Cisco 300-720 Securing Email with Cisco Email Security Appliance (300-720 SESA) Exam Practice Test
Securing Email with Cisco Email Security Appliance (300-720 SESA) Questions and Answers
Which predefined DLP category must be used by a network administrator to ensure that a company employee cannot send credit card information outside the company?
What is a benefit of implementing URL filtering on the Cisco ESA?
An admin istrator is managing multiple Cisco ESA devices and wants to view the quarantine emails from all devices in a central location.
How is this accomplished?
Which two Cisco ESA features are used to control email delivery based on the sender? (Choose two.)
What is the function of authenticating SMTP sessions using client certificates?
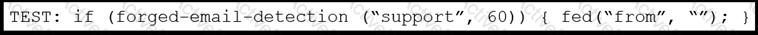
Refer to the exhibit. An engineer needs to change the existing Forged Email Detection message filter so that it references a newly created dictionary named ‘Executives’.
What should be done to accomplish this task?
An engineer is configuring a Cisco Secure Email Gateway and needs to reject email messages to a recipient with email address user0516585210@acme.com . Which list contains the allowed recipient addresses?
An engineer must configure Directory Harvest Attack Prevention for SMTP in Cisco Secure Email Gateway. This error message must be sent when the listener receives more than 50 invalid
recipients per hour.
•500 - Too many requests
•Max. Invalid Recipients Per Hour was set to 50 already.
Which two actions must be taken next to set maximum invalid recipients per hour to meet the requirement? (Choose two.)
Which two features are applied to either incoming or outgoing mail policies? (Choose two.)
Which component must be added to the content filter to trigger on failed SPF Verification or DKIM Authentication verdicts?
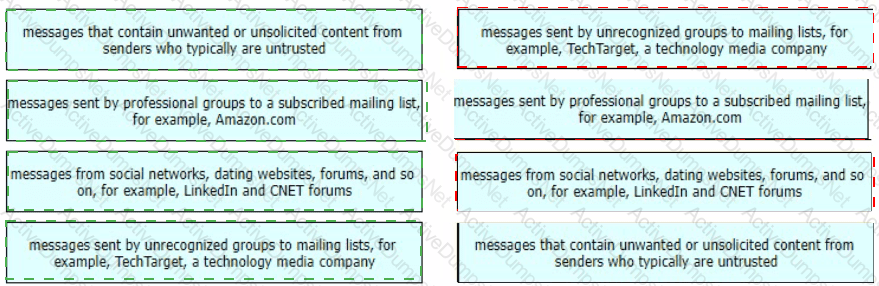
Drag and drop the graymail descriptions from the left onto the verdict categories they belong to on the right.

What is the purpose of Cisco Email Encryption on Cisco ESA?
A network engineer must tighten up the SPAM control policy of an organization due to a recent SPAM attack. In which scenario does enabling regional scanning improve security for this organization?
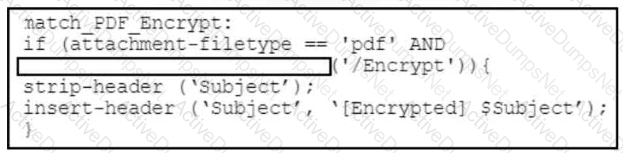
Refer to the exhibit. A security engineer must create a message filter on a Cisco Secure Email Gateway to scan all incoming emails for encrypted PDF files. Which code snippet completes the message filter?
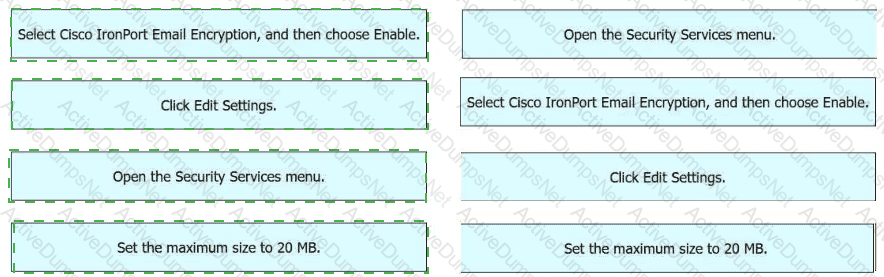
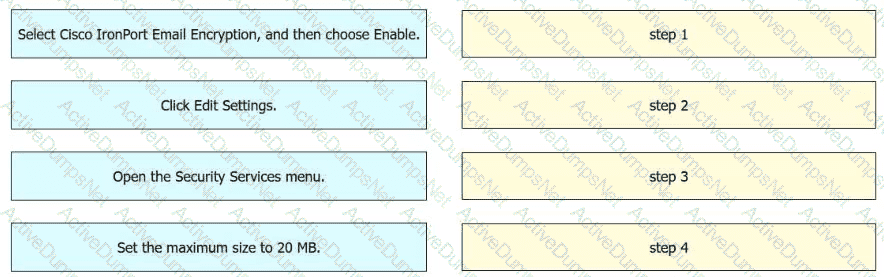
An engineer must enable encryption on a Cisco Secure Email Gateway. The maximum size of each message must be 20 MB. Drag and drop the actions from the left into sequence on the right to meet the requirement.
An engineer must modify the altsrchost table on a Cisco Secure Email Gateway Messages destined for a domain named @cisco.com must be mapped to Newlnterface with an IP address of 10.10.10.1. What must be added to the table?
The CEO sent an email indicating that all emails containing a string of 123ABCDEFGHJ cannot be delivered and must be sent into quarantine for further inspection. Given the requirement, which regular expression should be used to match on that criteria?
Which Cisco Secure Email Threat Defense visibility and remediation mode is only available when using Cisco Secure Email Gateway as the message source?
A Cisco Secure Email Gateway administrator must provide outbound email authenticity and configures a DKIM signing profile to handle this task. What is the next step to allow this organization to use DKIM for their outbound email?
The security administrator wants to configure alerts on Cisco Secure Email Gateway for outbreak filters. Which two actions must be taken to meet the requirement? (Choose two.)
An engineer must provide differentiated email filtering to executives within the organization Which two actions must be taken to accomplish this task? (Choose two)
A trusted partner of an organization recently experienced a new campaign that was leveraging JavaScript attachments to trick users into executing malware. As a result, they created a local policy to deny messages with JavaScript attachments. Which action should the administrator of the organization take to ensure encrypted communications are delivered to the intended partner recipient?
Which two steps are needed to disable local spam quarantine before external quarantine is enabled? (Choose two.)
Which of the following two steps are required to enable Cisco SecureX integration on a Cisco Secure Email Gateway appliance? (Choose two.)
What are two primary components of content filters? (Choose two.)
Refer to the exhibit.
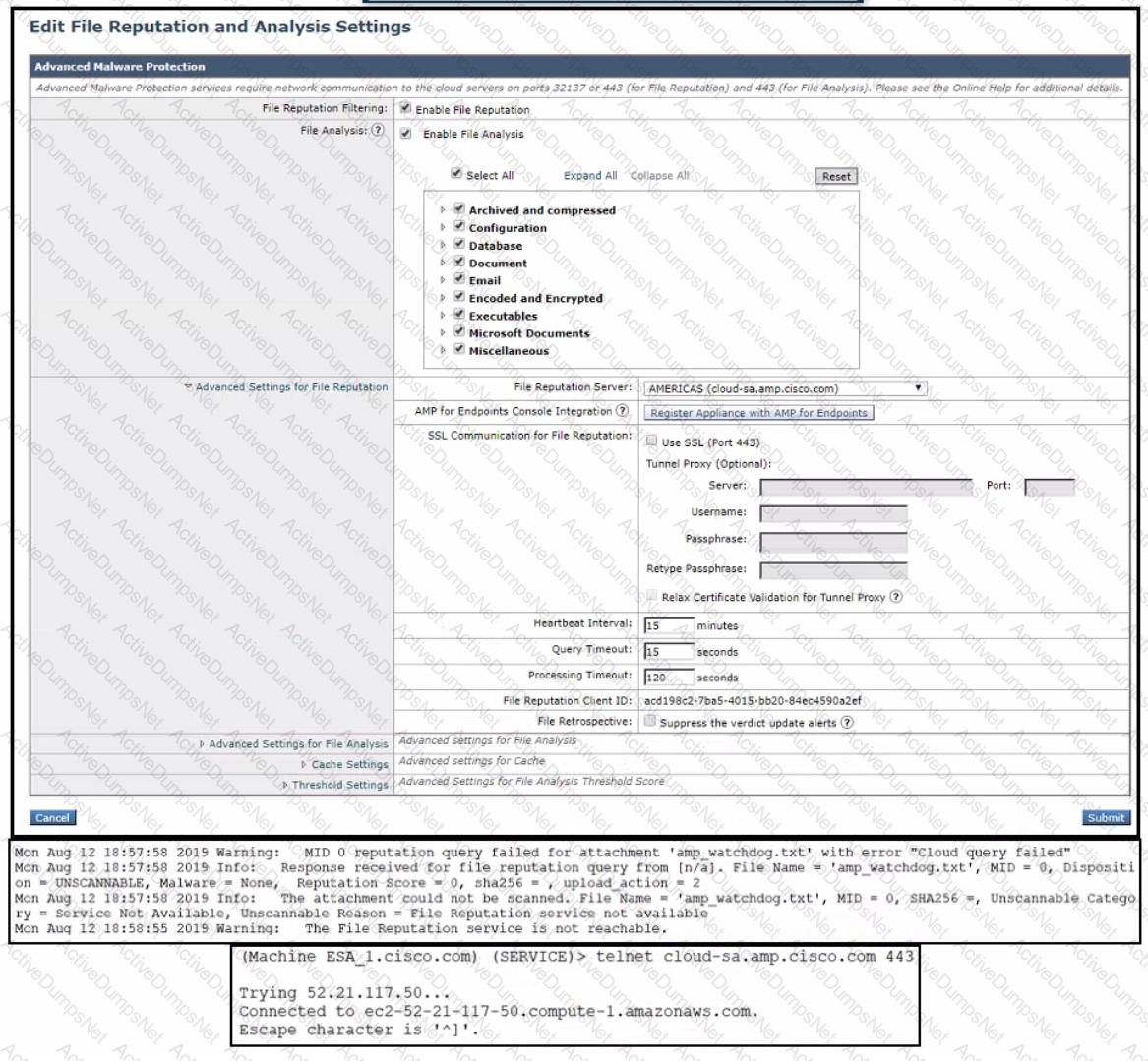
An administrator has configured File Reputation and File Analysis on the Cisco Secure Email Gateway appliance however it does not function as expected What must be configured on the appliance for this to function?
Which action is allowed while managing list of certificate authorities on Cisco Secure Email Gateway?
What are organizations trying to address when implementing a SPAM quarantine?
Refer to the exhibit.

Which SPF record is valid for mycompany.com?
When a network engineer is troubleshooting a mail flow issue, they discover that some emails are rejected with an SMTP code of 451 and the error message " #4.7.1 Unable to perform DMARC verification " . In the DMARC verification profile on the Cisco Secure Email Gateway appliance, which action must be set for messages that result in temporary failure to prevent these emails from being rejected?
Refer to the exhibit.
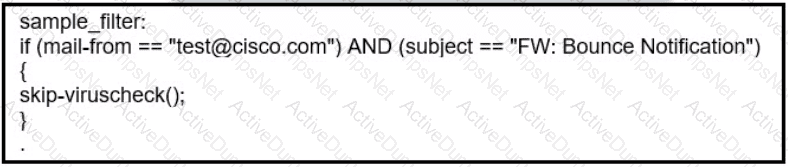
What results from this filter configuration?
When outbreak filters are configured, which two actions are used to protect users from outbreaks? (Choose two.)
An engineer tries to implement phishing simulations to test end users, but they are being blocked by the Cisco Secure Email Gateway appliance. Which two components, when added to the allow list, allow these simulations to bypass antispam scanning? (Choose two.)
An engineer tries to implement phishing simulations to test end users, but they are being blocked by the Cisco Secure Email Gateway appliance. Which two components, when added to the allow list, allow these simulations to bypass antispam scanning? (Choose two.)
Which action must be taken before a custom quarantine that is being used can be deleted?
What is the default behavior of any listener for TLS communication?
A network engineer is reviewing the record presented.

Which type of DNS record would contain the record as per the DKIM public key RFC 6376?
Which two steps configure Forged Email Detection? (Choose two.)
Which two components form the graymail management solution in Cisco ESA? (Choose two.)
An engineer must share threat reporting information from Cisco Secure Email Gateway to Cisco SecureX. Which setting must be enabled in Secure Email Gateway?
Which Cisco ESA security service is configured only through an outgoing mail policy?
Which setting affects the aggressiveness of spam detection?
What is the order of virus scanning when multilayer antivirus scanning is configured?
When virtual gateways are configured, which two distinct attributes are allocated to each virtual gateway address? (Choose two.)
Which SMTP extension does Cisco ESA support for email security?
Which attack is mitigated by using Bounce Verification?
Which method enables an engineer to deliver a flagged message to a specific virtual gateway address in the most flexible way?
What are two prerequisites for implementing undesirable URL protection in Cisco ESA? (Choose two.)
Which two components must be configured to perform DLP scanning? (Choose two.)
How does the graymail safe unsubscribe feature function?
A network engineer is integrating Cisco Secure Email Gateway with Cisco SecureX. Which two actions must be taken before registering Cisco Secure Email Gateway with Cisco SecureX? (Choose two.)
An engineer deploys a Cisco Secure Email Gateway appliance with default settings in an organization that permits only standard H feature does not work. Which additional action resolves the issue?
Which type of attack does Bounce Verification fight against?
Which feature must be activated on a Cisco Secure Email Gateway to combat backscatter?
Which benefit does enabling external spam quarantine on Cisco SMA provide?
Which two actions are configured on the Cisco ESA to query LDAP servers? (Choose two.)
The CEO added a sender to a safelist but does not receive an important message expected from the trusted sender. An engineer evaluates message tracking on the Cisco Secure Email Gateway appliance and determines that the message was dropped by the antivirus engine. What is the reason for this behavior?
Which feature must be configured before an administrator can use the outbreak filter for nonviral threats?