APICS CPIM-8.0 Certified in Planning and Inventory Management (CPIM 8.0) Exam Practice Test
Certified in Planning and Inventory Management (CPIM 8.0) Questions and Answers
An attacker was able to identify an organization’s wireless network, collect proprietary network resource information, and capture several user credentials. The attacker then used that information to conduct a more sophisticated and impactful attack against the organization. Which method did the attacker MOST likely use to gather the initial information?
An organization implemented a threat modeling program focusing on key assets. However, after a short time it became clear that the organization was having difficulty executing the threat modeling program.
Which approach will MOST likely have been easier to execute?
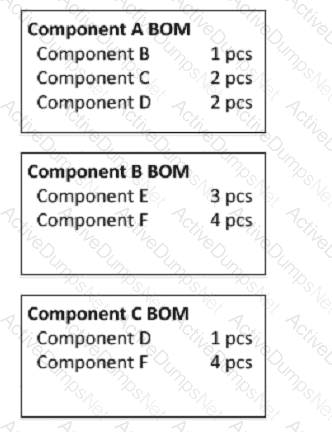
Given the bill of material (BOM) information below and independent requirements of 10 pieces (pcs) per week of Component A and 20 pieces (pcs) per week of Component B, what is the weekly gross requirement of component F?
Which of the following incorporates design techniques promoted by Crime Prevention Through Environmental Design (CPTED)?
Payment Card Industry Data Security Standard (PCI DSS) allows for scanning a statistical sample of the environment without scanning the full environment. Scanning a statistical sample has many advantages and disadvantages.
Which of the following is the MOST accurate set of advantages and disadvantages?
A product manager wishes to store sensitive development data using a cloud storage vendor while maintaining exclusive control over passwords and encryption credentials. What is the BEST method for meeting these requirements?
Which of the following provides that redundancy and failover capabilities are built into a system to maximize its uptime?
What does the Role-Based Access Control (RBAC) method define?
A security engineer is implementing a Supervisory Control and Data Acquisition (SCADA) system.
What is the BEST action the engineer can take to ensure secure operations?
Which of the following is the MOST significant flaw when using Federated Identity Management (FIM)?
A large retail organization will be creating new Application Programming Interfaces (API) as part of a customer-facing shopping solution. The solution will accept information from users both inside and outside of the organization. What is the safest software development practice the team can follow to protect the APIs against Structured Query Language Injection (SQLi) attacks?
In the context of mobile device security, which of the following BEST describes why a walled garden should be implemented?
An organization has identified that an individual has failed to adhere to a given standard set by the organization. Based on the needs of the organization, it was decided that an exception process will be created. What is the PRIMARY benefit of establishing an exception process?
Which of the following production activity control (PAC) techniques focuses on optimizing output?
Which of the following should Business Impact Analysis (BIA) reports always include?
An organization is implementing Zero Trust Network Access (ZTNA) and needs a strategy to measure device trust for employee laptops. Which measurement strategy is BEST suited and why?
In a lean environment, the batch-size decision for planning " A " items would be done by:
Which of the following is a document that will be obtained at the end of an asset’s lifecycle?
In a make-to-order (MTO) production environment, fluctuations in sales volumes are managed by adjustments to the:
Up-to-date Information about production order status is required to do which of the following tasks?
If organizational leadership determines that its required continuous monitoring plan is too costly for the organization, what action should be taken by leadership and the Authorizing Official (AO)?
An organization is transitioning from a traditional server-centric infrastructure to a cloud-based Infrastructure. Shortly after the transition, a major breach occurs to the organization ' s databases. In an Infrastructure As A Service (IaaS) model, who would be held responsible for the breach?
An organization recently completed an acquisition of another entity and staff members are complaining about the excessive number of credentials they need to remember as each application requires separate logins. This is negatively affecting collaboration efficiency and increasing the risk of human errors. What will the organization consider implementing as part of the solution to improve the situation?
An organization wishes to utilize a managed Domain Name System (DNS) provider to reduce the risk of users accessing known malicious sites when web browsing. The organization operates DNS forwarders that forward queries for all external domains to the DNS provider. Which of the following techniques could enable the organization to identify client systems that have attempted to access known malicious domains?
What is the HIGHEST security concern on trans-border data?
Capacity requirements planning (CRP) is applicable primarily In companies operating In an environment where:
An advertising agency is working on a campaign for a prospective client. Competitors are working on a similar campaign and are interested in knowing what the firm has designed. What should the advertising agency do to BEST ensure intellectual property does not leave the organization?
Which of the following factors is the MOST important consideration for a security team when determining when determining whether cryptographic erasure can be used for disposal of a device?
When the discrete available-to-promise (ATP) method is used, the master production receipt quantity is committed to:
An organization ' s security policy requires remote hosts to be authenticated before they can access network resources. Which of the following is the BEST option for the organization to enforce its policy?
Which of the following statements is true about the meantime between failures (MTBF) measure?
In times of monetary inflation, which of the following methods of inventory valuation results in the greatest cost of sales for the early years of a particular product?
Which of the below represent the GREATEST cloud-specific policy and organizational risk?
How would blockchain technology support requirements for sharing audit information among a community of organizations?
What should an organization do to prepare for Disaster Recovery (DR) efforts?
Which of the following is the MOST effective approach to reduce the threat of rogue devices being introduced to the internal network?
In a Discretionary Access Control (DAC) model, how is access to resources managed?
The question below is based on the following information:
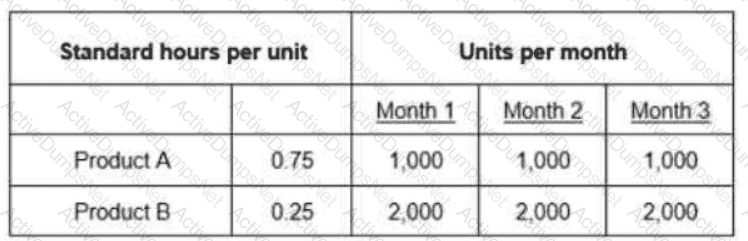
Work Center 1 has an available capacity of 1,200 hours per month. Which of the following amounts represents the cumulative difference between the required capacity and the available capacity of Months 1 through 3?
Privacy requirements across national boundaries MOST often require protection of which data types?
An organization has decided to leverage open source software for its latest application development project. Which of the following would be the MOST effective way to ensure the open source software can be used securely while still meeting business requirements?
A financial institution is implementing an Information Technology (IT) asset management system. Which of the following capabilities is the MOST important to include?
A security administrator of a large organization is using Mobile Device Management (MDM) technology for protecting mobile devices. Which of the following is the BEST way to ensure that only company-approved mobile software can be deployed?
A security specialist is responsible to improve the security awareness program of a medium-sized organization and tasked to track blocked targeted attacks. Which of the following BEST describes the outcome of the security specialist’s use of metrics for this task?
Which if the following is the FIRST control step in provisioning user rights and privileges?
A security engineer needs to perform threat modeling on a microprocessor design for an Internet of Things (IoT) application. Using the MITRE Common Weakness Enumeration (CWE) catalog for hardware, a risk analysis is performed. What kind of threat modeling approach would be BEST to identify entry points into the system based on motivation?
What is the total load requirement for this work center based on the following data?
A part is sold as a service part, and It is also used as a component In another part. Which of the following statements about the planning for this part is true?
An organization’s computer incident response team PRIMARILY responds to which type of control?
Which of the following items does the master scheduler have the authority to change in the master scheduling process?
A newly hired Chief Information Security Officer (CISO) is now responsible to build a third-party assurance for their organization. When assessing a third-party, which of the following questions needs to be answered?
A health care organization ' s new cloud-based customer-facing application is constantly receiving security events from dubious sources. What BEST describes a security event that compromises the confidentiality, integrity or availability of the application and data?
What is the PRIMARY benefit an organization obtains by cybersecurity framework to their cybersecurity program?
Which of the following actions hinders the transition from a push system to a pull system?
An OpenID Connect (OIDC) authorization server received two requests from a client. The server identifies the request as replay attack and rejects the request. Which of the following BEST describes these requests?
What can help a security professional assess and mitigate vulnerabilities of an embedded device?
An organization provides customer call center operations for major financial service organizations around the world. As part of a long-term strategy, the organization plans to add healthcare clients to the portfolio. In preparation for contract negotiations with new clients, to which cybersecurity framework(s) should the security team ensure the organization adhere?
A security engineer developing software for a professional services organization has a requirement that users cannot have concurrent access to data of clients that are competitors. Which security model should the security engineer implement to meet this requirement?
Zombieload, Meltdown, Spectre, and Fallout are all names of bugs that utilized which of the following types of attack?
A hot Disaster Recovery (DR) data center is the victim of a data breach. The hackers are able to access and copy 10GB of clear text confidential information. Which of the following could have decreased the amount of exposure from this data breach?
An organization donates used computer equipment to a non-profit group. A system administrator used a degausser on both the magnetic and Solid State Drives (SSD) before delivery. A volunteer at the non-profit group discovered some of the drives still contained readable data and alerted the system administrator. What is the BEST solution to ensure that computer equipment does not contain data before release?
To mitigate risk related to natural disasters, an organization has a separate location with systems and communications in place. Data must be restored on the remote systems before they are ready for use. What type of remote site is this?
A Software As A Service (SaaS) solution was compromised due to multiple missing security controls. The SaaS deployment was rushed and the Software Development Life Cycle (SDLC) was not followed. Which SDLC phase would have been MOST effective in preventing this failure?
Which of the following does a federated Identity Provider (IDP) need in order to grant access to identity information?
An organization has network services in a data center that are provisioned only for internal use, and staff at offices and staff working from home both use the services to store sensitive customer data. The organization does not want the Internet Protocol (IP) address of the service to receive traffic from users not related to the organization. Which technology is MOST useful to the organization in protecting this network?
An organization’s system engineer arranged a meeting with the system owner and a few major stakeholders to finalize the feasibility analysis for a new application.
Which of the following topics will MOST likely be on the agenda?
A house of quality (HOQ) chart aligns which pair of functions?
Which of the following data is needed to determine gross requirements when conducting distribution requirements planning (DRP)?
The question below is based on the following standard and actual data of a production order
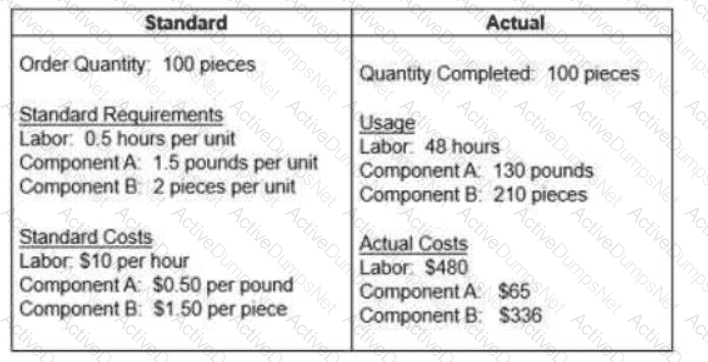
Which of the following statements about variances is true?
What is the MAIN purpose of risk and impact analysis?
An organization is restructuring its network architecture in which system administrators from the corporate office need to be able to connect to the branch office to perform various system maintenance activities. What network architecture would be MOST secure?
What resources does a respondent have when contesting disciplinary action taken by the ISC2 Board of Directors?
A Structured Query Language (SQL) database is hosted on a hardened, secure server. All unused ports are locked down, but external connections from untrusted networks are still required to be allowed through. What is the BEST way to ensure transactions to/from this server remain secure?
An organization’s computer incident responses team PRIMARY responds to which type of control?
Which of the following is the MOST effective practice for tracking organizational assets when removed from the premises?
A large organization wants to implement a vulnerability management system in its internal network. A security professional has been hired to set up a vulnerability scanner on premises and to execute the scans periodically. Which of the following should be the FIRST action performed by the security professional?
An information system containing Protected Health Information (PHI) will be accessed by doctors, nurses, and others working in a hospital. The same application will be used by staff in the pharmacy department only for dispensing prescribed medication. Additionally, patients can log in to view medical history. The system owner needs to propose an access control model that considers environment, situation, compliance, and security policies while dynamically granting the required level of access. Which access control model is the MOST suitable?
An organization has hired a new auditor to review its critical systems infrastructure for vulnerabilities. Which of the following BEST describes the methodology the auditor will use?
A cybersecurity analyst is responsible for identifying potential security threats and vulnerabilities in the organization ' s software systems. Which action BEST demonstrates the understanding and application of threat modeling concepts and methodologies?
An organization is running a cloud-based application to process the information obtained at point-of-sale devices. Which guideline should be applied to the application?
Which of the following systems would be the most cost-efficient for inventory management of a low value item?
Which of the following is the GREATEST threat for a Border Gateway Protocol (BGP) deployment on the internet?
When considering Defense in Depth (DiD) as part of a network’s architectural design, what is the FIRST layer in a multi-layered defensive strategy?
In pyramid forecasting, the " roll up " process begins with:
Which role is MOST accountable for allocating security function resources in order to initiate the information security governance and risk management policy?
A manufacturer begins production of an item when a customer order is placed. This is an example of a(n):
In order to meet retention requirements, it may be necessary to migrate digital records to different media because of which of the following issues?
An organization is aiming to be System and Organization Controls (SOC) 2 certified by an audit organization to demonstrate its security and availability maturity to its sub service organizations. Which type of audit does this engagement BEST describe?
Internet Small Computer Systems Interface (iSCSI) protocol relies on Transmission Control Protocol/Internet Protocol (TCP/IP). Which can be used maliciously to interrupt the flow of data. Which Information Technology (IT) component would be impacted by such a disruption?
A financial services organization wants to deploy a wireless network. Which of the following is the WEAKEST option for ensuring a secure network?
What is the BEST way to plan for power disruptions when implementing a Disaster Recovery Plan (DRP)?
A disadvantage of a capacity-lagging strategy may be:
Which of the following sampling techniques is BEST suited for comprehensive risk assessments?
An effective approach to projecting requirements for materials with long lead times Includes which of the following options?
What is the BEST item to consider when designing security for information systems?
Which technology is BEST suited to establish a secure communications link between an individual’s home office and the organization’s Local Area Network (LAN)?
Based on the above table, calculate the mean absolute deviation (MAD).
A security team is analyzing the management of data within the human resources systems, as well as, the intended use of the data, and with whom and how the data will be shared. Which type of assessment is the team MOST likely performing?
Which of the following situations is most likely to occur when using a push system?
What is the BEST reason to include a Hardware Security Module (HSM) in the key management system when securing cloud storage?
A regular remote user executed an application that allowed the execution of commands with elevated permissions. It was allowed to create new users, start and stop services, and view critical log files. Which exploit type did the application use in this scenario?
A web developer was recently asked to create an organization portal that allows users to retrieve contacts from a popular social media platform using Hypertext Transfer Protocol Secure (HTTPS). Which of the following is BEST suited for authorizing the resource owner to the social media platform?
Return on investment (ROI) is decreased by which of the following activities?
A third-party vendor is procured to conduct a non-financial audit. Which report evaluates the effectiveness of the controls?
Global outsourcing and shared suppliers serving an industry are drivers of which category of risk?
Which of the following are steps involved in the identity and access provisioning lifecycle?
Which of the following roles is the BEST choice for classifying sensitive data?
What is the main negative effect of changing the due dates of open orders?
Additional requirements that are outside the original design are being added to a project, increasing the timeline and cost of the project.
What BEST describes the requirement changes that are happening?
Which is the MOST valid statement around the relationship of security and privacy?
To gain entry into a building, individuals are required to use a palm scan. This is an example of which type of control?
An organizations is developing a new software package for a financial institution. What is the FIRST step when modeling threats to this new software package?
Long lead-time items with stable demand would best be supported by a supply chain:
Which of the following threats MUST be included while conducting threat modeling for a Cloud Service Provider (CSP)?
A company’s Marketing and Sales departments have identified an opportunity to develop a new market for a product family and requested an increase in the production plan. Which of the following actions would be most appropriate to account for the new market opportunity?
Which of the following capabilities BEST distinguishes a Next-Generation Firewall (NGFW) from a traditional firewall?
Health information stored in paper form may be destroyed using which of the following methods?
A systems engineer has been tasked by management to provide a recommendation with a prioritized, focused set of actions to help the organization stop high-risk cyber attacks and ensure data security. What should the systems engineer recommend the organization use to accomplish this?
Which software development methodology is an iterative customer-value-centric approach which helps teams deliver value to their customers faster and with fewer problems?
Which of the following tactics can be employed effectively to reduce appraisal quality costs?
Which of the following controls should a financial Institution have in place in order to prevent a trader from both entering and executing a trade?
Cloud computing introduces the concept of the shared responsibility model. This model can MOST accurately be described as defining shared responsibility between which of the following?
Following the setting of an organization’s risk appetite by senior management, a risk manager needs to prioritize all identified risks for treatment. Each risk has been scored based on its Annualized Loss Expectancy (ALE). Management has asked for an immediate risk mitigation plan focusing on top risks. Which is the MOST effective approach for the risk manager to quickly present a proposal to management?
Which of the following is a threat modeling methodology used for accessing threats against applications and Operating Systems (OS)?
An organization is considering options to outsource their Information Technology (IT) operations. Although they do not sell anything on the Internet, they have a strong requirement in uptime of their application. After the offerings received by the Cloud Service Provider (CSP), the IT manager decided it was mandatory to develop processes to continue operations without access to community or public cloud-based applications. Which of the following arguments MOST likely led the IT manager to make this decision?
Which of the below represents the GREATEST cloud-specific policy and organizational risk?
A newer automotive supplier has not fully developed its information technology (IT) systems. The supplier has Just received a contract from a large automotive manufacturer which requires the supplier to use electronic data interchange (EDI) transactions for receiving orders, sending advance ship notices (ASNs), and receiving invoice payments. What strategy can the supplier adopt to immediately meet the EDI requirements?
Which of the following BEST characterizes the operational benefit of using immutable workloads when working on a cloud-based project?
An organization has received the results of their network security risk assessment. What is the BEST course of action for the organization to take in response to the analyzed report findings?
A security practitioner notices that workforce members retain access to information systems after transferring to new roles within the organization, which could lead to unauthorized changes to the information systems.
This is a direct violation of which common security model?
An example of an assignable cause of variation in process performance is:
The master schedule is an Important tool in the sales and operations planning (S & OP) process because it:
An organization is having bandwidth utilization issues due to unauthorized devices on the network. Which action should be taken to solve the problem?
Objective security metrics tend to be easier to gather, easier to interpret, and easier to include in reports to management.
What is the BEST objective metric for the effectiveness of a security awareness training?
What FIRST step should a newly appointed Data Protection Officer (DPO) take to develop an organization ' s regulatory compliance policy?
When designing a production cell, which of the following items would be the most important consideration?
Which of the following tools shows process changes and random variation over time?
Which of the following Internet Protocol Security (IPSec) components provides the MOST confidentiality for the information that is being transmitted?
Which of the following methods would be appropriate for forecasting the demand for a product family when there is a significant trend and seasonality in the demand history?
An organization is migrating its access controls to a certificate-based authentication system.
What will need to be established to verify the identity of all users connecting to the network before rolling out the system?
A forecasting method that responds slowly to changes in demand would be most appropriate when the historical demand pattern shows a:
Which of the following attributes describes a company with a global strategy?
An organization is concerned that if an employee’s mobile device is lost or stolen and does not reconnect to the carrier network, the data on the device may still be at risk. Consequently, the organization has implemented a control on all mobile devices to require an eight-character passcode for unlock and login. What should happen after multiple incorrect passcode attempts?
Which of the following statements is an advantage of a fourth-party logistics (4PL) provider?
The time spent In queue by a specific manufacturing job is determined by which of the following factors related to the order?
An organization decides to conduct penetration testing. Senior management is concerned about the potential loss of information through data exfiltration. The organization is currently preparing a major product launch that is time-sensitive. Which of the following methods of testing is MOST appropriate?
An organization has hired a new auditor to review its critical systems infrastructure for vulnerabilities. Which of the following BEST describes the methodology the auditor will use to test whether servers are set up according to the organization ' s documented policies and standards?
Which of the following ensures privileges are current and appropriately reflect an individual’s authorized roles and responsibilities?
The most relevant measure of customer service performance Is:
Which of the following security features is utilized to validate both user credentials and the health of the client device on a network?
An information security professional is tasked with configuring full disk encryption on new hardware equipped with a Trusted Platform Module (TPM). How does TPM further enhance the security posture of full disk encryption if configured properly?
A stockout of dependent-demand item X occurred during the holiday season. To understand the root cause of the stockout, the planner should check if:
A manufacturer uses a low-cost strategy. It recently reviewed its components and realized it is using multiple versions of one screw. Reducing the variety of screws will contribute to its cost advantage by:
Which of the following criteria is used to determine safety stock in a distribution center (DC)?
A security specialist is responsible to improve the security awareness program of a medium-sized organization and is tasked to track blocked targeted attacks. Which of the following BEST describes the outcome of the security specialist’s use of metrics for this task?
Which of the following can allow an attacker to bypass authentication?
Which of the following is the BEST activity to mitigate risk from ransomware on mobile devices and removable media in a corporate environment?
The development team wants new commercial software to Integrate into the current systems. What steps can the security office take to ensure the software has no vulnerabilities?
An organization is implementing improvements to secure the Software Development Life Cycle (SDLC). When should defensive three modeling occur?
A reduction In purchased lot sizes will reduce which of the following items?
What function prevents unauthorized devices from gaining access to a network?
A company implementing a localized multi-country strategy to increase market share should engage in which of the following actions?
Business management should be engaged in the creation of Business Continuity (BC) and Disaster Recovery plans (DRP) because they need to
In the sales and operations planning (S & OP) process, the demand management function provides:
Plans are being made to move an organization’s software systems to the cloud in order to utilize the flexibility and scalability of the cloud. Some of these software systems process highly sensitive data. The organization must follow strict legal requirements regarding the location of the highly sensitive data processed by the software systems. Which cloud model will BEST fit the organization’s requirements?
A security consultant is recommending the implementation of a security-focused Configuration Management (CM) process in an organization. What would be the BEST benefit the security consultant would include in the recommendation?
In order for an organization to mature their data governance processes to ensure compliance, they have created a data classification matrix.
What are the next BEST activities to build on this completed work?
The Cloud Security Alliance (CSA) publishes the Egregious Eleven, a list of common threats to organizations using cloud services. According to the CSA Egregious Eleven, which of the following cases falls under the category of misconfiguration and inadequate change control?
The horizon for forecasts that are input to the sales and operations planning (S & OP) process should be long enough that:
Which of the following is the benefit of using Security Content Automation Protocol (SCAP) version 2 on endpoint devices?
Which of the following BEST represents a security benefit of Software-Defined Networking (SDN)?
An organization is preparing for a natural disaster, and management is creating a Disaster Recovery Plan (DRP). What is the BEST input for prioritizing the restoration of vital Information Technology (IT) services?
Which of the following BEST describes web service security conformance testing as it relates to web services security testing?
A Generic Routing Encapsulation (GRE) tunnel moves data across a third-party Internet Protocol (IP) network. What is the risk of using GRE tunnels?
Which of the following BEST effective when protecting against insider threats?
Disaster Recovery (DR) training plan outcomes should have which KEY quality?
An organization discovered that malicious software was installed on an employee’s work laptop and allowed a competing vendor to access confidential files. The employee was fully aware of the policy not to install unauthorized software on the organization laptop. What is the BEST automated security practice for an organization to implement to avoid this situation?
In a rapidly changing business environment, a primary advantage of an effective customer relationship management (CRM) program is:
What order BEST reflects the steps when adding threat modeling practices to a Software Development Life Cycle (SDLC)?
An organization’s security team is looking at ways to minimize the security risk of the container infrastructure. The lead engineer needs to select a suite of remediation actions to minimize risks. Which programmatic approach will result in preventing, detecting , and responding to the GREATEST number of threats aimed at container operations?
A United States (US)-based online gaming provider, which operates in Germany, collects and uses a large amount of user behavioral data. A customer from Germany requests a copy of all their personal data.
What is the MOST appropriate course of action for the organization to take?
Which of the following documents is the BEST reference to describe application functionality?
