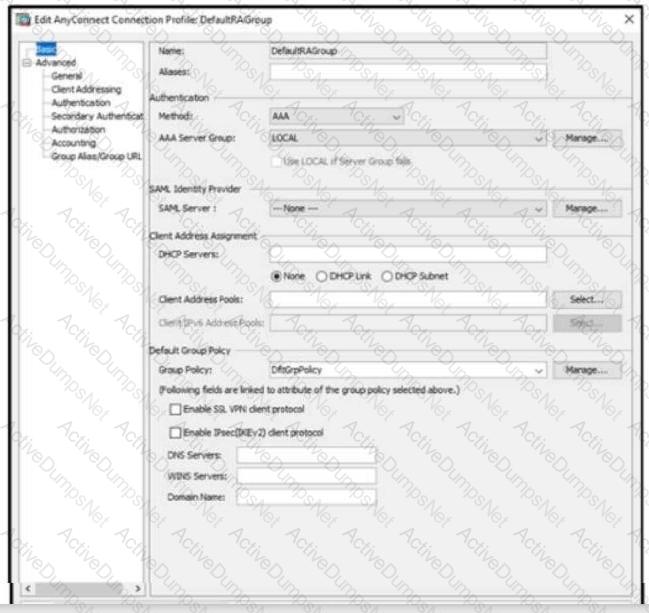
When configuring a remote access VPN solution terminating on the Cisco ASA, an administrator would like to utilize an external token authentication mechanism in conjunction with AAA authentication using machine
certificates. Which configuration item must be modified to allow this?
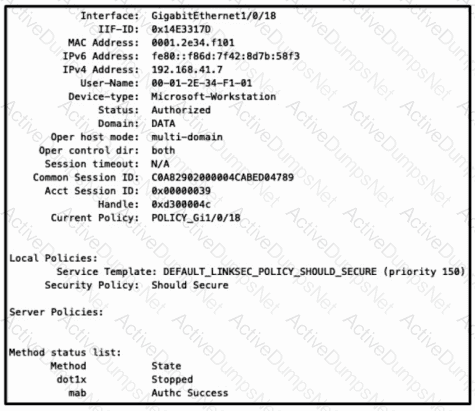
Refer to the exhibit. Which configuration item makes it possible to have the AAA session on the network?
An engineer needs a solution for TACACS+ authentication and authorization for device administration.
The engineer also wants to enhance wired and wireless network security by requiring users and endpoints to
use 802.1X, MAB, or WebAuth. Which product meets all of these requirements?
What is a required prerequisite to enable malware file scanning for the Secure Internet Gateway?
A university policy must allow open access to resources on the Internet for research, but internal workstations are exposed to malware. Which Cisco AMP feature allows the engineering team to determine whether a file is installed on a selected few workstations?
Refer to the exhibit.
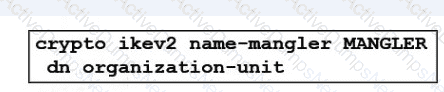
An engineer is implementing a certificate based VPN. What is the result of the existing configuration?
Which two parameters are used to prevent a data breach in the cloud? (Choose two.)
A network engineer has entered the snmp-server user andy myv3 auth sha cisco priv aes 256
cisc0380739941 command and needs to send SNMP information to a host at 10.255.254.1. Which command achieves this goal?
An organization deploys multiple Cisco FTD appliances and wants to manage them using one centralized
solution. The organization does not have a local VM but does have existing Cisco ASAs that must migrate over
to Cisco FTDs. Which solution meets the needs of the organization?
How is DNS tunneling used to exfiltrate data out of a corporate network?
Which feature of Cisco ASA allows VPN users to be postured against Cisco ISE without requiring an inline
posture node?
Which Cisco security solution determines if an endpoint has the latest OS updates and patches installed on the system?
The Cisco ASA must support TLS proxy for encrypted Cisco Unified Communications traffic. Where must the
ASA be added on the Cisco UC Manager platform?
What is an attribute of Cisco Talos?
Which characteristic is unique to a Cisco WSAv as compared to a physical appliance?
What is the primary role of the Cisco Email Security Appliance?
Which two configurations must be made on Cisco ISE and on Cisco TrustSec devices to force a session to be adjusted after a policy change is made? (Choose two)
What is the function of the Context Directory Agent?
What are two ways a network administrator transparently identifies users using Active Directory on the Cisco WSA? (Choose two.)
What must be configured on Cisco Secure Endpoint to create a custom detection tile list to detect and quarantine future files?
How does a cloud access security broker function?
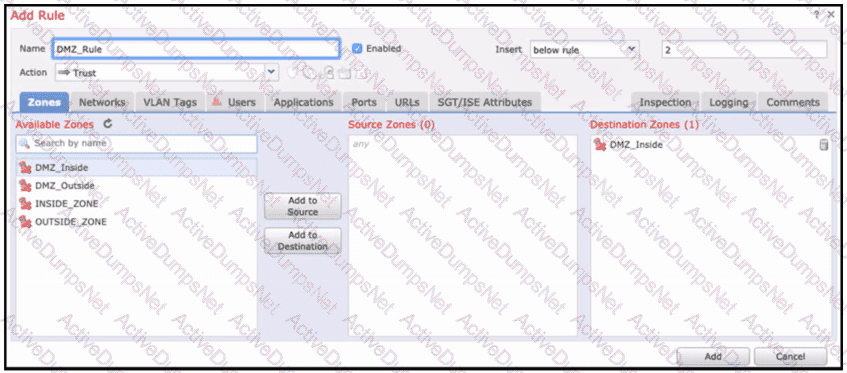
Refer to the exhibit. When configuring this access control rule in Cisco FMC, what happens with the traffic destined to the DMZ_inside zone once the configuration is deployed?
A network engineer must monitor user and device behavior within the on-premises network. This data must be sent to the Cisco Stealthwatch Cloud analytics platform for analysis. What must be done to meet this
requirement using the Ubuntu-based VM appliance deployed in a VMware-based hypervisor?
Refer to the exhibit.
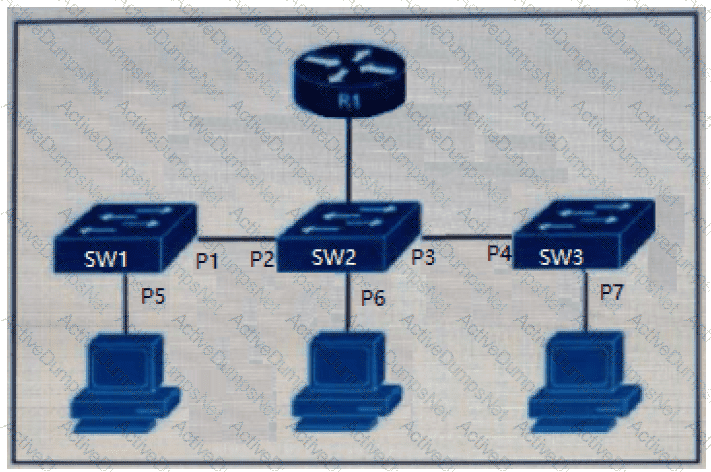
The DHCP snooping database resides on router R1, and dynamic ARP inspection is configured only on switch SW2. Which ports must be configured as untrusted so that dynamic ARP inspection operates normally?
A Cisco Firepower administrator needs to configure a rule to allow a new application that has never been seen
on the network. Which two actions should be selected to allow the traffic to pass without inspection? (Choose
two)
Which statement about the configuration of Cisco ASA NetFlow v9 Secure Event Logging is true?
An administrator is adding a new Cisco ISE node to an existing deployment. What must be done to ensure that the addition of the node will be successful when inputting the FQDN?
What is a benefit of using a multifactor authentication strategy?
An organization is trying to improve their Defense in Depth by blocking malicious destinations prior to a
connection being established. The solution must be able to block certain applications from being used within the network. Which product should be used to accomplish this goal?
A network engineer is configuring DMVPN and entered the crypto isakmp key cisc0380739941 address 0.0.0.0 command on hostA. The tunnel is not being established to hostB. What action is needed to authenticate the VPN?
What is a description of microsegmentation?
An organization is trying to implement micro-segmentation on the network and wants to be able to gain visibility on the applications within the network. The solution must be able to maintain and force compliance. Which product should be used to meet these requirements?
When a Cisco WSA checks a web request, what occurs if it is unable to match a user-defined policy?
Which security product enables administrators to deploy Kubernetes clusters in air-gapped sites without needing Internet access?
What is a difference between an XSS attack and an SQL injection attack?
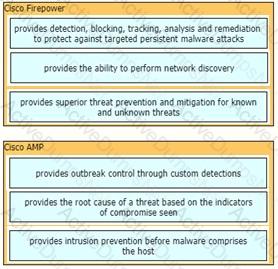
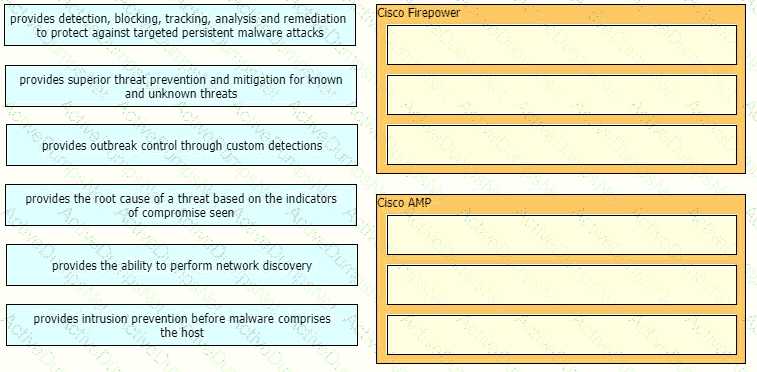
Drag and drop the capabilities of Cisco Firepower versus Cisco AMP from the left into the appropriate category on the right.
Which type of DNS abuse exchanges data between two computers even when there is no direct connection?
Which cloud model is a collaborative effort where infrastructure is shared and jointly accessed by several organizations from a specific group?
What is the benefit of installing Cisco AMP for Endpoints on a network?
A Cisco Secure Email Gateway network administrator has been tasked to use a newly installed service to help create policy based on the reputation verdict. During testing, it is discovered that the Secure Email Gateway is not dropping files that have an undetermined verdict. What is causing this issue?
Which two descriptions of AES encryption are true? (Choose two)
An engineer is implementing DHCP security mechanisms and needs the ability to add additional attributes to profiles that are created within Cisco ISE Which action accomplishes this task?
Which flaw does an attacker leverage when exploiting SQL injection vulnerabilities?
A network engineer is tasked with configuring a Cisco ISE server to implement external authentication against Active Directory. What must be considered about the authentication requirements? (Choose two.)
A Cisco FTD engineer is creating a new IKEv2 policy called s2s00123456789 for their organization to allow for additional protocols to terminate network devices with. They currently only have one policy established and need the new policy to be a backup in case some devices cannot support the stronger algorithms listed in the primary policy. What should be done in order to support this?
Which method must be used to connect Cisco Secure Workload to external orchestrators at a client site when the client does not allow incoming connections?
What is a difference between GETVPN and IPsec?
Refer to the exhibit.
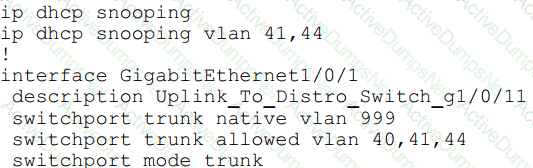
An organization is using DHCP Snooping within their network. A user on VLAN 41 on a new switch is
complaining that an IP address is not being obtained. Which command should be configured on the switch
interface in order to provide the user with network connectivity?
Which two aspects of the cloud PaaS model are managed by the customer but not the provider? (Choose two)
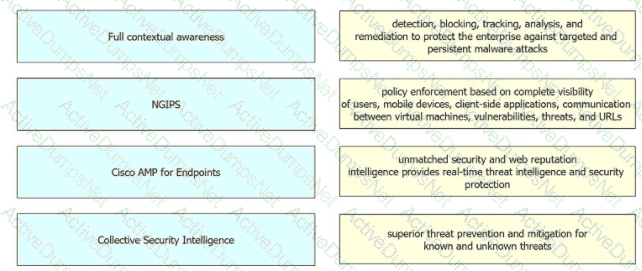
Drag and drop the security solutions from the left onto the benefits they provide on the right.
An engineer is configuring device-hardening on a router in order to prevent credentials from being seen
if the router configuration was compromised. Which command should be used?
An engineer is configuring Cisco Umbrella and has an identity that references two different policies. Which action ensures that the policy that the identity must use takes precedence over the second one?
Which telemetry data captures variations seen within the flow, such as the packets TTL, IP/TCP flags, and payload length?
What is a benefit of an endpoint patch management strategy?
What are two functionalities of SDN Northbound APIs? (Choose two.)
Which CoA response code is sent if an authorization state is changed successfully on a Cisco IOS device?
Which cloud service offering allows customers to access a web application that is being hosted, managed, and maintained by a cloud service provider?
After deploying a Cisco ESA on your network, you notice that some messages fail to reach their destinations.
Which task can you perform to determine where each message was lost?
An engineer needs to configure a Cisco Secure Email Gateway (SEG) to prompt users to enter multiple forms of identification before gaining access to the SEG. The SEG must also join a cluster using the preshared key of cisc421555367. What steps must be taken to support this?
Which technology limits communication between nodes on the same network segment to individual applications?
What does endpoint isolation in Cisco AMP for Endpoints security protect from?
Refer to the exhibit.
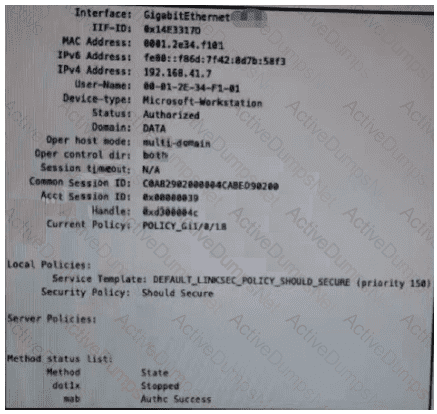
Which configuration item makes it possible to have the AAA session on the network?
An engineer must configure Cisco AMP for Endpoints so that it contains a list of files that should not be executed by users. These files must not be quarantined. Which action meets this configuration requirement?
Which feature is configured for managed devices in the device platform settings of the Firepower Management
Center?
An organization wants to secure data in a cloud environment. Its security model requires that all users be
authenticated and authorized. Security configuration and posture must be continuously validated before access is granted or maintained to applications and data. There is also a need to allow certain application traffic and deny all other traffic by default. Which technology must be used to implement these requirements?
An organization recently installed a Cisco Secure Web Appliance and would like to take advantage of the AVC engine to allow the organization to create a policy to control application-specific activity. After enabling the AVC engine, what must be done to implement this?
A hacker initiated a social engineering attack and stole username and passwords of some users within a company. Which product should be used as a solution to this problem?
Which attack is commonly associated with C and C++ programming languages?
Due to a traffic storm on the network, two interfaces were error-disabled, and both interfaces sent SNMP traps.
Which two actions must be taken to ensure that interfaces are put back into service? (Choose two)
In which type of attack does the attacker insert their machine between two hosts that are communicating with each other?
Which solution is made from a collection of secure development practices and guidelines that developers must follow to build secure applications?
Which two characteristics of messenger protocols make data exfiltration difficult to detect and prevent?
(Choose two)
What does Cisco AMP for Endpoints use to help an organization detect different families of malware?
Refer to the exhibit.
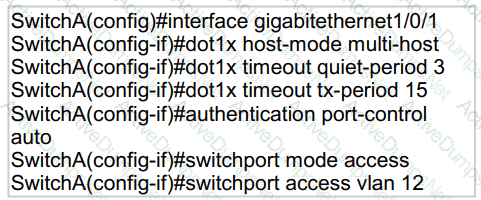
An engineer configured wired 802.1x on the network and is unable to get a laptop to authenticate. Which port configuration is missing?
Which technology enables integration between Cisco ISE and other platforms to gather and share
network and vulnerability data and SIEM and location information?
Which solution is more secure than the traditional use of a username and password and encompasses at least two of the methods of authentication?
In which two customer environments is the Cisco Secure Web Appliance Virtual connector traffic direction method selected? (Choose two.)
Refer to the exhibit.
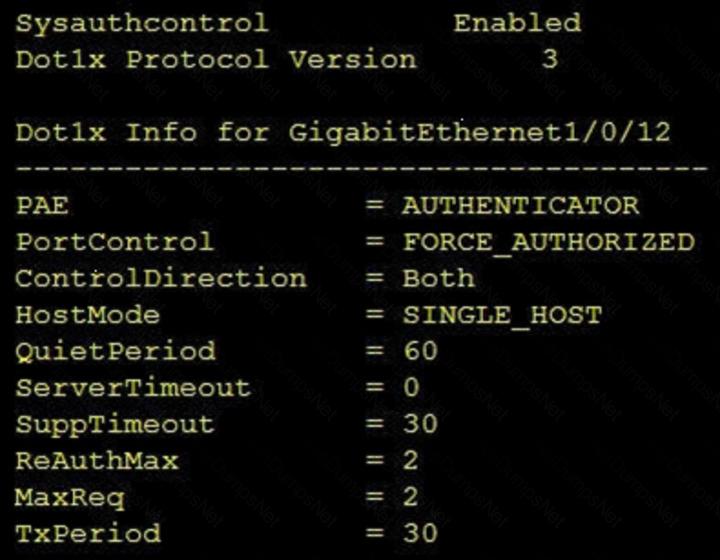
Which command was used to display this output?
In which scenario is endpoint-based security the solution?
A Cisco ESA administrator has been tasked with configuring the Cisco ESA to ensure there are no viruses before quarantined emails are delivered. In addition, delivery of mail from known bad mail servers must be prevented. Which two actions must be taken in order to meet these requirements? (Choose two)
Which form of attack is launched using botnets?
What is provided by the Secure Hash Algorithm in a VPN?
Which capability is provided by application visibility and control?
Which two features of Cisco DNA Center are used in a Software Defined Network solution? (Choose two)
Which ID store requires that a shadow user be created on Cisco ISE for the admin login to work?
An engineer is configuring their router to send NetfFow data to Stealthwatch which has an IP address of 1 1 11 using the flow record Stea!thwatch406397954 command Which additional command is required to complete the flow record?
On Cisco Firepower Management Center, which policy is used to collect health modules alerts from managed
devices?
Refer to the exhibit.
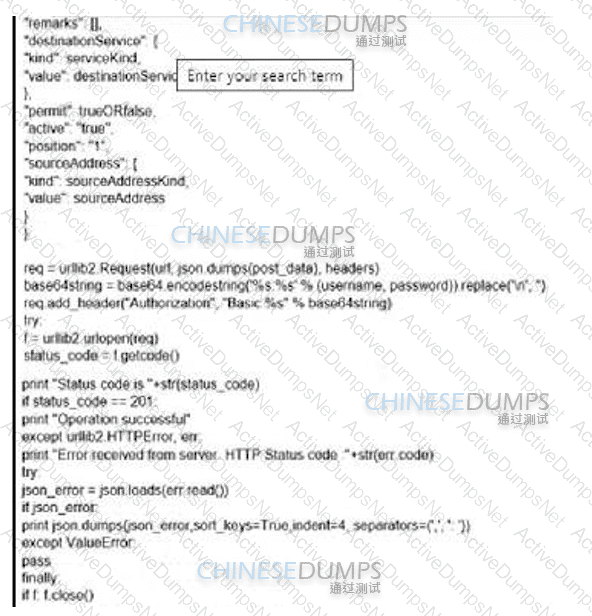
What is the function of the Python script code snippet for the Cisco ASA REST API?
What is an advantage of network telemetry over SNMP pulls?
A network engineer is deciding whether to use stateful or stateless failover when configuring two ASAs for high availability. What is the connection status in both cases?
Which type of protection encrypts RSA keys when they are exported and imported?
Which two fields are defined in the NetFlow flow? (Choose two)
An organization is implementing URL blocking using Cisco Umbrella. The users are able to go to some sites
but other sites are not accessible due to an error. Why is the error occurring?
Which security solution uses NetFlow to provide visibility across the network, data center, branch offices, and cloud?
An organization has a Cisco ESA set up with policies and would like to customize the action assigned for
violations. The organization wants a copy of the message to be delivered with a message added to flag it as a
DLP violation. Which actions must be performed in order to provide this capability?
Which factor must be considered when choosing the on-premise solution over the cloud-based one?
Drag and drop the VPN functions from the left onto the description on the right.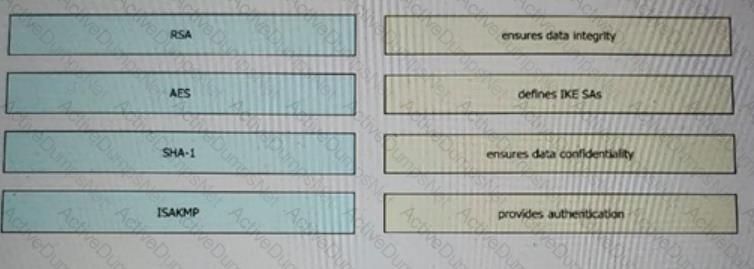
A web hosting company must upgrade its older, unsupported on-premises servers. The company wants a cloud solution in which the cloud provider is responsible for:
Server patching
Application maintenance
Data center security
Disaster recovery
Which type of cloud meets the requirements?
An engineer recently completed the system setup on a Cisco WSA Which URL information does the system send to SensorBase Network servers?
Which command enables 802.1X globally on a Cisco switch?
What limits communication between applications or containers on the same node?
What is an advantage of the Cisco Umbrella roaming client?
Which method is used to deploy certificates and configure the supplicant on mobile devices to gain access to
network resources?
Which benefit does endpoint security provide the overall security posture of an organization?
Which RADIUS feature provides a mechanism to change the AAA attributes of a session after it is
authenticated?
A network engineer is deciding whether to use stateful or stateless failover when configuring two Cisco ASAs for high availability. What is the connection status in both cases?
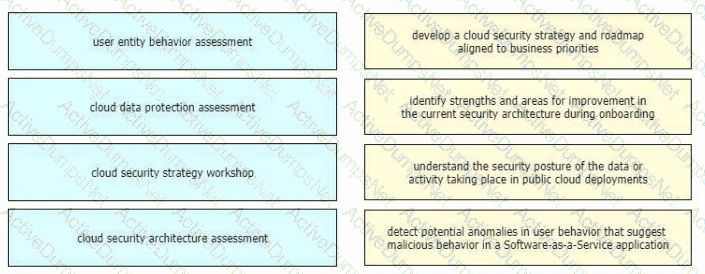
Drag and drop the cloud security assessment components from the left onto the definitions on the right.
An engineer must implement a file transfer solution between a company's data center and branches. The company has numerous servers hosted in a hybrid cloud implementation. The file transfer protocol must support authentication, protect the data against unauthorized access, and ensure that users cannot list directories or remove files remotely. Which protocol must be used?
DoS attacks are categorized as what?
A network engineer must configure a Cisco ESA to prompt users to enter two forms of information before gaining access The Cisco ESA must also join a cluster machine using preshared keys What must be configured to meet these requirements?
An engineer is trying to decide whether to use Cisco Umbrella, Cisco CloudLock, Cisco Stealthwatch, or Cisco AppDynamics Cloud Monitoring for visibility into data transfers as well as protection against data exfiltration Which solution best meets these requirements?
Which Cisco cloud security software centrally manages policies on multiple platforms such as Cisco ASA, Cisco Firepower, Cisco Meraki, and AWS?
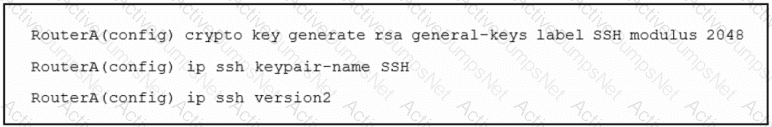
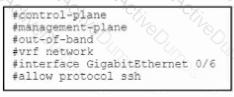
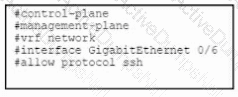
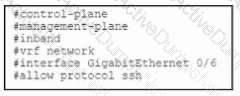
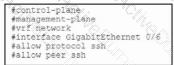
Refer to the exhibit. An engineer must enable secure SSH protocols and enters this configuration. What are two results of running this set of commands on a Cisco router? (Choose two.)
A company has 5000 Windows users on its campus. Which two precautions should IT take to prevent WannaCry ransomware from spreading to all clients? (Choose two.)
Which cloud service model offers an environment for cloud consumers to develop and deploy applications
without needing to manage or maintain the underlying cloud infrastructure?
An administrator is implementing management plane protection and must configure an interface on a Cisco router to only terminate management packets that are destined for the router. Which set of IOS commands must be used to complete the implementation?
A company identified a phishing vulnerability during a pentest What are two ways the company can protect employees from the attack? (Choose two.)
What is a function of Cisco AMP for Endpoints?
What are two functions of TAXII in threat intelligence sharing? (Choose two.)
With which components does a southbound API within a software-defined network architecture communicate?
An organization is using Cisco Firepower and Cisco Meraki MX for network security and needs to centrally
manage cloud policies across these platforms. Which software should be used to accomplish this goal?
An organization has two systems in their DMZ that have an unencrypted link between them for communication.
The organization does not have a defined password policy and uses several default accounts on the systems.
The application used on those systems also have not gone through stringent code reviews. Which vulnerability
would help an attacker brute force their way into the systems?
Which feature is supported when deploying Cisco ASAv within AWS public cloud?
What are two features of NetFlow flow monitoring? (Choose two)
Which function is included when Cisco AMP is added to web security?
What are two workloaded security models? (Choose two)
A network engineer must migrate a Cisco WSA virtual appliance from one physical host to another physical host by using VMware vMotion. What is a requirement for both physical hosts?
What is a function of 3DES in reference to cryptography?
An administrator configures new authorization policies within Cisco ISE and has difficulty profiling the devices. Attributes for the new Cisco IP phones that are profiled based on the RADIUS authentication are seen however the attributes for CDP or DHCP are not. What should the administrator do to address this issue?
An engineer is configuring 802.1X authentication on Cisco switches in the network and is using CoA as a mechanism. Which port on the firewall must be opened to allow the CoA traffic to traverse the network?
Which benefit is provided by ensuring that an endpoint is compliant with a posture policy configured in Cisco ISE?
A network administrator is configuring a switch to use Cisco ISE for 802.1X. An endpoint is failing
authentication and is unable to access the network. Where should the administrator begin troubleshooting to verify the authentication details?
Which Cisco platform processes behavior baselines, monitors for deviations, and reviews for malicious processes in data center traffic and servers while performing software vulnerability detection?
What are the two most commonly used authentication factors in multifactor authentication? (Choose two)
Which Talos reputation center allows for tracking the reputation of IP addresses for email and web traffic?
Which solution supports high availability in routed or transparent mode as well as in northbound and
southbound deployments?
Which IPS engine detects ARP spoofing?
What is the purpose of the Cisco Endpoint loC feature?
Which Cisco firewall solution supports configuration via Cisco Policy Language?
Which benefit does DMVPN provide over GETVPN?
Email security has become a high priority task for a security engineer at a large multi-national organization due to ongoing phishing campaigns. To help control this, the engineer has deployed an Incoming Content Filter with a URL reputation of (-10 00 to -6 00) on the Cisco ESA Which action will the system perform to disable any links in messages that match the filter?
Which two deployment modes does the Cisco ASA FirePower module support? (Choose two)
The main function of northbound APIs in the SDN architecture is to enable communication between which two areas of a network?
A network administrator is configuring a role in an access control policy to block certain URLs and selects the "Chat and instant Messaging" category. which reputation score should be selected to accomplish
this goal?
An engineer integrates Cisco FMC and Cisco ISE using pxGrid Which role is assigned for Cisco FMC?
An engineer must deploy a Cisco Secure Web Appliance. Antimalware scanning must use the Outbreak Heuristics antimalware category on files identified as malware before performing any other processes. What must be configured on the Secure Web Appliance to meet the requirements?
An administrator is trying to determine which applications are being used in the network but does not want the
network devices to send metadata to Cisco Firepower. Which feature should be used to accomplish this?
What is the target in a phishing attack?
An engineer is trying to decide between using L2TP or GRE over IPsec for their site-to-site VPN implementation. What must be un solution?
What are two benefits of using Cisco Duo as an MFA solution? (Choose two.)
What is the difference between EPP and EDR?
What must be enabled to secure SaaS-based applications?
An engineer is deploying a Cisco Secure Email Gateway and must configure a sender group that decides which mail policy will process the mail. The configuration must accept incoming mails and relay the outgoing mails from the internal server. Which component must be configured to accept the connection to the listener and meet these requirements on a Cisco Secure Email Gateway?
An engineer is configuring a Cisco ESA and wants to control whether to accept or reject email messages to a
recipient address. Which list contains the allowed recipient addresses?
An engineer is configuring AMP for endpoints and wants to block certain files from executing. Which outbreak
control method is used to accomplish this task?
Which two methods are available in Cisco Secure Web Appliance to process client requests when configured in Transparent mode? (Choose two.)
What is the purpose of the Trusted Automated exchange cyber threat intelligence industry standard?
Which two application layer preprocessors are used by Firepower Next Generation Intrusion Prevention
System? (Choose two)
Drag and drop the security responsibilities from the left onto the corresponding cloud service models on the right.
An engineer needs to add protection for data in transit and have headers in the email message Which configuration is needed to accomplish this goal?
What is a difference between Cisco AMP for Endpoints and Cisco Umbrella?
What can be integrated with Cisco Threat Intelligence Director to provide information about security threats,
which allows the SOC to proactively automate responses to those threats?
An organization wants to secure users, data, and applications in the cloud. The solution must be API-based and
operate as a cloud-native CASB. Which solution must be used for this implementation?
An organization wants to use Cisco FTD or Cisco ASA devices. Specific URLs must be blocked from being
accessed via the firewall which requires that the administrator input the bad URL categories that the
organization wants blocked into the access policy. Which solution should be used to meet this requirement?
Cisco SensorBase gaihers threat information from a variety of Cisco products and services and performs analytics to find patterns on threats Which term describes this process?
What are two ways a network administrator transparently identifies users using Active Directory on the Cisco WSA? (Choose two.) The eDirectory client must be installed on each client workstation.
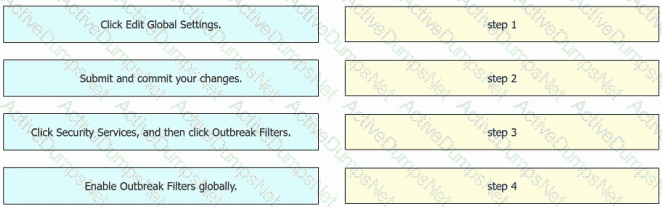
An engineer must enable Outbreak Filters globally on an AsyncOS for Cisco Secure Email Gateway to protect the network from large-scale malware attacks. Drag and drop the steps from the left into the sequence on the right to complete the configuration.
In which situation should an Endpoint Detection and Response solution be chosen versus an Endpoint
Protection Platform?
An attacker needs to perform reconnaissance on a target system to help gain access to it. The system has weak passwords, no encryption on the VPN links, and software bugs on the system’s applications. Which
vulnerability allows the attacker to see the passwords being transmitted in clear text?
Refer to the exhibit.
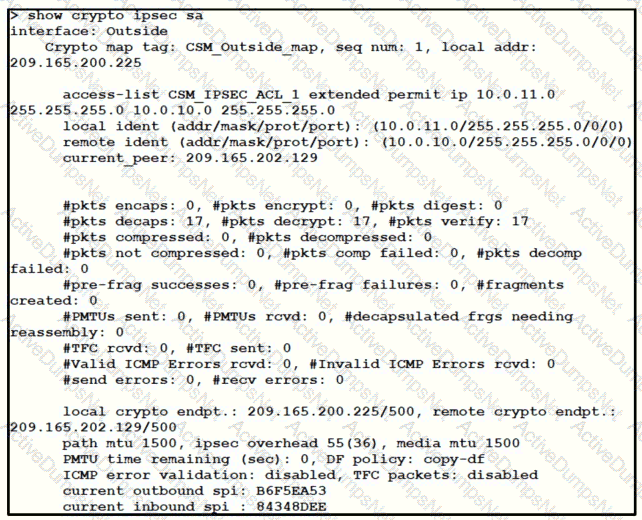
Traffic is not passing through IPsec site-to-site VPN on the Firepower Threat Defense appliance. What is causing this issue?
Which security solution uses NetFlow to provide visibility across the network, data center, branch
offices, and cloud?
When MAB is configured for use within the 802.1X environment, an administrator must create a policy that allows the devices onto the network. Which information is used for the username and password?