Cisco 350-101 Implementing and Operating Cisco Wireless Core Technologies (350-101 WLCOR)v1.0 Exam Practice Test
Implementing and Operating Cisco Wireless Core Technologies (350-101 WLCOR)v1.0 Questions and Answers
A university is deploying Cisco Catalyst 9176 APs at several satellite campuses, each with its own subnet and DNS services. The APs will be shipped with only their MAC addresses preregistered on the WLC. The satellite campuses do not use DHCP option 43, but they have access to a central DNS server. IT staff want APs to discover and join the Catalyst 9800 WLC automatically without site visits. Which solution must the IT staff implement?
How does the optimized roaming function operate in a WLC implementation?
How does the optimized roaming function operate in a WLC implementation?
A network engineer must ensure that guest users connecting to a Cisco 9800 WLC are assigned IP addresses from a specific subnet that is separate from corporate users. The guest network must support at least 200 simultaneous connections and isolate traffic from internal devices. The DHCP server must allocate addresses only within the 10.20.30.0/24 subnet. Which action must the network engineer take to accomplish this task?
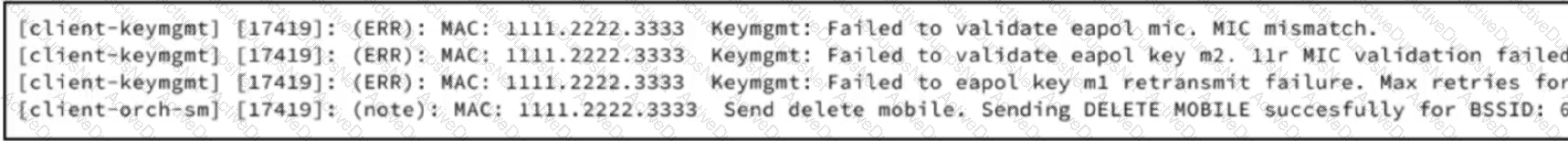
Refer to the exhibit. A network engineer must create a PSK WLAN that will be anchored to the DMZ. After this WLAN is created, users cannot connect to it. Based on the output from the RA trace, which action must the engineer take to resolve the issue?
What is a benefit of applying TACACS authentication for device access?
What defines RSSI in radio signal measurements?
Refer to the exhibit.
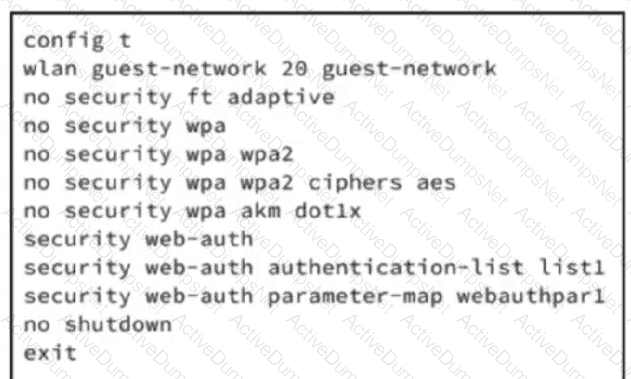
An engineer must configure wireless guest networking for a deployment at site A, which requires support for guest VLAN assignment and assignment for wlan guest-network 20. The controller will provide network segregation and restrict access to internal resources. Based on the configuration commands, which action meets the requirements?
Which Cisco technology leverages machine learning methods and a cloud learning platform that helps to identify critical issues?
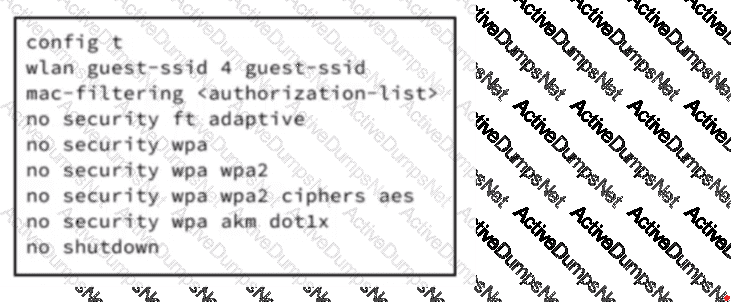
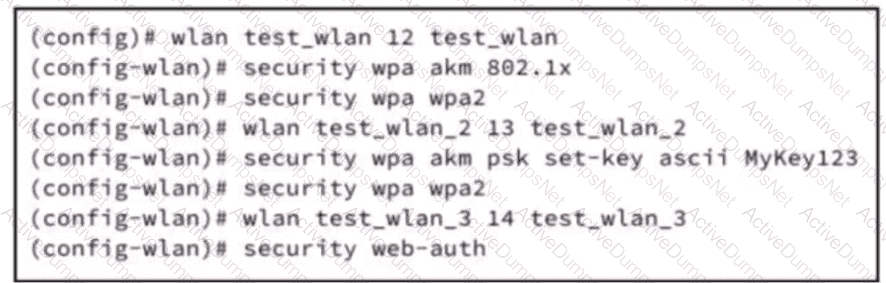
Refer to the exhibit. An engineer must configure a wireless guest WLAN, which requires clients to use VLAN 10 for a deployment at site A. Based on the configuration commands shown, which additional configuration meets the requirements?
Refer to the exhibit.
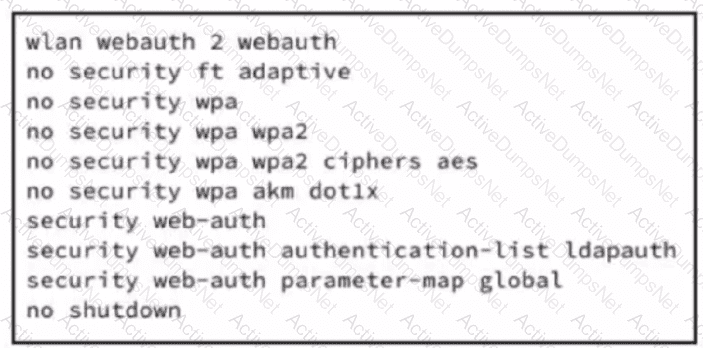 A wireless controller is deployed at a branch location to facilitate guest client connectivity. A network engineer configures one WLAN using Web authentication and activates web-based method to align with company security policies. Which configuration enables client authentication for this WLAN?
A wireless controller is deployed at a branch location to facilitate guest client connectivity. A network engineer configures one WLAN using Web authentication and activates web-based method to align with company security policies. Which configuration enables client authentication for this WLAN?
A network engineer has been tasked with migrating the management mode of a Cisco 9176 AP named "Cisco-AP053540555" in a large enterprise wireless deployment. The AP is currently managed by a Cisco Catalyst 9800 Series WLC, but the organization is transitioning to Meraki cloud management for centralized control and monitoring. To complete this migration, the engineer needs to change the AP's management mode to Meraki with force and noprompt to skip validations using the CLI on the wireless controller. What command must the engineer use?
What is a benefit of network adaptability in terms of improved operational outcomes when using AI-RRM in Cisco Catalyst Center?
A medium-sized enterprise must provide wireless internet to visitors in their lobby using a Cisco 9800 WLC. The solution must meet these requirements:
Ensure that guests cannot access the corporate LAN.
Guests are redirected to a login page before browsing.
The guest network must use a separate VLAN from internal users.
Access must be limited to web browsing only.
Guest access does not require any preshared keys or certificates.
Which two actions must be taken to achieve this solution? (Choose two.)
Refer to the exhibit.
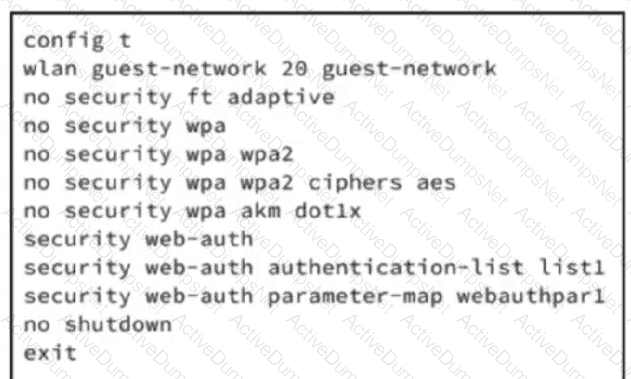
An engineer must configure wireless guest networking for a deployment at site A, which requires support for guest VLAN assignment and assignment for wlan guest-network 20. The controller will provide network segregation and restrict access to internal resources. Based on the configuration commands, which action meets the requirements?
Which process is managed by Ministry of Internal Affairs and Communications in Japan?
A wireless controller is deployed at a branch location to facilitate secure client connectivity. A network engineer configures one WLAN using WPA2 Personal authentication and activates the preshared key method to align with company security policies. Which action must be taken to enable the client to connect to the WLAN?
Which process is managed by Ministry of Internal Affairs and Communications in Japan?
A hotel wants to provide guests with wireless connectivity via a captive portal using a Cisco 9800 WLC. The solution must meet these requirements:
• Ensure that guests are redirected to a custom web page for login and after authentication must have only internet access.
• The guest SSID must not require a password and must be visible to all clients.
• Network segmentation between staff and guests is required at the VLAN level.
What must the IT team configure on the WLAN?
What does a low SNR value result in?
A network administrator at a marketing company is deploying a Cisco Catalyst 9800 Series Wireless Controller running Cisco IOS XE 17.x. The corporate WLAN named XYZ-Guest supports visitor devices. To address intermittent connectivity issues due to client association limits and short session timeouts, the network administrator must optimize the WLAN to allow more client connections and extend session timeouts for the devices. The administrator must set the maximum number of clients for the XYZ-Guest WLAN to 50 and must set a session timeout to prevent frequent device disconnections. Which two commands must be configured on the controller? (Choose two.)
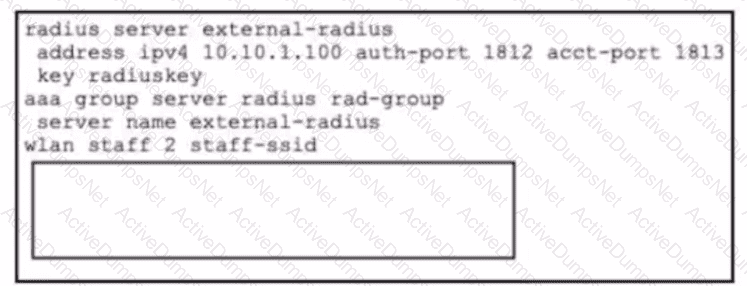
A network administrator is working on a Cisco Catalyst 9800 WLC running Cisco IOS XE Software to enable user access for staff smartphones using WPA2-Enterprise with RADIUS. The administrator verifies the external authentication configuration and plans to test network connectivity. Which configuration command must be added to the box in the code to configure the WLC to support authentication with an external server?
A hotel wants to provide guests with wireless connectivity via a captive portal using a Cisco 9800 WLC. The solution must meet these requirements:
• Ensure that guests are redirected to a custom web page for login and after authentication must have only internet access.
• The guest SSID must not require a password and must be visible to all clients.
• Network segmentation between staff and guests is required at the VLAN level.
What must the IT team configure on the WLAN?
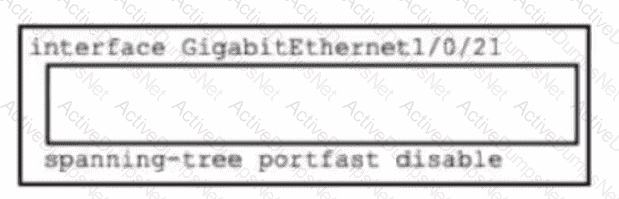
Refer to the exhibit. An engineer is configuring a switch port for a Cisco Spaces deployment at a new branch site. The Spaces connector requires access to the management VLAN 30. The network team plans to add more analytics services in the future, so the configuration must also allow for easy scalability and avoid service interruption for currently connected devices and default switch VLAN settings. Which set of commands must be added to the box in the CLI to complete the configuration?
Which role does a fabric edge node perform in a Cisco wireless fabric architecture?
Refer to the exhibit.
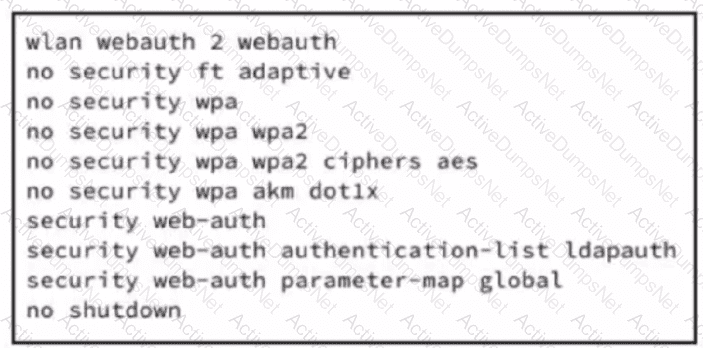 A wireless controller is deployed at a branch location to facilitate guest client connectivity. A network engineer configures one WLAN using Web authentication and activates web-based method to align with company security policies. Which configuration enables client authentication for this WLAN?
A wireless controller is deployed at a branch location to facilitate guest client connectivity. A network engineer configures one WLAN using Web authentication and activates web-based method to align with company security policies. Which configuration enables client authentication for this WLAN?
What is the main benefit of using AI Enhanced RRM on the Cisco Catalyst 9800 wireless controller?
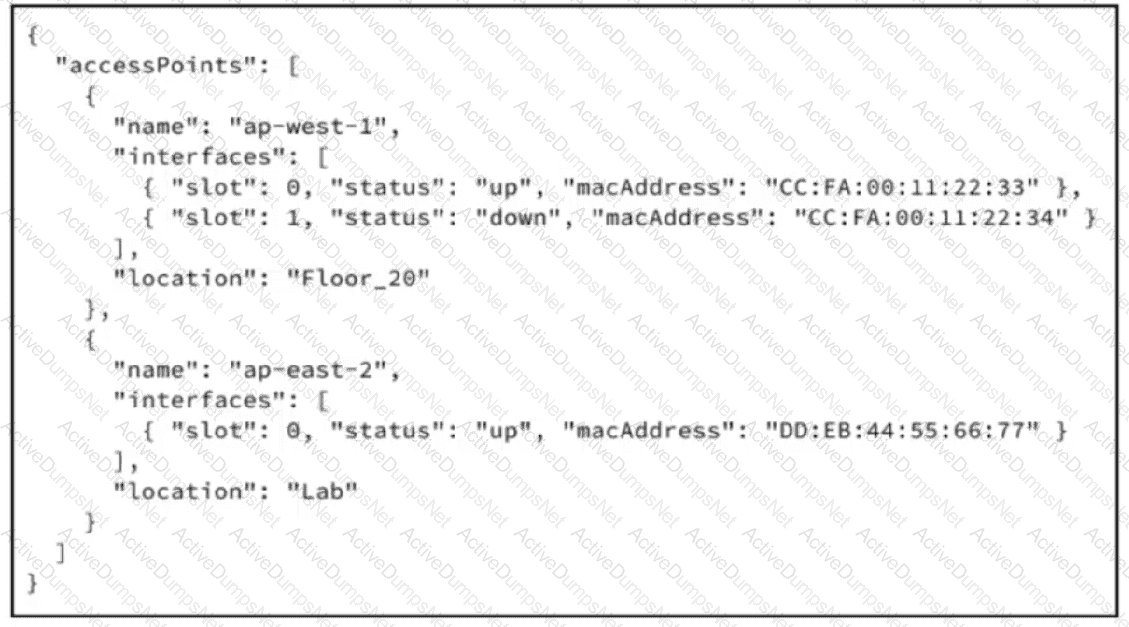
Refer to the exhibit. A JSON response from a wireless management API contains access point inventory and interface state information. Which JSON expression retrieves the MAC address of the second interface on the first access point?
What is a benefit of network adaptability in terms of improved operational outcomes when using AI-RRM in Cisco Catalyst Center?
Exhibit:
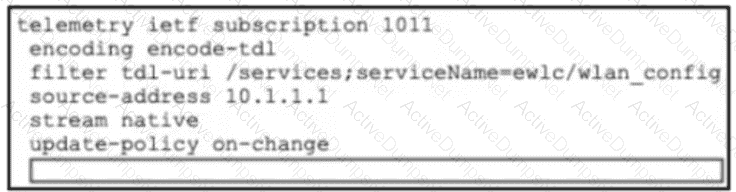
Refer to the exhibit. An organization wants to use Cisco Spaces for location analytics, and an engineer is setting up the Cisco Catalyst 9800 WLC to send location data. The Spaces connector has already been configured and is operational on the WLC. The engineer must now configure the controller to forward telemetry data to the correct Spaces cloud endpoint using TLS to complete the integration. Which CLI command must be added to the box in the code?
